2 Features Num - E
This chapter describes features starting with numbers and letters from A to E.
2.1 1M System TPS (Release 45.0)
The 1M System TPS feature increases the allowed System TPS (SIGTRAN TPS + ATM TPS) to 1 million transactions per second (TPS). This feature adds capacity to users who already have HIPR2 High Rate Mode feature ON and are running with any of the suggested system configuration and traffic pattern.
The maximum allowed System TPS for all SIGTRAN and ATM links and linksets provisioned in the system includes IPGW, IPSG, IPLIM and ATM links and linksets. The maximum allowed System TPS value is 500,000, 750,000 or 1,000,000 depending on the status of the HIPR2 High Rate Mode, MFC, and 1M System TPS features:
- If the HIPR2 High Rate Mode feature is disabled or turned off, the maximum allowed System TPS is 500,000 (500k).
- If the HIPR2 High Rate Mode feature is turned on and the 1M System TPS feature is disabled or turned off, the maximum allowed System TPS is 750,000 (750k).
- If the HIPR2 High Rate Mode feature, the MFC feature, and the 1M System TPS feature are turned on, the maximum allowed System TPS is 1,000,000 (1M).
The System TPS calculation includes IPLIM TPS and ATM TPS usage. This calculation may cause existing configurations to exceed the maximum allowed System TPS value of 500k, 750k or 1M. The current configuration will continue to function; however, the user will be prevented from entering a provisioning command that increases their System TPS value.
The user can also provision more IPGW, IPLIM, IPSG and ATM cards to configure the higher System TPS. If user wants to add new IPSG or ATM links, add the first link to an IPLIM card, increase the iptps of an IPGW linkset or increase the slktps/rsvdslktps/maxslktps values of an IPSG linkset beyond 750,000, the 1M System TPS feature must be turned on. For provisioning the system TPS above 750,000 and up to 1,000,000, the 1M System TPS feature must be turned on.
If the EAGLE already has 1,000,000 System TPS provisioned, the user cannot enter a provisioning command that will increase the provisioned System TPS.
2.2 3 Links per E5-ATM Card (Release 43.0)
The 3 Links per E5-ATM Card feature allows the E5-ATM card to support a maximum of 3 ATM links. The third link is referred to as link A1 and can be assigned to the third port on an E5-ATM card. The E5-ATM card must be re-loaded before link A1 can be supported.
The 3 Links per E5-ATM Card feature is a quantity feature with part numbers ranging from 893-0391-01 to 893-0391-77. Each quantity FAK supports the feature in the increment of 5 E5-ATM cards.
2.2.1 Feature Control Requirements
- FAK for Part Number in the range 893-0391-01 to 893-0391-77. Each FAK enables the 3 Links per E5-ATM Card feature for an increment of 5 E5-ATM cards.
- Any ATM link provisioned on the system must have a VCI value less than or equal to 16383 before the feature can be enabled.
- A temporary FAK cannot be used to enable the feature.
- After a feature quantity is enabled, the default status of the feature is ON. A feature cannot be turned off after being turned on.
- After a feature quantity is enabled, a feature with a lower quantity cannot be enabled.
2.3 5 Minute Linkset Data (Release 25.0)
Release 25.0 adds two new schedules to the EAGLE reporting capabilities: D_NM and D_MTCS. Both schedules are available through the EAGLE terminal interface, and through the SEAS interface via the OAP.
The following figure provides a high-level diagram of the capabilities implemented by these new schedules. The D_MTCS schedule is a new capability for generating an on-demand maintenance status report using the rept-meas command (EAGLE) or the send-dem-meas command (SEAS). The report is generated from maintenance block data that is currently maintained within the OAM.
D_NM is a five-minute linkset schedule and supports the lnkset entity type. D_MTCS is a snapshot of the maintenance status indicators, and supports the link and lnkset entity types.
Figure 2-1 Concept Diagram

The D_NM schedule provides five-minute throughput measurements on a per-linkset basis, on demand. The schedule is available through the EAGLE HMI or the SEAS interface. Although the reporting of the D_NM schedule is new for Release 25.0, the mechanisms for collecting the data contained in the schedule are currently implemented in the EAGLE for link data collection. This feature reorganizes the link data collection to collect on a linkset basis. The linkset measurements are aggregated in a new data store over a five-minute period, and reported in the D_NM schedule. This feature does not impact per-link measurements data reporting.
The D_MTCS schedule provides the current maintenance state (active, out-of-service, or unavailable) of signaling links and linksets. The D_MTCS schedule is available on demand via the rept-meas command through the EAGLE HMI, or via the send-dem-meas command through the SEAS interface. Both interfaces support a parameter to specify reporting current data (period=active) for a link or linkset.
2.4 5-8 Bit Sequencing Assurance (Release 24.0)
Description
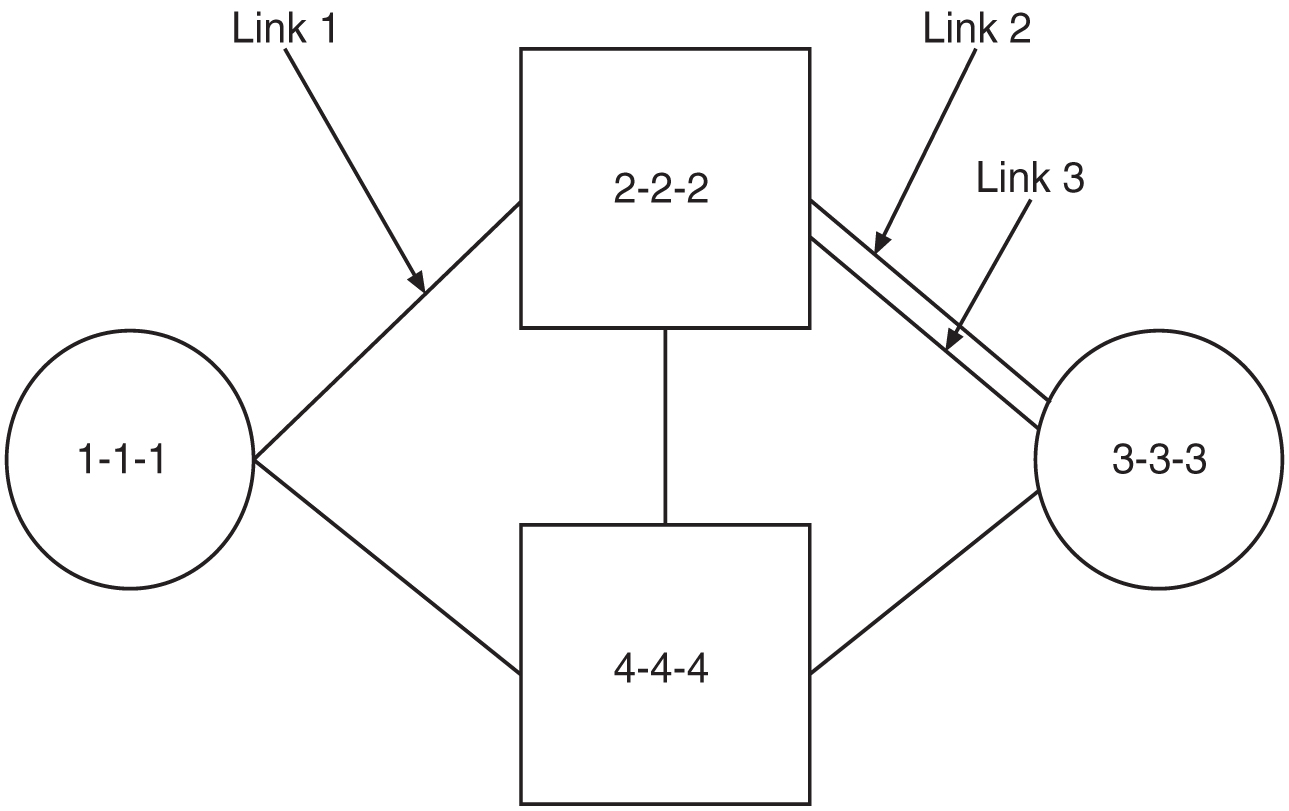
The signaling link selection field (SLS) in an MSU is used to balance traffic across the links in each linkset that a message passes through. The originator of the traffic can, by using the same SLS for a group of messages, guarantee that the same links are selected and guarantee that the traffic will be in sequence. In previous releases, the EAGLE evenly distributed traffic using a 5-bit SLS by using a 3-bit counter to fill in the three most significant bits in the SLS. This can result in missequencing of MSUs, as shown in the following example and figure:
-
Node 1-1-1 generates two messages with the same SLS, intending for them to be sequenced, and transmits them across link 1.
-
STP 2-2-2 converts the 5-bit SLS to an 8-bit SLS, resulting in two different SLS codes. The two messages leave STP 2-2-2 on links 2 and 3 and arrive out of order at node 3-3-3.
Figure 2-2 Example Network for Problem Description
This feature ensures that when a 5-bit SLS is converted to an 8-bit SLS, the MSUs arrive at the destination node in the order that they were generated by the originating node. The EAGLE also makes these SLS conversions:
-
5-bit ANSI SLS to 4-bit ITU SLS
-
4-bit ITU SLS to 5-bit ANSI SLS
-
8-bit ANSI SLS to 4-bit ITU SLS
The EAGLE does not convert a 4-bit ITU SLS to an 8-bit ANSI SLS.
The 5-bit to 8-bit SLS conversion takes place during the routing process, after the linkset is selected, but before the signaling link is selected. The ITU to ANSI SLS conversion takes place during the ANSI to ITU MSU conversion and after the outgoing signaling link is chosen.
Signaling Link Selection Conversion
5-bit to 8-bit SLS conversion is performed under these conditions:
-
The incoming linkset is an ANSI linkset
-
The
asl8=noparameter is assigned to the incoming linkset -
The outgoing linkset is an ANSI linkset
-
The outgoing linkset has either the
slscnv=onandslsci=yesparameters, or theslscnv=perlsandslsci=yesparameters assigned to it -
The three most significant bits of the SLS are zero.
When an ITU SLS is converted to an ANSI SLS, the ITU SLS is always converted to an ANSI 5-bit SLS. If the MSU containing the converted SLS is rerouted because of a link outage, the SLS may be converted from a 5-bit SLS to an 8-bit SLS.
When an ANSI SLS is converted to an ITU SLS, the ANSI SLS is always converted to an ITU 4-bit SLS.
When a 5-bit ANSI SLS is converted to an 8-bit ANSI SLS, the three most significant bits of the SLS are set using a function of originating point code and incoming port. This ensures that MSUs with the same originating point code, SLS, and incoming port will always have the same SLS after the conversion, guaranteeing that the MSUs arrive at the destination in the same sequence that they were sent.
All ANSI MSUs originating from the EAGLE will have an 8-bit SLS.
2.5 6-Way Loadsharing on Routesets (Release 41.0)
The 6-Way Loadsharing on Routesets feature allows loadsharing across all 6 routes to a destination or exception route.
2.6 8-Bit SLS Support (Release 21.0)
The signaling link selection (SLS) is a field in the routing label of the MSU. It is set by the originator of the MSU to a random value. It is used by EAGLE to pick which outgoing linkset and signaling link to use. MSUs with the same destination and the same SLS take the same path through the network, the same linksets and the same links. The MSUs are guaranteed to arrive at the destination in sequence.
The value of the SLS is used by the EAGLE to distribute traffic over the available signaling links in a linkset. The EAGLE uses only 16 SLS codes for assignment to linksets or combined linksets. For linksets containing 9 to 15 signaling links, some signaling links are assigned two SLS codes while other signaling links are assigned a single SLS code. This can create an imbalance in traffic distribution and inefficient link utilization. To overcome this problem, the EAGLE uses an 8 bit SLS code which provides the EAGLE with 256 SLS codes. More SLS codes means the traffic can be distributed more evenly.
Because some signaling points will still be generating messages with a 5 bit SLS, the EAGLE provides an option to convert 5 bit SLSs in messages to 8 bit SLSs. This option is set on an outgoing linkset basis. ITU messages continue to use 4 bit SLSs. Messages that go from ITU to ANSI are currently converted from a 4 bit SLS to a 5 bit SLS. If the outgoing linkset uses 5 to 8 bit conversion, the ITU messages are converted to 8 bit SLSs. If the linkset does not use 5 to 8 bit conversion, the ITU messages are converted from 4 bit to 5 bit SLS.
MSUs generated by the EAGLE (MTP management, SCCP management, and messages received from X25) will have an 8 bit SLS.
The slsci parameter, used with either the ent-ls or chg-ls commands, indicates whether the 5 bit to 8 bit SLS conversion feature is used to select signaling links for outgoing messages directed to the specified linkset. If the slsci=yes parameter is specified, the EAGLE replaces any 5 bit SLS value contained in received messages with a random 8 bit value before they are used by the EAGLE to select the outgoing signaling link in that linkset. The slsci=yes parameter can only be specified for linksets with ANSI SS7 adjacent point codes.
2.7 15 Minute Measurements (Release 31.3)
The 15 minute Measurements feature is controlled by a feature access key and a measurement option. Turning on the feature requires a part number. The feature cannot be turned off once turned on. It is a Permanently ON feature. Upon turn on, the collection period defaults to the 30-minute option to maintain compatibility with the existing system capabilities.
The feature becomes operational when the collection period has been changed to 15 minutes. The collection period can be changed from 30 minutes to 15 minutes (and vice versa) by changing the 15 Minute Measurements collection option of the Measurements Platform options table. When the 15 Minute Measurements collection is disabled, measurements data will be collected and reported each half-hour at hh:00 and hh:30. When the 15 Minute Measurements collection option is selected to enabled, measurements data will be collected and reported four times each hour at hh:00, hh:15, hh:30, and hh:45. The current state of the option is displayed with the Measurements Platform options. Report types supported by 15 Minute measurements are: systot, comp, gtwy, and avl.
Turning on the feature requires a feature access key. This feature cannot be turned off once turned on, therefore it is a Permanently ON feature. When the feature is turned on, the collection period defaults to the 30-minute option to maintain compatibility with the existing system capabilities.
2.8 18 GB to 36 GB Hard Drive Upgrade (Release 29.1) (IP7 Release 7.1)
Description
EAGLE Release 29.1 requires that the EPAP databases accommodate 56 million G-Flex entries. Additional disk space is being provided by way of a hardware disk replacement, from 18 GB disks to 36 GB disks. All the new space on the data disk (18 GB minus overhead) will be appended to the database file system /usr/db. The additional space on the system disk (18 GB minus overhead) will be appended to the swap space. The disk upgrade will occur during a maintenance window, when no software upgrade is scheduled.
Although this feature has been developed specifically for the EPAP, it is not application-specific. This hard drive upgrade could be performed on any MPS server running any GA release.
Upgrade Procedure
The upgrade will be performed as follows:
-
The technician will label the disks in the system and the disks in the upgrade kit.
-
Using Disksuite functionality, half of the old disks will be replaced with the new disks, and will sync with the remaining old disks.
-
Once the disks have been sync’d, the remaining old disks will be replaced with the remaining new disks. The new disks will then sync again.
-
A script will expand the
/usr/dband swap file systems to use all the space available.
A backout will be performed as follows:
-
The MPS will be brought to run-level zero.
-
The technician will remove the 36 GB disks, install all the old disks, and remove the new disks.
-
The technician will boot the MPS.
-
A script will re-mirror and repair the metadbs.
Hardware Requirements
This feature requires that all four 18 GB disks on an individual MPS be replaced with 36 GB disks. (New MPS’s with the EPAP application will be manufactured with the 36 GB disks.)
2.9 24-Bit ITU-N Point Code Support Feature (Release 31.0)
The 24-bit ITU-N point code routing label structure consists of the Destination Point Code (DPC), Originating Point Code (OPC), and the Signaling Link Selection fields.
Both the DPC and OPC are 24 bits in length, and SLS is the code for signaling link selection for load sharing. Currently, only the least 4 bits of the SLS are used. The upper 4 bits are used as part of CIC in the telephone message label. For other messages, the upper 4 bits of the SLS are set to 0000.
Figure 2-3 24-bit ITU-N Point Code Routing Label

2.10 48 Million Numbers (Release 27.0)
Overview
The 48 Million Number feature for EAGLE Release 27.0 provides the capability to expand the number of ported numbers supported on one EAGLE platform from 12 to 48 million numbers. This feature represents both an increase in the number of ported records a single EAGLE node can support and a re-architecture of the current LNP solution (i.e. the LSMS-OAP-OAM LNP interface) for increased database update performance.
The terms MPS and ELAP are used to describe the hardware and software that is replacing the EOAP and the LNP functions of the OAM. MPS refers to the hardware and OS software of the new platform. ELAP refers to the 48 million number application running on the MPS.
This feature is optional and requires a corresponding LSMS feature.
General Description
Customer databases of Local Number Portability (LNP) data are constantly growing. EAGLE Release 27.0 and LSMS Release 4.0 introduce the 48 Million Number feature to satisfy customer database size requirements. Because of the magnitude of the database size increase, several areas of the existing EAGLE/LNP architecture have been upgraded. The following functionality has been changed and improved for Release 27.0:
-
Ownership of the "master" or "golden" real-time LNP database has moved from the EAGLE OAM to the ELAP.
The data model for the new LNP solution closely resembles that of the International LNP solution. Data is collected at the LSMS from the NPAC (for subscription data) and from local provisioning on the LSMS (for default NPANXX, split NPANXX and other types of LNP records). This data is sent to the active ELAP at an EAGLE running Release 27.0 across a TCP/IP connection in the customer's network. The ELAP stores the data locally, and replicates it to the mate ELAP. The ELAP provides real-time database loading and provisioning functions for the EAGLE DSM cards, using two dedicated Ethernet networks between the MPS System and the EAGLE DSM cards.
When the 48 Million Number feature is enabled, this new data model supersedes the existing EAGLE LNP model. The EAGLE OAM will not store LNP databases in Release 27.0. Also eliminated with the 48 Million Number feature are the BLM and DCM cards that previously were required to support EBD&A.
-
The transmission rate of database updates from the LSMS to the EAGLE has increased from 2 TN/sec to 25 TN/sec.
Prior to Release 27.0, LNP updates were sent from the LSMS to the OAP over the customer's network. The minimum OAP hardware in the field today runs on an 85MHz Sparc-4 platform. The OAP translates the data from the LSMS to character based commands resembling SEAS UPL commands for LNP. These commands are sent across a dedicated serial link to an EAGLE terminal port at 19,200 Kpbs. The command is then parsed and validated by the EAGLE before the real-time database is updated. Real-time updates are sent to SCCP cards serially using a card list.
With Release 27.0, the 48 Million Number feature provides a much faster path for updates. LNP updates are sent from the LSMS to the ELAP over the customer's network. The ELAP performs minimal parsing and validation before updating the real-time database. Real-time updates are sent to the EAGLE DSMs in parallel using multicast technology.
-
Enhanced Bulk Download and Audit (EBD&A) is supported directly by the ELAP.
The ELAP now provides all of the functionality of EBD&A.
-
All cartridge-based bulk download operations have been eliminated.
Bulk loading is accomplished using the EBD&A functionality provided by the ELAP. Since EAGLE will not store the real-time database on disk, a cartridge based bulk load is no longer necessary.
-
Real-time databases are recovered from one of the mate EAGLE's ELAPs in a disaster situation (ELAP failure at one EAGLE).
In the unlikely event of a catastrophic failure of the complete MPS system at one EAGLE, resulting in the loss of the real-time database, it will be possible to copy the data from one of the MPS servers of the mated EAGLE node. After the MPS fault has been corrected, a craftsperson may gain access to it via a modem or through the customer's network. It will then be possible to initiate a connection to one of the MPS servers at the mate EAGLE site and initiate a transfer of the real-time database.
-
The EAGLE security log functionality has been moved to the ELAP.
The following figure shows the system architecture supporting the 48 Million Number feature.
Figure 2-4 System Architecture Supporting 48 Million Number

Attached to each EAGLE is an MPS System, consisting of two MPS Servers (Server A and B) and their associated platform software (e.g., Operating System, DBMS, etc.). The servers in the MPS System execute the software developed for the 48 Million Number feature, which is referred to as the "ELAP software."
Throughout the remainder of this description, when the term "ELAP" is used, it means "the ELAP software running on an MPS Server." Thus when we say that there are two ELAPs attached to each EAGLE, we mean that there are two MPS Servers attached to each EAGLE, both of which are running the ELAP software. These two ELAPs run in a mated-pair configuration, with one behaving as the "active ELAP" and the other as the "standby ELAP."
System-Level Requirements
When the 48 million number feature bit is on, the following attributes of the EAGLE change:
-
OAM-based LNP commands are not be allowed (
tt-servis allowed). -
MPS-based LNP commands are allowed (
rtrv-commands only). -
Enhanced Bulk Download (EBDA) functionality is implicitly inherited by the new architecture
The 48 million number architecture inherits all functionality of the 12 million number architecture (except for a separate bulkdownload component). This includes:
-
Support DN to LRN mapping and up to six services for message relay. CLASS,LIDB,ISVM and CNAM message relay service are supported. (Customer-defined services are supported.)
-
Support AIN/IN, IS-41 and PCS 1900 LNP query/response.
-
Support Measurements (OAM can retain LNP Measurements).
-
Support Transaction Log for LNP updates.
-
Support for MPS alarming via EAGLE terminal.
-
Support warm restart/incremental loading of the DSM card.
-
Support loading the DSM card.
-
Support Warm/Cold Restart of the DSM card
-
Database storage of the LNP data from the LSMS.
Note:
The MPS architecture supports a real-time database only -
LNP Commands (
tt-servandrtrv-only)
There is one security log on the ELAP. The security log on the ELAP logs global (across all DSM cards) LNP updates as one entry, regardless of the number of DSM's provisioned. However, actions taken for a specific DSM card by the ELAP are logged on a per-DSM card basis.
The 48 million number architecture does not preclude the operation of the mate STP with the 12 million number architecture.
Required Hardware
To support 48 Million Numbers feature and the increased download rate from the NPAC/LSMS, the following new hardware is being introduced:
DSM
The Database Services Module (DSM) supports 48 million numbers by providing 1 GB daughterboard memory increments up to a total of 4GB. The DSM also provides TCP/IP connectivity directly to the MPS.
Table 2-1 Supported DSM Configurations
|
Name |
Description |
Maximum number of ported numbers supported |
|
DSM1GB |
DSM with 1GB populated memory |
12,000,000 |
|
DSM2GB |
DSM with 2GB populated memory |
24,000,000 |
|
DSM3GB |
DSM with 3GB populated memory |
36,000,000 |
|
DSM4GB |
DSM with 4GB populated memory |
48,000,000 |
The DSM does not support the alloc-mem command to allocate daughterboard memory. Instead, the memory physically present on the board determines the number of ported records supported.
MPS
The Multi-Purpose Server (MPS) running the ELAP application is designed as a replacement not only for the LNP functionality contained in the EOAP, but also for the LNP database that currently resides on the OAM. The MPS fits into one general purpose frame (GPF).
Upgrade Considerations
ELAP
ELAP software is new software. All initial applications of this feature will be new installations. Future software upgrades will be addressed with the Solaris "pkgadd" utility. The following data must be preserved or re-generated for upgrade:
-
Data configured through the user interface
-
Security logs
-
Data provisioned from the LSMS
Each of these must be addressed by any future upgrade.
Maintenance
Three upgrade considerations affect maintenance:
-
Support the EPAP alarms defined in Release 26.05 and 26.1 during upgrade. This must be done for both UAMs and the
rept-stat-mpsoutput. -
Allow TSM cards to co-exist with DSM cards and support the output in all
rept-statreports. -
Allow for the conversion of DSMs from DSM operation to TSM operation via a database restore operation.
Measurements
Measurements data are not preserved from a prior release to the upgrade release during an upgrade. If the customer desires to retain a record of pre-upgrade measurements, a hardcopy of the measurements data can be obtained using the documented LNP measurement report procedures. Alternatively, measurements data can be copied to a Measurements removable cartridge using the copy-meas command. The data is then available for offline (non-EAGLE) processing. Measurements data cannot be restored to the upgraded EAGLE due to potential changes in data formats as a result of the upgrade.
LNP Measurements are preserved when the LNP48MIL feature bit is enabled after upgrade.
2.11 56 Million G-Flex Entries (Release 29.1) (IP7 Release 7.1)
Description
The 56 Million G-Flex Entries feature is a product of the 18GB (P/N 804-1282-01) to 36GB disk (P/N 804-1548-01) hard drive upgrade; see “18GB to 36GB Hard Drive Upgrade (Release 29.1) (IP7 Release 7.1)”. As a result of this increased storage capacity, the existing EPAP and EAGLE software now can support 56 Million G-Flex entries.
Hardware Requirements
This feature requires the 36 GB disk hard drive (P/N 804-1548-01).
2.12 64 PC support in M3UA DAUD message (Release 42.0)
Transmitted M3UA network management messages in response to M3UA DAUDs are revised to be handled in separate phases before and after MSUs are transmitted during time slice processing. This separation allows support of up to 64 point codes.
For the first phase, no more than 20% of the total reserved SLKTPS (RSVDSLKTPS) assigned to the association on which the DAUD was received is used to transmit DAUD response messages. If one or more of the association’s links is found with the RSVDSLKTPS set to zero, then the TPS sum is set to the maximum SLKTPS (MAXSLKTPS) for the first link found. No more than 20% of the MAXSLKTPS assigned to the association’s first link found with no RSVDSLKTPS is used to transmit DAUD response messages. For additional discussion of RSVDSLKTPS and MAXSLKTPS, see Support IPSG Link Capacity Sharing (Release 42.0).
For the second phase, after all the MSUs on the transmit queue have been sent, all associations can compete for the remaining card capacity if needed. The capacity is based on the MAXSLKTPS. The available remaining capacity is shared among the associations that perform DAUD processing. If more than one association needs grants, then grants are distributed in a round robin fashion.
For a DAUD message received with 64 affected point codes, in order for the audit responses to be guaranteed enough bandwidth, it is recommended to set the RSVDSLKTPS/MAXSLKTPS high enough to accommodate potentially up to 128 responses from this audit.
2.13 80 SE-HSLs on E5 Cards (Release 41.1)
The 80 SE-HSLs on E5 Cards feature allows the Synchronous E1 High Speed Link (SE-HSL) feature to support quantities of 72 or 80 high speed links on HC-MIM and E5-E1T1 cards.
2.14 96M Database on E5-SM4G card (Release 38.0, EPAP 10.0)
The 96M Database on E5-SM4G card feature allows an EPAP user to use E5-SM4G cards to support the same database capacity that is currently supported for DSM cards, using combinations of DN, IMSI, and IMEI entries.
