5 SEAS Over IP Configuration Procedures
Chapter 5, SEAS Over IP Configuration Procedures, describes the procedures used to configure the SEAS over IP feature.
5.1 Introduction
The SEAS over IP feature is a TCP/IP-based interface for SEAS that creates a path between the EAGLE and the CCS MR (Common Channel Signaling Message Router). The CCS MR is a stand-alone, self-contained system developed by Telcordia that provides a centralized mechanism for routing CCS network operations traffic between STPs/SCPs and existing and new OSs.
One of the eight telnet terminals on the E5-IPSM is used to provide the connection from the EAGLE and the CCS MR. This terminal is referred to as a SEAS terminal.
Note:
As of Release 46.5, the E5-IPSM card and its functionality is replaced by the E5-ENET-B (p/n 870-2971-01) or SLIC (p/n 7094646) card. Any references to E5-IPSM and the 870-2877-01 part number should be replaced by the 46.5 and greater card and part number.The EAGLE can contain a maximum of two SEAS terminals. Only one SEAS terminal can be assigned to an E5-IPSM. The remaining seven telnet terminals on the E5-IPSM continue to provide generic IP-based services such as Telnet and FTP.
SEAS over IP Feature Configurations
The SEAS over IP feature supports three configurations"
- Dual SEAS terminals with a single CCS MR
- Dual SEAS terminals with dual CCS MRs
- One SEAS terminal with one CCS MR.
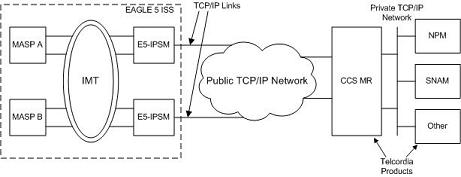
Dual SEAS Terminals with a Single CCS MR SEAS Configuration
The two SEAS terminals are connected to a single CCS MR as shown in Figure 5-1. The two SEAS terminals operate in a redundant fashion allowing a maximum of two active connections to the CCS MR. While the connection to the CCS MR is dedicated to SEAS, the other terminals on the E5-IPSM may still be used for other IP-based operations, such as Telnet and FTP, or their secure counterparts, SSH and SFTP. Different SEAS information can be transmitted and received separately over each connection to the CCS MR.
Figure 5-1 Dual SEAS Terminals with Single CCS MR SEAS Configuration
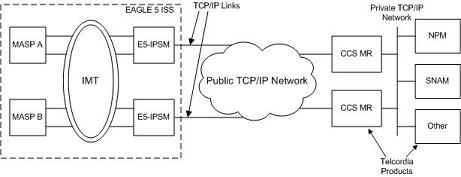
Dual SEAS Terminals with Dual CCS MRs SEAS Configuration
When the two SEAS terminals are connected to two CCS MRs, as shown in Figure 5-2, the operation of the SEAS connections is similar to the "Dual SEAS Terminals with a Single CCS MR SEAS Configuration" section with the following exceptions:
- Each SEAS terminal is configured with a connection to one of the CCS MRs.
- The pair of CCS MRs operate in a round robin manner if they each have an active connection to a SEAS terminal. When the EAGLE receives a command request from a CCS MR, the response to the command request is sent to the CCS MR on the same TCP connection that the CCS MR used to send the command request.
Figure 5-2 Dual SEAS Terminals with Dual CCS MRs SEAS Configuration
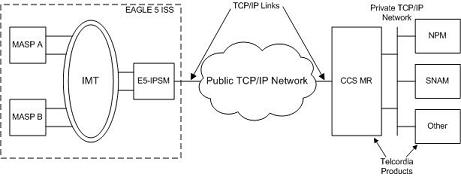
Simplex SEAS Terminal Operation
With the simplex SEAS terminal operation, there is only one SEAS terminal connected to one CCS MR. There are no redundant connections to the CCS MR and this configuration is intended to serve as a restricted mode of operation until another SEAS terminal is returned to service. The simplex mode of operation is not recommended as a standard mode of operation for the SEAS over IP feature.
- All SEAS information is transmitted over this single IP connection to the CCS MR.
- The SEAS system will be in an IS-ANR/Restricted state while the system is in the simplex SEAS terminals operation and a major alarm, UAM 0348, is generated for the SEAS system. Refer to Unsolicited Alarm and Information Messages Reference for more information on UAM 0348.
Figure 5-3 Simplex SEAS Terminal Configuration
Provisioning the SEAS over IP Feature
To provision the SEAS over IP feature, perform these steps.
