- Installing and Configuring Oracle WebCenter Sites
- Configuring WebCenter Sites Components
- Switching to External Authentication
12 Switching to External Authentication
For maximum security in production environments, Oracle recommends integrating Oracle WebCenter Sites with Oracle Access Management, for an advanced identity management solution and a seamless single sign-on user experience. You also have the option of integrating WebCenter Sites with an external LDAP authentication provider directory.
The following topics describe how to configure WebCenter Sites for authentication against either external identity management solution:
Switching to Authentication Against an LDAP Directory
This topic describes how to switch WebCenter Sites to authentication against an external LDAP authentication provider directory. This is a recommended solution for production environments if integration with Oracle Access Management is not viable.
- (Optional) Modify
ldap.caseAwareproperty value totrue, if the LDAP server you are using is case sensitive.By default the value ofldap.caseAwareis set tofalse. Sign in will fail if you are using a case-sensitive LDAP server and this property is set tofalse. To modify theldap.caseAwarevalue toTruefollow the steps:-
Sign in to the WebCenter Sites Admin interface and navigate to
Admin treetab>System Tools>Property Managementoption. -
Search for
ldapand change the value fromFalsetoTrue. -
Restart the Managed server.
Note:
During the integration of Sites with LDAP, if the users data in LDAP is separated by a comma the data does not get fetched. for example:test,user. To retrieve the data, you need to change the syntax in thedir.inifile located at..sites/installdirectory from"syntax.escape=\\ tosyntax.escape=\#". -
- Access the LDAP Configurator at
http://sites-host:sites-port/sites-context/ldapconfig, follow the instructions on the screen, and enter the values for your environment. - For LDAP rollback, restart the WebCenter Sites Managed Server, and go to the same LDAP Configurator URL.
Now there is only manual LDAP integration. Nothing is written to your LDAP Server, only an LDIF file is created under the
DOMAIN_HOME/wcsites/wcsites/config/ldapfolder (This is the default install location of WebCenter Sites application. All customizations and path modifications should be made after successful LDAP integration). Thepeopleparent,groupparent,username, and other fields are not prepopulated, as in the previous release. - (Optional) Modify the
LDIFfile located inNEW_DOMAIN_HOME/wcsites/wcsites/config/with values appropriate for your environment.Because the fields are not prepopulated, follow this example for
ORACLEDIR:ldap server type -- ORACLEDIR ldap DSN -- dc=oracle,dc=com ldap host -- localhost ldap port -- 389 ldap username -- cn=orcladmin ldap password -- password ldap peopleParent -- cn=Users,dc=oracle,dc=com ldap groupparent -- cn=Groups,dc=oracle,dc=com - If you choose Oracle Virtual Directory as your LDAP authentication provider, WebCenter Sites generates an
LDIFfile, which you can import to your Oracle Internet Directory server and then create an adaptar in Oracle Virtual Directory to connect to the Oracle Internet Directory server.You cannot import an LDIF file directly to an Oracle Virtual Directory LDAP server because it does not have a storage of its own.
- Import the
LDIFfile into the external LDAP authentication provider. - Restart the WebLogic Managed Server running this WebCenter Sites instance.
Switching to Authentication Against Oracle Access Manager
You can configureWebCenter Sites for authentication against Oracle Access Manager. This solution is recommended for production environments.
oamconsole and some configuration changes in the Sites.