2.14.1 Feature Control Requirements
There are no feature control requirements identified for this feature.
2.14.2 Hardware Requirements
This feature requires E5-SM4G or 4G DSM cards with EPAP-based applications.
2.14.3 Limitations
When this feature is implemented, the capacity limits for combinations of DN/IMSI entries may not support 96M. The limits are as follows.
Table 2-2 DN/IMSI Capacity Limits
| # DN (millions) | # IMSI (millions) |
|---|---|
| 96 | 0 |
| 90 | 7.5 |
| 84 | 7.5 |
| 78 | 15 |
| 72 | 22.5 |
| 66 | 30 |
| 60 | 30 |
| 54 | 37.5 |
| 48 | 45 |
| 36 | 52.5 |
| 24 | 67.5 |
| 18 | 75 |
| 6 | 82.5 |
| 0 | 90 |
This decrease in capacity is based on high-level engineering design for the feature.
2.15 120 Million EPAP DN/IMSI Entries (Release 39.1)
The 120 Million EPAP DN/IMSI Entries feature allows up to 120 million entries to be provisioned in the RTDB database. The entries can consist of directory numbers (DNs), International Mobile Subscriber Identities (IMSIs) or a mixture of DNs and IMSIs. Up to 100,000 DN range entries are supported.
2.15.1 Hardware Requirements
The 120 Million EPAP DM/IMSI Entries feature requires Service Module cards. Any DSM cards that are used must have 4G of memory.
250 GB hard disk drives are required in the EPAP provisioning servers.
2.15.2 Limitations
The 120 Million EPAP DN/IMSI Entries feature has the following limitations:
-
Once customers have installed the 120 Million EPAP DN/IMSI Entries feature, all prior PDB backups are no longer valid. Restoration of a backup made prior to the upgrade to the 120 Million EPAP DN/IMSI Entries feature can result in an inability of the PDBA software and MySQL daemon to start up. Contact Tekelec Customer Service for assistance with these restorations.
-
Once customers have upgraded from EPAP 10.0 or 11.0 to EPAP 12.0 and beyond, RTDB backups made prior to the upgrade are no longer compatible with the software. If the EPAP software detects that such an incompatible RTDB has been restored, the database will be marked DB DIFF and RTDB. A reload (or restore from a post-upgrade backup) must be performed.
Table 2-3 DN/IMSI Capacity Limits
| # DN (millions) | # IMSI(millions) |
|---|---|
| 120,000,016 | 0 |
| 112,500,015 | 7,500,001 |
| 105,000,014 | 15,000,002 |
| 97,500,013 | 22,500,003 |
| 90,000,012 | 30,000,004 |
| 82,500,011 | 37,500,005 |
| 75,000,010 | 45,000,006 |
| 67,500,009 | 52,500,007 |
| 60,000,008 | 60,000,008 |
| 52,500,007 | 67,500,009 |
| 45,000,006 | 75,000,010 |
| 37,500,005 | 82,500,011 |
| 30,000,004 | 90,000,012 |
| 22,500,003 | 97,500,013 |
| 15,000,002 | 105,000,014 |
| 7,500,001 | 112,500,015 |
| 0 | 120,000,016 |
2.16 120 Million LNP Numbers (Release 32.0)
Description
The 120 Million LNP number feature provides the capability to expand the maximum number of ported/pooled LNP numbers supported on one EAGLE platform from 96 million to up to 120 million LNP numbers. Local Service Management System (LSMS) _ EAGLE LNP Application Processor (ELAP) reload, audit and reconcile times increase proportionally to the size of the database. Aggregate times for Multi-Purpose Server (MPS) to DSM audit, reconcile, and reload increase slightly due to the increase in LNP database capacity, but the rate-per-time unit remain the same.
Hardware Requirements
The existing 4G DSM card is used for 120 Million LNP numbers.
Limitations
-
This feature is only available for North American LNP customers.
-
This feature is dependent on the LSMS 120 Million LNP number feature.
-
If the Message Relay Group (MRG) Table exceeds 2 million entries then the Software Release Upgrade cannot occur. This is an incompatible situation and loss of data may occur if the upgrade is executed for either the EAGLE 5 ISS or ELAP.
2.17 120 SE-HSL Support (Release 46.0)
The 120 SE-HSL Support feature increases the maximum SE-High Speed Link support from 80 to 120 per EAGLE node. The following Feature Access Keys (FAKs) are used to support the increased number. Refer to Commands User's Guide for a detailed description.
-
893013012 :SE-HSL SLK Capacity :QTY=88
-
893013013 :SE-HSL SLK Capacity :QTY=96
-
893013014 :SE-HSL SLK Capacity :QTY=104
-
893013015 :SE-HSL SLK Capacity :QTY=112
-
893013016 :SE-HSL SLK Capacity :QTY=120
2.18 120M DN and 120M IMSIs via Split Database (Release 45.0)
The 120M DN and 120M IMSIs via Split Database feature, or EPAP Data Split feature, splits EPAP data into DN and IMSI subsets. Each subset of data is loaded on a specific set of E5-SM4G or E5-SM8G-B cards. Since each set can support 120 million, splitting the data allows a system-wide EPAP data capacity of 240 million.
chg-card command is used to designate E5-SM4G and E5-SM8G-B cards as
either DN or IMSI cards. The DN, DN Block, ASD and Entity data will be loaded on the DN
card, and the IMSI, IMEI, IMEI block, and Entity data will be loaded on the IMSI card.
Note:
For the complete list of cards supported by EAGLE Release 47.0, see Hardware Reference Guide.2.18.1 Feature Control Requirements
- FAK for Part Number 893-0398-01
- A temporary FAK cannot be used to enable the feature.
- The feature cannot be turned off after it is turned on.
- The EPAP Data Split feature requires EPAP 15 or higher.
- Message Flow Control must be turned on before the EPAP Data Split feature can be enabled.
- At least one EPAP-related feature must be turned on before the EPAP Data Split feature can be enabled.
- E5-SM4G or E5-SM8G-B cards must be present in the system before the feature can be enabled.
- The feature cannot be enabled if a DSM, E1-ATM, E1T1-MIM, LIM-ATM, or MPL card is equipped and running in the system.
2.18.2 Hardware Requirements
E5-SM4G or E5-SM8G-B cards must be running in the system before the EPAP Data Split feature can be enabled. If a DSM card is running, then the feature cannot be enabled.
If a DSM, E1-ATM, E1T1-MIM, LIM-ATM, or MPL card is installed after the EPAP Data Split feature is turned on, then the card will auto-inhibit.
2.19 120M DNs plus 120M IMSIs via Split Database (EPAP 15.0)
The 120M DNs and 120M IMSIs via Split Database feature is supported in EPAP 15.0 and EAGLE Release 45.0 when the EPAP Data Split feature (part number 893-0398-01) is enabled and turned on using a Feature Access Key (FAK) at the EAGLE. This feature must be turned on at both the EAGLE and the EPAP. As a permanently-on feature, the feature cannot be turned off after it is turned on.
After the EPAP Data Split feature is turned on, all Service Module cards are initialized as combined cards which contain DN and IMSI data. For the 120M DNs and 120M IMSIs via Split Database feature, a Service Module card must be configured as either a DN card or an IMSI card, using the chg-card command. The Service Module card configured as a DN card supports DN, DN Block, ASD, and Entity entries. The Service Module card configured as an IMSI card supports IMSI, IMEI, IMEI Block, and Entity entries. The 120M DNs and 120M IMSIs via Split Database feature requires E5-SM4G or E5-SM8G-B Service Module cards (E5-SMxG cards). The 120M DNs and 120M IMSIs via Split Database feature is not supported on DSM Service Module cards.
The 120M DNs and 120M IMSIs via Split Database feature expands the EPAP capacity from 120 million to 240 million database entries with a combined maximum of 120 million DNs and 120 million IMSIs. The DN count is independent of the IMSI and IMEI count. The DN entries reside on a one set of Service Module cards, while the IMSI and IMEI entries reside on another set of Service Module cards. A maximum of 120 million DN entries are supported on a Service Module card configured as a DN card. The database count of 240 million entries does not include the ASD and IMEI counts. However, EPAP can support more than 240 million database entries with allowed combinations of IMSI and IMEI counts on the IMSI card and with combinations of DN and ASD counts on the DN card. A Service Module card configured as an IMSI card supports a maximum of 120 million IMSIs or the following combination of IMSIs and IMEIs.
Maximum Combinations of IMSI, IMEI entries
- 120 million, 6 million
- 112.5 million, 16 million
- 105 million, 26 million
- 97.5 million, 32 million
2.20 192 Million LNP Numbers (Release 34.0, ELAP 5.0)
Description
The 192 Million LNP Numbers Support feature expands the maximum number of ported/pooled Local Number Portability (LNP) numbers supported on one EAGLE 5 ISS platform to 192 million LNP numbers. The feature supports feature access keys for 132, 144, 156, 168, 180, or 192 million ported/pooled numbers.
Configurable alarm thresholds indicate:
-
When the transactions-per-second (TPS) for the EAGLE 5 ISS (as a whole) reaches the threshold value.
-
When the number of LNP ported TNs and LRNs in the database is approaching the configured percent of the enabled maximum number allowed in the database.
-
When the thermal limits of an HC-MIM card have been reached.
The 192 Million LNP Numbers Support feature requires the ELAP 5.0 database application. The ELAP 5.0 database application is installed and runs on the T1100 application server.
Hardware Requirements
The existing 4GB DSM card must be used for the 192 Million LNP Numbers feature.
The ELAP 5.0 database application that supports 192 million LNP numbers runs on the T1100 platform.
Limitations
-
The 192 Million LNP Numbers feature is available only for North American LNP customers.
-
This feature requires the LSMS 192 Million LNP Numbers feature.
-
Prior to the upgrade, Tekelec will perform a pre-upgrade health check to access the compatibility of your current hardware and software configuration. If the Message Relay Group (MRG) table exceeds 2 million entries, the Software Release Upgrade cannot occur. This is an incompatible situation, and a loss of data may occur if the upgrade is executed for either the EAGLE 5 ISS or ELAP.
-
192 Million LNP Numbers feature activation on the EAGLE 5 ISS is based on the following conditions:
-
The ELAP LNP Configuration feature access key must be on.
-
4-Gigabyte DSMs are required; at least one 4-Gigabyte DSM must be provisioned in the system.
-
The ELAP software version must be ELAP 4.0 if an EAGLE 5 ISS feature access key for 96-120 Million LNP Numbers is enabled.
-
The ELAP software version must be ELAP 5.0 if an EAGLE 5 ISS feature access key for more than 120 Million LNP Numbers is enabled.
-
2.21 228 Million LNP Numbers (ELAP 6.0)
Description
As Local Number Portability becomes more established, competition increases, and number pooling becomes more widespread, the number of ported TNs continues to increase. Customers would like to manage a single LSMS that is capable of maintaining the national LNP database. Increased capacity is required on the ELAP.
Currently, Tekelec supports 192 Million LNP numbers per node on a 4 GB DSM card. With the advent of wireless portability and continued wireline LNP porting and pooling activity, it is anticipated that the 192 Million LNP numbers capacity will be exceeded sometime early-mid 2007 as shown in Figure FN-1.
Figure 2-5 Current LNP Growth Projections
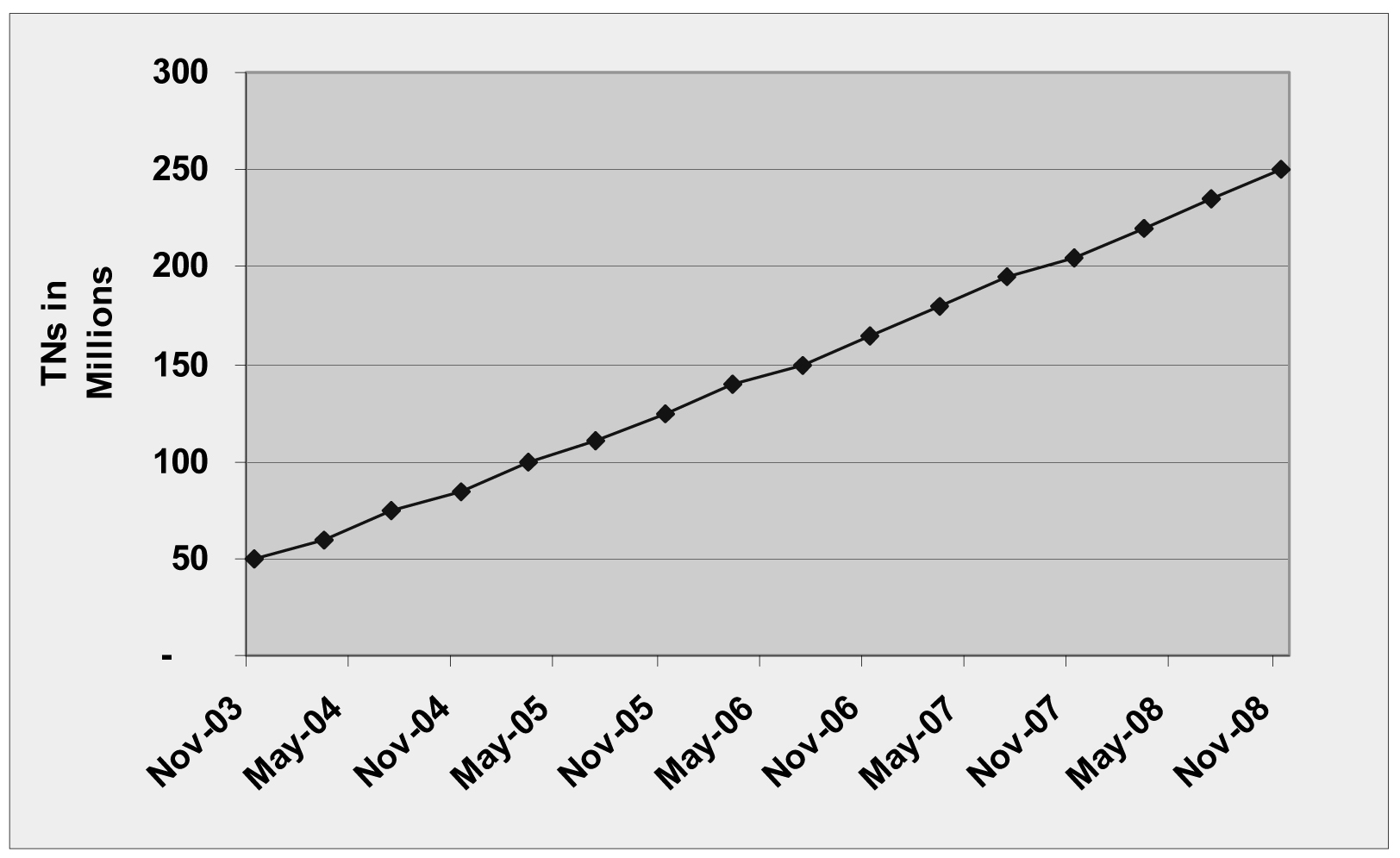
The 228 Million LNP Numbers feature allows customers to use their existing hardware and remain in a centralized Eagle LNP architecture (all LNP numbers in one node).
The 228 Million LNP Numbers feature expands the maximum number of ported/pooled LNP numbers supported on one EAGLE node to 228 million LNP numbers in increments of 12 million numbers. Additional database improvements include faster MPS-to-DSM audit reconcile and reload times, and LSMS-to-ELAP audit times.
The 228 Million LNP Numbers feature expands the maximum number of ported/pooled Local Number Portability (LNP) numbers supported on one on the ELAP to 228 Million LNP Numbers. The feature supports feature access keys for increments from 204, 216, or 228 million ported/pooled numbers across all NPAC regions.
Hardware Requirements
The 228 Million LNP Numbers feature requires the existing 4 GB DSM card.
The 228 Million LNP Numbers feature runs on the T1100 platform.
Limitations
The 228 Million LNP Numbers feature is available only for North American LNP customers.
The 228 Million LNP Numbers feature requires the LNP 228 Million numbers feature on the LSMS.
2.22 228 Million LNP Numbers (Release 35.0)
Description
The 228 Million LNP Numbers feature allows the capacity of an EAGLE 5 ISS node to increase to 228 million LNP numbers without adding new hardware.
The increase is achieved by using existing 4GB DSM cards and enhancing the database. EAGLE 5 ISS supports the following feature access keys for LNP growth beyond 120 million LNP numbers on the existing 4GB DSM card:
- 132 Million LNP – 893-0110-15
- 144 Million LNP – 893-0110-16
- 156 Million LNP – 893-0110-17
- 168 Million LNP – 893-0110-18
- 180 Million LNP – 893-0110-19
- 192 Million LNP – 893-0110-20
- 204 Million LNP – 893-0110-21
- 216 Million LNP – 893-0110-22
- 228 Million LNP – 893-0110-23
The 228 Million LNP Number feature must be activated on the LSMS, ELAP, and EAGLE 5 ISS products. LSMS 8.5 and ELAP 6.0 with 228 Million LNP Numbers support are required to enable the feature on EAGLE 5 ISS.
Hardware Requirements
The 228 Million Numbers LNP feature has the following hardware requirement:
- The existing 4GB DSM card must be used for the 192 Million LNP Numbers feature.
- The ELAP 5.0 database application that supports 192 million LNP numbers runs on the T1100 platform.
Limitations
The 228 Million LNP Numbers feature has no limitations.
2.23 384 Million LNP Records (Release 39.0, ELAP 8.0)
The 384 Million LNP Records feature is a quantity feature that increases the LNP capacity from 228 million LNP numbers and number pool blocks to 384 million LNP numbers and number pool blocks per EAGLE 5 ISS node.
This feature also provides up to 200 thousand location routing numbers (LRNs) and 350 thousand numbering plan area and exchange (NPA-NXX) numbers on a single node.
The 384 Million LNP Records feature is an EAGLE 5 ISS feature. However, the feature interacts with the ELAP and LSMS systems. All of the systems must be at the required release before the 384 Million LNP Records feature can be enabled.
For information on the ELAP component of the 384 Million Records feature, refer to the ELAP Administration Manual of your EAGLE 5 ISS Release 39.0 documentation set. For information on the LNP component, refer to the LNP Feature Activation Guide.
2.23.1 Feature Control Requirements
The 384 Million LNP Records feature has the following feature control requirements:
- The LSMS, EAGLE 5 ISS, and ELAP systems must be running at the required release levels.
- The 384 Million Records feature for the LSMS must be turned on before the 384 Million LNP Records feature for the EAGLE 5 ISS can be enabled.
- The 384 Million LNP Records feature is a quantity feature. The numbers of LNP records are increased beyond 228 million in increments of 12 million. A FAK for the part number corresponding to the desired increment is required:
- 893-0110-24: 240 million
- 893-0110-25: 252 million
- 893-0110-26: 264 million
- 893-0110-27: 276 million
- 893-0110-28: 288 million
- 893-0110-29: 300 million
- 893-0110-30: 312 million
- 893-0110-31: 324 million
- 893-0110-32: 336 million
- 893-0110-33: 348 million
- 893-0110-34: 360 million
- 893-0110-35: 372 million
- 893-0110-36: 384 million
- A temporary FAK cannot be used to enable the feature.
- The feature cannot be turned off after being turned on.
- After the feature is turned on, a feature that provides a lower number of records cannot be enabled and turned on.
2.23.2 Hardware Requirements
The hardware requirements for the 384 Million LNP Records feature varies depending on the quantity that is enabled and the version of ELAP that is used.
Table 2-4 Hardware Compatibility Matrix
| Quantity FAK Enabled | ELAP 7.0 or Less | ELAP 8.0 |
|---|---|---|
| <= 192M | Service Module cards | E5-SM4G cards |
| 204M - 228M | DSM cards | E5-SM4G cards |
| >= 240M | N/A | E5-SM4G cards |
Note:
Quantities of >228M require ELAP 8.0 and LSMS 11.0.Note:
Total system TPS capacity cannot exceed 40,000 TPS when E5-SM4G cards are used.2.24 500 SS7 Links (Release 21.0)
In Release 21.0, the maximum number of SS7 signaling links the EAGLE can contain is being increased from 268 to 500. For the EAGLE to contain 500 SS7 signaling links (a maximum of 250 LIMs), the system configuration has been increased from 3 frames to 6 frames. Each frame can contain 3 shelves, with the exception of the last frame which can contain only 1 shelf, for a maximum of 16 shelves. The numbering of the shelves is 1100 to 6100. This provides card location numbers from 1101 to 6118. Also in Release 21.0, card locations 1111 and 1112 are also configurable in the database. The following table shows the new numbering scheme for card locations.
Table 2-5 Release 21.0 Card Location Numbering Scheme
| Frame | Shelf 1 | Shelf 2 | Shelf 3 |
|---|---|---|---|
|
Frame 1 |
1101 - 1108, 1111 - 1118 |
1201 - 1208, 1211 - 1218 |
1301 - 1308, 1311 - 1318 |
|
Frame 2 |
2101 - 2108, 2111 - 2118 |
2201 - 2208, 2211 - 2218 |
3201 - 3208, 3211 - 3218 |
|
Frame 3 |
3101 - 3108, 3111 - 3118 |
2301 - 2308, 2311 - 2318 |
3301 - 3308, 3311 - 3318 |
|
Frame 4 |
4101 - 4108, 4111 - 4118 |
4201 - 4208, 4211 - 4218 |
4301 - 4308, 4311 - 4318 |
|
Frame 5 |
5101 - 5108, 5111 - 5118 |
5201 - 5208, 5211 - 5218 |
5301 - 5308, 5311 - 5318 |
|
Frame 6 |
6101 - 6108, 6111 - 6118 |
Not Equipped |
Not Equipped |
As a result of the change in the system configuration, the range of values specified for any command that uses the card location or the shelf location as a parameter (the loc parameter) have been changed. These commands are:
Table 2-6 Commands Changed for 500 SS7 Links
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
If the EAGLE is using the gateway screening, global title translation, X.25 gateway, or STP LAN features, the card requirements to support these features will reduce the maximum number of SS7 signaling links the EAGLE can contain. The card requirements for these features are:
-
For the gateway screening feature, the EAGLE can contain a maximum of 8 ASMs running the
glsapplication. -
For the global title translation feature, the EAGLE can contain a maximum of 25 ASMs running the
sccpapplication. -
There can only be one X.25 signaling link assigned to a LIM.
-
For the STP LAN feature, the EAGLE can contain a maximum of 20 ACMs.
2.25 504 Million LNP Entries (Release 10.1)
This feature increases the capacity from 384 Million to 504 Million Telephone Number (TN) or Number Pool Block (NPB) records. This feature also removes incremental capacity control in ELAP. This feature increases the TN count; the maximum allowed count for all other data types remains unchanged:
Table 2-7 Max Data
| Value | LNP 384M Solution | LNP 504M Solution |
|---|---|---|
| TN | 384,000,000 | 504,000,000 |
| NpaNxx | 350,000 | 350,000 |
| Lrn | 200,000 | 200,000 |
| Mr | 2,000,000 | 2,000,000 |
| LrnMr | 2,000,000 | 2,000,000 |
| OGTT | 200,000 | 200,000 |
The default system capacity is 120M. The user is be able to configure the system capacity to 504M by setting the MAX_RECORDS feature value to 504 on the LSMS.
See Administration and LNP Feature Activation User's Guide for more information on configuring quantity keys.
2.26 1100 TPS/DSM for ITU NP (Release 36.0)
Description
The 1100 TPS/DSM for ITU NP feature allows a DSM card to support up to 1100 transactions per second (TPS) for the EAGLE 5 ISS G-Port, A-Port, INP, IS41 GSM Migration, EIR, and ANSI-41 INP Query features.
The 1100 TPS/DSM for ITU NP feature increases the TPS capacity of each DSM card from the current 850 TPS to 1100 TPS per card when an EPAP-based ITU feature (G-Port, G-Flex, INP, EIR, Prepaid IDP Query Relay, A-Port, IS41 GSM Migration, or AINPQ) has been turned on. Increasing the TPS of each card increases the maximum capacity of an EAGLE 5 ISS, with 25 DSM cards in a 24 + 1 configuration, from 20,400 to 26,400 TPS. (The capacity of a DSM card is rated at 1700 TPS when features requiring EPAP-based database lookup have not been enabled or turned on.)In most systems, only 50% or less of the traffic needs an EPAP-based database lookup while the rest of the traffic requires GTT-related database lookup. The 1100 TPS/DSM for ITU NP feature assumes that at most 70% of the traffic shall require EPAP-based database lookup.
A feature access key (FAK) for part number 893018001 is required to enable this feature.
-
A temporary FAK is not allowed for this feature.
-
This feature is an ON/OFF feature, it can be turned on and off after it has been enabled.
-
At least one EPAP-based ITU feature (G-Port, G-Flex, INP, EIR, Prepaid IDP Query Relay, A-Port, IS41 GSM Migration, or AINPQ) must be on before this feature can be enabled.
-
The ansigflex STP option cannot be used when this feature is enabled; this feature cannot be enabled when the ansigflex STP option is used.
Hardware Requirements
The 1100 TPS/DSM for ITU NP feature requires DSM cards running the VSCCP application
Limitations
When the 1100 TPS/DSM for ITU NP feature is on and more than 70% of the traffic requires EPAP-based database lookup, the DSM cards provisioned in the system for SCCP might not be able to support 1100 TPS.
2.27 2500 Routing Keys (IP7 Release 7.1)
Description
This feature increases the total number of routing keys on a SSEDCM IPGWx application from 1000 routing keys to 2500, while retaining the DCM IPGWx application to a maximum of 1000 routing keys. The total number of routing keys for each application may be all dynamic, all static, or a combination of both.
The SG supports two types of routing keys for use by the IPGWx application, Static Routing Keys and Dynamic Routing Keys. Both routing keys are stored in one routing key table which is located in RAM on the IPGWx application.
-
Static Routing Keys. These routing keys are provisioned via administration commands and are stored in the OAM static database. The SS7IGWx application keeps a copy of the static routing keys in the SS7 Routing Key Table on-board in RAM for quick access.
-
Dynamic Routing Keys. Dynamic Routing Keys are provisioned via a request sent over an IP connection and allows an IP connection to automatically direct traffic towards (or away from) themselves by sending messages to the Signaling Gateway.
Note that all IP connections (TALI/TCP, M3UA/SCTP and SUA/SCTP) on the IPGWx application use routing keys. Currently, only TALI sockets have the capability to create dynamic routing keys via dynamic registration. However, this feature makes no assumptions regarding an IP connection’s ability to register dynamic routing keys.
