2 EPAP Security Overview
This chapter describes basic security considerations and provides an overview of EPAP security.
2.1 Basic Security Considerations
The following principles are fundamental to using any application securely:
- Keep software up to date. This includes the latest product release and any patches that apply to it. Consult with your Oracle support team to plan for EPAP software upgrades.
- Limit privileges as much as possible. Users should be given only the access necessary to perform their work. User privileges should be reviewed periodically to determine relevance to current work requirements.
- Monitor system activity. Establish who should access which system components, and how often, and monitor those components.
- Install software securely. For example, use firewalls, secure protocols such as SSL, and strong passwords.
- Learn about and use the EPAP security features. See Implementing EPAP Security for more information.
- Keep up to date on security information. Oracle regularly issues security-related patch updates and security alerts. You must install all security patches as soon as possible. See the "Critical Patch Updates and Security Alerts" Web site: http://www.oracle.com/technetwork/topics/security/alerts-086861.html
2.2 Understanding the EPAP Environment
The EPAP platform, coupled with the Provisioning Database Application (PDBA), facilitates and maintains the database required by EPAP-related features. See the Glossary for a list of EPAP-related features. The EPAP serves two major purposes:
- Accept and store data provisioned by the customer
- Update customer provisioning data and reload databases on the Service Module cards in the Multi Purpose Server (MPS)
The MPS hardware platform supports high speed provisioning of large databases for the EAGLE. The MPS is composed of hardware and software components that interact to create a secure and reliable platform. MPS supports the EPAP.
During normal operation, information flows through the EPAP and PDBA with no intervention. Each EPAP has a graphical user interface that supports maintenance, debugging, and platform operations. The EPAP user interface includes a PDBA user interface for configuration and database maintenance.
2.3 Recommended Deployment Configurations
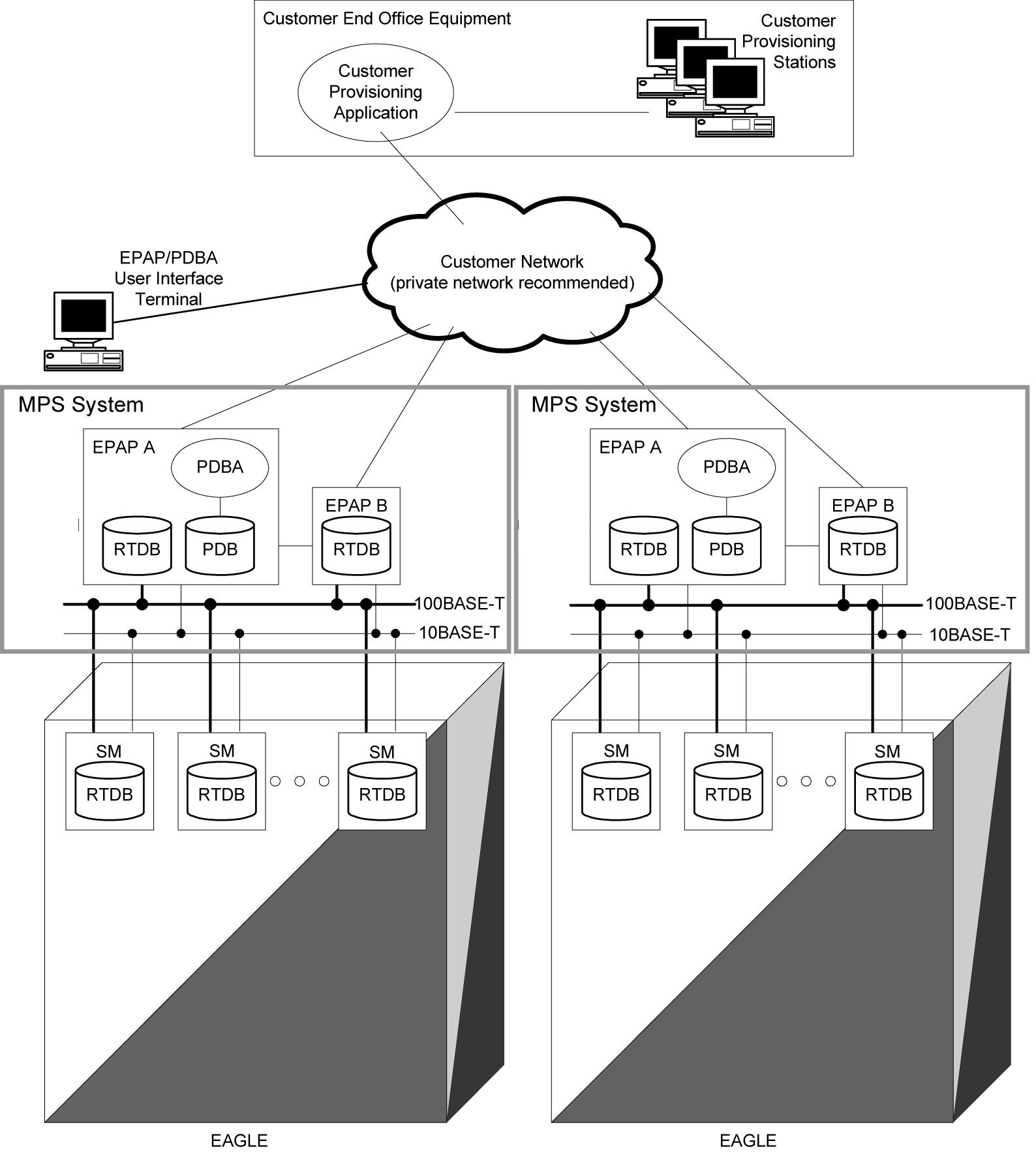
The EPAP is deployed in the central office of the carrier and service provider, co-located with the EAGLE STP. The customer network should be secured via firewall, and making the EPAP provisioning network its own private network or VLAN is further recommended where possible. For a generic model of the deployment strategy, see Figure 2-1.
Figure 2-1 Generic EPAP Deployment Model
In addition to the firewalls, the EPAP system provides additional security capabilities that include application-specific remote IP address control.
2.4 EPAP SSL Certificate Security
Currently, EPAP uses self-signed SSL certificates. You can install an X.509 certificate for a provisionable or backup provisionable interface with customized parameters, install an SSL certificate for a provisionable or backup provisionable interface from a trusted Certificate Authority (CA), install an SSL certificate for a Virtual IP (VIP) with customized parameters, and install an SSL certificate for a Virtual IP (VIP) from a trusted Certificate Authority (CA). For more information, see the following procedures:
- Installing an SSL Certificate For a Provisionable Interface With Customized Parameters
- Installing an SSL Certificate For a Provisionable Interface From a Trusted Certificate Authority
- Installing an SSL Certificate For a Backup Provisionable Interface With Customized Parameters
- Installing an SSL Certificate For a Backup Provisionable Interface From a Trusted Certificate Authority
- Installing an SSL Certificate For a VIP With Customized Parameters
- Installing an SSL Certificate For a VIP From a Trusted Certificate Authority
These procedures are devised to be executed on the EPAP 16.2 system deployed on TPD 7.4, on E5-APP-B-01/02 hardware.
2.5 Root User Is Disabled for SSH Login
The root user can log in through the serial interface for installation of the application. The root user will not have the permission to log in as an SSH user.
To login as an SSH user, the user admusr is provided. The admusr can run all commands, and when root permissions are required sudo can be used along with admusr.