File Server Patterns for Allowlisting
By default, File Server provides a high level of security by authenticating all access using either user logins or a public key. You can supplement this security by configuring an allowlist for File Server.
When you use the File Server allowlist, the following patterns are available for access requests that go to File Server.
| Pattern | Description |
|---|---|
|
This pattern is the only option for access requests that originate outside Oracle Cloud. |
|
|
By default, access requests that originate within the Oracle Cloud go through the Service Gateway. Your organization must add the CIDR block for the Service Gateway to the File Server allowlist. |
|
|
If your organization doesn't want to add the CIDR block for the Service Gateway to the File Server allowlist, you can bring your own load balancer, create a NAT gateway, and add the NAT gateway's IP address to the allowlist instead. |
Note:
The File Server allowlist is separate from the Oracle Integration allowlist. See Create an Allowlist for Public IP Addresses.Pattern 1. Requests from Outside Oracle Cloud
All File Server access requests that come from outside Oracle Cloud must be from IP addresses that are identified on the File Server allowlist.
To configure this pattern, update the self-service File Server allowlist so that it contains the IP address of all clients that much access File Server. See Create an Allowlist for Public IP Addresses.
Pattern 2. Oracle Cloud Requests Through the Service Gateway
By default, all File Server access requests that come from Oracle Cloud are routed through the service gateway. Therefore, the File Server allowlist must grant access to the service gateway's CIDR block.
To configure this pattern, update the self-service File Server allowlist so that it contains the CIDR block for the service gateway: 240.0.0.0/4. See Create an Allowlist for Public IP Addresses.
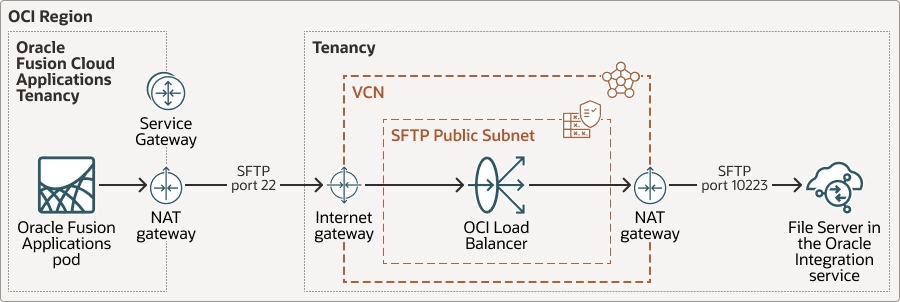
Pattern 3. Oracle Cloud Requests Through a NAT Gateway
Some organizations don't want to add the CIDR block for the service gateway to the File Server allowlist. In such cases, you can bring your own load balancer and route access requests for File Server through a NAT gateway.
Then, instead of adding the CIDR block for the service gateway to the File Server allowlist, you add the IP address for the NAT gateway. The File Server allowlist verifies that the request is from the NAT gateway's IP address.
Note:
-
The diagram shows traffic originating from an Oracle Fusion Cloud Applications tenancy, but traffic could also originate from another source. For example, a private subnet.
-
The File Server allowlist includes the IP address for the NAT gateway on the VCN.
How Requests Are Routed
Requests go through a load balancer and NAT gateway and then on to File Server.
-
The access request goes through a NAT gateway from the client, which could be a Oracle Fusion Cloud Applications tenancy or a private subnet.
This diagram shows the NAT gateway routing the request through SFTP port 22 to an internet gateway, but you can use an alternate port.
-
The internet gateway routes the access request to a load balancer that you set up in your virtual cloud network (VCN). The load balancer contains an SFTP TCP listener.
-
The load balancer sends the request through a NAT gateway on the VCN.
-
The NAT gateway routes the request through SFTP port 10223 to the allowlist for File Server.
-
If the allowlist includes the IP address for the NAT gateway that is on the VCN, the allowlist grants access.
Configure This Pattern
To route requests through a NAT gateway, complete the following tasks.
| Task | More information |
|---|---|
|
1. Configure a VCN |
If your organization doesn't have a virtual cloud network (VCN), configure one. See Creating a VCN in Oracle Cloud Infrastructure Documentation. |
|
2. Configure a NAT gateway |
If the VCN doesn't already have a NAT gateway, configure one. See Configure NAT gateway for private compute instances. |
|
3. Configure a subnet |
Create a public subnet in the VCN. See Creating a Subnet in Oracle Cloud Infrastructure Documentation. |
|
4. Configure the route rules for the VCN |
Configure rules that perform the following tasks:
See VCN Route Tables in Oracle Cloud Infrastructure Documentation. |
|
5. Set up a load balancer |
Create a load balancer, and perform the following configuration steps:
|
|
6. Create a security list for the subnet |
For the public subnet, add an ingress rule that allows inbound traffic from the client through the port of your choice, such as port 22. |
|
7. Update your allowlist |
Update the allowlist for File Server by adding the IP address for the NAT gateway on the VCN. See Create an Allowlist for Public IP Addresses. |