New Auto-inhibit Facility
The System Configuration Manger (SCM) software is responsible for determining if the proper GPL should be fully loaded onto the requested card. For IPGWx applications, the SCM software will now calculate the sum of the CHG-SG-OPTS command parameters :SRKQ and :DRKQ to see if the total is over 1000.
If the sum is over 1000 and the IPGWx application board is a DCM, the card will be automatically inhibited, and the alarm message Insufficient memory for provisioning will be displayed. When a DCM IPGWx card is auto-inhibited, it will remain inhibited, unless the following sequence of events occurs.
-
The number of routing keys on all IPGWx applications must be reduced to 1000 or less.
-
Once the number of routing keys is reduced to 1000, the
CHG-SG-OPTScommand must be issued such that drkq + srkq <= 1000. -
The inhibited IPGWx card must be manually allowed.
Hardware Requirements
This feature requires the SSEDCM-based IPGWx GPLs (870-2372-xx).
2.28 4000 Routesets (Release 23.0)
This feature increases the size of the routing table in the EAGLE database from 2000 entries to 4000 entries. With this feature turned on, the user can configure up to 4000 routesets in the database. The EAGLE requires that the destination point code of each routeset be entered in the database. So to enter 4000 routesets in the database, 4000 destination point codes must be entered in the database. The size of the destination point code table has been increased from 2000 destination point codes to 4000 destination point codes.
The 4000 routeset feature is activated using the chg-feat command. A new parameter, DSTN4000, has been added to the chg-feat command to turn the 4000 routeset feature on. Before the chg-feat command can be executed, the link interface modules (LIMs), both low-speed and high-speed, must have the proper memory installed.
All link interface modules (LIMs) running the ss7ansi, ss7gx25, and ccs7itu applications, the low-speed LIMs, must be equipped with one dual inline memory module (DIMM), containing 4 Mbytes of static RAM. All LIMATMs, the link interface module used for the high-speed ATM signaling link, must be equipped with two DIMMs providing a total of 8 Mbytes of memory. This additional memory is required so that the larger routing table can be downloaded to each LIM.
If the DSTN4000 parameter is specified with the chg-feat command and even one LIM does not have the proper memory installed, the chg-feat command is rejected with this message, and the 4000 routeset feature will not be turned on:
2.29 5000 Routes (Release 26.1)
Some customers with large network configurations require more than 4000 routes, due to the expansion of link capability and/or collapsing networks. This feature is a continuation of route expansion for the EAGLE platform, and is intended to replace the 4000 route feature.
The maximum number of administered routes supported in the EAGLE STP has been increased from 4000 to 5000 as a system-wide option. The minimum number of x-list entries remains 500.
The EAGLE STP now supports, as a system-wide option, the administration and protocol changes required to support 5000 routes. The default for the routing option remains 2000 routes, and 500 x-list entries. No change in x-list capacity is required. Total routes table capacity is 5500 entries.
2.30 6000 Routesets (Release 29.0)
Description
The 6000 Routesets feature expands the SS7 routing connectivity between the EAGLE and other nodes by increasing the number of routesets supported by the EAGLE. This allows for the EAGLE to function in larger SS7 networks.
The functionality of this feature applies to all LIM types except LIMs running the GX25 GPL, which will continue to utilize the X.25 2000 Routeset feature. However, the increased 6000 SS7 routeset table will also be downloaded on GX25 card.
Note:
There is a feature access key for the 6000 Routeset feature. It can not be activated unless the 5000 routeset feature bit is ON and the active and standby OAM is a GPSM-II running the EOAM GPL.
Hardware Requirements
This feature requires the GPSM-II in the active and standby OAM slot, and a TDM change (870-0774-10 or later).
Caution:
Never install or initialize MCAP cards in MASP slots 1113 and 1115 after features that require GPSM-II cards are provisioned. Attempting to initialize MCAP cards with GPSM-II features provisioned will cause a system outage. Before replacing an existing GPSM-II card in a MASP slot (1113 and 1115) contact Tekelec Customer Service.
2.31 8,000 Routesets (Releases 31.8, 34.0)
Description
The 8,000 Routesets feature expands the SS7 routing connectivity between the EAGLE 5 ISS and other nodes by increasing the number of routesets supported by EAGLE 5 ISS from 6000 to 8000. This feature can be viewed as an extension to the 6000 Routesets feature, which expanded the EAGLE 5 ISS routesets from 5000 to 6000.
A Feature Access Key (FAK) allows the customer to set the routeset limit to either 7000 or 8000. With the exception of a routeset provisioning limit imposed by the 7000 FAK, the 7000 Routeset and 8000 Routeset implementations are identical.
Limitations
If the customer has more than 8000 aliases provisioned, then the 7000 or 8000 Routesets feature cannot be enabled. Aliases must be deleted from the system until the 8000 alias limit is met.
Hardware Requirements
The 8000 Routesets feature permits customers to add additional routesets without requiring hardware change.
2.32 10,000 Routesets (Release 43.0)
The 10,000 Routesets feature allows up to 10,000 routesets or destinations to be provisioned on the EAGLE 5 ISS. The maximum number of supported aliases and exception list entries are increased to 10,000, each. The maximum number of supported normal and exception routes (combined) is increased to 10,000.
An additional 500 entries continue to be supported for dynamically-created exception list entries. These entries are available only if the Cluster Routing feature is turned on.
2.32.1 Feature Control Requirements
- FAK for Part Number 893-0064-05
- The 5000 Routesets feature must be turned on before the 10,000 Routesets feature can be enabled.
- The Cluster Routing feature must be turned on before the additional 500 entries that are reserved for dynamically-created entries are available.
- A temporary FAK cannot be used to enable the 10,000 Routesets feature.
- The 10,000 Routesets feature cannot be turned off after being turned on.
2.33 40,000 GTT Capacity (Release 28.0) (IP7 Release 6.0)
The EAGLE currently supports a maximum of 20,400 GTT/sec/system. For many customers, this GTT capacity is insufficient. This is especially true for customers who use a single node, or a single pair of nodes, to centralize GTT for their entire network. This feature allows the EAGLE to process a minimum of 40,800 GTT/sec/system.
The 40,000 GTT Capacity feature assumes the use of DSM cards for GTT functionality.
For more information on the GTT feature, refer to the Database Administration Manual - Features.
2.34 50,000 GTT Capacity (Release 35.1)
Description
The 50,000 GTT Capacity featur increases the GTT processing capability of EAGLE 5 ISS GTT-only nodes from 40,800 TPS to 52,700 TPS through the use of 32 DSMs per node (31 active and 1 for +1 redundancy), each running at 1700 TPS per card (31 x 1700 = 52,700).
Hardware Requirements
The 50,000 GTT Capacity feature requires 32 DSM cards exclusively for GTT functionality.
Limitations
The 50,000 GTT Capacity feature has the following limitations:
-
The LNP, G-Flex, G-Port, INP, or EIR features cannot be activated if there are more than 25 DSM cards in the system. Therefore, these features are not supported in conjunction with the 50,000 GTT Capacity feature.
-
The maximum number of SCCP cards allowed in a single EAGLE 5 ISS node is 32 (to provide n+1 functionality). 32 DSM cards are required to achieve 52,700 TPS: therefore, if any TSM cards are in the system, the total TPS rate will be less than the system maximum.
-
The 50,000 GTT Capacity feature is not available on systems that are equipped with MPS.
2.35 65,535 Entries per Translation Type (Release 22.0)
This feature improves the performance of the global title translation subsystem of the EAGLE to these levels.
-
850 messages per second
-
21,000 global title translations per second per system
-
65,536 entries per translation type
There is no mechanism to limit the number of global title translation entries to less than 65,537 per translation type. The maximum number of entries in the global title translation table has not changed and is still 270,000 entries. It is possible to enter all 270,000 entries under one translation type. The performance of the global title translation subsystem is not guaranteed when more than 65,536 translations are entered for a single translation type.
The rtrv-gtt command output has been changed to show the capacity of the global title translation table is as a percentage of the total number of entries in the system (270,000 entries).
2.36 150,000 GTT TPS and 75,000 EPAP TPS (Release 37.0)
Description
The 150,000 GTT TPS feature increases the throughput capacity of the EAGLE 5 ISS from 52,700 to 150,000 TPS for a node in which the SCCP message throughput traffic is processed by the GTT feature.
The 75,000 EPAP TPS feature increases the throughput capacity of the EAGLE 5 ISS from 20,400 to 75,000 TPS for a node that processes part of the SCCP message throughput traffic by one or more of the EPAP-based features (e.g. G-Port, G-Flex, EIR, or INP) or for a node that processes a combination of GTT and EPAP traffic.
These features require the E5-SM4G card to be installed in the EAGLE 5 ISS. The E5-SM4G Throughput Capacity feature must be enabled and turned on in order to operate at 5000 TPS (if traffic is processed by GTT) or 3125 TPS (if traffic is processed by the EPAP-based features).
- All of the DSM cards must be replaced with E5-SM4G cards.
- The E5-SM4G Throughput Capacity feature must be enabled and turned on.
If all of the SCCP traffic is processed by GTT, then a maximum of 32 E5-SM4G cards can be provisioned in the EAGLE 5 ISS. If the E5-SM4G Throughput Capacity feature is enabled and turned on, then each E5-SM4G card can process traffic at a rate of 5000 TPS, and the 150,000 TPS rate can be reached.
If any of the SCCP traffic is processed by an EPAP-based feature, then a maximum of 25 E5-SM4G cards can be provisioned in the EAGLE 5 ISS. If all of the SCCP traffic is processed by EPAP-based features, and if the E5-SM4G Throughput Capacity feature is enabled and turned on, then the rate of 75,000 TPS can be reached.
E5-SM4G cards can co-exist with DSM cards in the EAGLE 5 ISS; however, if both kinds of cards are used, then the maximum TPS rates cannot be reached.
Feature Control Requirements
The E4-SM4G Throughput Capacity feature has the following feature control requirements:
- A FAK for part number 893-0191-01
- A temporary key cannot be used to enable the E5-SM4G Throughput Capacity feature.
- After the E5-SM4G Throughput Capacity feature has been turned on, it cannot be turned off.
- The E5-SM4G Throughput Capacity feature cannot be enabled if any of the following features or options are turned on:
- E5IS (EAGLE 5 Integrated Monitoring) feature
- LNP feature
- ANSIGFLEX STP option
Hardware Requirements
The E5-SM4G Throughput Capacity feature requires HIPR cards to be installed in all the shelves in an EAGLE 5 ISS node.
Limitations
The 150,000 GTT TPS and 75,000 EPAP TPS features have the following limitations:
- The real time database entry capacity of the E5-SM4G card for the EPAP-based features is smaller than the capacity supported by the current DSM 4G card.
- If the E5IS IMF or LNP feature, or the ANSIGFLEX system option is enabled, then the TPS level is held to the level of a DSM card (1700 TPS). The E5-SM4G Throughput Capacity feature cannot be enabled, and the 150,000 GTT TPS feature cannot be used.
2.37 Ability to Change System Required User Passwords (ELAP 9.0)
With the ability to support many users comes the need for tighter security. The user interface addresses security concerns with various restrictions and controls. In many cases, the frequency or severity of these checks is configurable by the administrator at both a user specific and system-wide level.
- New password requirement for viewing logs.
- Stricter password complexity rules, with password complexity required.
- Stricter password aging rules.
- Stricter password reuse rules.
- New requirement to enter the password for
elapdevUser ID on the Copy RTDB from Remote screen.
2.38 Ability to Change System Required User Passwords (EPAP 14.0)
The Ability to Change System Required User Passwords feature enhances the EPAP Graphic User Interface (GUI) to increase security restrictions and controls. The frequency and severity of these controls is can be configured by the administrator at user-specific level and system-wide levels.
Security enhancements include a new password requirement for viewing logs. The appuser user is the only user authorized to view logs and must supply a password to view the logs. In addition, strict password complexity, password aging, and password reuse rules are introduced.
Password Complexity
Password complexity rules for user passwords implemented by EPAP 14.0:
- The password cannot exceed 100 characters in length.
- The password must include at least one alpha character.
- The password must include at least one numeric character.
- The password must include at least one special punctuation character: question mark (?), period (.), exclamation point (!), comma (,), or semicolon (;).
- The password cannot contain three or more of the same alphanumeric or special punctuation character in a row.
- The password cannot contain three or more consecutive ascending alphanumeric characters in a row.
- The password cannot contain three or more consecutive descending alphanumeric characters in a row.
- The password cannot contain the user account name (login name).
- The password must not contain the user account name in reverse character order.
- The password must not be blank or null.
- The password must not be a default password.
Note:
The option to enforce or not enforce password complexity has been removed.Password Aging
Users can be forced to change their passwords after a certain number of days. The administrator can set a maximum password age of up to 180 days as a default for the system and can specify a different maximum password age for any individual user.
Password Reuse
Users cannot reuse their last N passwords, where N is a system-wide configurable number from 3 to 99, with a default of 5. The administrator cannot turn off this restriction by setting N to 0 (zero).
2.39 Ability to Configure a Single EPAP Server (Release 16.2)
This feature supports the configuration of EPAP on a single setup. This feature allows the user to perform disaster recovery on mixed/non-prov setup and other to configure the EPAP on single setup.
Note:
This feature is not supported on PDBonly setup.This feature eliminates the manual steps required for the Network Configuration. Instead, a menu option is provided in the epapconfig menu that allows the user to perform disaster recovery that performs the network configuration.
See the "Configure Mate Disaster Recovery" section in Administration Guide for more information.
2.40 Additional DRA values for INP formatting (Release 43.0)
The existing INP (Part Number 893-0179-01) and AINPQ (Part Number 893-0178-01) features are enhanced to support additional DRA values:
- GRN
- GRN+DN
- CC+GRN+DN
2.41 Additional Integrated Sentinel Support (Release 28.2)
Description
This feature adds the following EAGLE cards to those supported by the EAGLE with Integrated Sentinel Feature introduced in EAGLE Release 28.0. Sentinel 8.1 supports monitoring for links on E1-ATM and LIM-ATM cards, and supports SS STC cards for monitoring:
-
E1-ATM - With Release 28.2, the EAGLE supports Integrated Sentinel functionality for the E1-ATM card.
-
LIM-ATM - With Release 28.2, the EAGLE supports Integrated Sentinel functionality for the LIM-ATM card.
-
SS STC - With Release 28.2, the EAGLE supports the existing Sentinel routing functionality (EROUTE GPL) on a SS STC card.
New Hardware Required
No new hardware is required for this feature. Note, however, that the EAGLE with Integrated Sentinel feature does require the use of GPSM-II cards in place of MCAP cards, and HMUX cards in place of IPMX cards. Also, the EAGLE Time Synchronization feature must be active in conjunction with this feature. In addition, the timing requirements include the use of an external Bits clock.
Caution:
Never install or initialize MCAP cards in MASP slots 1113 and 1115 after features that require GPSM-II cards are provisioned. Attempting to initialize MCAP cards with GPSM-II features provisioned will cause a system outage. Before replacing an existing GPSM-II card in a MASP slot (1113 and 1115) contact Tekelec Customer Service.
2.42 Add GTT on SLIC IPSG [6500] (Release 46.5)
This feature ports GTT functionality to SLIC IPSG cards. A new IPSG32 GPL combines GTT and IPSG capabilities to the SLIC card.
In order to load the new combined GPL (IPSG32), a SLIC card must be flashed with 32-bit flash (BLSLC32), and provisioned with type=slic, appl=ipsg, and data=gtt.
Note:
The TPS performance was increased from 6,500 to 10,000 via an enhancement that is also part of EAGLE 46.5. The GTT throughput provided by LIM (IPSG) cards is limited to 400K. Since each GTT-enabled SLIC IPSG card supports 10K TPS, up to 40 GTT-enabled SLIC IPSG cards can be supported on a node.The GTT throughput of 400K provided by LIM cards is counted separately from the SCCP SM subsystem throughput. The rept-stat-sccpcommand is enhanced to display the GTT statistics on GTT on LIM cards.
See unresolvable-reference.html#GUID-07E4F62D-EE90-48CC-8FB0-F3B598B8FB2C__V6671712 for the enhancement bug details, and Commands User's Guide for rept-stat-sccp details.
2.42.1 Hardware
The Add GTT on SLIC IPSG [6500] functionality only runs on SLIC cards with a 32-bit BLSLC32 flash GPL.
The following table describes hardware and provisioning combinations for IPSG cards:
Table 2-8 Supported Card Types for the IPSG Application
| Card Provision Type/GTT ON/OFF | ENET-B/32-bit BLMCAP OR ENET-A | SLIC/32-bit BLSLC32 | SLIC 64-bit BLSLC64 |
|---|---|---|---|
| ENET/ENETB (GTT cannot be enabled on ENET/ENETB card type) | Supported
Loads IPSG GPL |
Supported (will work as IPSG card with the ENETB card type)
Loads IPSG GPL |
Auto-Inhibit (HW Verification Code 174) |
| SLIC with GTT disabled (DATA=NOSCCP) | Not Supported (Card will Auto-inhibit) (HW Verification Code 172) | Supported (will work as a GTT disabled IPSG card with the card type SLIC)
Loads IPSG GPL |
Auto-Inhibit (HW Verification Code 174) |
| SLIC with GTT enabled (DATA=GTT) | Not Supported (Card will Auto-inhibit) (HW Verification Code 172) | Supported
Loads IPSG32 GPL |
Auto-Inhibit (HW Verification Code 174) |
2.43 Additional PDBI Provisioning Statistics on EPAP (EPAP 15.0)
The PDBI Provisioning Statistics reports include new performance information: total number of commands with a return code of zero that successfully updated the database for the reported period. Only ent, upd, and dlt commands are counted in the statistics report; rtrv commands are not included. This performance information is displayed in the report output, generated from the GUI or CLI, as Total Number of successful PDBI commands, as shown in the following example.
Example of Report Contents for a specified interval:
Average Number of PDBI Connections = 3
Peak Number of PDBI Connections = 10
Average system PDBI CPS = 78
Peak CPS = 99
Total Number of successful PDBI commands = 4885
Percentage of successful PDBI commands = 962.44 Additional Subscriber Data (Release 40.0, EPAP 12.0)
- IDP Relay Additional Subscriber Data
The IDP Relay ASD feature provides a Numbering Plan Processor (NPP) service action to extract ASD information from the called party (CdPN) and calling party (CgPN) lookups.
- IDP Relay Generic Routing Number
The IDP Relay GRN feature provides an NPP service action to extract GRN information from the CdPN and CgPN lookups.
- TIF Additional Subscriber Data
The TIF ASD feature allows an ASD digit string to be inserted into the CdPN of an outgoing IAM or REL ISUP message.
- TIF Generic Routing Number
The TIF GRN feature allows a GRN digit string to be inserted into the CdPN of an outgoing IAM or REL ISUP message. The GRN value is obtained from the RTDB.
The new TIF and IDPR features allow EPAP ASD that is associated with a specific subscriber to be inserted into either the CgPN or CdPN based on RTDB lookup
Note:
The TIF ASD and TIF GRN features are built on the services provided by the Triggerless ISUP Framework (TIF) and are considered to be TIF applications or services. Refer to the Feature Manual - TIF for additional information.In addition, existing features and commands are enhanced to support ASD. For example, the IS-41 to GSM Migration Phase 1 (IGM) and GSM MAP SRI Redirect to Serving HLR features allow provisioning of new Mobile Station Routing Number (MSRN) formatting options. If a successful database lookup returns ASD as one of the entities, and if the ASD option is provisioned, then the ASD is encoded into the outgoing SRIACK message. The existing behavior for encoding messages is then followed.
2.44.1 Feature Control Requirements
The following feature control requirements impact the features that are added to support ASD and GRN information:
- The IDP Relay ASD feature requires a FAK for part number 893-0257-01.
- The IDP Relay GRN feature requires a FAK for part number 893-0256-01.
- The IDP Relay feature must be turned on before the IDP Relay ASD or the IDP Relay GRN feature can be enabled.
- The TIF ASD feature requires a FAK for part number 893-0245-01.
- The TIF GRN feature requires a FAK for part number 893-0255-01.
- The TIF Number Portability feature must be turned on before the TIF ASD or TIF GRN feature can be enabled.
- The TIF ASD, TIF GRN, IDPR ASD, and IDPR GRN features can be turned on and off.
2.45 Administrable SLTMs (Release 20.0)
This feature allows the user to configure signaling link test messages (SLTMs). To test the coherency of a particular link, two signaling points can transmit periodic test messages. The signaling point initiating the test selects a link to test and then transmits an SLTM containing a test pattern. The other signaling point responds with an echo of the test pattern contained in the SLTM. The intervals between transmission of signal link test messages (SLTMs) are controlled by the sltm_enabled field in a corresponding SLTM table record. The SLTM table record also controls the following:
-
the length of the test pattern in the SLTM
-
automatic generation of SLTMs
-
generation of periodic SLTMs when a link is put in service
The SLTMs can be sent to a signaling link that is in service whenever desired.
2.46 Advanced GT Modification (Release 38.0)
The Advanced GT Modification feature (AMGTT) allows information in the SCCP calling party address (CgPA) to be modified as part of global title translation (GTT). This information includes the global title address (GTA), translation type (TT), numbering plan (NP), and network address indicator (NAI) parameters.
Note:
If the message requires SCCP Conversion, then modification to the called party address (CdPA) occurs even if the AMGTT feature is turned on.2.46.1 Feature Control Requirements
The AMGTT feature has the following feature control requirements:
- The current GT Modification (MGTT) feature bit is removed immediately upon upgrade to the release that contains the AMGTT feature. This feature bit is replaced with a tiered FAK for the following part numbers:
- FAK for part number 893-0218-01: “Advanced Global Title Modification”. If the MGTT feature is turned off before upgrade, then this FAK is used to enable CdPA and CgPA modification after upgrade.
- Non-sellable FAK for part number 893-0218-02: "Advanced GT Modification, Called Party Only". If the MGTT feature is turned on before upgrade, then this FAK is used to automatically allow continued use of the CdPA modification functionality after upgrade. This FAK does not allow any CgPA modification.
- FAK for part number 893-0218-03: “Advanced GT Modification, Calling Party Upgrade”. If the MGTT feature is turned on before upgrade, then this FAK is used enable CdPA and CgPA modification after upgrade.
- If the MGTT feature is turned off before upgrade, then all AMGTT functionalities are disabled after upgrade. The CdPA and CgPA parameters cannot be modified until the “Standard” functionality (893-0218-01), is enabled and turned on.
- The GTT feature must be turned on before the “Standard” functionality (893-0218-01) can be enabled.
- If the "Upgrade" functionality (893-0218-03) is enabled, then the "CdPA Mod Only" functionality (893-0218-02) is disabled.
- The AMGTT feature, including all subsets of AMGTT functionality, cannot be turned off after it has been turned on.
- The AMGTT feature, including all subsets of AMGTT functionality, cannot be enabled with a temporary FAK.
- The CgPA modification options cannot be used until either the “Standard” (893-0218-01) or “Upgrade” (893-0218-03) AMGTT functionality is enabled and turned on.
2.47 AIN LNP Message Support (Release 46.0)
The AIN LNP Message Support feature extends support of a Local Number Portability feature to allow processing AIN messages using a Mobile Number Portability database. The AIN message types are managed using a Query/Response architecture.
2.48 AINF Applique (Release 21.0)
The AINF is an integrated applique which supports the DSOA, DSCS and V.35 interfaces on the same applique. The AINF applique can be configured as either a DSOA, OCU, or V.35 interface from the user terminal.
2.49 AINPQ Service Portability (Release 41.1)
Service Portability support for the AINPQ feature indicates whether Service Portability applies to ANSI-41 NPREQ messages for own-network subscribers. When Service Portability is applicable, GRN digits are used in place of RN digits in the response message.
2.50 Alarm Enhancements (Release 26.0)
Note:
This is an engineering feature.Currently, adding new UAMs to the system requires many modifications to the software. It requires adding ATH events, adding fields to the maintenance block (MB), changing ATH on the application card to set the new field in the MB, possibly updating the MB revision, and changing SCM to analyze the new field and generate the UAM.
Application Defined UAMs allow the application card to generate UAMs without modifying the OAM build. Initially, this capability will be given to every application using the Generic Maintenance Block. The application will then only be required to supply a message reference number (MRN), an output group, a device type, and element information (example: port number) to the Application Defined UAM software.
There will only be one Application Defined UAM allowed per card in the EAGLE. That is, only one Application Defined UAM may be active at any given time. Multiple Application Defined UAMs may be defined and sent by the application, but not simultaneously. There is only one slot in the MB for Application Defined UAM.
2.51 Allow a Mated Application to Work as Primary-Secondary and Secondary-Primary (Release 22.0)
There are two ways to load share global title translations.
-
A mated application in load shared mode.
-
Two mate applications in dominant mode. The global title translation addresses are split into two ranges such that half of the addresses translate to one mated application and the other half translates to the other.
This feature supports the second method of load sharing. This method of load sharing allows two replicated applications to load share and back each other up in the event of a network failure. Global title translation is load shared by splitting the range of global title addresses and have them work as two separate mated applications. If one application becomes prohibited, SCCP routing translates all the GTT messages in both address ranges to the mated application. The subsystem management messages (SBR/SNR) and SCCP management messages (SSP/SSA) are sent to the adjacent mated application and concerned signaling points.
The following example illustrates how this feature works using a split global title address range.
-
Enter two mated applications as a dominant point code/subsystem pair. In this example, mated application A is point code 001-001-001,
ssn10. Mated application B is point code 001-001-002,ssn10.Input Example
ent-map:pc=001-001-001:ssn=10:mpc=001-001-002:mssn=10 :mult=dom:adj=yesThis mated application pair entered as A backed up by B, automatically creates an entry of B backed up by A. Either the primary or the backup point code and subsystem can be used as the preferred destination for a global title translation range. The other point code/subsystem is treated as the backup.
-
To split the global title ranges, enter two global title translation address ranges. One range uses mated application A and the other uses mated application B.
Input Examples
ent-gtt:type=10:gta=800000:egta=800555:xlat=dpcssn:ri=ssn :pc=001-001-001:ssn=10ent-gtt:type=10:gta=800556:egta=800999:xlat=dpcssn:ri=ssn :pc=001-001-002:ssn=10If mated application A becomes unavailable, all global title translation traffic for both address ranges is routed to mated application B. If mated application B becomes unavailable, the specified global title translation traffic is routed to mated application A. If both point code/subsystem pairs are available, the traffic is split according to the translation type and address ranges specified. Normally, the address range is split so that mated application A receives half the translated global title translation traffic and mated application B receives the other half.