- Add the E5-IPSMs to the database using the
ent-cardcommand. Perform the Adding an E5-IPSM procedure. - Enable the SEAS over IP feature using the
enable-ctrl-featcommand. Perform the Activating the SEAS over IP Feature procedure. - Configure the SEAS connections using the
chg-seas-configcommand. Perform the Performing the Initial SEAS Configuration procedure. - Configure the SEAS terminals using the
chg-trmcommand. Perform the Configuring SEAS Terminals procedure. - Turn the SEAS over IP feature on using the
chg-ctrl-featcommand. Perform the Activating the SEAS over IP Feature procedure.
5.2 Activating the SEAS over IP Feature
This procedure is used to enable and turn on the SEAS over IP feature using the feature’s part number and a feature access key.
The feature access key is based on the feature’s part number and the serial number of the EAGLE, making the feature access key site-specific.
The enable-ctrl-feat command enables the feature by inputting the feature’s access key and the feature’s part number with these parameters:
:fak – The feature access key provided by Oracle.
:partnum – The Oracle-issued part number of the SEAS over IP feature, 893018801.
Once this feature is enabled, it is permanently enabled. This feature cannot be enabled with a temporary feature access key.
The Telnet feature (IP User Interface), part number 893005701, must be enabled and turned on before the SEAS over IP feature can be enabled. Perform the Activating Controlled Features procedure to enable and turn on the Telnet feature.
Once the SEAS over IP feature has been enabled, the SEAS over IP feature must be turned on with the chg-ctrl-feat command. The chg-ctrl-feat command uses these parameters:
:partnum – The Oracle-issued part number of the SEAS over IP feature, 893018801.
:status=on – used to turn the SEAS over IP feature on.
Note:
To turn the SEAS over IP feature on in step 5, these items must be provisioned in the database.- The
seascllivalue must be provisioned. - The IP address and port for at least one connection must be provisioned.
- At least one SEAS terminal must be provisioned.
- If the Eagle OAM IP Security Enhancement feature is enabled and turned on, the
loginandhnamevalues for at least one connection must be provisioned.
If you wish to provision the EAGLE for the SEAS over IP feature at this time, perform these procedures.
Once the SEAS over IP feature has been turned on, it be can be turned off. For more information on turning the SEAS over IP feature off, go to the Turning Off the SEAS Over IP Feature procedure.
The status of the SEAS over IP and Telnet features is shown with the rtrv-ctrl-feat command.
Caution:
When the SEAS over IP feature is turned on, and the SEAS terminals and SEAS configuration is provisioned, SEAS traffic is sent to the CCS MR using the SEAS terminals.Figure 5-4 Activating the SEAS over IP Feature
5.3 Performing the Initial SEAS Configuration
This procedure is used to configure the connections to the CCS MR using the chg-seas-config command. This procedure is performed only when configuring the connections to the CCS MR for the first time.
The chg-seas-config command can be used to change the SEAS configuration after the connections have been configured for the first time. Perform the Changing the Existing SEAS Configuration procedure to make this type of change.
The chg-seas-config command uses these parameters.
:conn – The name of the SEAS connection, either IPMR1 or IPMR2
:seasclli – The CLLI part of node name of the EAGLE consisting of one alphabetic character and up to 15 alphanumeric characters. The seasclli value is different from the EAGLE clli value that is entered with the chg-sid command. The seasclli value must also be configured on the Telcordia Message Router (CCS MR). Refer to Telcordia Configuration Specification "Telcordia Technologies System Documentation", BD-SNAM-ADMIN-4 Issue 14, November 2006.
:ipaddr – The IP address of the CCS MR.
:port – The port number of the CCS MR that the EAGLE connects to, from 1024 to 5000.
:hname – The name of the remote host of the CCS MR, 1 to 15 alphanumeric characters.
:login – The login name of the CCS MR, 1 to 15 alphanumeric characters.
:authmode – The method of authentication used for the connection. Currently, only password authentication is used for SEAS connections, so this parameter has only one value, password. This parameter is optional and does not need to be specified.
The hname, login, and authmode parameters are used only when the Eagle OA&M IP Security feature is enabled and turned on. The values for these parameters are displayed in the rtrv-seas-config output only when the Eagle OA&M IP Security feature is enabled and turned on. The status of the Eagle OA&M IP Security feature is shown in the rtrv-ctrl-feat output.
Caution:
The IP address andport value combination for each SEAS connection must be unique or the chg-seas-config command will be rejected.
The IP address for the SEAS over IP configuration cannot be shown as the IPADDR value in the rtrv-ip-lnk or rtrv-ftp-serv outputs, or the BPIPADDR value in the rtrv-ip-card output.