- Sign in to Oracle Access Manager Server through
oamconsole, for example:http://<oam_host:oam_port>/<oam console>/and configure a WebGate. - Deploy the
oamlogin.warandoamtoken.warapplication files located underNEW_ORACLE_HOME/wcsites/webcentersites/sites-homeon the WebLogic domain containing the targetWebCenter Sites instance. - Create the
wemsites_settings.propertiesproperty file underDOMAIN_HOME/wcsites/wcsites/config/. - Enter the values in the
wemsites_settings.propertiesfile as follows:Elements Properties oamredirecthttp://oam_server_host:oam_port/oam/server/auth_cred_submitoamlogoutoamlogout=http://oam_server_host:oam_port/oam/server/logoutforgotpasswordhelpdesk-email-address - Set the following properties in
NEW_DOMAIN_HOME/wcsites/wcsites/config/SSOConfig.xml. See Step 12 of Integration Steps.Elements Properties serviceUrlhttp://{ohs_server_host}:{ohs_port}/{sites_context_root}/RESTticketUrlhttp://{oamtoken_server_host}:{oamtoken_port}/oamtokensignoutURL
Use this URL when invokingWebCenter Sites logout. It includes the encoded URL where the browser will return after all logout processing has been completed by Oracle Access Manager.http://{oam_server_host}:{oam_port}/oam/server/logout?end_url={end_url}end_urlFor test (staging) and production (delivery) environments:
http%3A%2F%2F{ohs_server_host}%3A{ohs_port}%2F{sites_context_root}%2Fwem%2Ffatwire%2Fwem%2FWelcomedbUsernameName of theWebCenter Sites general Administrator user account. dbPasswordPassword for the WebCenter Sites general Administrator user account. Note:
The
ohs_serverhost andohs_portcan be WebLogic host and port or any other HTTP server host and port depending on your configuration. For more information on OHS configuration, see Step 2 to Step 9 of Integration Steps. Add the below example for configuration inOAM OHS,mod_wl_ohs.conffile.<IfModule weblogic_module> <Location /oamlogin> SetHandler weblogic-handler WebLogicHost SITES_HOST WebLogicPort SITES_PORT </Location> </IfModule> <IfModule weblogic_module> <Location /sites> SetHandler weblogic-handler WebLogicHost SITES_HOST WebLogicPort SITES_PORT </Location> </IfModule> - Copy the
obAccsessClient.xmlandcwallet.ssofiles from your Oracle Access Manager instance into theNEW_DOMAIN_HOME/wcsites/wcsites/config/oblix/lib/directory on the targetWebCenter Sites instance.Note:
These files are auto-generated after the WebGate is configured. - Edit the
oamtoken.xmlfile in thesites-configdirectory by setting the compatibility mode andoblixpath. The compatibility mode should be set to11gand theoblixpath to thesites-configfolder under which you have theoblix/libfolder. - In the Oracle Access Manager configuration for WebCenter Sites, update the protected, public, and excluded resources as follows:
Figure 12-1 List of Protected, Public, and Excluded Resources for WebCenter Sites
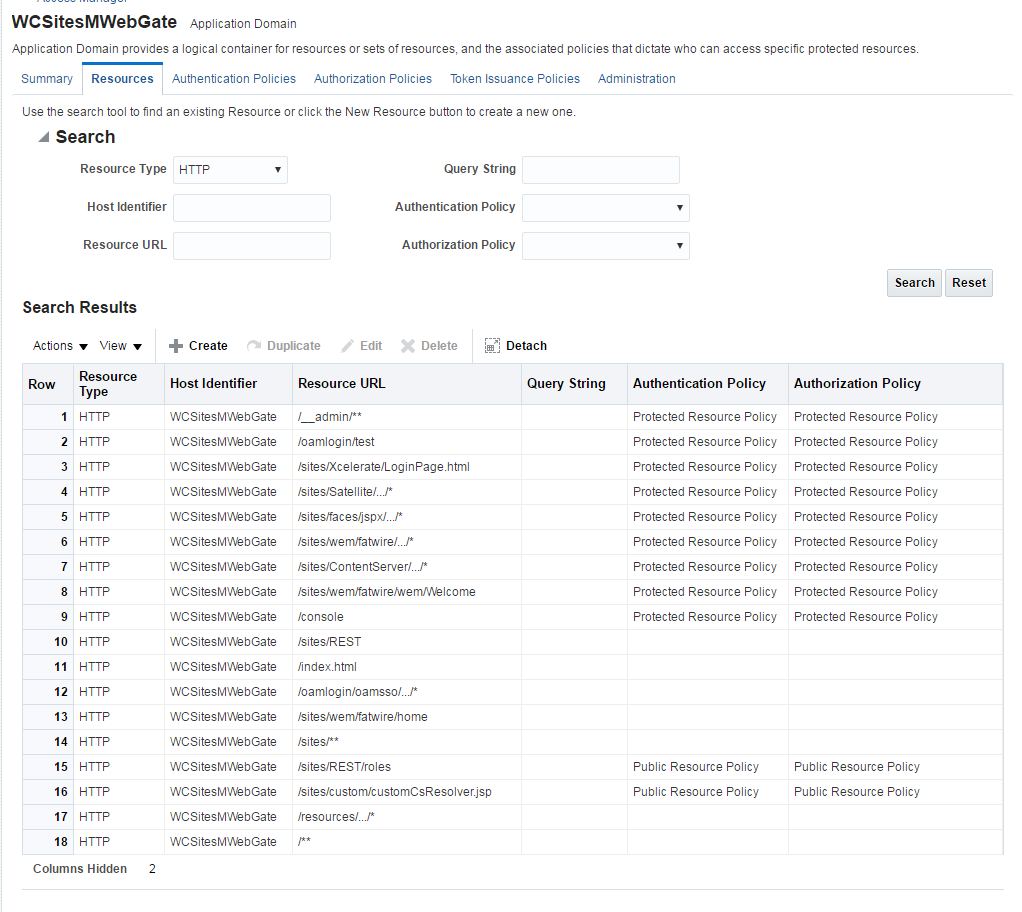
Description of "Figure 12-1 List of Protected, Public, and Excluded Resources for WebCenter Sites" - To integrate the OAMSDK Client with
WebLogic Server as the
oamtoken.warapplication, edit thejps-config.xmlfile for the WebCenter Sites domain. By default, the WebLogic domain runs with this file, which is part of the WebLogic Server startup script:-Doracle.security.jps.config=NEW_ORACLE_HOME/user_projects/domains/DOMAIN_NAME/config/fmwconfig/jps-config.xml- Add a service instance, as the following example shows, next to existing service instances in the existing