The adjacency, concerned signaling point code group, message routing under congestion and subsystem routing parameters in the
ent-mapcommand apply to both point code/subsystem pairs.The table shows how SCCP routing and subsystem management is handled according to the mated application parameters
adj(adjacency),srm(subsystem routing messages), andmrc(message routing under congestion).
Table 2-9 SCCP Routing and SCCP Management Actions for a Primary-Secondary and Secondary-Primary Mated Application
| Event | ADJ | SRM | MRC | SCCP Routing and SCCP Management Action |
|---|---|---|---|---|
|
Preferred application fails because an MTP_PAUSE message for its point code has been received |
yes |
yes |
yes or no |
|
|
no |
yes |
yes or no |
|
|
|
yes or no |
no |
yes or no |
||
|
Previously prohibited preferred application becomes available because an MTP_RESUME message for its point code has been received |
yes |
yes |
yes or no |
|
|
no |
yes |
yes or no |
|
|
|
yes or no |
no |
yes or no |
||
|
Receive an SSP for the preferred application that is allowed. |
yes |
yes |
yes or no |
|
|
no |
yes |
yes or no |
|
|
|
yes or no |
no |
yes or no |
||
|
Receive an SSA for the preferred application that is prohibited. |
yes |
yes |
yes or no |
|
|
no |
yes |
yes or no |
|
|
|
yes or no |
no |
yes or no |
||
|
Preferred application becomes congested. |
yes or no |
yes or no |
no |
|
2.52 Allow MOBR Exception Routes to Adjacent Point Codes (Release 44.0)
The Origin-Based MTP Routing (MOBR) feature is enhanced to allow exception routes to be provisioned for adjacent point codes (APCs).
Exception routes are allowed through the use of a 'dummy' point code as an APC. After the true APC is replaced by a dummy APC, MOBR exception routes can be configured for the true APC with the same method used for non-adjacent destinations.
The dummy point code is configured and known only to the EAGLE 5.
The linkset to the dummy point code should have the SLTSET set to 0, using the ent-ls or chg-ls command. The sltset parameter specifies the SLT record to be associated the linkset. If a value of 0 is provisioned for the sltset parameter, then a dummy SLTSET is created and designated as 'Reflect'.
If the SLTSET for a linkset is configured as Reflect, then the EAGLE 5 does not send an SLTM message to the adjacent node. When an SLTM message is received, the EAGLE 5 responds with an SLTA message with the OPC and DPC of the SLTA swapped from the SLTM message.
2.52.1 Feature Control Requirements
The sltset=0 parameter can be configured only for an 'A' linkset.
2.52.2 Limitations
The following limitations exist for a linkset with an SLTSET that is provisioned as reflect:
- SLT failures are not reported.
- Periodic SLT messages are not generated for links in the linkset.
- Peer-to-peer network management messages generated by the EAGLE 5 towards an adjacent node are not processed by adjacent nodes configured as the dummy point code. Incorrect route status at these adjacent nodes may result.
- The real point code of the adjacent node is treated as a non-adjacent node. Therefore, network management messages expected only from adjacent nodes are rejected.
- Any traffic generated by an adjacent node for other nodes that have prohibited status at the EAGLE 5 are discarded at the EAGLE 5 and a TFP message is sent back to adjacent node. Adjacent nodes may ignore TFP messages from the EAGLE 5.
-
The change-over and change-back for link failures are time controlled because the destination point code of the Changeover Order (COO) and Changeback Declaration (CBD) messages is the dummy point code, causing these messages to be ignored by the adjacent node. Also, the COO and CBD messages received by the EAGLE 5 from the adjacent node (configured as the dummy point code) are ignored by the EAGLE 5.
2.53 Allowed Affected Destination Field Screen (Release 22.0)
Release 22.0 introduces a new gateway screening entity, the Allowed Affected Destination Field. The Allowed Affected Destination Field contains the affected destination point code of incoming MTP network management messages. This is also referred to as the concerned point code.
The current method of screening the affected point code in network management messages involves a check for the point code in the routing table, self point codes, and capability point codes. This check is applied after the message has passed all screenings in the configured screen set. This check is independent of the screen set. In order to provide the same capability as currently exists, this method of screening for the affected point code in network management messages is retained. The network management message can also be screened with gateway screening screensets. To screen the network management message with the existing capability, the destfld parameter with either the ent-scrset or chg-scrset command (a new parameter introduced in Release 22.0) must be set to yes.
If the destfld=yes parameter is specified, all MSU's with the service indicator of 0 (:si=0), including through switched messages, are screened by gateway screening against the routing table, self point codes, and capability point codes. This screening step is performed after the MSU has passed all other screening tables.
The advantage of using the configured Allowed Affected Destination Field screening table over the routing table is that it is now possible to reject messages containing point codes in the routing table. Previously, if a network management message concerned a point code in the routing table, it would pass this phase of screening and there was no way to prevent its entry into the network. An interconnecting network could then either accidentally or maliciously send a network management message for a destination in the home network.
The network management messages that require screening by the Allowed Affected Destination Field screen are:
-
TFP, TFA, TFR
-
TCP, TCA, TCR
-
TFC
-
UPU
-
SRST (RSP, RSR)
All other network management messages are passed.
For cluster messages (TCP, TCA, and TCR), the member of the affected destination field is set to 0. If the affected cluster contains a point code with a member 0, the affected destination field for a TFx message for the member and a TCx message for the cluster will have the same affected destination. For example, a TFP concerning point code 007-007-000 and a TCP concerning cluster point code 007-007-* will both have an affected destination of 007-007-000. Typically, a user would provision an entry in the allowed affected destination field with these parameters, :ni=007, :nc=007, :ncm=*, all TFx messages concerning the member of the cluster and all TCx messages concerning the cluster are passed. If the user wants to screen TFx messages and TCx messages separately, the allowed SIO screen can be used to send TCx messages to one affected destination table, and send TFx messages to a different affected destination table.
The allowed affected destination field screen is configured with these commands.
-
ent-scr-destfld- adding a new allowed affected destination field entry into the database -
dlt-scr-destfld- removing an allowed affected destination field entry from the database -
chg-scr-destfld- changing an existing allowed affected destination field entry in the database -
rtrv-scr-destfld- displaying the allowed affected destination field entries in the database
All these commands use these parameters.
-
srfor the screening reference name of the allowed affected destination field screen -
ni,nc,ncmfor ANSI point codes -
zone,area,idfor ITU international point codes -
npcfor ITU national point codes
The chg-scr-destfld command also uses these parameters for the point code values being changed.
-
nni,nnc,nncmfor new ANSI point code values -
nzone,narea,nidfor new ITU international point code values -
nnpcfor new ITU national point code values
The rtrv-scr-destfld command also uses the all=yes parameter to display a detailed output of the allowed affected destination field screen. The following is an example of the output of the rtrv-scr-destfld:all=yes command.
Output Example:
RLGHNCXA03W 97-06-07 13:14:18 EDT Rel 22.0.0
SCREEN = ALLOWED DESTFLD
SR NI NC NCM NSFI NSR/ACT
IEC 240 001 010 STOP -, -
IEC 241 010 * STOP -, -
SR ZONE AREA ID NSFI NSR/ACT
IEC 1 003 4 STOP -, -
IEC 1 003 5 STOP -, -
SR NPC NSFI NSR/ACT
IEC 00235 STOP -, -
IEC 00240 STOP -, -
The allowed affected destination field screen can be referenced, the next screening function indicator (NSFI), by the allowed SIO, allowed DPC, and blocked DPC screens. If the allowed affected destination field screen is the NSFI of the allowed SIO screen, the service indicator of the allowed SIO entry must be 0, specified by the :si=0 parameter with the ent-scr-sio and chg-scr-sio commands, and the entry 0 in the SI field in the rtrv-scr-sio command output.
The NSFI for the allowed affected destination field screen has only one value, STOP.
The redirect and copy functions, for the STP LAN and DTA features, (:redirect=yes and :copy=yes parameters with the ent-scr-destfld, chg-scr-destfld, and rtrv-scr-destfld commands) can be used with the allowed affected destination field screen.
2.54 Allowed CDPA Screen on SCCP Management Format ID (Release 22.0)
The allowed called party address (CDPA) screen can screen messages for the SCMG format ID (SCCP Management Format ID). A new parameter, scmgid, has been added to the ent-scr-cdpa, dlt-scr-cdpa, and chg-scr-cdpa commands to configure the allowed CDPA screen to screen for the SCMG format ID. A new field, SCMGID, has been added to the output of the rtrv-scr-cdpa command to show the SCMG format ID in the allowed CDPA screen. The following is an example of the new output.
Output Example:
RLGHNCXA03W 97-06-07 15:41:38 EDT Rel 22.0.0
SCREEN = ALLOWED CDPA
SR NI NC NCM SSN SCMGID NSFI NSR/ACT
IEC 240 001 010 001 002 STOP -, -
IEC 240 001 011 002 ------ STOP -, -
IEC 240 001 010 12 ------ STOP -, -
IEC 241 010 * * ------ AFTPC IAFT
The value for the scmgid parameter is 1 - 255 or *. This parameter must be specified if the subsystem number of the called party address is set to 1 (ssn=1). An SCCP management message has the subsystem field of the called party address set to 1. The SCCP management format ID only applies to SCCP management messages.
The message type of the message being screened for the SCCP message format ID must be either a UDT, UDTS, XUDT or XUDTS message. All other message types are passed.
The wildcard value for the subsystem parameter (ssn=*) indicates the range of values from 2 to 255. When the subsystem number is a wildcard, the next screening function identifier must be stop (nsfi=stop). The SCMG format ID does not apply because messages with a subsystem of 2 to 255 are not SCCP management messages.
If the value of the ssn parameter is not a wildcard (1 - 255), the NSFI for the Allowed CDPA screen can be either the allowed affected point code screen (aftpc) or stop.
2.55 Alternate Command Keywords (Release 20.0)
This feature provides an alternate set of keywords for current EAGLE commands. The following are the new, industry-standard keywords:
Table 2-10 Alternate Set of Command Keywords
|
EAGLE Keyword |
Alternate Keyword |
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
2.56 ANSI G-Flex Support at 1700 TPS per DSM (Release 30.3)
The feature ANSI G-Flex Support at 1700 tps per DSM Card increases the current transaction-per-second (tps) capacity of the G-Flex application running on DSMs cards from 850 tps to 1700 tps in an ANSI environment.
-
In an ITU environment, the capacity will remain at 850 tps per DSM card
-
The Service Selector table cannot contain an ITU entry Only G-Flex is defined as a service (see the -srvsel commands)
-
The G-Flex feature is turned on
-
The ansigflex system option is enabled using the chg-stpopts command.
2.57 ANSI support for RANDOM SLS on Incoming Linkset (Release 40.0)
The ANSI support for RANDOM SLS on Incoming Linkset (ANSI Random SLS) feature allows the Random SLS (Signaling Link Selector) feature to support ANSI Class0 and ISUP traffic on the incoming linkset. If the Replace system option is provisioned, then the SLS value in the message is replaced with a randomized SLS value. This value is used for linkset and link selection during message routing instead of the SLS on an incoming ANSI MSU.
2.57.1 Feature Control Requirements
The ANSI Random SLS feature has the following feature control requirements:
- The
chg-stpopts:randsls=perlscommand must be entered before ANSI RANDSLS processing can occur.Note:
ANSI RANDSLS processing occurs only on incoming linksets where the linkset randsls parameter is set to a value other than off. - The
chg-ss7opts:slsreplace=yescommand must be entered before the SLS in the message can be replaced with a random SLS value.
2.58 ANSI-41 AnalyzedInformation Query - no EPAP/ELAP (Release 42.0)
The ANSI-41 AnalyzedInformation Query (ANSI41 AIQ) feature allows customer migration from one technology to another (e.g. CDMA to LTE), on an individual subscriber basis. This feature addresses termination call handling by providing the ability to indicate which calls are destined for a particular technology.
The feature allows an AnalyzedInformation query to be responded to using an optional parameter that contains pre-configured response digits. These digits are configured to map to trigger type parameter values in the query. The Mobile Switching Center (MSC) that sent the AnalyzedInformation query interprets the response digits to route the call appropriately.
The trigger type in the AnalyzedInformation query is determined by prior interaction between the MSC and the Home Location Register (HLR) which contains the subscriber information,
The ANSI41 AIQ feature is implemented as a local AIQ SCCP subsystem on the EAGLE 5 ISS and does not require the EPAP or ELAP database. A new AIQOPTS table is used to provision ANSI41 AIQ options. This table is part of the existing EGLEOPTS table.
The AIQ subsystem supports SCCP UDT and non-segmented XUDT Class 0 or Class 1 messages and ITU MTP/SCCP, ANSI MTP/SCCP, and ANSI TCAP messages. The subsystem does not support segmented SCCP or TCAP messages.
The ANSI41 AIQ feature does not support the ITU-N24 point code type.
2.59 ANSI-41 INP Query (AINPQ) (Release 36.0)
Description
The ANSI-41 INP Query (AINPQ) feature adds support for using an ITU-N ANSI-41 NPREQ message for querying the INP database, in addition to the existing INP feature number portability query using the ITU-N and ITU-N24 INAP IDP message.
A feature access key (FAK) for part number 893017801 is required to enable the AINPQ feature.
-
The GTT feature must be on before the AINPQ feature can be enabled.
-
After the feature is enabled and turned on, it cannot be turned off.
-
No temporary FAK is allowed for the feature.
-
If any LNP quantity feature is enabled, the INP and AINPQ features cannot be enabled. If either the INP feature or the AINPQ feature is enabled, no LNP quantity feature can be enabled.
-
The AINPQ feature and the EIR feature cannot be enabled in the system at the same time.
The AINPQ feature supports a mix of ITU and ANSI protocols in querying the INP database using the ANSI-41 NPREQ query.
Service selectors, INP options, and measurements are common to the INP and AINPQ features.
INP message relay functions operate when the INP feature, the AINPQ feature, or both features are turned on. The parameter values defined for INP query processing (through the INPQ service or PC/SSN) can apply to both the INP and AINPQ feature if both features are turned on.
INP query processing can be invoked by the following mechanisms (MTP routed NPREQ is not supported):
-
For GTT-routed NPREQ query, INP query processing can be invoked using the inpq service selector that is defined using the SCCP Service Selector commands.
-
For NPREQ-routed-based PC/SSN query, INP query processing can be invoked using the EAGLE 5 ISS point code and local subsystem number (PC/SSN) defined for the INP feature.
When the AINPQ featureis turned on,the INP query processing operates as follows:
-
Handling of an ITU-N Point Code ANSI-41 NPREQ query encoded in ANSI-41 TCAP, ITU SCCP, and ITU MTP protocol stack is supported.
-
ITU MTP/SCCP protocol validation and ANSI TCAP protocol validation for a received ANSI-41 NPREQ query are supported.
-
For a received ANSI-41 NPREQ query subject to the INP query processing, the EAGLE 5 ISS uses the digits encoded in the DGTSDIAL parameter for database lookup.
-
The EAGLE 5 ISS performs number conditioning on the DGTSDIAL value in preparation for database lookup. The Called Party Prefix, National Escape Code, Service Nature of Address, Nature of Number, and Country Codes are used to condition the number as a National or International number.
-
Enhanced AINPQ and INP options for the Global Option for Connect on INP Query feature can be used to format information in the response that results from the database lookup.
-
The AINPQ feature and the INP feature share the INP local subsystem, including SCCP subsystem management and service selection.
-
The AINPQ feature and the INP feature share the CPCTYPE (Capability Point Code Type) state.
When the INP feature is turned on, the INP query processing operates as follows:
-
Handling of the ITU-N and ITU-N24 INAP IDP message is supported.
-
CDPN number conditioning is performed in preparation for database lookup.
-
Enhanced AINPQ and INP options for the Global Option for Connect on INP Query feature can be used to format information in the response that results from the database lookup.
The INP options in the EAGLE 5 ISS have been enhanced to support the AINPQ feature.
-
A new INP option is provided to define the National Escape Code (NEC) value, up to 5 digits, for each EAGLE 5 ISS node.
-
The maximum number of Called Party Prefix entries allowed in the INPOPTS table has been increased from 5 to 40.
-
AINPQ supports the Global Option for Connect on INP Query Response feature that was previously implemented for INP. The destination routing address (DRA) options have been enhanced for INP and AINPQ for formatting the ROUTDGTS parameter in the INP “Connect” message or AINPQ NPREQ “Return Result“ response message, as follows:
-
Support RN + [CDPNPFX] + DN in INP “Connect” or AINPQ “Return Result” response messages
-
Support Routing Number in in INP “Connect” or AINPQ “Return Result” response messages
-
Support [CDPNPFX] + CC + RN + DN in INP “Connect” or AINPQ “Return Result” response messages
-
Support RN + [CDPNPFX] + NEC + DN in INP “Connect” or AINPQ “Return Result” response messages (the National Escape Code must be provisioned)
-
There are no new measurements pegs for NPREQ queries. The existing INP registers are pegged for the NPREQ query, the IDP query, or both; the peg for “IDP received” is a total count of the number of the IDP and NPREQ queries received if both the AINPQ and INP features are turned on.
Hardware Requirements
The ANSI-41 INP Query feature has the following hardware requirements:
-
DSM card with at least 4G of memory running the VSCCP application
-
After AINPQ is enabled, no DSM cards with less than 4G of memory can be provisioned. DSM cards installed with less than 4G of memory will be auto-inhibited if AINPQ is enabled.
Assumptions
The ANSI-41 INP Query feature assumes that an MSC will not initiate an NPREQ query for a call prefixed with International Escape Code (commonly defined as “00”) + CC+DN, as the call is intended for terminating to an international subscriber.
Limitations
None
2.60 ANSI-41 Mobile Number Portability (A-Port™) (Release 36.0)
Description
The ANSI-41 Mobile Number Portability (A-Port) feature enables an IS41 subscriber to change to a different service provider while retaining the same Mobile Dialed Number (MDN).
A-Port uses the EPAP (EAGLE Provisioning Application Processor) RTDB provisioning database to retrieve the subscriber portability status and provision directory numbers for exported and imported IS41 subscribers. This database maintains information related to subscriber portability in the international E.164 format. A-Port uses RN and PT values to provision directory numbers (DNs) for exported subscribers. In addition, A-Port uses SP to provision DNs for imported subscribers. It is optional to provision the PT values for imported subscribers.
Service Selector Lookup
Service selector lookup is performed using the MTP/SCCP data. If the selectors match and MNP service is assigned, A-Port handling is performed.
To manage number portability, A-Port uses the MNP SCCP Service Selector to process LOCREQ and SMSREQ SCCP messages. The EAGLE ISS intercepts LOCREQ messages for the RTDB database lookup. An ANSI-41 LOCREQ message is initiated by a TDMA/CDMA MSC that queries the HLR for information regarding user subscription/location before terminating a voice call.
A-Port supports both GT- and MTP-routed messages.
-
GT-routed messages support UDT and non-segmented XUDT message types and perform service selector lookup after SCCP verification.
-
A-Port processes MTP-routed messages if the MTP Messages for SCCP Applications (MTP Msgs for SCCP Apps) feature is turned on (see IS41 GSM Migration (Release 36.0) for details of MTP-routed message processing).
MNP begins A-Port general TCAP/MAP verification if the message is ANSI TCAP and A-Port is turned on. TCAP/MAP verification is performed on all messages; A-Port supports only the ANSI TCAP format.
Database Lookup and Routing
The DN is used for database lookup.
-
For LOCREQ messages, the DN is derived based on the setting of the LOCREQDN option (see the new
chg-is41optscommand). -
For non-LOCREQ messages, the DN is derived from the SCCP portion of the message.
-
A-Port performs number conditioning upon successful decode and verification of the message. HomeRN and IEC or NEC prefixes are removed. The DN is conditioned to international number format based on the service nature of address (SNAI or TCAPSNAI or MTPLOCREQNAI).
A-Port performs RTDB lookup on the conditioned number, and routes or relays the message based on the lookup result.
-
An SMSREQ message is relayed like any other non-LOCREQ message. No changes are performed to the TCAP/MAP portion of the message.
-
A-Port modifies the TCAP information for LOCREQ messages only when a HomeRN was deleted from the TCAP DN and LOCREQRMHRN = YES. Any gaps in the data caused by a change in field length will be resolved by shifting the remaining information up. Any IEC or NEC code is left.
-
A-Port falls through to GTT if number conditioning fails or does not find the DN in the RTDB database, or the DN is found with non-A-Port data.
-
If a HomeRN is detected in the Called Party and a matching DN with RN is found in the database, the EAGLE 5 ISS generates UIM 1256, indicating detection of circular routing, and routes the message using normal routing if both the MNP Circular Route Prevention feature and the IS41 GSM Migration featureare turned on.
-
Normal routing is performing GTT if the incoming message is sent to the EAGLE 5 ISS Self Point Code. Normal routing is routing the message to the MTP DPC if the incoming message is MTP-routed (the MTP DPC of the message is not the EAGLE 5 ISS Self Point Code).
A-Port shares the service state and re-route with the IS41 GSM Migration feature and the G-Port feature, under one service called the MNP service state. (The G-Port service state is used if only the G-Port feature is on.) A-Port supports re-route functions as part of MNP service re-route. Alternate PCs are shared by all three features.
Alarms and the rept-stat-sccp command output show MNP Service information if the A-Port feature is enabled.
Feature Access Key
A feature access key (FAK) for part number 893015501 is required to enable the A-Port feature.
-
The GTT feature must be on before the A-Port feature can be enabled.
-
After the feature is enabled and turned on, it cannot be turned off.
-
No temporary FAK is allowed for the feature.
-
An LNP quantity feature and the A-Port feature cannot be enabled in the system at the same time.
Measurements
The following enhancements support the collection and retrieval of measurements related to the A-Port feature. These new measurement registers are supported with and without the Measurements Platform feature enabled.
-
New registers are added to the NP SSP reports: Hourly Maintenance Measurements on NP SSP (MTCH-SSP) and Daily Maintenance Measurements on NP SSP (MTCD-SSP).
-
APLRACK—Number of call related LOCREQ messages acknowledged.
-
APLRRLY—Number of call related LOCREQ messages relayed.
-
APNOCL—Number of non-call non-LOCREQ related messages relayed.
-
APNOCLGT—Number of non-call Non-LOCREQ related messages that fell through to GTT.
-
Feature Interactions
G-Port, A-Port, and IS41 GSM Migration solve the problem of number portability from one network to another or number migration from one mobile protocol to another. One, two, or all three features could be active on a single EAGLE 5 ISS node at a given point. Because all of these features could have same type of MTP and SCCP layers (ITU or ANSI), it may look like same kind of message at service selection, which looks at the network domain and SCCP parameters. Therefore, all three features share one service. Because of this, existing functions like SRVSEL, Service, Re-route, CPC and rept-stat-sccp command service snapshot counts are affected.
Hardware Requirements
The A-Port feature has the following hardware requirements:
-
DSM cards with at least 4G of memory
-
A-Port cannot be enabled if any DSM cards with less than 4G of memory or any TSM cards for SCCP are present in the system. When A-Port is enabled, no DSM cards with less than 4G of memory and no TSM cards for SCCP can be provisioned for SCCP.
Assumptions
Within a portability domain (ordinarily a country) a Mobile Directory Number (MDN) assigned to an IS41 subscriber will not overlap with an MSISDN assigned to a GSM subscriber (one dialed DN can either be an IS41 or a GSM subscriber). Therefore, IS41 and GSM subscriber data can co-exist in the same EPAP provisioning database.
Limitations
The A-Port feature has the following limitations:
-
Communication between the SMSCs in the originating network (a calling party’s home network or the network where the call was originated) and the SMSC in the terminating network is through SS7 and not SMPP.
-
Number Portability across multiple countries is not supported.
2.61 ANSI-ITU-China SCCP Conversion (Release 31.3)
Since some ANSI and ITU SCCP parameters are incompatible in format and/or coding, subsequently the EAGLE has not historically supported SCCP traffic between ANSI and ITU networks. A specialized SCCP/TCAP conversion was previously implemented for MTP Routed UDT/UDTS messages. This feature will not interact with the Release 22.2 SCCP/TCAP conversion feature but will be mutually exclusive of it. Since the specialized SCCP/TCAP conversion was implemented, many improvements have been made to the EAGLE in regards to ITU SCCP compliance and features. (e.g. EGTT, MGTT). ANSI-ITU-China SCCP Conversion will provide a generic capability that will correctly format and decode/encode the following inter-network SCCP traffic:
-
UDT and UDTS messages - includes SCMG messages, which are a specialized form of a UDT
-
MTP routed
-
GT routed
The feature also provides SCCP management (SCMG) across network type boundaries, i.e. concerned point codes for a mated application may be of a different network type than the mated application.
UDTS message return is controlled inherently by the SCCP layer protocol within the protocol class byte. If bits 5-8 indicate return message on error, a UDTS message will be sent when there is an error. Otherwise, no UDTS is returned to the originator.
2.62 ANSI/ITU MTP Gateway (Release 20.0)
The EAGLE acts as a gateway to connect ANSI, ITU international, and ITU national networks. The EAGLE also continues to switch traffic that does not need to be converted when the origination network is the same network type as the destination network. In order to be able to perform these functions, the EAGLE does the following.
-
Discriminates between MSUs originating from each type of network
-
Converts MSUs to the appropriate format by converting the message transfer part (MTP) and ISDN user part
-
Routes MSUs to the correct destinations
Level 3 MSU Discrimination
The EAGLE must determine whether an incoming MSU terminates at the STP or must be routed to another destination. To accomplish the discrimination task, the EAGLE does the following.
-
Compares the network indicator (NI) of an MSU to a database of valid NIs. If the network indicator is not valid, the MSU is discarded.
-
Extracts the network indicator and destination point code (DPC) information from the incoming MSU. If an MSU is transmitted to an ANSI linkset, the network indicator is forced to a binary pattern of “10” before being extracted.
-
Determines whether an incoming MSU terminates at the EAGLE or must be routed to another destination by joining the network indicator and DPC to a list of self point codes. The self point code is a combination of the true point code and capability point code. The capability point code identifies a group of nodes that have similar capabilities.
MSU Routing
MSU routing occurs after MSU discrimination and before MSU conversion (if conversion is necessary). The EAGLE selects an outgoing link on which to transmit the MSU. The MSU formats must be compatible with the linksets that transmit the MSUs.
EAGLEs are typically deployed in mated pairs. The EAGLE has a linkset for each supported network type. The EAGLE should have a unique adjacent point code. The EAGLE supports up to three self point codes—one for ANSI point codes, one for ITU international point codes, and one for ITU national point codes.
Figure 2-6 shows a sample network with mated gateway STPs. Note that there are different linksets for each network type. In the sample, STP (A) has an ANSI point code (007-001-001), an ITU National point code (09270), and an International point code (5-060-1).