Figure 5-5 Performing the Initial SEAS Configuration
Sheet 1 of 2
Sheet 2 of 2
5.4 Configuring SEAS Terminals
This procedure is used to configure SEAS terminals for the SEAS over IP feature. The SEAS terminal can be configured only on E5-IPSMs.
Note:
As of Release 46.5, the E5-IPSM card and its functionality is replaced by the E5-ENET-B (p/n 870-2971-01) or SLIC (p/n 7094646) card. Any references to E5-IPSM and the 870-2877-01 part number should be replaced by the 46.5 and greater card and part number.The EAGLE can contain a maximum of two SEAS terminals, but only one SEAS terminal can be configured on an E5-IPSM. When an E5-IPSM is configured in the database, eight telnet terminals are created. To configure the SEAS terminal, one of these telnet terminals is changed to a SEAS terminal using the chg-trm command with these parameters.
:trm – The number of the telnet terminal being changed, 17 through 40
:type=seas – The SEAS terminal type.
The chg-trm command contains other parameters, but these parameters cannot be used in this procedure. For more information on these parameters, see the Changing Terminal Characteristics procedure in this manual, or the chg-trm command description in Commands User's Guide.
SEAS terminals can be configured only if the SEAS over IP feature is enabled. The status of the SEAS over IP feature is shown in the rtrv-ctrl-feat output. If the SEAS over IP feature is not enabled, perform the Activating the SEAS over IP Feature procedure in this chapter to enable the SEAS over IP feature.
When the SEAS terminal is configured, the value for the SEAS output group parameter is set to YES. The values for the other output group parameters and the tmout, dural, and mxinv parameters are not changed.
The other output group parameters can be changed with the specific output group parameter or the all parameter. If the all=no parameter is specified for a SEAS terminal (type=seas), all the output group values are changed to NO except for the SEAS output group. The SEAS output group value remains set to YES and this message is displayed.
SEAS Output Group is SET for SEAS terminal <terminal number>Figure 5-6 Configuring SEAS Terminals
Sheet 1 of 3
Sheet 2 of 3
Sheet 3 of 3
5.5 Changing the Existing SEAS Configuration
This procedure is used to change the existing SEAS configuration using the chg-seas-config command.
The chg-seas-config command uses these parameters.
:conn – The name of the SEAS connection, either IPMR1 or IPMR2
:seasclli – The CLLI part of node name of the EAGLE consisting of one alphabetic character and up to 15 alphanumeric characters. The seasclli value is different from the EAGLE clli value that is entered with the chg-sid command. The seasclli value must also be configured on the Telcordia Message Router (CCS MR). Refer to Telcordia Configuration Specification "Telcordia Technologies System Documentation", BD-SNAM-ADMIN-4 Issue 14, November 2006.
:ipaddr – The IP address of the CCS MR.
:port – The port number of the CCS MR that the EAGLE connects to, from 1024 to 5000.
:hname – The name of the remote host of the CCS MR, 1 to 15 alphanumeric characters.
:login – The login name of the CCS MR, 1 to 15 alphanumeric characters.
:authmode – The method of authentication used for the connection. Currently, only password authentication is used for SEAS connections, so this parameter has only one value, password. This parameter is optional and does not need to be specified.
The hname, login, and authmode parameters are used only when the Eagle OA&M IP Security feature is enabled and turned on. The values for these parameters are displayed in the rtrv-seas-config output only when the Eagle OA&M IP Security feature is enabled and turned on. The status of the Eagle OA&M IP Security feature is shown in the rtrv-ctrl-feat output.
If the seasclli value is being changed, all the SEAS terminals must be taken out of service. If the connection information for one connection is being changed, only the terminal associated with this connection must be taken out of service.
Caution:
The IP address andport value combination for each SEAS connection must be unique or the chg-seas-config command will be rejected.
The IP address for the SEAS over IP configuration cannot be shown as the IPADDR value in the rtrv-ip-lnk or rtrv-ftp-serv outputs, or the BPIPADDR value in the rtrv-ip-card output.
Figure 5-7 Changing the Existing SEAS Configuration
Sheet 1 of 3
Sheet 2 of 3
Sheet 3 of 3
5.6 Turning Off the SEAS Over IP Feature
This procedure is used to turn off the SEAS over IP feature using the chg-ctrl-feat command.
The chg-ctrl-feat command uses the following parameters:
:partnum - The part number of the SEAS over IP feature, 893018801.
:status=off – used to turn off the SEAS over IP feature.
The status of the SEAS over IP feature must be on and is shown with the rtrv-ctrl-feat command.
Caution:
If the SEAS over IP feature is turned off, all SEAS terminal traffic stops.Figure 5-8 Turning Off the SEAS Over IP Feature