jsp-config.xmlfile:<serviceInstance name="credstore.oamtoken" provider="credstoressp" location="./oamtoken"><description>File Based Credential Store Service Instance</description><property name="location" value="./oamtoken"/></serviceInstance>locationis the path to the directory that contains thecwallet.ssofile. The preceding example sets this path with reference to the currentjsp-config.xmlfile. Make sure theomtokenfolder is created with respect to the current directory and thecwallet.ssofile is placed there. Thelocationvalue can also be an absolute path to where thecwallet.ssofile is placed - Add
<serviceInstanceRef ref="credstore.oamtoken"/>under<jpsContext name="default">. - Add following
<jpsContext>element under<jpsContexts default="default">:<jpsContext name="OAMASDK"><serviceInstanceRef ref="credstore.oamtoken"/></jpsContext>
- Add a service instance, as the following example shows, next to existing service instances in the existing
- Add permissions so that code in
oamtoken.warcan be used.The WebGate instance created in Oracle Access Manager is accessed by the client. You need to add the credential to the WebCenter Sites domain so that the security restriction can be taken care of.- Launch the WebLogic Scripting Tool with the
wlst.shscript:cd NEW_ORACLE_HOME/oracle_common/common/bin/./wlst.sh - Connect to the Administration Server for the WebCenter Sites domain:
connect('user-name','password','sites-host:admin-port') - Grant the permissions:
grantPermission(codeBaseURL="file:/scratch/idc/newoam/rend/Oracle_Home/user_projects/domains/renddomain/servers/wcsites_server1/tmp/_WL_user/oamtoken/-",permClass="oracle.security.jps.service.credstore.CredentialAccessPermission",permTarget="context=SYSTEM,mapName=OAMAgent,keyName=*",permActions="*")The preceding path is basically the path where WebLogic Server has deployed theoamtoken.warapplication. - Restart the target WebCenter Sites Managed Server.
- Launch the WebLogic Scripting Tool with the
- (Optional) If trust betweenWebCenter Sites and Oracle Access Manager has not been established, modify the configuration of theWebCenter Sites web tier as follows:
- Sign in to the Oracle Access Manager Console.
- In the WebGate authorization policy (under the protected resource policy), go to the Responses tab.
- Enable (select) the Identity Assertion check box.
- Click Apply to save your changes.
- (Optional) If WebCenter Sites is deployed on a cluster is using OAM Integration. Following steps are required to be replicated on
oamticketcachecache.- In the config directory, we have
cas-cache.xmlwhere oamticketcache is configured by default. - Uncomment the commented section in the cache named
oamticketcachethe section appear as:<cacheEventListenerFactory class="net.sf.ehcache.distribution.RMICacheReplicatorFactory" properties="replicateAsynchronously=true, replicatePuts=true, replicateUpdates=true, replicateUpdatesViaCopy=false, replicateRemovals=true"/> <bootstrapCacheLoaderFactory class="net.sf.ehcache.distribution.RMIBootstrapCacheLoaderFactory" properties="bootstrapAsynchronously=false, maximumChunkSizeBytes=5000000" propertySeparator="," /> - Change the
cacheManagerPeerProviderFactoryas follows, make sure port is unique.<cacheManagerPeerProviderFactory class="net.sf.ehcache.distribution.RMICacheManagerPeerProviderFactory" properties="peerDiscovery=automatic, multicastGroupAddress=230.0.0.8, multicastGroupPort=40002, timeToLive=1" /> - The port should be different for
cacheManagerPeerProviderFactoryandcacheManagerPeerListenerFactoryas specified in the earlier steps. - All the cluster nodes should have same port for both the properties.
- In the config directory, we have
- For working on the
SSOConfig.xmlfile, follow the steps:- Modify the
SSOConfig.xmlfile of theWebCenter Sites deployment. This file controls the loaded authentication classes and the properties that are required by those classes. - Shutdown the Sites server.