Figure 2-6 Sample Gateway STP Network

Administering Point Codes
The EAGLE can support multiple network types because each destination can be addressed by a true point code or by a list of alternate point codes. The list of alternate point codes contains from 0 to 2 alternates. The true point codes and alternate point codes are entered in the key table (by using the ent-dstn command). For example, an ANSI destination could have both a true point code and an alternate point code that point to the same routing translation in the routing table.
Local Link Congestion
When a link is congested, the EAGLE sends ANSI TFCs to the ANSI origination point code (OPC) and ITU TFCs to the ITU origination point code (OPC). Figure 2-7 shows both an ANSI and an ITU network sending traffic to a congested link (the type of congested link does not matter). When an ANSI node is the source of the traffic to the congested link, the TFC contains a status. When an ITU node is the source of the traffic, the TFC does not contain a status.
Figure 2-7 Traffic to and from a Congested Link

All links in the system operate with four levels of congestion. If the congestion level is “0”, there is no congestion, the EAGLE does not transmit TFCs, and no MSUs are discarded. At level 3 (indicating a maximum level of congestion), the EAGLE transmits TFCs, and discards MSUs.
Whenever the congestion onset status is above congestion onset level 1, and has not abated below congestion abatement level 1, the EAGLE generates a TFC. Whenever the congestion discard status is above discard level 1, and has not abated below discard level 1, the EAGLE discards the MSU. See Figure 2-8.
Figure 2-8 Congestion Levels

Remote Link Congestion
Table 2-11 shows the EAGLE’s response to remote congestion indicators.
Table 2-11 Remote Congestion Response
| Event | EAGLE’s Response |
|---|---|
|
EAGLE receives an ANSI TFC |
When the EAGLE receives an ANSI TFC, the routing table is modified to discard lower priority MSUs being routed to the concerned point code. The TFC contains the congestion status of the concerned point code. The routeset congestion test mechanism is used to abate the congestion. |
|
EAGLE receives an ITU TFC |
When the EAGLE receives an ITU TFC, the routing table is modified to discard the lower priority MSUs being routed to the concerned point code. The TFC does not contain the congestion status of the concerned point code. Instead, the congestion status is user-configurable using the |
|
EAGLE receives an ANSI RCT |
There is no change in the EAGLE response when the EAGLE receives ANSI routeset congestion test messages. |
|
EAGLE receives an ITU RCT |
The H0H1 message codes are not contained in the ITU environment. These codes generate an invalid H0H1 MRN, and the message is discarded. This has no impact on the ITU network because the EAGLE uses a timer to abate congestion and does not rely on a reply to the RCT message. |
2.63 ANSI/ITU SCCP and TCAP Conversion (Optional) (Release 22.2)
As an option for release 22.2, the ANSI/ITU SCCP and TCAP Conversion feature enables the EAGLE STP to convert MTP-routed SCCP and TCAP messages from ANSI to ITU format and to convert ITU formatted messages to ANSI. The following formatting and coding is supported:
-
MTP routed Unitdata (UDT) non-segmented SCCP connectionless messages, including SCMG messages.
-
MTP routed Unitdata Service (UDTS) messages (UDT messages returned due to error).
SCCP and TCAP conversion is turned on by way of two separate feature bits, one for the SCCP conversion and one for the TCAP conversion. The SCCP conversion feature must be turned on before, or at the same time as, the TCAP conversion feature.
2.64 ANSI/ITU SCCP and TCAP Conversion (Release 24.0)
As an option for release 24.0, the ANSI/ITU SCCP and TCAP Conversion feature enables the EAGLE STP to convert MTP-routed SCCP and TCAP messages from ANSI to ITU format and to convert ITU formatted messages to ANSI.
Note:
This feature is a customized feature and does not conform to any known standard or specification.
The following formatting and coding is supported:
-
MTP routed Unitdata (UDT) non-segmented SCCP connectionless messages, including SCMG messages.
-
MTP routed Unitdata Service (UDTS) messages (UDT messages returned due to error).
SCCP and TCAP conversion is turned on by way of two separate feature bits, one for the SCCP conversion and one for the TCAP conversion. The SCCP conversion feature must be turned on before, or at the same time as, the TCAP conversion feature.
2.65 ANSI/ITU SCCP Conversion – Optional Conversion of CgPA when Crossing ITU-x Domains (Release 45.0)
The SCCPOPTS:CNVCLGITU parameter makes the SCCP CgPA conversion optional for messages crossing ITU-x<->ITU-y domain. The default value of this parameter is off when the ANSI/ITU SCCP Conversion feature is turned on. In case of ITU-x<->ITU-y domain crossing, SCCP conversion will not be performed on CgPA. x and y are different variants of ITU networks: International, National, International Spare, and National Spare. ITU-x<->ITU-y SCCP CgPA conversion is optional for GTT, GTT Actions, GTMOD, and MAP SCRN. This does not apply to services and subsystem that perform GTT on CgPA, such as G-Port, EIR, and IDPR.
2.66 ANSI/ITU Translation (Release 35.0)
Description
The ANSI/ITU Translation feature allows any domain GTT selector to be assigned to a ‘cross’ domain GTT set. This allows access to GTA data within a GTT set that can be used to translate ANSI and ITU messages.
ANSI/ITU translation allows a user to provision a single cross domain GTT set with one set of GTA data and assign it to multiple GTT selectors, regardless of their domain. Since the user does not have to provision a GTT set with the same GTA data for each network domain GTT selector (gtia=2, gtii=2, gtii=4), GTA table space and user-provisioning activity is conserved.
The Enhanced GTT feature and ANSI-ITU-China SCCP Conversion feature must be on before the ANSI/ITU Translation feature can be enabled.
Hardware Requirements
The ANSI/ITU Translation feature has the following hardware requirements:
- Use of TSM or higher SCCP cards.
- LIM hardware types.
Limitations
The ANSI/ITU Translation feature has no associated limitations.
2.67 A-Port Circular Route Prevention (Release 41.1)
The existing MNP Circular Route Prevention feature is enhanced to provide the same functions for A-Port and IS41 messages as it currently provides for G-Port and GSM messages. A-Port Circular Route Prevention (A-Port CRP) detects and prevents circular routing for all messages that receive A-Port service, including LOCREQ and SMSREQ messages. The functions help to detect circular routing that is caused by incorrect information in number portability databases in one or more networks.
- If this called party number is a ported-out number (foreign subscriber), UIM 1256 “NP Circular Route detected” is generated and, depending on the GTT provisioning, either a UDTS is sent using SCCP information or the message is routed to a GT translated point code.
- If the number is a ported-in number (own network subscriber), the EAGLE 5 ISS relays the message directly to the HLR using the RTDB result information.
2.67.1 Feature Control Requirements
The GTT, A-Port, and MNP Circular Route prevention features must be enabled and turned on before circular route prevention can be performed for the A-Port feature.
2.67.2 Hardware Requirements
The A-Port feature requires Service Module cards (4G or higher DSM cards, E5-SM4G cards, or a mixture of both).
2.67.3 Limitations
Circular route conditions occur only for Other Licensed Operator (OLO) subscribers and not for migrated customers (who are still in their own network). Therefore, running the MNP Circular Route Prevention feature when only the IS41 GSM Migration (IGM) feature is on (A-Port or G-Port is not on) is not valid. Support for Circular Route Prevention when only the IGM feature is ON is already supported and will continue to exist only for ITU MAP messages.
2.68 ASM Obsolescence (Release 31.6)
The current Application Services Module (ASM) card is an aging board with limited functionality when compared with today's modern day processors. This feature removes ASM card support in EAGLE software. The ASM card currently supports only two application Generic Program Loads (GPLs), the Signaling Connection Control Part (SCCP) and Gateway Loading Services (GLS) applications. The TSM card already supports both of these applications. Supported GPLs by card type are shown in Table 2-12.
Table 2-12 GPL Support for ASM and TSM Cards
| GPL | ASM Card | TSM Card |
|---|---|---|
|
Before ASM Obsolescence |
||
|
GLS Application supported |
Yes |
Yes |
|
SCCP Application supported |
Yes |
Yes |
|
After ASM Obsolescence |
||
|
GLS Application supported |
No |
Yes |
|
SCCP Application supported |
No |
Yes |
Hardware Required
Any ASM cards in the system must be replaced with TSM cards before the Release 31.6 upgrade can occur.
Note:
Release 31.X baseline hardware includes GPSMIIs, HMUXs, -10s TDMs. If these modules are not equipped the act-upgrade command will be rejected.Limitations
-
Beginning with EAGLE software release 31.6, there will be no support for the ASM card and card type.
2.69 ATINP Service Portability (Release 41.1)
Service Portability support for the ATINP feature indicates whether Service Portability applies to ATI ACK messages for own-network subscribers. When Service Portability is applicable, and the atiackrn=rn parameter is provisioned, GRN digits are used to encode RN digits in the response message..
As part of the support for Service Portability, ATINP no longer considers the incoming MSISDN numbering plan; the numbering plan in the MSISDN in the ATI ACK message will be the same as the incoming MSISDN numbering plan.
2.70 ATI Number Portability Query (ATINP) (Release 39.2)
The ATINP feature is used to obtain number portability and routing information for a subscriber directly from the EAGLE 5 ISS number portability database. The feature allows a node to send a GSM MAP_Any_Time_Interrogation (ATI) query directly to the EAGLE 5 ISS (which supports the ATINPQ local subsystem) to obtain number portability and routing information for a mobile subscriber from the number portability database. This information is encoded in the ATI response message.
The ATINP feature supports RT-on-SSN and RT-on-GT messages to the EAGLE 5 ISS TSPC/ATINP CPC if the message criteria matches the SSN and service selectors, respectively, for ATINP. If an SCCP message arrives and matches the ATINP service selectors, then it is automatically forwarded to the ATINPQ local subsystem.
The ATINP feature supports ASD digits that are returned from the database lookup for an individual directory number (DN) or a range of DNs. If ASD digits are found in the lookup, then the digits are used to format the routing number, MSISDN, and IMSI entities in the outgoing response.
Note:
The ATINP feature must be turned on before full processing of an ATI message by the ATINPQ subsystem can be performed.2.70.1 Feature Control Requirements
The ATINP feature has the following feature control requirements:
- FAK for part number 893-0221-01
- The GTT feature bit must be turned on before the ATINP feature can be enabled.
- The defcc parameter for the
chg-stpoptscommand must have a value other than none. - The ATINP feature can be turned on and off.
- A temporary FAK cannot be used to enable the feature.
- The ATINP feature cannot exist on the same node as the LNP features.
2.71 Auto Point Code Recovery (Releases 35.6, 37.5)
The Auto Point Code Recovery feature enhances the ability of the EAGLE 5 ISS to handle circular routing that is caused by far-end loopback. The feature also automatically resets a destination point code (DPC) that has been marked as prohibited due to circular route detection (CRD).
The EAGLE 5 ISS detects far-end loopback in a link through the signaling link test control (SLTC) procedure. The originating point code (OPC) sends a signaling link test message (SLTM) across a link to the STP and expects a signaling link test acknowledgement (SLTA) from the STP. If far-end loopback occurs in the connecting link, then the OPC receives the same SLTM instead of an SLTA. The OPC marks the link as failed as soon as it receives the SLTM.
The circular route caused by the loopback can cause multiple MSUs to be returned to the OPC, which can increase the congestion level on the link and invoke CRD processing. CRD marks the link as failed and marks the DPCs as CRD-prohibited. After a link has been marked, the link cannot be used until the DPC is cleared.
The Auto Point Code Recovery feature consists of two separate features. Each feature addresses an aspect of far-end loopback and CRD.
- Enhanced Far-End Loopback Detection
The Enhanced Far-End Loopback Detection feature significantly decreases the time required to take a link out of service by failing a link as quickly as possible when an SLTM is received. The rapid failure prevents the EAGLE 5 ISS from marking DPCs as CRD-prohibited.
- Circular Route Auto-Recovery
The Circular Route Auto-Recovery feature automatically clears CRD when far-end loopback is detected, and the failing link is part of the linkset that detected the circular route. If the Circular Route Auto-Recovery feature is not enabled, the user must clear CRD manually by executing the
rst-dstncommand.
2.71.1 Feature Control Requirements
The Auto Point Code Recovery feature has the following feature control requirements:
- Separate FAKs are required to enable the Circular Route Auto-recovery and Enhanced Far-End Loopback Detection features.
- Circular Route Auto-Recovery feature: FAK for part number 893-0176-01
- Enhanced Far-End Loopback Detection feature: FAK for part number 893-0181-01
- The Enhanced Far-End Loopback Detection and Circular Route Auto-Recovery features can be enabled separately.
- The Enhanced Far-End Loopback Detection and Circular Route Auto-Recovery features can be turned on and off.
- Temporary FAKs cannot be used to enable the Enhanced Far-End Loopback Detection or Circular Route Auto-Recovery features.
- SLTMs must be enabled (
chg-sltcommand) before the Enhanced Far-End Loopback Detection or Circular Route Auto-Recovery feature can operate.
2.71.3 Limitations
When this feature is implemented, the capacity limits for combinations of DN/IMSI will be less than what is supported today.
- Existing limit: {DN, IMSI} = {36M, 60M}, {12M, 82M} and {6M, 90M}
- New limit for EPAP 10.0: {DN, IMSI} = {36M, 52M}, {12M, 75M} and {6M, 82M}
This decrease in capacity is based on high-level engineering design for the feature. Since these combinations are not used in the field, this limitation does not affect any customers.
2.72 Automatic PDB and RTDB Backup (EPAP 7.0)
Description
The Automatic PDB/RTDB Backup feature allows for the scheduling of automated backups of EPAP PDBs and RTDBs. The PDB backup copy is created on the EPAP A server and the RTDB backup copy is created on the standby EPAP server (A or B). A specific destination for the backup copy can be configured at the users discretion.
From the EPAP GUI terminal (Web UI only), the user can access a graphical user interface screen and configure the time, frequency, and destination of the backup copy.
Tekelec recommends that an Automatic PDB/RTDB Backup be performed on a daily (24 hour) basis. Both the PDB and RTDB backups are scheduled together and cannot be scheduled separately. The Time of the day to Start The Backup is the time that the RTDB backup starts. The PDB backup automatically starts 1 hour later.
Backups can only be scheduled and created on a provisionable EPAP server pair. An automatic PDB/RTDB backup is not allowed and cannot be scheduled on a non-provisionable EPAP server pair.
Normal provisioning is allowed during the automatic PDB/RTDB backup. This includes provisioning from
-
the customer network to the PDB,
-
the PDB to the Active EPAP RTDB, and
-
the Active EPAP RTDB to the DSM RTDB.
RTDB backups are always created from the standby EPAP RTDB (A or B). The RTDB can resume receiving updates when it is brought back on line.
Disk Space Limitations
This feature supports the retention of three backup copies of the PDB and RTDB databases. However, the disk space in the EPAP free directory may not be sufficient to accommodate the retention of three backup copies on sites with large PDB and RTDB databases. When insufficient disk space exists, a dialog box appears asking the user “Do you want to delete the old backups”.
-
If yes, the new database backup copy is written over the previous version.
-
If no, the user must create a directory in a location with sufficient disk space and then specify the location of the backup directory to create the backup copy in.
Automatic PDB/RTDB Backup Screen
This feature adds to the list of EPAP Maintenance menu options, the item “Automatic PDB/RTDB Backup”. The scheduled time, frequency, and destination of the backup file can be configured by the user from the Automatic PDB/RTDB Backup screen.
Figure 2-9 Automatic PDB/RTDB Backup screen.
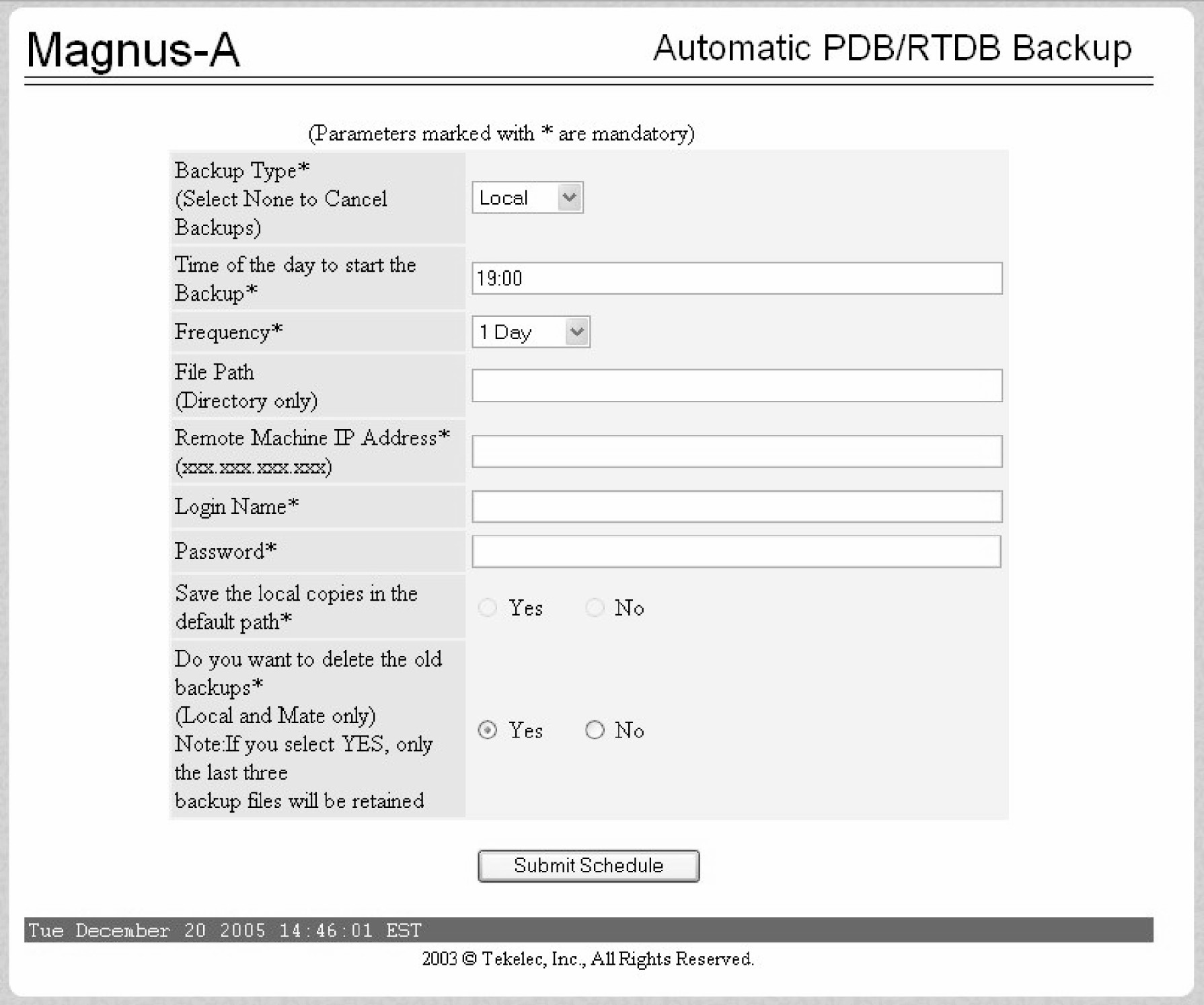
Most of the input parameters are self explanatory. The following options are configurable by the user:
The frequency of the backup copy can be any of the following increments:
-
12 hours (see Note below)
-
1 Day (daily)
-
2 Days
-
3 Days
-
5 Days
-
7 Days
The Backup Type parameter is the destination for the backup file:
-
Local - A backup copy of the data is saved to the local disk on the same EPAP server as the PDB/RTDB being backed up.
-
Mate - A backup copy of the data is created on the local server and then sent via SCP to the mate EPAP server.
-
Remote - A backup copy of the data file is created on the local EPAP server and then sent via SFTP to a remote server configured by the user. This server may or may not run EPAP software and can be any machine on the network that is running an SFTP daemon or service.
-
None - No backup is scheduled and cancel all previously scheduled backups. This will not affect a backup that is currently in progress.
The following table can be used as a guide when scheduling the Automatic PDB/RTDB Backup.
Table 2-13 Mandatory verses Optional Parameters
| Parameter | Automatic PDB/RTDB Backup Type | ||
|---|---|---|---|
| Local | Mate | Remote | |
|
Time of day to start backup |
Mandatory |
Mandatory |
Mandatory |
|
Frequency |
Mandatory |
Mandatory |
Mandatory |
|
File Path |
Optional |
Optional |
Mandatory |
|
Remote Machine IP Address |
N/A |
N/A |
Mandatory |
|
Login Name |
N/A |
N/A |
Mandatory |
|
Password |
N/A |
N/A |
Mandatory |
|
Save the Local copies in the default path |
N/A |
Optional |
Mandatory |
|
Do you want to delete the old backups Note: If you choose Yes, only the last three backup files, including the current one are kept. |
Mandatory |
Mandatory |
N/A |
The default file path where subdirectories are created (on the mate and local servers) is /var/TKLC/epap/free/
Table 2-14 Backup File Default Filenames
|
PDB |
pdbBackup_<hostname>_<CurrentTime>_DBBirthdate_<DBBirthdate>_DBLevel_<level>.bkp.tar.gz |
|
RTDB |
rtdbBackup_<hostname>_<CurrentTime>.tar.gz |
2.73 Automatic PDB Export Enhancement (EPAP 9.0)
Description
The Automatic PDB Export Enhancement feature provides more flexible scheduling for automatic PDBA exports.
With more options to choose from, scheduling an automatic PDB export is now very similar to the way tasks or appointments can be scheduled in a calendar manager.
In addition to the previously available choices for export format, mode, and data type, these enhancements allow the user to:
- View, modify, or delete existing reports
- Choose from multiple options for the frequency of the export:
- Daily
- Weekly
- Monthly
- Yearly
- Choose the time of day to start the export
- Add comments to describe the export
Hardware Requirements
None.
Limitations
None.
2.74 Backup Provisioning Network Interface (Release 29.0)
Currently, the MPS machines only make use of one interface to the customer network. There is an unused interface (QFE3) available. This feature allows for the configuring of a second interface to the customer network. This second interface must exist on a different subnet than the primary (HME0) interface. The customer can then use either interface to communicate with the MPS (WebUI, PDBI, telnet, etc).
Note:
It is important to note that this backup interface could also be used for Versant's FTS replication, in the event that something is wrong with the HME0 path. However, this switch is not automatic. A user would have to manually make the change through the configuration text UI at both sites.Hardware Requirements
No new hardware is needed to support this feature.
2.75 Calling Name Conversion Facility (CNCF) (Release 23.1)
This feature provides a conversion of ISUPIAM messages using two versions of calling name identification presentation (CNIP) for calling name information delivery. One version of the CNIP uses the nonstandard, proprietary ISUP party information (PIP) parameter. The other version uses the ANSI standard ISUP generic name (GN) parameter. The conversion will either replace the PIP parameter with the GN parameter or the GN parameter with the PIP parameter in the ISUPIAM message.
The gateway screening feature is used to select which ISUP messages are converted. The incoming messages are selected based on the OPC and DPC in the routing label of the message, and the message type in the service information octet. The message type is defined by the value of the service indicator (SI) field of the SIO. ISUP messages contain the value 5 in the service indicator field of the SIO. Screening rules for Allowed OPC, Allowed DPC, and the Allowed SIO entities must be configured in the database for this feature. The redirect=yes parameter must be specified with the last entity in the screening process (nsfi=stop) to use the CNCF feature to convert the message.
This feature is an optional feature and must be turned on with the chg-feat command and the new parameter, cncf=on. Before this feature can be turned on, the gateway screening feature must be on. This is shown by the entry GWS = on in the output of the rtrv-feat command. If the gateway screening feature is not on when an attempt is made to turn the CNCF feature on, the chg-feat command is rejected with this message:
Error Message
E3646 Cmd Rej: GWS must be ON before CNCF can be ON
The rtrv-feat command output has been changed to add the CNCF field showing whether the CNCF feature is on or not.
If the CNCF feature is turned on, the DTA feature is disabled. There are no other command changes to support this feature.
Figure 2-10 shows an example network that contains these two separate ISUP versions. Based on this example, Table 2-16 shows when the ISUPIAM message conversion by the CNCF feature occurs.
Figure 2-10 PIP/GN Parameter Conversion

Table 2-15 ISUP IAM Message Conversion Examples
| Origination Point Code | Destination Point Code | ISUPIAM Message Conversion |
|---|---|---|
|
001-002-003 |
004-005-006 |
Yes |
|
001-002-003 |
007-008-009 |
No |
|
004-005-006 |
001-002-003 |
Yes |
|
004-005-006 |
007-008-009 |
Yes |
|
007-008-009 |
001-002-003 |
No |
|
007-008-009 |
004-005-006 |
Yes |
Caution:
Take care when configuring the gateway screening rules for this feature. The CNCF feature has no way to validate the gateway screening rules to detect errors in converting messages between compatible networks. For example, using the example network in Figure 2-10, the ISUP IAM message traffic from node 001-002-003 to node 007-008-009 does not need to be converted because they are using the same calling name delivery parameter, PIP. If the gateway screening rules are not carefully configured, these messages could be converted when they do not need to be.
Limitations
No measurements are collected showing the number of MSUs converted by this feature.
No error message is generated if an error occurs during the conversion of the PIP and GN parameters.
If the CNCF feature is turned on, the DTA feature is disabled. No message redirection using the DTA feature will be performed.
If the copy=yes parameter is specified with the redirect=yes parameter, the MSU is copied for the STP LAN feature after it has been converted by the CNCF feature.
If there are multiple PIP parameters or GN parameters with calling name information within a single ISUPIAM, only the first occurrence of the parameter in the ISUPIAM message is converted.
Messages on X.25 linksets cannot be converted with the CNCF feature.
Only GNIAM messages containing calling name information (Type of Name = Calling Name, Presentation = Allowed, Parameter Length >1) are converted to PIPIAM messages.
Only PIPIAM messages containing Calling Name Information (Sub-Parameter Code = Name Information, Name Element Indicator = Calling Party) are converted to GNIAM messages.
If the received IAM message contains both a GN and a PIP parameter with calling name information, the GN parameter is retransmitted and the PIP parameter is deleted.
Any MSU that is not converted is simply retransmitted. These MSUs include non-ISUPMSUs, non-IAMMSUs, and any IAMMSU received that does not contain either a GN or PIP parameter.
If the PIP parameter contains other information in addition to the calling party name information, only a GN parameter containing calling party name information is generated.