- Backup the
SSOConfig.xmlfile located in theWEB-INF/classesdirectory of the deployed WebCenter Sites application.For example:/u01/software/Apps/OraMiddleware/user_projects/domains/OAMSitesDomain/wcsites/wcsites/config/SSOConfig.xml. - Modify
SSOConfig.xmlas follows:Note:
Further steps explains on setting properties for the following:serviceUrl,ticketUrl,signoutURL,dbUsername, anddbPassword. See Step 5. - The
signoutUrlproperty specifies the URL to be used when invoking WebCenter Sites logout. It includes the encoded URL where the browser will return after all logout processing has been completed by OAM. - For Sites management, use the following value for end_url: http%3A%2F%2F{ohs_server_host}%3A{ohs_port}%2F{sites_context_root}%2Fwem%2Ffatwire%2Fwem%2FWelcome
- For Sites delivery, use the following value for end_url: http%3A%2F%2F{ohs_server_host}%3A{ohs_port}%2F{sites_context_root}%2Fwem%2Ffatwire%2Fwem%2FWelcomeFor the
dbUsernameanddbPasswordproperties, you can enter the credentials of the WebCenter Sites general administrator, which by default is fwadmin/xceladmin. The values for these properties will be encrypted on startup of the WebCenter Sites application.Note:
In the code example below, you will set the following properties:
csServerUrl,serviceUrl,ticketUrl,signoutURL,dbUsername,dbPassword. See Step 5.<?xml version="1.0" encoding="UTF-8"?> <beans xmlns="http://www.springframework.org/schema/beans" xmlns:xsi="http://www.w3.org/2001/XMLSchema-instance" xmlns:context="http://www.springframework.org/schema/context" xsi:schemaLocation="http://www.springframework.org/schema/beans http://www.springframework.org/schema/beans/spring-beans-2.5.xsd http://www.springframework.org/schema/context http://www.springframework.org/schema/context/spring-context-2.5.xsd"> <!-- Single Sign On provider --> <bean id="ssoprovider" class="com.fatwire.wem.sso.oam.OAMProvider"> <property name="config" ref="ssoconfig" /> </bean> <!-- OAM IdentityResolver bean --> <bean id="oamIdentity" class="com.fatwire.auth.identity.RemoteUsernameResolver id="oamIdentity"> <property="csServerUrl" value="http://<sites_server_host>:<sites_port>/<sites_context_root>/custom/customCsResolver.jsp </bean> <!-- Single Sign On filter --> <bean id="ssofilter" class="com.fatwire.wem.sso.oam.filter.OAMFilter"> <property name="config" ref="ssoconfig" /> <property name="provider" ref="ssoprovider" /> <property name="identityResolver" ref="oamIdentity" /> <property name="trustConfigured" value="false" /> </bean> <!-- Single Sign On listener --> <bean id="ssolistener" class="com.fatwire.wem.sso.oam.listener.OAMListener"> </bean> <!-- Single Sign On configuration --> <bean id="ssoconfig" class="com.fatwire.wem.sso.oam.conf.OAMConfig"> <!-- URL prefix for REST service endpoint --> <property name="serviceUrl" value="http://{ohs_server_host}:{ohs_port}/{sites_context_root}/REST" /> <!-- URL prefix for Token Service servlet --> <property name="ticketUrl" value="http://{oamtoken_server_host}:{oamtoken_port}/oamtoken" /> <!-- URL to be called when WEM logout is required. --> <property name="signoutUrl" value="http://{oam_server_host}:{oam_port}/oam/server/logout?end_url=http%3A%2F%2F{ohs_server_host}%3A{ohs_port}%2F{sites_context_root}%2Fwem%2Ffatwire%2Fwem%2FWelcome" /> <!-- Proxy tickets, tt's the last server in the call chain --> <property name="proxyTickets" value="true" /> <!-- Your application protected resources (relative to applicationUrl) --> <property name="protectedMappingIncludes"> <list> </list> </property> <property name="protectedMappingStatelessIncludes"> <list> <value>/REST/**</value> </list> </property> <!-- Your application protected resources excludes (relative to applicationUrl) --> <property name="protectedMappingExcludes"> <list> </list> </property> </bean> </beans>
- Modify the
Integrating SiteCapture with OAM
This topics covers steps to integrate SiteCapture with OAM.
- Integrate Oracle WebCenter Sites with Oracle Access Manager. For more information see, Integrating OAM with Oracle WebCenter Sites.
- Additional configuration required for Oracle Access Manager for
SiteCapture.
- Create additional resource definitions (see table below) for the
WebCenter Sites application domain.
Resource URL Protection level Authentication Authorization /<sites-context>/REST/rolesUnprotected
Public
All Allowed
/<sites-context>/custom/customCsResolver.jspUnprotected
Public
All Allowed
/resources/.../*Excluded
NA
NA
/__admin/.../*Protected
Protected
Protected
- Configure the Protected Resource Policy as follows:
- Click Application Domains and click the Open icon.