The linkset being screened for this feature should not contain C links (lst=c parameter of the ent-ls and chg-ls commands). This would result in the double conversion of the ISUPIAM messages.
IAM messages containing a GN parameter that are to be converted, must be 262 bytes or less. The ANSISS7MSU can contain a maximum of 272 bytes, including the Level 3 routing label. Without the routing label, the MSU can contain 265 bytes, starting at the Circuit ID code field. Since the PIP parameter has 3 bytes more than the GN parameter, the MSU can contain a maximum of 262 bytes.
Table 2-16 summarizes the conversion action performed based on the optional parameters found within the MSU.
Table 2-16 CNCF Conversion Actions
| PIP Parameter Content | GN Parameter Content | ||
|---|---|---|---|
| GN Parameter with Calling Name Information | GN Parameter without Calling Name Information | GN Parameter Not Found | |
|
PIP Parameter with Calling Name Information |
The PIP parameter is deleted. The GN parameter is retransmitted without conversion. No network-specific parameters (0xFD and 0xFE) are deleted. |
The PIP parameter is converted to a GN parameter. The GN parameter is retransmitted if it is present. Network-specific parameters (0xFD and 0xFE) are deleted. |
The PIP parameter is converted to a GN parameter. The GN parameter is retransmitted if it is present. Network-specific parameters (0xFD and 0xFE) are deleted. |
|
PIP Parameter without Calling Name Information |
The PIP parameter is deleted. The GN parameter is retransmitted without conversion. No network-specific parameters (0xFD and 0xFE) are deleted. |
The PIP parameter is deleted. The GN parameter is retransmitted if it is present. Network-specific parameters (0xFD and 0xFE) are deleted. |
The PIP parameter is deleted. The GN parameter is retransmitted if it is present. Network-specific parameters (0xFD and 0xFE) are deleted. |
|
PIP Not Found |
The PIP parameter is not involved. The GN parameter is converted to PIP. No network-specific parameters (0xFD and 0xFE) are deleted. |
No parameters are converted. No parameters are deleted. |
No parameters are converted. No parameters are deleted. |
|
Note: Parameters with calling name information have precedence over parameters without calling name information. For example, an MSU that has both a GN parameter with calling name information and a GN parameter without calling name information is treated as if it were an MSU with a GN parameter with calling name information. |
|||
PIP and GN Parameters
The PIP format contains a parameter name (0xFC), parameter length and optional sub-parameters. The format is shown in Table 2-17. The Name Element Indicator, Name Element Length and Name Information fields can be repeated within a single PIP.
Table 2-17 PIP Parameter Format
| Field | Length | Bits Value HGFEDCBA | Comments |
|---|---|---|---|
|
Parameter Name |
1 octet |
1111 1100 |
Party Information |
|
Parameter Length |
1 octet |
— |
Length of the parameter excluding the parameter name and the parameter length octet |
|
Sub-Parameter Code |
1 octet |
1111 1110 |
Name Information |
|
Sub-Parameter Length |
1 octet |
— |
Sum of the number of octets in the Name Element Indicator, Name Element Length, and Name Information fields |
|
Name Element Indicator |
1 octet |
0000 0001 |
Calling party name |
|
0000 0010 |
Connected party name |
||
|
0000 0011 |
Redirecting party name |
||
|
Name Element Length |
1 octet |
— |
Number of characters in the name information field (maximum of 15) |
|
Name Information |
up to 15 octets |
— |
Maximum of 15 IA5 characters |
The GN format contains a parameter name (0xC7), parameter length and up to 16 additional octets. The format is shown in Table 2-18.
Table 2-18 GN Parameter Format
| Field | Bits Value HGFEDCBA | Comments | |
|---|---|---|---|
|
Parameter Name |
1100 0111 |
Generic Name |
|
|
Parameter Length |
— |
Length of the parameter excluding the parameter name and length fields |
|
|
Octet 1 |
Presentation |
XXXXXX00 |
Presentation Allowed |
|
XXXXXX01 |
Presentation Restricted |
||
|
XXXXXX10 |
Blocking Toggle |
||
|
XXXXXX11 |
No indication |
||
|
Spare |
XXXX 00XX |
Not Used |
|
|
Availability |
XXX0XXXX |
Name available or name availability unknown |
|
|
XXX1XXXX |
Name not available |
||
|
Type of name |
000X XXXX |
Spare |
|
|
001X XXXX |
Calling name |
||
|
010X XXXX |
Original called name |
||
|
011X XXXX |
Redirecting name |
||
|
100X XXXX |
Connected name |
||
|
101X XXXX to 111X XXXX |
Spare |
||
|
Octets 2-n |
— |
Maximum of 15 IA5 characters |
|
Conversion of PIP to GN
The mapping of PIP parameters to GN parameters for this conversion is shown in Figure 2-11. The new GN parameter length field is computed based on the PIP name element length and not the PIP parameter length or Sub-Parameter length fields.
Figure 2-11 PIP to GN Parameter Mapping

Conversion of GN to PIP
The mapping of GN parameters to PIP parameters for this conversion is shown in Figure 2-12.
Figure 2-12 GN to PIP Parameter Mapping

Table 2-19 shows how the PIP and GN parameters are mapped during the conversion process.
Table 2-19 PIP/GN Parameter Mapping
| Party Information Parameter | Generic Name Parameter | ||
|---|---|---|---|
| Field Name | Value | Field Name | Value |
|
Parameter Name |
Party Information (0xFC) |
Parameter Name |
Generic Name (0xC7) |
|
Parameter Length |
as calculated |
Parameter Length |
as calculated |
|
Sub-Parameter Code |
Name Information (0xFE) |
— |
no mapping |
|
Sub-Parameter Length |
as calculated |
— |
no mapping |
|
Name Element Indicator |
Calling Party Name (1) |
Type of Name |
Calling Name (HGF=001) |
|
— |
no mapping |
Presentation |
Allowed (BA=0) |
|
— |
no mapping |
Availability |
Name Available (E=0) |
|
Name Element Length |
as calculated |
— |
no mapping |
|
Name Information |
Calling Party Name (maximum 15 characters) |
Characters |
Calling Party Name (maximum 15 characters) |
Message Conversion
The conversion process only occurs in ISUP Initial Address Messages (IAM) with either the PIP or GN optional parameters that contain calling party name information. The conversion either replaces PIP parameters with GN parameters or GN parameters with PIP parameters. In some cases, network-specific optional parameters are also deleted from the message. The Level 2 Length Indicator is also updated since the MSU length is changing. The sections shown in bold type show which fields of an IAM with the GN parameter are effected by the CNCF feature.
Output Example
Protocol Flavor: ANSI-SS7
Total Message Length: 56
*** Start of MTP Level 2 ***
MTP
000 00000000 00
-0000000 Backward Sequence Number 0
0------- Backward Indicator Bit 0
001 00000000 00
-0000000 Forward Sequence Number 0
0------- Forward Indicator Bit 0
002 00110101 35
--110101 Length Indicator 53
00------ Spare 0
*** Start of MTP Level 3 ***
MSU
003 10000101 85
----0101 Service Indicator 0101 - ISDN User Part
--00---- Network Priority 00 - priority 0
10------ Network Indicator 10 - National Network
004 00000110 06 Destination Point Code 4-5-6
005 00000101 05
006 00000100 04
007 00000011 03 Origination Point Code 1-2-3
008 00000010 02
009 00000001 01
010 00000000 00 Signaling Link Selection 0
*** Start of ISDN User Part ***
Initial address Message
011 00000000 00 Circuit Identification Code 0
012 00000000 00
--000000
00------ Spare 0
013 00000001 01 Message Type 01
Nature of connection indicators
014 00000000 00
------00 Satellite Indicator 00 - no satellite in the connection
----00-- Continuity check indicator 00 - continuity check not required
---0---- Echo Control Device Indicator 0 - outgoing half echo cntrl dev not inc
000----- Spare 0
Forward call indicators
015 00000000 00
-------0 Incoming International Call Indicator 0 - not an incoming international call
-----00- End-to-End Method Indicator 00 - no end-to-end method available
----0--- Interworking Indicator 0 - no interworking encountered -all SS7
---0---- IAM Segmentation Indicator 0 - no indication
--0----- ISDN User Part Indicator 0 - ISDN user part not used all the way
00------ ISDN User Part Preference Indicator 00 - ISDN-UP preferred all the way
016 00000000 00
-------0 ISDN Access Indicator 0 - originating access non-ISDN
-----00- SCCP Method Indicator 00 - no indication
----0--- Spare 0
0000---- Reserved for National Use 0
Calling party's category
017 00000010 02 Calling party's category 00000010 - operator, language English
Variable Portion
018 00000011 03 User service information Pointer Offset 021
019 00000101 05 Called party number Pointer Offset 024
020 00010001 11 Optional Portion Pointer Offset 037
User service information
021 00000010 02 User service information Length 2
Octet 3
022 11000000 c0
---00000 Information transfer capability 00000 - speech
-10----- Coding Standard 10 - national standard
1------- Extension 01
Octet 4
023 10010000 90
---10000 Information transfer rate 10000 - 64 kbit/s
-00----- Transfer mode 00 - circuit mode
1------- Extension 4 Excluded
User information layers
Called party number
024 00001100 0c Called party number Length 12
025 00000011 03
-0000011 Nature of address indicator national (significant) number
0------- Odd/even indicator 0 - even number of address signals
Octets 2-10
026 00010000 10
----0000 Spare 00
-001---- Numbering plan 001 - ISDN(Telephony) numbering plan
0------- Spare 00
027 00100001 21 Address 12345678901234567890
028 01000011 43
029 01100101 65
030 10000111 87
031 00001001 09
032 00100001 21
033 01000011 43
034 01100101 65
035 10000111 87
036 00001001 09
Optional Portion
Generic Name
037 11000111 c7 Generic Name Type 199
038 00010000 10 Generic Name Length 16
039 00100000 20
------00 Presentation 00 - Presentation Allowed
----00-- Spare 00
---0---- Availability 0 - Name available, or unknown
001----- Type of Name 01
040 01000001 41 NAME ABCDEFGHIJKLMNO
041 01000010 42
042 01000011 43
043 01000100 44
044 01000101 45
045 01000110 46
046 01000111 47
047 01001000 48
048 01001001 49
049 01001010 4a
050 01001011 4b
051 01001100 4c
052 01001101 4d
053 01001110 4e
054 01001111 4f
055 00000000 00 End of optional parameters 00
The sections shown in bold type show which fields of an IAM with the PIP parameter are effected by the CNCF feature.
Output Example
Protocol Flavor: ANSI-SS7
Total Message Length: 59
*** Start of MTP Level 2 ***
MTP
000 00000000 00
-0000000 Backward Sequence Number 0
0------- Backward Indicator Bit 0
001 00000000 00
-0000000 Forward Sequence Number 0
0------- Forward Indicator Bit 0
002 00111000 38
--111000 Length Indicator 56
00------ Spare 0
*** Start of MTP Level 3 ***
MSU
003 10000101 85
----0101 Service Indicator 0101 - ISDN User Part
--00---- Network Priority 00 - priority 0
10------ Network Indicator 10 - National Network
004 00000110 06 Destination Point Code 4-5-6
005 00000101 05
006 00000100 04
007 00000011 03 Origination Point Code 1-2-3
008 00000010 02
009 00000001 01
010 00000000 00 Signaling Link Selection 0
*** Start of ISDN User Part ***
Initial address Message
011 00000000 00 Circuit Identification Code 0
012 00000000 00
--000000
00------ Spare 0
013 00000001 01 Message Type 01
Nature of connection indicators
014 00000000 00
------00 Satellite Indicator 00 - no satellite in the connection
----00-- Continuity check indicator 00 - continuity check not required
---0---- Echo Control Device Indicator 0 - outgoing half echo cntrl dev not inc
000----- Spare 0
Forward call indicators
015 00000000 00
-------0 Incoming International Call Indicator 0 - not an incoming international call
-----00- End-to-End Method Indicator 00 - no end-to-end method available
----0--- Interworking Indicator 0 - no interworking encountered -all SS7
---0---- IAM Segmentation Indicator 0 - no indication
--0----- ISDN User Part Indicator 0 - ISDN user part not used all the way
00------ ISDN User Part Preference Indicator 00 - ISDN-UP preferred all the way
016 00000000 00
-------0 ISDN Access Indicator 0 - originating access non-ISDN
-----00- SCCP Method Indicator 00 - no indication
----0--- Spare 0
0000---- Reserved for National Use 0
Calling party's category
017 00000010 02 Calling party's category 00000010 - operator, language English
Variable Portion
018 00000011 03 User service information Pointer Offset 021
019 00000101 05 Called party number Pointer Offset 024
020 00010001 11 Optional Portion Pointer Offset 037
User service information
021 00000010 02 User service information Length 2
Octet 3
022 11000000 c0
---00000 Information transfer capability 00000 - speech
-10----- Coding Standard 10 - national standard
1------- Extension 01
Octet 4
023 10010000 90
---10000 Information transfer rate 10000 - 64 kbit/s
-00----- Transfer mode 00 - circuit mode
1------- Extension 4 Excluded
User information layers
Called party number
024 00001100 0c Called party number Length 12
025 00000011 03
-0000011 Nature of address indicator national (significant) number
0------- Odd/even indicator 0 - even number of address signals
Octets 2-10
026 00010000 10
----0000 Spare 00
-001---- Numbering plan 001 - ISDN(Telephony) numbering plan
0------- Spare 00
027 00100001 21 Address 12345678901234567890
028 01000011 43
029 01100101 65
030 10000111 87
031 00001001 09
032 00100001 21
033 01000011 43
034 01100101 65
035 10000111 87
036 00001001 09
Optional Portion
Party Information Parameter
037 11111100 fc Party Information Parameter Type 252
038 00010011 13 Party Information Parameter Length 19
039 11111110 fe Sub-Parameter Code 254 - Name Information
040 00010001 11 Sub-Parameter Length 17
041 00000001 01 Name Element Indicator 01 - Calling Party Name
042 00001111 0f Name Element Length 15
043 01000001 41 Name Information ABCDEFGHIJKLMNO
044 01000010 42
045 01000011 43
046 01000100 44
047 01000101 45
048 01000110 46
049 01000111 47
050 01001000 48
051 01001001 49
052 01001010 4a
053 01001011 4b
054 01001100 4c
055 01001101 4d
056 01001110 4e
057 01001111 4f
058 00000000 00 End of optional parameters 00
2.76 Calling Name Conversion Facility (CNCF) with Redirect Capability (Release 24.0)
Description
This feature provides a conversion of ISUP IAM messages using two versions of calling name identification presentation (CNIP) for calling name information delivery. One version of the CNIP uses the nonstandard, proprietary ISUP party information (PIP) parameter. The other version uses the ANSI standard ISUP generic name (GN) parameter. The conversion will either replace the PIP parameter with the GN parameter or the GN parameter with the PIP parameter in the ISUP IAM message.
The gateway screening feature is used to select which ISUP messages are converted. The incoming messages are selected based on the OPC and DPC in the routing label of the message, and the message type in the service information octet. The message type is defined by the value of the service indicator (SI) field of the SIO. ISUP messages contain the value 5 in the service indicator field of the SIO. Screening rules for Allowed OPC, Allowed DPC, and the Allowed SIO entities must be configured in the database for this feature.
Refer to the Database Administration Manual - Gateway Screening for details on using this feature.
Unsolicited Information Messages
The commands chg-scr-aftpc, chg-scr-cdpa, chg-scr-cgpa, chg-scr-tt, ent-scr-aftpc, ent-scr-cdpa, ent-scr-cgpa, and ent-scr-tt cannot use any entry shown in the rtrv-gws-actset command output that contains the redirect stop action (RDCT) or the CNCF stop action (CNCF). This restriction is not enforced when the chg-gws-actset and the chg-scr-aftpc, chg-scr-cdpa, chg-scr-cgpa, chg-scr-tt, ent-scr-aftpc, ent-scr-cdpa, ent-scr-cgpa, and ent-scr-tt commands are entered into the database. The database will accept these commands using entries from the gateway screening stop action table, but when the EAGLE encounters MSUs that pass gateway screening at the AFTPC, CDPA, CGPA or TT screens, these UIMs (unsolicited information messages) are generated indicating that gateway screening received a MSU that could not be redirected or converted.
UIM 1125 – Gateway Screening received a Called Party Address that could not be Redirected for the DTA feature
RLGHNCXA03W 99-01-07 00:57:31 EST Rel 24.0.0
1001.1125 CARD 1103,A INFO GWS rcvd CDPA that could not be RDCTd
SIO=03 OPC=001-001-001 DPC=002-002-002
SCCP MT= 18
CDPA: AI=10 PC=003-003-003 SSN=005 TT=250 ADDR=1234567890
CGPA: AI=10 PC=004-004-004 SSN=005 TT=251 ADDR=1234567890
SR=scrb LSN=A1234567
Report Date: 98-09-07 Time: 16:27:19
UIM 1126 – Gateway Screening received a Calling Party Address that could not be Redirected for the DTA feature
RLGHNCXA03W 99-01-07 00:57:31 EST Rel 24.0.0
1002.1126 CARD 1103,A INFO GWS rcvd CGPA that could not be RDCTd
SIO=03 OPC=001-001-001 DPC=002-002-002
SCCP MT= 18
CDPA: AI=10 PC=003-003-003 SSN=005 TT=250 ADDR=1234567890
CGPA: AI=10 PC=004-004-004 SSN=005 TT=251 ADDR=1234567890
SR=scrb LSN=A1234567
Report Date: 98-09-07 Time: 16:27:19
UIM 1127 – Gateway Screening received an Affected Point Code that could not be Redirected for the DTA feature
RLGHNCXA03W 99-01-07 00:57:31 EST Rel 24.0.0
1003.1127 CARD 1103,A INFO GWS rcvd AFTPC that could not be RDCTd
SIO=03 OPC=001-001-001 DPC=002-002-002
SCCP MT= 18
CDPA: AI=10 PC=003-003-003 SSN=005 TT=250 ADDR=1234567890
CGPA: AI=10 PC=004-004-004 SSN=005 TT=251 ADDR=1234567890
SR=scrb LSN=A1234567
Report Date: 98-09-07 Time: 16:27:19
UIM 1128 – Gateway Screening received a Translation Type that could not be Redirected for the DTA feature
RLGHNCXA03W 99-01-07 00:57:31 EST Rel 24.0.0
1004.1128 CARD 1103,A INFO GWS rcvd TT that could not be RDCTd
SIO=03 OPC=001-001-001 DPC=002-002-002
SCCP MT= 18
CDPA: AI=10 PC=003-003-003 SSN=005 TT=250 ADDR=1234567890
CGPA: AI=10 PC=004-004-004 SSN=005 TT=251 ADDR=1234567890
SR=scrb LSN=A1234567
Report Date: 98-09-07 Time: 16:27:19
UIM 1215 – Gateway Screening received a Called Party Address that could not be processed by the Calling Name Conversion Facility feature
RLGHNCXA03W 99-01-07 00:57:31 EST Rel 24.0.0
1005.1215 CARD 1103,A INFO GWS rcvd CDPA that could not be CNCFd
SIO=03 OPC=001-001-001 DPC=002-002-002
SCCP MT= 18
CDPA: AI=10 PC=003-003-003 SSN=005 TT=250 ADDR=1234567890
CGPA: AI=10 PC=004-004-004 SSN=005 TT=251 ADDR=1234567890
SR=scrb LSN=A1234567
Report Date: 98-09-07 Time: 16:27:19
UIM 1216 – Gateway Screening received a Calling Party Address that could not be processed by the Calling Name Conversion Facility feature
RLGHNCXA03W 99-01-07 00:57:31 EST Rel 24.0.0
1006.1216 CARD 1103,A INFO GWS rcvd CGPA that could not be CNCFd
SIO=03 OPC=001-001-001 DPC=002-002-002
SCCP MT= 18
CDPA: AI=10 PC=003-003-003 SSN=005 TT=250 ADDR=1234567890
CGPA: AI=10 PC=004-004-004 SSN=005 TT=251 ADDR=1234567890
SR=scrb LSN=A1234567
Report Date: 98-09-07 Time: 16:27:19
UIM 1217 – Gateway Screening received an Affected Point Code that could not be processed by the Calling Name Conversion Facility feature
RLGHNCXA03W 99-01-07 00:57:31 EST Rel 24.0.0
1007.1217 CARD 1103,A INFO GWS rcvd AFTPC that could not be CNCFd
SIO=03 OPC=001-001-001 DPC=002-002-002
SCCP MT= 18
CDPA: AI=10 PC=003-003-003 SSN=005 TT=250 ADDR=1234567890
CGPA: AI=10 PC=004-004-004 SSN=005 TT=251 ADDR=1234567890
SR=scrb LSN=A1234567
Report Date: 98-09-07 Time: 16:27:19
UIM 1218 – Gateway Screening received a Translation Type that could not be processed by the Calling Name Conversion Facility feature
RLGHNCXA03W 99-01-07 00:57:31 EST Rel 24.0.0
1008.1218 CARD 1103,A INFO GWS rcvd TT that could not be CNCFd
SIO=03 OPC=001-001-001 DPC=002-002-002
SCCP MT= 18
CDPA: AI=10 PC=003-003-003 SSN=005 TT=250 ADDR=1234567890
CGPA: AI=10 PC=004-004-004 SSN=005 TT=251 ADDR=1234567890
SR=scrb LSN=A1234567
Report Date: 98-09-07 Time: 16:27:19
In order to stop these UIMs from being generated, the gateway screening rule shown in the UIM must be identified. Once the gateway screening rule has been identified, a gateway screening change command can be used either to remove the gateway screening action set name or change the gateway screening action set name to a different gateway screening action set not containing the CNCF or redirect gateway screening stop actions. The gateway screening stop action set can also be changed with the chg-gws-actset command to remove the redirect or CNCF gateway screening stop actions. However, this could keep other gateway screening rules from redirecting or converting MSUs passing gateway screening from the BLKOPC, BLKDPC, SIO, OPC, DPC, or DESTFLD screens.
2.77 CDU for DSM (Release 26.05)
CDU (CAP Downloadable Utility) is an existing software platform for diagnostics used by manufacturing in identifying and isolating expansion memory problems in the EAGLE cards quickly and reliably. This feature ports the existing CDU and provides an efficient “go/no go” memory test for the DSM/DCM card.
CDU Port
The existing CDU utility has been ported for the DSM/DCM card, and a new GPL VCDU has been created. The new GPL has all the existing functionality. The DSM board can hold up to 4GB of memory. The CDU or the VCDU utility is downloaded automatically, depending on the type of the board. For the DSM, the VCDU utility is downloaded; for the other boards, the CDU utility is downloaded.
The CDU or the VCDU can be downloaded into any card with the following command:
alw-card:loc=xxxx:code=utility
The following act-memtst command used with the parameter set to "fast" lets the VCDU utility test 4GB of memory in 4 hours:
cdu:loc=xxxx:cmd=
" ACT-MEMTST:BEG=H'100000:END=H'200000 :TYPE=FAST
"
Quick Test
The quick go/no go test is implemented with the ACT-QCKTST command in CDU/VCDU. Using this command, the VCDU utility can check the basic integrity of the memory within 10 minutes. This test includes verifying the address and data lines to the memory, and verifying accessibility of each memory chip of 4GB.
Ping Test
The VCDU utility uses a new command, act-pingtst, to test the network. The ping test applies to the DCM/DSM card only.
cdu:loc=xxxx:cmd=
" act-pingtst:port=<a/b>:dest=<ip_address> :router=<router>:loop=n
"
This command activates the ping test. The port parameter specifies the origination address. The dest parameter specifies the destination address to be pinged. The router parameter is an optional parameter that specifies the router through which the network interface can be tested. The loop parameter specifies the number of times the test should be run before termination.
2.78 CgPA GWS Routing Indicator Enhancement (Release 31.3)
The wildcarding of the CgPA routing indicator (RI=*) produced 2 entries in the GWS database on the LIM card; that reduced the number of CgPA rules available to the customer from 4000 to 2000 per screenset.
The wildcarding has been changed to produce a single database entry for wildcard (*) of the routing indicator in CgPA GWS screening rules. The EAGLE does not expand the provisioned wildcard routing indicator into multiple rules in the bound screenset.
Upgrade to Release 31.3 auto consolidates existing entries that were provisioned with RI=*.
2.79 Change Default ATM CLP Bit for Data Cells from 1 to 0 (Release 31.3)
The Cell Loss Priority (CLP) bit is in the ATM packet header and is used by ATM network elements to determine which messages are discarded when an ATM network element is in congestion. Should there be congestion in an ATM network element, it will first start to discard ATM packets with a CLP bit of 1 first before discarding any ATM packets with a CLP bit of 0. The CLP bit has the following characteristics:1. The CLP bit for ATM-SS7 signaling (data cells) is specified to be either be 0 or 1 and is not specifically assigned a default value in GR-2878 CORE (ANSI) nor I.361 (ITU). The CLP bit for ATM unassigned/idle (filler) cells is specified to be 0 for T1 interfaces and 1 for E1 interfaces. ATM equipment is required to discard these cells upon receipt and therefore the CLP bit for unassigned/idle (filler) cells will remain unchanged.2. The CLP bit for ATM-SS7 signaling (data cells) is used by ATM network equipment much in a similar fashion as the priority field is used by TDM SS7 equipment 3. The CLP bit determines how important a message is when an ATM network node is in congestion and needs to discard messages/packets. Currently, the CLP bit for ATM-SS7 signaling (data cells) is a non-configurable value in the EAGLE ATM header that is defaulted to 1 for both LIM-ATM (ANSI) and E1-ATM (ITU) cards. Effective in Release 31.3, this default will be changed to 0 (higher priority). The new CLP bit value of 0 has a higher priority than the current CLP bit value of 1.
2.80 Changeover and Changeback Procedure for Processor Outage and LIN (Release 21.0)
Currently, the EAGLE performs a sequence controlled changeover instead of a time-controlled changeover when the signaling link gets locally or remotely inhibited or when a local or remote processor outage condition is entered. In these cases, sending a changeover order could result in failure of the signaling link. The EAGLE also sends SIPOs when a signaling link is remotely or locally inhibited and also performs a sequence controlled changeover by sending a changeover order to the remote end.
With this release, the EAGLE now performs a time controlled changeover under these conditions. The EAGLE behaves in the following manner:
-
When the signaling link is inhibited locally or remotely, the EAGLE does not send SIPOs. Instead a time diversion changeover procedure is started for the inhibited signaling link.
-
When the signaling link is unavailable because of a remote or local processor outage, a time controlled changeover is performed instead of sequence controlled changeover.