- Click Search and select WCSitesWebGate.
- Click the Authentication Policies tab and select Authentication Policies . For Authentication Scheme, select LDAPWemScheme, the authentication scheme previously created.
- Click Responses tab.
- Select the Identity Assertion checkbox.
- When an Authentication policy is satisfied, it can create responses. The responses are required by the WebCenter Sites HTTP filter to recognize LDAP attributes and provide information about the authenticated user. In the following steps, you will create these responses.
- Click the Add (+) icon. and enter the following:
- For Name: Enter FATGATE_CSTIMEOUT
- For Type: Select Header
- For Value: Enter 30
- Create additional resource definitions (see table below) for the
WebCenter Sites application domain.
- SiteCapture Application Installation. During installation process of
SiteCapture use parameters that are mentioned below:
Property Description Property Value Content server host name or IP fw.cs.hostname
{ohs_host}
Content server app server port fw.cs.port
{ohs_port}
Content server context fw.cs.context
{sites_context_root}
Content server protocol (http or https) fw.cs.protocol
{sites.protocol}
Content Server user name having RESTADMIN role
fw.cs.username
{username}
Content server user password
fw.cs.password
{password}
SiteCapture server hostname or IP
fw.sc.hostname
{sc_host}
SiteCapture app server port
fw.sc.port
{sc_port}
SiteCapture protocol (http or https)
fw.sc.protocol
{sc.protocol}
CAS server hostname
fw.cas.host
{ohs_host} in installer. Or
Empty in sitecapture.properties
CAS server port
fw.cas.port
{ohs_port} in installer. Or
Empty in sitecapture.properties
CAS server context
fw.cas.context
cas in installer. Or
Empty in sitecapture.properties
- Adjust the
root-context.xmlfile in SiteCapture Application. SiteCapture shipped with two files:root-context.xmlBackuproot-context.xmlfile and rename toroot-context.xml.bakfile.oam_root-context.xmlRenameoam_root-context.xmlfile toroot-context.xmlfile.<?xml version="1.0" encoding="UTF-8"?> <beans xmlns="http://www.springframework.org/schema/beans" xmlns:xsi="http://www.w3.org/2001/XMLSchema-instance" xmlns:jdbc="http://www.springframework.org/schema/jdbc" xmlns:p="http://www.springframework.org/schema/p" xmlns:context="http://www.springframework.org/schema/context" xsi:schemaLocation="http://www.springframework.org/schema/beans http://www.springframework.org/schema/beans/spring-beans-3.1.xsd http://www.springframework.org/schema/jdbc http://www.springframework.org/schema/jdbc/spring-jdbc-3.1.xsd http://www.springframework.org/schema/context http://www.springframework.org/schema/context/spring-context-3.1.xsd"> <bean id="propertyConfigurer" class="org.springframework.beans.factory.config.PropertyPlaceholderConfigurer" /> <!-- Root Context: defines shared resources visible to all other web components --> <jdbc:initialize-database data-source="dataSource" enabled="true" ignore-failures="ALL"> <!-- For installer the first jdbc:script will opened. Installer will configure it automatically --> <jdbc:script location="classpath:crawler_oracle_db.sql" /> <!--jdbc:script location="classpath:crawler_hsql_db.sql" /--> <!--jdbc:script location="classpath:crawler_sql_server_db.sql" /--> <!--jdbc:script location="classpath:crawler_oracle_db.sql" /--> <!--jdbc:script location="classpath:crawler_db2_db.sql" /--> </jdbc:initialize-database> <!-- Section# 1 Installer will consume below configuration to configure a datasource name created on the appservers --> <bean id="dataSource" class="org.springframework.jndi.JndiObjectFactoryBean"> <property name="jndiName" value="wcsitesDS"/> </bean> <!-- Single Sign On provider --> <bean id="ssoprovider" class="com.fatwire.wem.sso.oam.OAMProvider"> <property name="config" ref="ssoconfig" /> </bean> <!--It is invoked by the OAM filter to resolve an OAM authenticated user against a remote Site CS instance.--> <bean id="oamIdentity" class="com.fatwire.auth.identity.RemoteUsernameResolver" > <property name="csServerUrl" value="http://{ohs_server_host}:{ohs_port}/{sites_context_root}/custom/customCsResolver.jsp"/> </bean> <!-- Single Sign On filter --> <bean id="ssofilter" class="com.fatwire.wem.sso.oam.filter.OAMFilter"> <property name="config" ref="ssoconfig" /> <property name="provider" ref="ssoprovider" /> <property name="identityResolver" ref="oamIdentity" /> <!-- Set "trustConfigured" to "true" in case of trust relationship configured between WebGate and WLS. It will turn off check for OAM_ASSERTION header. --> <property name="trustConfigured" value="false" /> </bean> <!-- Single Sign On listener --> <bean id="ssolistener" class="com.fatwire.wem.sso.oam.listener.OAMListener"> </bean> <!-- Single Sign On configuration --> <bean id="ssoconfig" class="com.fatwire.wem.sso.oam.conf.OAMConfig"> <!-- URL prefix for REST service endpoint --> <property name="serviceUrl" value="http://{ohs_server_host}:{ohs_port}/{sites_context_root}/REST" /> <!-- URL prefix for Token Service servlet --> <property name="ticketUrl" value="http://{oamtoken_server_host}:{oamtoken_port}/oamtoken" /> <!-- URL to be called when WEM logout is required. --> <property name="signoutUrl" value="http://{oam_server_host}:{oam_port}/oam/server/logout?end_url=http%3A%2F%2F{ohs_server_host}%3A{ohs_port}%2F{sites_context_root}%2Fwem%2Ffatwire%2Fwem%2FWelcome"/> <!-- Do not proxy tickets, tt's the last server in thecall chain --> <property name="proxyTickets" value="false" /> <!-- Database Credentials needed by user lookup inOAMFilter --> <property name="dbUsername" value="fwadmin" /> <property name="dbPassword" value="xceladmin"/> <!-- Your application protected resources (relative to applicationUrl) --> <property name="protectedMappingIncludes"> <list> <value>/__admin</value> <value>/__admin/**</value> </list> </property> <!-- Your application protected resources excludes (relative to applicationUrl) --> <property name="protectedMappingExcludes"> <list> <value>/__admin/layout</value> </list> </property> <property name="applicationProxyCallbackPath" value="/sso/proxycallback" /> <property name="gateway" value="false" /> </bean> <context:component-scan base-package="com.fatwire.crawler.remote.dao" /> <context:component-scan base-package="com.fatwire.crawler.remote.support" /> <context:component-scan base-package="com.fatwire.crawler.remote.di" /> <context:component-scan base-package="com.fatwire.crawler.remote.resources.support" /> </beans>Note:
To updatemod_wl_ohs.conffile the following code has to be included:<IfModule weblogic_module> <Location /__admin> SetHandler weblogic-handler WebLogicHost SITECAPTURE_HOST WebLogicPort SITECAPTURE_HOST </Location> </IfModule>
Integrating OAM with Oracle WebCenter Sites: Satellite Server
This topics covers steps to integrate OAM with Oracle WebCenter Sites: Satellite Server.
Note:
The code example below gives the RSS configuration inOAM OHS, and mod_wl_ohs.conf file.<IfModule weblogic_module>
<Location /ss>
SetHandler weblogic-handler
WebLogicHost SATELLITESERVER_HOST
WebLogicPort SATELLITESERVER_HOST
</Location>
</IfModule>Integrating OAM with Visitor Services
This topic covers steps to integrate OAM with Visitor Services.
Note:
The code example below gives the Visitor configuration inOAM OHS, and mod_wl_ohs.conf file.<IfModule weblogic_module>
<Location /oamlogin>
SetHandler weblogic-handler
WebLogicHost SITES_HOST
WebLogicPort SITES_PORT
</Location>
</IfModule>
<IfModule weblogic_module>
<Location /visitors-webapp>
SetHandler weblogic-handler
WebLogicHost VISITORSERVICES_HOST
WebLogicPort VISITORSERVICES_HOST
</Location>
</IfModule>Switching to Authentication OAM Using Detached Credential Collector
This topic will show the steps to configure the two webgates and two OHS. You can configure Site Capture, Satellite Server, and Visitor Services to OAM in the similar using the steps in this topic.
Prerequisites
This chapter lists the prerequisites required for configuring the Detached Credential Collector.
- WebCenter Sites 14.1.2.0.0 is installed with CAS and is in working condition.
- OAM
11.1.2.3.0is installed and OAM domain is configured along with two OHS configured for webgate. The list below are required softwares for this installation:-
OAM
11.1.2.3.0. For example :ofm_iam_generic_11.1.2.3.0_disk*.zip. -
RCU
11.1.1.9.0. For example :ofm_rcu_linux_11.1.1.9.0_64_disk*.zip. -
Latest version of SOA suite.
-
WebTier
11.1.1.9.0. For example :ofm_webtier_linux_11.1.1.9.0_64_disk*.zip -
WebGate 11.1.2.3.0. For example :
ofm_webgates_generic_11.1.2.3.0_disk*.zip
-
DCC WebGate Configuration
This topic describes hot to configure DCC Webgate.
- Login to
oamconsole. The Launch Pad of Application Security opens. - Click Agents >Create Webgate. The Create Webgate form opens.