If a changeover order is received for the unavailable link, while the level 3 T1 timer is in progress, the buffer updating procedure and sequence controlled changeover is performed. The EAGLE responds with an emergency changeover acknowledgment if the changeover order is received after the level 3 T1 timer has expired.
This feature applies to both ANSI and ITU signaling links. This feature has no impact on X.25 gateway signaling links since the inhibit and processor outage procedures are not used in the X.25 protocol.
2.81 Cluster Routing and Management Diversity (Release 21.0)
Description
The cluster routing and management diversity feature eliminates the need for a full point code entry in the routing table to route to every signaling point in every network. The cluster routing and management diversity feature allows the EAGLE to configure one route set to a entire cluster of destinations. This allows the EAGLE to manage and switch traffic to more end nodes.
A cluster is defined as a group of signaling points whose point codes have identical values for the network and cluster fields of the point codes. A cluster entry in the routing table is shown with an asterisk (*) in the member field of the point code, for example, 111-011-*. Cluster entries can only be provisioned as ANSI destination point codes. ANSI destination point codes can be specified as either a full point code, for example, 123-043-045, or as a cluster of signaling point codes, for example, 111-011-*.
Provisioning of clusters as well as full point codes that belong to the same cluster as destination point codes is also supported. The point codes 111-011-*, 111-011-005 and 111-011-045 entries can be provisioned. The cluster destination point code 111-011-* represents all the point codes of the cluster except for point codes 111-011-005 and 111-011-045. Cluster entries in the destination point code table can also be used as a destination point code (DPC) for a route. A group of such routes with varying relative cost forms a routeset to a cluster just like a routeset to a full point code.
Exception Lists (X-lists)
An exception list for a cluster is a list of point codes in a cluster whose route status is more restricted than the corresponding route status of that cluster. The term “more restricted” is used when comparing the route status of a cluster member to the route status of the cluster. A PROHIBITED status is more restrictive than a RESTRICTED status and a RESTRICTED status is more restrictive than an ALLOWED status. This list contains point codes that are not assigned to any individual routeset and the only routesets to that node is through a cluster routeset. The exception list is a dynamic list that changes when the status of the cluster routeset or any member routesets in that cluster changes.
For each cluster, the user can specify an exception list exclusion indicator (ELEI) when configuring the cluster point code with the ent-dstn command. When the ELEI is yes, the EAGLE does not maintain exception list entries. When the ELEI is no, the EAGLE maintains exception list entries.
Exception list entries are stored as an extension of the destination point code table, which can contain up to 2500 entries. The EAGLE allows the user to specify the number of entries reserved for the exception list, between 500 to 2000 entries. The remainder of the 2500 entries in the destination point code table are reserved for the full and cluster point codes.
The outputs of the ent-dstn, dlt-dstn, chg-dstn, and rtrv-dstn commands display the following destination point code usage information.
-
The number of configured full point codes
-
The number of configured cluster point codes
-
The sum of configured destinations (full and cluster point codes)
-
The number of entries reserved for configured destinations (full and cluster point codes). This number is 2500 minus the number of entries reserved for the exception list.
-
The number of entries reserved for exception list
There is an STP-wide expiration time value for exception list entries. This timer specifies the amount of time an idle exception list entry can be in the exception list before it is discarded. When this timer expires, unsolicited information message (UIM) 1146, REPT-SLST-TIMO: X-LIST entry expired, is displayed on the terminal and the specified exception list entry is discarded. The following is an example of UIM 1146.
Output Example:
RLGHNCXA03W 96-04-16 16:21:11 EDT Rel 21.0.0
1234.1146 CARD 1101 INFO REPT-XLST-TIMO: X-LIST entry expired
DPC=011-212-033
Report Date: 96-04-16 Time: 16:20:19
In this example, the point code (DPC) 011-212-033 was in the exception list, the timer expired, and the point code was discarded from the exception list.
The value of the exception list timer is shown in the MTPXLET field of the rtrv-stpopts command output and is configured with the mtpxlet parameter of the chg-stpopts command.
The rtrv-stpopts command output contains three other fields that show the parameters of the exception list, MTPXLQ, MTPXLOT, and MTPDPCQ.
The MTPXLQ field shows the maximum number of entries the exception list (x-list) can contain. This value is configured with the mtpxlq parameter of the chg-stpopts command.
The MTPXLOT field shows the exception list (x-list) occupancy threshold (in terms of the percentage of the exception list space being used). The percentage of occupancy threshold is configured with the mtpxlot parameter of the chg-stpopts command. The default value for the threshold is 90%. For example, if there are 1500 entries configured for the exception list and the exception list contains 1000 entries, the percentage of the exception list space being used is 66%. If this threshold is exceeded, a minor alarm, unsolicited alarm message (UAM) 321, X-LIST occupancy threshold exceeded, is displayed. The following is an example of UAM 321.
UAM Messages
RLGHNCXA03W 96-04-16 16:21:11 EDT Rel 21.0.0
* 0061.0321 * XLIST X-LIST occupancy threshold exceeded
The MTPDPCQ field shows the maximum number of destination point codes that can be configured in the EAGLE.
The EAGLE raises a major alarm, UAM 338, X-LIST space full-entry(s) discarded, when the exception list becomes completely full and the EAGLE fails to create any more exception list entries. The following is an example of UAM 338.
RLGHNCXA03W 96-04-16 16:21:11 EDT Rel 21.0.0
** 0055.0338 ** SYSTEM X-LIST space full-entry(s) discarded
An exception list entry’s expiration timer is restarted when an exception list entry gets created, updated, or used for routing. This expiration timer can be set for a minimum of 20 minutes to a maximum of 24 hours. The default value for the expiration timer upon system start-up is 60 minutes. If the timer expires before it is restarted, the exception list entry is removed. The expiration timer allows the EAGLE to save resources if the exception list entry is sitting idle for a specified period of time.
An exception list entry can be created for three distinct set of conditions.
-
The first set of conditions creates exception list entries based on the status of the route (allowed, restricted, or prohibited) and are marked as “exception list due to routing.”
-
The EAGLE creates an exception list entry to maintain the congestion status of a non-provisioned, cluster routed destination point code. These entries are marked “exception list due to congestion.”
-
The EAGLE also creates an exception list to prohibit routing to a member of a cluster when circular routing to that member is detected. These exception list entries are marked “exception list due to circular routing.”
An exception list entry for a particular cluster can be removed from the exception list when the following conditions are met:
-
The status of all routes to the specified point code changes to a status that is less or equally restrictive than corresponding status of cluster’s routes. This can happen for two reasons.
-
A
dact-rststcommand was issued. Thedact-rststcommand changes the route’s status to allowed. -
A network management message (TFA or TFR) was received indicating the new status of the route to the specified point code.
-
-
The expiration timer for the exception list entry expires.
-
When a
chg-dstncommand is issued and changes the ELEI toyesfor the cluster; the EAGLE removes all exception list entries created for that cluster. -
The
chg-stpoptscommand was issued with themtpxletparameter and the new value for themtpxletparameter was smaller than the original value. This command can change allocation of routing table entries for exception lists. If the size of the exception list is reduced and the number of entries in the exception list is now greater than the new value of themtpxletparameter, the EAGLE will remove excess exception list entries at random. -
When a user allows a circular routed “exception list due to circular routing” entry after fixing the problem. The
rst-dstncommand is used to allow the routing. -
When congestion abates for an “exception list due to routing” entry.
Cluster Routing
When the EAGLE receives an MSU to route, the routing function looks for the MSUs destination point code as a full point code entry in the routing table. If found, the full point code entry is used to find the corresponding routeset and the outgoing route. If a full point code entry is not found, the routing function uses the destination point code’s network and cluster values to find a cluster entry to which a destination point code belongs. If found, the cluster entry is used to find the corresponding routeset and the outgoing route. If neither a full point code entry or cluster point code entry is found, the EAGLE generates UAM 1004, “MTP rcvd unknown DPC.”
Compatibility with Non-Cluster Routing STPs
It is possible that not all STPs in the network that the EAGLE is operating in are cluster routing STPs. In such a situation, those STPs not doing cluster routing will interpret TCx messages and apply them to each individual point code belonging to the concerned cluster. This may cause an inconsistency in the status records for exception listed point codes in different STPs. In order to avoid this situation, the EAGLE takes the following steps:
-
After broadcasting a TCR message for a cluster, the EAGLE enables TFPs for the cluster’s exception listed prohibited member point codes by stopping the level 3 T8 timer. This allows TFPs to be sent for prohibited members immediately after a TCR is broadcast.
-
After broadcasting a TCA message for a cluster, the EAGLE enables a one-time TFR for the cluster’s exception listed restricted member point codes by stopping the level 3 T18 timer and enables the TFPs for the cluster’s exception listed (prohibited) member point codes by stopping the level 3 T8 timer. This allows TFPs to be sent for prohibited members and TFRs for restricted members immediately after a TCA is broadcast.
Compatibility with the ITU Network and X.25 Gateway
ITU SS7 networks do not use the concept of clusters of point codes and cluster network management messages. The EAGLE does not generate TCx messages towards ITU nodes. The EAGLE does not send TCx messages to adjacent ITU point codes during the broadcast phase of TCx messages when the EAGLE is acting as an STP between an ITU network and an ANSI network. It is possible that messages may be lost in such a case. In order to reduce message loss and quickly notify the sending ITU node about the status, the EAGLE enables TFPs or TFRs immediately (with the level 3 T8 or T18 timers stopped) and relies on the TFPs or TFRs to convey the status information.
While sending response method network management messages in response to a received MSU, the EAGLE checks the MSU’s originating point code. If the MSU’s originating point code is an ITU point code, a TFx message is returned.
Cluster entries can only be provisioned as ANSI destination point codes. Cluster entries cannot be provisioned for ITU international or ITU national destination point codes. The ANSI alias point code for an ITU international or ITU national destination point code must be a full point code. Cluster routing is not supported for X.25 destinations. X.25 destinations and any alias point codes used for X.25 destinations must be full point code entries.
Cluster Management When the Cluster Routing Feature is Turned Off
Cluster routing is an optional feature and can be turned on with the chg-feat:crmd=on command. Once this feature is turned on, it cannot be turned off. If this feature is turned off, the EAGLE does not send any cluster management messages or allow cluster destination point codes to be added to the destination point code table. The EAGLE is capable of processing incoming cluster management messages even though the feature is turned off. When a cluster management message is received, the EAGLE treats this message as though network management messages were received for each full point code, configured in the destination point code table, belonging to that cluster.
2.82 Command Class Management (Release 29.0)
Description
The Command Class Management feature allows the user to place EAGLE commands into 32 new configurable command classes. The craftsperson can provision any of these configurable command classes to contain any of the EAGLE commands. The command classes can then be assigned to a user and/or terminal, thus allowing the user or terminal the privilege of executing any command in the class. This allows users and terminals to fully configure custom command classes. This capability is controlled via a feature access key.
Note:
The result is each user/terminal will have access to a set of commands tailored to a specific need. The new configurable command classes are in addition to the existing non-configurable command classes. The current basic and non-configurable command classes will remain.Refer to the Commands Manual for current detailed information on this feature.
Hardware Requirements
No new hardware is needed to support this feature.
Limitations
There is a limitation on the feature’s operation regarding the use of the ENT-USER, CHG-USER, CHG-SECU-TRM and CHG-CMD commands. These commands can assign a maximum of eight command classes per command execution. However, subsequent command executions can be used to readily assign the full number of required configurable command classes.
2.83 Command Output Changes (Release 22.0)
The method of displaying whether the copy=yes or redirect=yes parameters have been specified for a given screening entry in the gateway screening retrieve commands has been changed. The heading of the NSR field of the output has been changed to NSR/ACT to display either the next screening reference name (NSR) or the next action that is to be performed (ACT). The same field can be used to display both of these items, because in previous releases, the NSR field is blank when the copy=yes and redirect=yes parameters have been specified. These parameters can only be specified when the NSFI is set to stop and the nsr parameter cannot be specified.
If the NSFI of the screen is not stop or fail, the NSR/ACT field displays the name of the next screening table to be used in the gateway screening process.
When NSFI of the screen is stop, the NSR/ACT field contains the following entries.
-
-, - — if neither the
copy=yesorredirect=yesparameters have been specified. This entry is also displayed if the NSFI of the screen isfail(only with thertrv-scr-blkdpcandrtrv-scr-blkopccommands) -
C, - — if only the
copy=yesparameter has been specified -
-, R — if only the
redirect=yesparameter has been specified -
C, R — if both the
copy=yesandredirect=yesparameters have been specified
Refer to the Commands Manual for current command information..
The outputs of these commands have been changed to this new format.
-
rtrv-scr-opc -
rtrv-scr-dpc -
rtrv-scr-blkdpc -
rtrv-scr-blkopc -
rtrv-scr-destfld -
rtrv-scr-sio -
rtrv-scr-cgpa -
rtrv-scr-cdpa -
rtrv-scr-aftpc -
rtrv-scr-tt -
rtrv-scrset
2.84 Command to perform migration of IPLIM to IPSG (Release 42.0)
The Command to perform migration of IPLIM to IPSG feature introduces the chg-card command to automate the migration from an IPLIM configuration to an IPSG configuration.
Note:
If changing the configuration from IPLIM to IPSG exceeds the Transactions per Second (TPS) limits of the card or system, then the command is rejected.2.85 Configurable SCTP Heartbeat Timer (Release 46.0)
The SCTP HeartBeat Timer is configurable on a per association basis. The timer value is configurable from 500 milliseconds to 3000 milliseconds.
2.86 Configurable Timer for link NO-DATA Condition (Release 37.7, 39.0)
The Configurable Timer for link NO-DATA Condition core enhancement provides a configurable timer to measure the time that must pass with no transmissions on a link before a link or terminal equipment failure is declared and changeover procedures are initiated. This timer is referred to as a nodata timer.
The nodata timer is used by low speed links on the HC-MIM, E1/T1 MIM, and MPL cards.
2.87 Configuring the Frequency of RST Messages on Low Priority Routes (Release 22.0)
This feature allows the configuring of a timer to specify the frequency of signaling-route-set-test messages for routes of lower priority than the current route.
In earlier releases, the routeset test messages were sent for every route to every destination for a period of time equal to the value of the level 3 timer T10. With this feature, the EAGLE only sends the routeset test messages for routes of equal or higher priority that the current route.
Parameters
To send routeset test messages for lower priority routes, new parameters (mtplprst and mtpt10alt) have been added to the chg-stpopts command to turn this capability on and to set the timer to control the frequency that the routeset test messages are sent.
mtplprst — turns on or off the routeset test message for lower priority routes capability. The values for this parameter is yes or no. The default value for this parameter is yes.
mtpt10alt —the timer to control the frequency at which the routeset test messages are sent. The values for this parameter are from 30 to 10,000 milliseconds. The default value for this parameter is equal to the value of the level 3 T10 timer.
When the mtplprst=no parameter is specified with the chg-stpopts command, the EAGLE does not send routeset test messages for the lower priority routes. When the mtplprst=yes parameter is specified, the EAGLE sends routeset test messages at intervals specified by the value of the mtpt10alt parameter.
The network example shown in Figure Route Set Test Example shows how this feature works. The following table shows the priorities of the routesets to destination X.
Table 2-20 Routeset Priorities
| Routesets to Destination X | Cost |
|---|---|
|
Ls1 (high priority route) |
10 |
|
Ls2 (current route) |
20 |
|
Ls3 (low priority route) |
30 |
Destination X is currently accessible from STP A using route Ls2. STP C and STP B have sent TFP messages for destination X to STP A. STP C is on higher priority route than the current route while STP B is on lower priority route than the current route. By default, the EAGLE polls STPs B and C by sending RSP messages for destination X at intervals defined by the level 3 timer T10. The polling frequency to STP B can be changed by changing low priority route set test time interval with the mtpt10alt parameter of the chg-stpopts command and setting it to a value greater than the value of the level 3 timer T10. RSP messages for destination X are sent to STP C at intervals defined by the level 3 timer T10 and RSP message for destination X are sent to STP B at intervals defined by the mtpt10alt parameter.
Figure 2-13 Route Set Test Example

The level 3 T10 timer and mtpt10alt parameter of the chg-stpopts command are configured independently. The EAGLE requires that the value of the mtpt10alt parameter is greater than or equal to the value of the level 3 T10 timer. If the value of the level 3 T10 timer is increased to a value greater than the current value of the mtpt10alt parameter, the value of the mtpt10alt parameter is adjusted to be equal to the new value of the level 3 T10 timer and the following message is displayed in the scroll area of the terminal.
MTP T10alt Timer in STP Options Table adjusted to correspond with T10 Timer.
If the value of the level 3 T10 timer is decreased, the value of the mtpt10alt parameter is not adjusted.
Any changes in the values of the level 3 T10 timer and the mtpt10alt parameter of the chg-stpopts command take affect only after these timers have expired.
2.88 Configuring the Unauthorized Use Warning Message (Release 22.0)
Currently, the EAGLE displays the following message immediately after successfully logging into the EAGLE.
NOTICE: This is a private computer system.
Unauthorized access or use may lead to prosecution.
In Release 22.0, the user can now configure their own warning message that follows a successful login. The message can contain up to 20 lines of text with each line of text containing up to 70 characters.
When a login attempt is successful, the user sees the warning message (0 - 20 lines) and then 2 lines of login history information. The administrator can configure the warning message so that it and the login history information will not all fit into the scroll area of the EAGLE terminal. The user can use scroll area locking (F8) key so the login warning message can be read before it scrolls out of view.
Note:
When the EAGLE is delivered to the user, the database will contain the following login warning message. This complies with the suggested Bellcore default values.NOTICE: This is a private computer system. Unauthorized access or use may lead to prosecution.The chg-secu-dflt and rtrv-secu-dflt commands have been modified to configure this warning message.
Two parameters have been added to the chg-secu-dflt command to configure the login warning message, wrnln and wrntx.
The wrnln parameter specifies the line number of the login warning message that is being changed. The values for this parameter are from 1 to 20.
The wrntx parameter specifies the text for the line number of the login warning message. The text line can contain up to 70 alphanumeric characters and must be enclosed in quotes (“). A text line with no characters can be specified with this text string, “”. This prevents the text line from being displayed in the login warning message. A blank line is specified with this text string, ““.
The following is an example of how the login warning message can be configured.
Input Examples:
CHG-SECU-DFLT:WRNLN=1:WRNTX="*******************************************************"
CHG-SECU-DFLT:WRNLN=2:WRNTX="* NOTICE: This is a private computer system. *"
CHG-SECU-DFLT:WRNLN=3:WRNTX="* UNAUTHORIZED ACCESS OR USE WILL BE PROSECUTED *"
CHG-SECU-DFLT:WRNLN=4:WRNTX="* *"
CHG-SECU-DFLT:WRNLN=5:WRNTX="* *"
CHG-SECU-DFLT:WRNLN=6:WRNTX="* 06/07/97 Notice!!! EAGLE will be upgraded between *"
CHG-SECU-DFLT:WRNLN=7:WRNTX="* the hours of 2am-3am on 06/15/97. *"
CHG-SECU-DFLT:WRNLN=8:WRNTX="* *"
CHG-SECU-DFLT:WRNLN=9:WRNTX="* *"
CHG-SECU-DFLT:WRNLN=10:WRNTX="********************************************************"
CHG-SECU-DFLT:WRNLN=11:WRNTX=" "
CHG-SECU-DFLT:WRNLN=12:WRNTX=""
CHG-SECU-DFLT:WRNLN=13:WRNTX=""
CHG-SECU-DFLT:WRNLN=14:WRNTX=""
CHG-SECU-DFLT:WRNLN=15:WRNTX=""
CHG-SECU-DFLT:WRNLN=16:WRNTX=""
CHG-SECU-DFLT:WRNLN=17:WRNTX=""
CHG-SECU-DFLT:WRNLN=18:WRNTX=""
CHG-SECU-DFLT:WRNLN=19:WRNTX=""
CHG-SECU-DFLT:WRNLN=20:WRNTX=""
The following is an example of what this example login warning message would look like after a successful login attempt.
Output Example:
*******************************************************
*NOTICE: This is a private computer system.
**UNAUTHORIZED ACCESS OR USE WILL BE PROSECUTED
**
**
**06/07/97 Notice!!! EAGLE will be upgraded between
**the hours of 2am-3am on 06/15/97
**
**
********************************************************
0 LOGIN failures since last successful LOGIN
Last successful LOGIN was on port 3 on 97-06-07 @ 12:12:35
The parameter msg (with the values yes or no) has been added to the rtrv-secu-dflt command to display the text of each line of the login warning message. If the msg=yes parameter is specified, the security defaults for user IDs and passwords and the 20 lines of text for the login warning message are displayed. If the msg=no parameter (the default value for this parameter) is specified, the security defaults for user IDs and passwords are displayed, but the login warning message text lines are not displayed. The following is an example of the rtrv-secu-dflt:msg=yes command output.
Output Example:
RLGHNCXA03W 97-06-07 16:02:05 EDT Rel 22.0.0
SECURITY DEFAULTS
-----------------
PAGE 60
UOUT 90
MULTLOG NO
MINLEN 8
ALPHA 1
NUM 1
NC 1
WARNING MESSAGE
---------------
1:"*****************************************************"
2:"* NOTICE: This is a private computer system. *"
3:"* UNAUTHORIZED ACCESS OR USE WILL BE PROSECUTED *"
4:"* *"
5:"* *"
6:"* 06/07/97 Notice!!! EAGLE will be upgraded between *"
7:"* the hours of 2am-3am on 06/15/97. *"
8:"* *"
9:"* *"
10:"****************************************************"
11:" "
12:""
13:""
14:""
15:""
16:""
17:""
18:""
19:""
20:""
2.89 Congestion Abatement Reporting (Release 21.0)
When a signaling link’s congestion level changes, these changes are reported to the user as UAMs (unsolicited alarm messages), whether the congestion level increases or decreases. The UAMs show how the signaling link congestion level has changed. The following table shows the changes in the signaling link congestion level changes and the UAM that reports these changes. No alarms are associated with these UAMs.
Table 2-21 Signaling Link Congestion Messages
| From Level | To Level | Output Messages | UAM |
|---|---|---|---|
|
0 |
1 |
REPT-LINK-CGST: congestion level 0 to 1 |
0264 |
|
0 |
2 |
REPT-LINK-CGST: congestion level 0 to 1 REPT-LINK-CGST: congestion level 1 to 2 |
0264 0265 |
|
0 |
3 |
REPT-LINK-CGST: congestion level 0 to 1 REPT-LINK-CGST: congestion level 1 to 2 REPT-LINK-CGST: congestion level 2 to 3 |
0264 0265 0266 |
|
1 |
0 |
RCVRY-LINK-CGST: congestion has cleared |
0269 |
|
1 |
2 |
REPT-LINK-CGST: congestion level 1 to 2 |
0265 |
|
1 |
3 |
REPT-LINK-CGST: congestion level 1 to 2 REPT-LINK-CGST: congestion level 2 to 3 |
0265 0266 |
|
2 |
0 |
RCVRY-LINK-CGST: congestion level 2 to 1 RCVRY-LINK-CGST: congestion has cleared |
0268 0269 |
|
2 |
1 |
RCVRY-LINK-CGST: congestion level 2 to 1 |
0268 |
|
2 |
3 |
REPT-LINK-CGST: congestion level 2 to 3 |
0266 |
|
3 |
0 |
REPT-LINK-CGST: congestion level 3 to 2 RCVRY-LINK-CGST: congestion level 2 to 1 RCVRY-LINK-CGST: congestion has cleared |
0267 0268 0269 |
|
3 |
1 |
REPT-LINK-CGST: congestion level 3 to 2 RCVRY-LINK-CGST: congestion level 2 to 1 |
0267 0268 |
|
3 |
2 |
REPT-LINK-CGST: congestion level 3 to 2 |
0267 |
2.90 Consistent Command Response Conversion (Releases 22.0, 24.0)
The consistent Command Response Conversion feature enables GUI software to read a consistent command response from the EAGLE STP and display the information in a suitable format and language on Keyboard Send/Receive (KSR)-mode-provisioned ports. This requirement fulfills the GUI’s requirement to know when an EAGLE-initiated command is completed.
Command Execution
To ensure reliability and uniqueness of pattern, a sequence of eight End of Transmission (EOT) characters (h’04) is used to indicate that the entered command has completed. These End of Transmission characters are not visible on the terminal display. This sequence, in most cases, means that all associated data output in response to the command entered has been displayed. Exceptions in which data output between the start of a command and the receipt of the EOTs may differ from the norm include the following:
-
Commands with delayed completion that allow other output to be displayed (for example,
copy-diskandformat-disk). -
Commands that report completion but actually continue displaying results for some amount of time (for example,
rept-meas). -
Commands entered in midstream of unsolicited output via Ctrl-A. For example:
Output Example for Release 22.2:
lnpstp 97-12-30 18:02:07 EST Rel 22.2.0.0
Error writing table 206: on standby TDM (A);
>set-date:date=971201
Command Accepted - Processing
DMS0002:table not found on disk[H’290e].
;
lnpstp 97-12-30 18:02:07 EST Rel 220.18.0.0 set-date:date=971201 Command entered at terminal #5.
;
lnpstp 97-12-30 18:02:07 EST Rel 220.18.0.0 Date set complete. ;(Response Ended - string of EOTs here)
Output Example for Release 24.0:
RLGHNCXA03W 99-01-07 00:57:31 EST Rel 24.0.0
Error writing table 206:
on standby TDM (A);
>set-date:date=990301
Command Accepted - Processing
DMS0002:table not found on disk[H’290e].
;
RLGHNCXA03W 99-01-07 00:57:31 EST Rel 24.0.0
set-date:date=990301
Command entered at terminal #5.
;
RLGHNCXA03W 99-03-01 00:57:31 EST Rel 24.0.0
Date set complete.
;(Response Ended - string of EOTs here
2.91 Core Software Version Updates (EPAP 16.0)
The underlying operating system for EPAP is updated to CentOS Version 5.10, and the underlying database is updated to MySQL Version 5.6.
2.92 Cost Factor on Routing (Release 20.0)
This feature allows the assignment of a weighting factor to a route. The weighting factor is then used by MTP routing to determine which is the primary route, and which are the alternate routes. By using this feature, multiple routes may be assigned to a destination, with a primary route selected for all routing unless congestion or some other condition should be encountered, at which point one of the alternate routes would be chosen.
Each routeset (which is a combination or routes) may be assigned six routes, with each route assigned a different cost factor. The range for cost factors is 0 to 99, with 99 being the least favorable route (highest cost).
Combined linksets may be assigned the same cost factor, allowing equal load sharing over the two linksets. Alternate combined linksets may also be created by assigning a higher cost factor to subsequent linksets.