- In the Create Webgate form, enter the following values as given below:
- Version :
11g - Name :
DCC-11g-WG. For example, enter Some arbitrary name. - Host Identifier :
DCC-11g-WG. For example, enter Some arbitrary name. - Security : Select the option of your choice
- Auto Create Policies : Leave the default selected option.
- Version :
- Click Apply.
- A new webgate named DCC-11g-WG is created with default values. In the webgate form, update the following fields:
- Logout URL :
/oamsso-bin/logout.pl - Logout Callback URL :
/oam_logout_success - Logout Redirect URL :
http://{OAM_host:OAM_port}/oam/server/logout - Logout Target URL :
end_url - Allow Credential Collector Operations : Leave the default selected option.
- Logout URL :
- Click Apply.
- Navigate to Launch Pad and click on Access Manager>Host Identifiers.
- A Search form is displayed, click Search
- Click Host Identifier
DCC-11g-WGas created in Step 3c. - Add the Hostname and port by clicking on ‘+’ in Host Name Variations area.
- After entering all the details, click Apply.
Note:
These are the hostname and port of OHS to where DCC webgate files are copied to display the login challenge. - Navigate to Launch Pad and click Authentication Schemes.
- A Search form is displayed, click Create.
- Create a new Authentication theme that will be used by both the webgates as given in Step 15 a to g.
- Click Apply. Using Weblogic’s Embedded LDAP as LDAP authentication
module where
fwadminuser is added to myrealm using the WebLogic Remote Console.- Name : DCCAuthnScheme14c. For example, enter Some arbitrary name.
- Authentication Level : 2
- Challenge Method : FORM
- Challenge Redirect URL : http://{OHS_Host_of_Resource_Webgate:OHS_Port}
- Authentication Module : LDAP
- Challenge URL : /oamsso-bin/login.pl
- Context Type : external
- Navigate to Launch Pad and click Application Domains.
- A Search form is displayed, click Search, which should display all the application domains available that are created by default when a webgate is created.
- Click Application Domain (created in Step 3b), which should open the application domain with multiple tabs and Summary is opened by default.
- Click Resources tab, which will display search form along with Create button.
- Click Create, update the form as below:
Note:
Add other excluded URLS similar to below, with changing Resource URL with each Create.-
Type : HTTP
-
Host Identifier : DCC-11g-WG ( Name given in Step 3c)
-
Resource URL : /oamsso-bin/login.pl
-
Protection Level : excluded
-
- Click Apply.
- Click Authentication Policies tab and then click Protected Resource Policy. Update the form as below and click Apply.
-
Authentication Scheme : DCCAuthnScheme14c as created in Step 15.
-
- Copy the DCC webgate files as given below created in WebLogic domain ($DOMAIN_HOME/output/DCC-11g-WG) to the OHS folder ($OHS_INSTANCE_HOME/config/OHS/$OHS_NAME /webgate/config) hosting these webgate files.
-
ObAccessClient.xml
-
cwallet.sso
-
- Restart the OHS.
Resource WebGate Configuration
This topics provides steps to configure the Resource Webgate.
- Login to oamconsole, which should display Launch Pad of Application Security.
- Click Agents > create Webgate, which should display Create Webgateform.
- Input the values as below in the Create Webgate form.
- Version : 11g
- Name : Resource-11g-WG (Some arbitrary name)
- Host Identifier : Resource-11g-WG (Same as Name above or some arbitrary name)
- Security : Open (select the option of your choice)
- Auto Create Policies : Option Selected
- Click Apply
- A new webgate named Resoruce-11g-WG is created with default values. In the webgate form, update the following fields:
- Logout URL : /logout
- Logout Callback URL : /oam_logout_success
- Logout Redirect URL : http://{OAM_Host_of_DCC_Webgate:OAM_Port}/oamsso-bin/logout.pl
- Logout Target URL : end_url
- Click Apply
- Navigate to Launch Pad and click Access Manager> Host Identifiers, which should display a search form. Click Search.
- Click Host Identifier Resource-11g-WG as created in Step 3c.
- Add the hostname and port by clicking on ‘+’ in Host Name Variations.
- After all desired Host Name and Port are added then click Apply.
Note:
These are the hostname and port of OHS to where Resource webgate files are copied. - Navigate to Launch Pad and click Application Domains, which should display the Search form. Click Search, which should display all the application domains available that are created by default when a webgate is created.
- Click Application Domain as created in Step 3b, which should open the application domain with multiple tabs and Summary is opened by default.
- Click Resources tab, which will display search form along with Create button. Click Create for each row in below table, update the create form as below and click Apply.
Table 12-1 Resource Identifiers
Type Host Identifier Resource URL Protection Level Authentication Policy Authorization Policy HTTP
Resource-11g-WG
/{sites-context}/**
Protected
Protected Resource Policy
Protected Resource Policy
HTTP
Resource-11g-WG
/{sites-context}/ContentServer/* Protected
Protected Resource Policy
Protected Resource Policy
HTTP
Resource-11g-WG
/{sites-context}/Satellite/* Protected
Protected Resource Policy
Protected Resource Policy
HTTP
Resource-11g-WG
/{sites-context}/faces/jspx/…/* Protected
Protected Resource Policy
Protected Resource Policy
HTTP
Resource-11g-WG
/{sites-context}/wem/fatwire/…/* Protected
Protected Resource Policy
Protected Resource Policy
HTTP
Resource-11g-WG
/{sites-context}/Xcelerate/LoginPage.html Protected
Protected Resource Policy
Protected Resource Policy
- Click Authentication Policies tab and then click Protected Resource Policy. Update the form as below and click Apply.
-
Authentication Scheme : DCCAuthnScheme11g (Created in Step 8)
-
Click Responses tab and then select Identity Assertion. Click Add and include the following responses:
Table 12-2 Identity Assertion Elements
Type Name Value Header
FATGATE_POLICY
Protected
Header
FATGATE_EMAIL
$user.attr.mail
-
- Click Authorization Policies tab and then click Protected Resource Policy. Update the form as given in the table below.
-
Click Responses and then select Identity Assertion.
Table 12-3 Identity Assertion Elements
Type Name Value Header
FATGATE_POLICY
Protected
Header
FATGATE_EMAIL
$user.attr.mail
-
After adding the above responses, click Add
-
Click Apply.
-
- Click Resources tab, which will display search form along with Create button. Click Create for each row in below table, update the create form as below and click Apply.
- Copy the Resource webgate files as given below that's created in WebLogic domain ($DOMAIN_HOME/output/Resource-11g-WG) to the OHS folder ($OHS_INSTANCE_HOME/config/OHS/$OHS_NAME /webgate/config hosting these webgate files.
- ObAccessClient.xml
- cwallet.sso
- Restart OHS.
Sites OAM Integration
This topic provides steps to configure the Sites OAM integration with DCC
- Deploy oamtoken web application to sites server.
Note:
Do not deploy oamlogin web application since it is not used. - Undeploy cas web application from the sites server.
- Navigate to CS web application and open SSOConfig.xml in edit mode.
- Add the following bean to the file and Save the file.
<!-- Single Sign On configuration --> <bean id="ssoconfig" class="com.fatwire.wem.sso.oam.conf.OAMConfig"> <!-- URL prefix for REST service endpoint --> <property name="serviceUrl" value="http://{OHS_Host_of_Resource_Webgate:OHS_Port}/{sites-context}/REST" /> <!-- URL prefix for Token Service servlet --> <property name="ticketUrl" value="http://{Sites_Host:Sites_Port}/oamtoken" /> <!-- URL to be called when WEM logout is required. --> <property name="signoutUrl" value="http:// {OHS_Host_of_DCC_Webgate:OHS_Port }/oamsso-bin/logout.pl?end_url=http%3A%2F%2F{OHS_Host_of_Resource_Webgate} %3A{OHS_Port }%2F{sites-context}%2Fwem%2Ffatwire%2Fwem%2FWelcome" /> <!-- Do not proxy tickets, tt's the last server in the call chain --> <property name="proxyTickets" value="false" /> <!-- Database Credentials needed by user lookup in OAMFilter --> <property name="dbUsername" value="fwadmin" /> <property name="dbPassword" value="{password_for_above_user}" /> <!-- Your application protected resources (relative to applicationUrl) --> <property name="protectedMappingIncludes"> <list> <value>wem/fatwire/**value>wem/fatwire/**> <value>/faces/jspx/**value>/faces/jspx/**> <value>/ContentServer?[pagename=OpenMarket/Xcelerate/UIFramework/LoginPage|OpenMarket/Xcelerate/UIFramework/ShowMainFrames|fatwire/getAllUserGroups|fatwire/getAllSecurityConfigs|rest/asset,# </value> <value><Satellite?[pagename=fatwire/insitetemplating/request|OpenMarket/Xcelerate/ControlPanel/Request|OpenMarket/Xcelerate/ControlPanel/EditPanel|fatwire/wem/ui/Ping|fatwire/wem/sso/validateMultiticket|OpenMarket/Xcelerate/UIFramework/ShowPreviewFrames,#] </value> <value>Xcelerate/LoginPage.html</value> - Restart Sites server after the above changes.
- Use a protected URL from the resource webgate to login to Sites. For example :
http://{OHS_Host_of_Resource_Webgate:OHS_Port}/{sites-context}/.Note:
Site Capture, Satellite Server and Visitor Services can be configured to the OAM in the same way.