2.93 CRP for SRIs without HomeRN (Release 42.0)
The MNP Circular Route Prevention feature (CRP) is enhanced to allow CRP based on the translation type (TT) to be performed for SRI messages when a Home Routing Number (HomeRN) is not present.
SRI Messages must meet the following criteria to be eligible for TT-based CRP:
- The message is selected for G-Port or IS41 GSM Migration processing.
- The message is not identified as G-Port SRI Query for Prepaid.
- The message is not MTP-routed (the CdPA is Route-on-GT).
- The SCCP CdPA TT matches the provisioned TT.
- The TCAP Package type is ITU Begin.
- The OpCode is an SRI (hexadecimal 16).
- The Optimal Routing Interrogation Parameter (Tag = 0x04) is not present.
- The MSISDN is not assigned to the subscriber's network provider.
2.94 CSPC Increase in Groups (Release 34.0)
The maximum number of point codes that can be provisioned in a Concerned Signaling Point Code (CSPC) group is increased from 32 to 96.
2.95 Customer Definable Alarms (Release 20.0)
This feature allows the user to connect up to 10 external devices to the EAGLE for alarm reporting. These are defined in the EAGLE database as customer defined troubles. These external devices are monitored and any changes in the state of these devices is reported to the user as an unsolicited alarm message (UAM). Two of these UAMs generate critical alarms, two UAMs generate major alarms, six UAMs generate minor alarms. The following table lists the UAM, the alarm level, and the trouble ID.
Table 2-22 Customer Definable Troubles Alarm Levels
| Customer Trouble ID | Alarm Detected UAM | Alarm Clearing UAM | Customer Trouble ID | Alarm Detected UAM | Alarm Clearing UAM |
|---|---|---|---|---|---|
|
1 |
Reserved |
N/A |
9 |
Reserved |
N/A |
|
2 |
Reserved |
N/A |
10 |
Reserved |
N/A |
|
3 |
0058 - Critical |
0062 - Normal |
11 |
0060 - Minor |
0062 - Normal |
|
4 |
0058 - Critical |
0062 - Normal |
12 |
0060 - Minor |
0062 - Normal |
|
5 |
Reserved |
N/A |
13 |
0060 - Minor |
0062 - Normal |
|
6 |
Reserved |
N/A |
14 |
0060 - Minor |
0062 - Normal |
|
7 |
0059 - Major |
0062 - Normal |
15 |
0060 - Minor |
0062 - Normal |
|
8 |
0059 - Major |
0062 - Normal |
16 |
0060 - Minor |
0062 - Normal |
The following messages are examples of these UAMs.
UAMs
ralncstp01 95-05-12 12:14:59 EST Rel 20.0.0
*C 4054.0058 *C CDT 4 Critical Customer Trouble detected
ralncstp01 95-05-12 12:14:59 EST Rel 20.0.0
** 4055.0059 ** CDT 8 Major Customer Trouble detected
ralncstp01 95-05-12 12:14:59 EST Rel 20.0.0
* 4056.0060 * CDT 11 Minor Customer Trouble detected
ralncstp01 95-05-12 12:14:59 EST Rel 20.0.0
4058.0062 CDT 9 Customer Trouble cleared
The status of these UAMs are displayed with the rept-stat-cdt command.
When the alarm condition that displayed these UAMs is cleared, UAM number 0062 is displayed.
2.96 CutAndPaste parameter in Connect response to INP IDP Query (Release 42.0)
The INP feature is enhanced to allow the CutAndPaste parameter to be included in the Connect response to an INP IDP query. This parameter provides the number of digits that the originating node of the query should discard from the CdPN digit string that the node is holding. Any digits remaining after the discard are pasted at the end of the DRA digits included in the Connect response. The query originating node uses this digit combination to construct a new routing number.
The CutAndPaste parameter consists of 3 bytes (tag, length, and value). The value field is the length of the incoming CdPN digit string (incoming DN) received in the INP IDP query. Therefore, the query originating node discards the entire CdPN digit string and uses the DRA digits as the routing digits.
If the CutAndPaste functionality is provisioned as ON, then the CutAndPaste parameter is included in the Connect response. Otherwise, the parameter is excluded. If the INPOPTS:DRA setting has a DN component, then the value field of the CutAndPaste parameter is the length of the incoming CdPN digit string (incoming DN) received in the IDP query. This informs the querying node to discard all stored digits, because the DN is supplied in the Connect response. If the INPOPTS:DRA setting does not have a DN component, then the value is zero. This informs the querying node to use all stored digits, because none are present in the DRA.
2.97 Database Integrity Enhancements (Release 20.0)
With this feature, the system audits the actual data in each module, provides checksum information, and verifies the checksum information against the original checksum that was downloaded to the module.
2.98 Database Management Command Functions (Release 20.0)
Description
In this feature, the database management commands are used to perform the following operations.
-
Backing up the database to the fixed disk and to the removable cartridge
-
Restoring the database from the fixed disk and from the removable cartridge
-
Copying the approved GPLs from the active fixed disk onto a removable cartridge
-
Copying the measurements data from the fixed disk onto a removable cartridge
-
Displaying the directories and files on either the fixed disks or the removable cartridge
These five operations are discussed separately, below.
Backup
This command makes a backup copy of the administered data that can later be used to restore the data. The backup is made onto both the fixed disks or onto the removable cartridge according to a parameter of the command. The original data is taken from the current partition on the fixed disk.
If the backup is made to the fixed disks, the current partition on a fixed disk is copied to the backup partition on the same fixed disk.
If the backup is made to the removable cartridge, it is taken from the current partition of the fixed disk of the active MASP and copied to the removable cartridge. There is only one data partition on the removable cartridge, and this is defined to be the backup partition.
Restore
This command allows the user to bring back onto the fixed disk a set of known good tables, which had been previously backed-up on a disk (either fixed or removable). This command only restores the administered data tables, not the GPLs or measurement tables.
When the restore is from the fixed disk, the backup partition is copied into the current partition.
When the restore is done from the removable cartridge, the backup partition on the removable cartridge is copied onto the current partition on the fixed disk. This command modifies the data tables on the fixed disks of both the active and standby MASPs.
When the restore is from the removable cartridge, the tables are copied to the fixed disks on both TDMs. It does not propagate any data changes to the SCCP cards, LIMs, and so forth. To propagate the changes resulting from the restored database, the EAGLE must be reinitialized.
Copy GPL
This command copies the set of approved GPLs from the active fixed disk on the TDM onto a removable cartridge. This is typically done after the installation of a new GPL on the system, when the GPLs have been approved, and will allow the user to keep one removable cartridge with a copy of all the approved GPLs in use on the system.
These GPLs may be brought back into the system from the removable cartridge using change GPL commands if there is a need to bring a system back to a prior state, or if a spare fixed disk needs to be brought up to date.
Copy Measurements
When there is a need to perform offline analysis of the raw measurements data, this command copies that data onto the removable cartridge. The data is copied from the active fixed disk on the TDM to the removable cartridge.
Measurements collection is not allowed to continue while this command is copying the tables, since this may result in data from one collection period spilling over into data from another collection period. Measurements cannot be copied if measurement collection is turned on. Measurement collection must be turned off if you wish to copy the measurements tables.
Since there are two formats for removable cartridges, and only one of these is valid for measurements, the command will give a clear error message if the wrong type of removable cartridge is mounted in the drive.
Disk Directory
This command displays the directory on the specified disk. It can be used to display the creation date for each file or selected files and to verify that the correct version of files are on the fixed disks or the removable cartridge.
Note:
Wildcards “*” and “?” can be used for filename matching. The “*” will match any number of characters, and any “?” will match any single character.
2.99 Database Transport Access (DTA) (Release 20.0)
This feature interconnects the X.25 and SS7 network protocols. This connection enables the interworking of several telephony and financial database application protocols carried within the X.25 and SS7 messages.
Refer to the Database Administration Manual - Features for current details of this feature.
2.100 DEIR on SLIC Network Redundancy Enhancement (Release 46.4)
This feature implements SCTP Multi-homing to provide network redundancy for the EAGLE Diameter EIR feature executing on SLIC. SCTP multi-homing provides a level of fault tolerance against network failures by using alternate paths through the IP network between two endpoints.
Figure 2-14 Network Redundancy Model Using SLIC
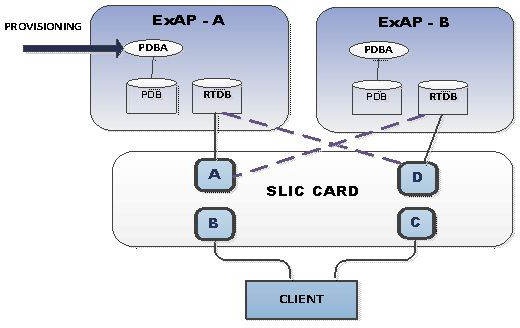
2.101 Delay Vs. Throughput (IP7 Release 5.0)
Description
This feature provides some level of user control over the TCP retransmission behavior that an individual TALI socket exhibits. Several aspects of TCP retransmissions need to be introduced in order to understand how this delay versus throughput feature will work.
As far as this feature is concerned, there are three primary aspects of TCP retransmissions that need to be understood.
-
Retransmission timer
-
Retransmission mode
-
Congestion window
Retransmission Timer
Conceptually, the TCP retransmission timer is a timer that is started when a TCP data segment is sent on a socket. The TCP data segment is encapsulated in an IP packet (we will refer to this data segment being sent as a TCP packet, even though TCP is a byte oriented transport layer that does not typically send 'packets'). If an acknowledgement for the TCP packet arrives before the timer expires, the timer is stopped. If the timer expires before an acknowledgement arrives, the original packet is assumed to be lost/corrupted and a retransmission of that packet occurs.
In practice, most TCP implementations do not start a separate timer for each packet, rather an internal timer expiration occurs at a fixed interval and upon each internal timer expiration the data related to outstanding transmit packets without acknowledgements is analyzed to determine which retransmissions occur. It may take multiple expirations of the internal timer until the overall timeout exceeds the retransmission timer. Therefore the actual time delay for each initial retransmission falls within a range determined by the frequency of the fixed timer expiration. For example, if a 50 millisecond internal timer is used, and it takes three expirations of the internal timer until a retransmission occurs, the actual timeout used varies from 101 milliseconds to 150 milliseconds.
In this document, the term 'internal retx timer' refers to the internal TCP timer that expires at a fixed interval regardless of how many transmit packets are outstanding. Upon each internal retx timer expiration, retransmissions are analyzed and possibly sent.
In this document, the term 'initial retransmission timeout' refers to the minimum amount of time that passes from when a packet is first transmitted until the initial retransmission occurs. It is important to note that the timeout refers to the minimum time before retransmission (not the maximum or average).
In this document, the term 'retransmission timeout' refers to the minimum amount of time that passes until the next retransmission occurs. The pending retransmission may or may not be the first retransmission based on the condition being described. The 'retransmission timeout' always refers to the current timeout.
In this document, the terms 'previous retransmission timeout' and 'next retransmission timeout' refer to the minimum timeouts before and after the current retransmission timeout.
Retransmission Mode
The retransmission mode refers to how the timeout varies from previous to current to next retransmission timeout.
There are several modes discussed in this document.
-
BSD mode refers to exponential growth of the timeout. Upon each timeout the next retransmission timeout is equal to 2 x the current retransmission timeout. Usually there is an upper limit on the exponential growth (exponential up to a threshold, then stays at the threshold).
-
FIXED mode refers to a constant timeout that does not change as subsequent retransmissions of the same packet occurs.
-
MODIFIED mode refers to a combination of the above two modes. One implementation of this mode may use a fixed mode for two out of every three consecutive retransmissions, shifting to the BSD mode on every third retransmit.
The following figure shows the relative spacing of timeouts for the three different retransmissions modes. Note that the spacing for BSD mode is incomplete due to its relatively long sequence
Figure 2-15 Spacing of Retransmissions in the Three Modes

-
The TCP protocol uses a sliding window to determine how much transmit data can be sent at one time, based on the minimum of the node's transmit window size and the far end's receive window size. The default TCP sliding window size is 8K bytes. Once 8K bytes of transmit data have been sent, with no acknowledgements received, the transmitter is prohibited from sending more until the far end sends acknowledgments for some portion of the window. The TCP window is said to slide when acknowledgments arrive, allowing packets with higher sequence numbers to be sent as packets with lower sequence numbers are acknowledged.
-
Even though a particular socket within a TCP stack is configured for an 8K sliding window size, there are times when the TCP protocol does not take advantage of the entire 8K sliding window. One of these times is when retransmissions occur.
-
When the TCP layer needs to retransmit one or more packets on a socket, the TCP protocol uses the minimum congestion window size rather than the TCP sliding window size to limit how much traffic can be sent until it must wait for acknowledgments. The minimum congestion window size is typically much less than the TCP sliding window size. As acknowledgments arrive from the far end after a retransmission event, the node slowly grows the congestion window up from the minimum congestion window to the size of the TCP sliding window.
-
Another way of looking at this aspect of retransmission is to state that when a retransmission occurs, a transmitter intentionally lowers its own throughput until enough evidence from the far end arrives to assure the transmitter that the network is not congested. This phenomena is also referred to as congestion avoidance.
Socket Connection Dropped due to Retransmission Timeouts
-
One other aspect of TCP retransmissions that should be mentioned is what happens when the same packet gets retransmitted over and over. When multiple retransmissions occur for a single packet, the TCP layer counts the number of retransmissions that is performed, and when this count gets too high the TCP socket is closed due to excessive retransmission timeouts. This shows up in the netstat -p tcp output in the 'connection dropped by rexmit timeout' row.
-
In the BSD TCP stack, when a packet has been retransmitted 12 times, the socket is closed. Given the use of the exponential retransmit mode in standard BSD, the 12 retransmissions correspond to a time period of approximately 205.5 seconds where the packet was not able to sent/ack'd. (205.5 is based on 500 ms x 511, 511 is the sum of the tcp_backoff[] array which governs how the exponential backoff occurs and when the top threshold is reached).
-
In the IP7 SG stack, when a packet has been retransmitted 12 times, the socket is closed. Given the use of fixed retransmission mode with a 125ms timer, the 12 retransmissions correspond to a time period of approximately 1.5 seconds where the packet was not able to be send/ack'd.
Behavior of Standard BSD Sockets
The following table summarizes the TCP retransmission characteristics of a standard BSD socket.
Table 2-23 BSD Socket Retransmission Characteristics
| Characteristic | Setting or Behavior (not configurable, applies to all sockets) |
|---|---|
|
initial retransmission timeout |
500 milliseconds |
|
tcp window size |
8k |
|
retransmission mode |
exponential |
|
minimum congestion window |
2 x the maximum segment size |
|
how does cong window grow |
initially grows exponentially via 1 MSS per ack. past a certain threshold, the growth is linear up to the point where the window is fully open |
|
socket dropped due to retransmission timeout |
after approx 205.5 seconds |
|
RTO |
500 ms default, algorithm to “learn” RTO by averaging recent round trip times, with software imposed upper bound |
BSD sockets are extremely tolerant of poor network conditions and continue to wait for longer and longer time periods before performing subsequent retransmissions. These characteristics are not very well suited for time sensitive data such as SS7.
Behavior of IP7 SG Release 4.0 IPLIMX & IPGWX Sockets
The following table summarizes the IPLIMX & IPGWX retransmission characteristics present in the IP7 SG Release 4.0 product.
Table 2-24 IPLIMX Socket Retransmission Characteristics on IP7 SG 4.0
| Characteristic | Setting or Behavior (not configurable, applies to all sockets) |
|---|---|
|
initial retransmission timeout |
125 milliseconds |
|
tcp window size |
192k |
|
retransmission mode |
fixed |
|
minimum congestion window |
32k |
|
how does cong window grow |
grows exponentially via 1 MSS per ack up to the point where the window is fully open |
|
socket dropped due to retransmission timeout |
after approx 1.5 seconds |
|
RTO |
fixed, no dynamic information about actual round-trip times used |
IPLIMX & IPGWX sockets have been tuned to handle time sensitive data and expect network conditions with low RTT and few transmission errors. The configuration shown above is not tolerant of networks with RTT above a certain threshold (approximately 100ms) or with too many transmission errors. The 4.0 implementation does not expect packet loss due to congestion. The only loss that is expected is due to hardware and/or transmission errors, bad checksums, and so forth. The 4.0 implementation expects little or no congestion on the network, and does not react in a fair manner (with respect to congestion avoidance) when congestion does occur.
Behavior of IP7 SG Release 5.0 IPLIMX & IPGWX Sockets
The following table summarizes the IPLIMX and IPGWX retransmission characteristics that are available in the IP7 SG Release 5.0 product.
Table 2-25 IPLIMX Socket Retransmission Characteristics on IP7 SG 5.0
| Characteristic | Setting or Behavior (configurable on a per socket basis) |
|---|---|
|
initial retransmission timeout |
as low as 125 milliseconds, settable in 125ms increments |
|
tcp window size |
192k |
|
retransmission mode |
fixed | bsd | modified |
|
minimum congestion window |
32k |
|
how does cong window grow |
exponential when mode = fixed | modified exponential followed by linear when mode = bsd |
|
socket dropped due to retransmission timeout |
varies from 1.5 to 205.5 seconds based on the mode and retransmission timeout configured |
|
RTO |
fixed, no dynamic information about actual round-trip times used |
As seen in the tables above, the Delay vs. “Throughput for TALI Sockets” feature allows the end user to tune the retransmission characteristics of individual sockets. Sockets can be set so that they can function in a variety of network conditions (for example, LAN connection vs. a trans-Pacific WAN connection).
Upgrade Considerations
The addition of two new parameters in the entry (in the Socket Table) for each TCP/IP Socket necessitates the need for changes to the Upgrade Procedures for Engineering Release 37. These two new fields, Retransmission Mode and Round Trip Time Value, must be initialized to default values. The Retransmission Mode is initially set to "FIXED", with the Round Trip Time set to 60 milliseconds. A third field, the Congestion Window Lower Limit must be set to a calculated value using the default Round Trip Time (60 milliseconds). These fields must be set up for every assigned socket. The upgrade applies to both the OAM and Application copies of the Socket Table.
Limitations
The TCP/IP Protocol Stack timing mechanism has been modified by Tekelec software engineers. These changes enable the protocol to support TCP timers with resolutions as low as 125 milliseconds. It is not within the scope of the "Delay Vs. Throughput for TALI Sockets" feature to implement any other TCP timer resolutions than those currently supported. Each value entered as part of the Round Trip Time parameter is mapped to a corresponding Retransmission Timer, with a resolution of 125 milliseconds.
2.102 Digit Action to Delete Country Code when Present and Prefix with Database Entity (Release 44.0)
The Digit Action to delete country code if present and prefix database entity feature allows the DELCCPREFIX Digit Action to be applied to the Called Party Global Title Address (CdPA GTA) when the GTA has a National format as well as when the GTA has an International format.
When the option is configured and the GTA has an International format, the Country Code is deleted and the GTA is prefixed with the Entity Id. When the GTA has a National format, the GTA is prefixed with the Entity ID.
2.103 DigitAction Expansion (Releases 31.11, 34.0)
Description
G-Port and G-Flex allow the SCCP CdPA GTA field to be overwritten if G-Port determines the call should be relayed to its destination after a PDB lookup is performed.
G-Port and G-Flex support options that can be selected to overwrite or not to overwrite the SCCP CdPA GTA field. These options are defined by the DigitAction field of the PDBI Enter Network Entity command and Update Network Entity command. The user can also set these options to format the SCCP field before the EAGLE relays the message to the destination.
The rules for formatting the SCCP CdPA GTA field are based on the value specified in the DigitAction field. If digitaction = none, the EAGLE 5 ISS does not overwrite the SCCP CdPA GTA field. For all other values, the EAGLE 5 SAS formats the SCCP CdPA GTA field according to the value assigned to DigitAction field.
The following table provides samples of the format of the SCCP CdPA GTA field of an outgoing message using RN/SP ID= 1404 and default country code=886.
Table 2-26 DigitAction Applications
| DigitAction | Value in Incoming CdPA GTA | Value in Outgoing CdPA GTA |
|---|---|---|
|
none |
886944000213 |
886944000213 (no change is made) |
|
prefix |
886944000213 |
1404886944000213 |
|
replace |
886944000213 |
1404 |
|
insert |
886944000213 |
8861404944000213 |
|
delccprefix |
886944000213 |
1404944000213 |
|
delcc |
886944000213 |
944000213 |
|
spare1 |
886944000213 |
is treated as "none" |
|
spare2 |
886944000213 |
is treated as "none" |
This feature expands the DigitAction field in PDBI and the EPAP GUI to support additional values "delcc," "delccprefix," "spare1," and "spare2." If the DigitAction value is "delccprefix," the SCCP CdPA GTA field of an outgoing message is formatted by prepending the RN/SP ID to the incoming SCCP CdPA GTA field and deleting the default country code if present. If the DigitAction value is "delcc," the SCCP CdPA GTA field of an outgoing message is the incoming SCCP CdPA GTA field without the default country code if present. The result of specifying the DigitAction field values “spare1” and “spare2” is the same as specifying the value “none.”
Hardware Requirements
Refer to the hardware baseline.
2.104 Disallow Simultaneous Logins Sessions with the Same User ID (Release 21.0)
In Release 21.0, the EAGLE does not allow more than one login session to be active at any given time for a specific user ID. During login command processing, a check is made to see if the user ID is associated with any currently active login session, or is in the process of logging on to another port. If the user ID is found to be already in use on some other EAGLE terminal port, then the login is rejected and the error message (the duplicate login error message) is displayed.
E2750 Cmd Rej: UserID already logged on (or is logging on) another port
The following message is also displayed in the scroll area of the terminal that gives the terminal port (port yy) that the user (UserID xxxxxxxx) is already logged to.
Info: UserID xxxxxxxx is currently logged on to port yy.
The check for multiple login sessions is made after the user ID and password have been successfully validated and before any password aging or force password change checking is done. As a result, the following events can occur.
-
If the user specifies an invalid login or password, this message is displayed and the duplicate login error message is not displayed.
E2757 Cmd Rej: Invalid userID/password combination
-
If the user ID and password is valid, but the user's password requires changing, they do not see the messages or prompts to change the password. Instead, they see the duplicate login error message.
This feature can be disabled by specifying the chg-secu-dflt command with the multlog=yes parameter
2.105 Discard TFC Traffic (Release 34.0)
The chg-ss7opts command includes the discardtfci and discardtfcn parameters to enable and disable the discarding of TFC traffic. The rtrv-ss7opts command displays the current setting of the parameters.
2.106 Disk Coherency Tests (Release 20.0)
This feature checks that the information in the database contains the correct pointers. The system can determine whether an update to the database failed and whether the information in the database was corrupted.
2.107 Disk Copy Fixed to Fixed (Release 20.0)
This feature allows maintenance personnel to create a mirror image from the active TDM fixed disk drive to the standby TDM fixed disk drive. This is used when replacing or updating a TDM.
If more than one message is sent to the EOAP without the LSMS waiting for a response, the LSMS must manage retries and the sequencing of messages.
The EOAP must be configured locally with the LSMS OSI-Address information necessary for association establishment. The EOAP will initiate association connections with the LSMS.
2.108 Display Inhibited Alarms (Release 29.0)
Description
This feature enhances the rept-stat-alm report to show all the devices that are alarm-inhibited, at what level and duration they are inhibited, and their current alarm level, if any.
Use of the Display Parameter
-
If DISPLAY=INHB is used, a plus sign (+) seen in the “Alarm Inhibit Report” (i.e. in the CUR ALM LVL column) indicates that the current alarm is not inhibited, because the level of the inhibit is less than the level of the alarm.
-
Column description:
-
Device and element is listed first. Only devices that are alarm inhibited are shown.
-
Duration shows whether the device is alarm inhibited permanently or temporarily.
-
The “alm inh lev” shows the level in which devices are alarm inhibited. The inh-alm command defaults level to major. Devices cannot be alarm inhibited at a critical level unless the stpopt critalminh is turned on.
-
The “current alm lev” shows the level of the current alarm on that device. “None” means there is no alarm currently on that device. If there is no alarm currently on that device, the Duration should show “Perm.”
-
Hardware Requirements
No new hardware is needed to support this feature.
2.109 Dual ExAP Configuration (Release 45.0)
The Dual ExAP Configuration feature allows one EAGLE to support both ELAP and EPAP in one node. EPAP and ELAP provide separate databases for various EAGLE features. Features such as G-Flex, G-Port, EIR, TIF use the EPAP database. Features such as LNP use the ELAP database. The features using the EPAP database and the ELAP database have been mutually exclusive. With the Dual ExAP Configuration feature, the EPAP-based features and ELAP-based features can be enabled and turned on simultaneously on the same EAGLE.
With the Dual ExAP Configuration feature, all Service Modules acquire a new attribute called Data Type:
- EPAP - a Service Module containing all data from EPAP, including both EPAP tables, DN & IMSI
- ELAP - a Service Module loaded with data from ELAP.
- GTT - a Service Module which is not loaded with data from ELAP or EPAP; loaded only with data from OAM.
A new option SCCPOPTS:GTTDIST controls the distribution of GTT-only traffic with no Real Time Database (RTDB) or Range Indexed Database (RIDB) lookup required.
2.109.1 Feature Control Requirements
- FAK for Part Number 893-0405-01
- A temporary FAK cannot be used to enable the feature.
- The feature cannot be turned off after it has been turned on.
- Message Flow Control must be turned on before the Dual ExAP Configuration feature can be turned on.
- The E5-SM4G Throughput Capacity feature must be enabled before the Dual ExAP Configuration feature can be turned on.
- The feature cannot be turned on if a DSM, E1-ATM, E1T1MIM, LIM-ATM, or MPL card is equipped and running in the system.
2.110 E1 Administration and Alarms (Release 26.3)
Description
Instead of a card having to be removed to change the configuration, each card can be configured using new commands and extensions to existing commands. This capability allows customers ease of configuring and updating their network using the EAGLE. Also, since the DIP switches are no longer required, they can be removed from future production E1 appliques.
Note:
This feature is backward compatible with the E1 hardware, with or without the DIP switches.
With the introduction of this feature, the administration of the E1 will be done by EAGLE commands. Thus various EAGLE commands have been created or modified.
Currently E1 cards are "provisioned" via dip switches on the LIM board. Although this method of provisioning is functional, customers desire to integrate the provisioning of E1 functionality similar to other LIM cards, via software. This feature enhances the current 2-Port E1 feature by allowing the customer to configure the E1 hardware without using the DIP switches on the applique. This feature also provides support for E1 Master Timing.
Description of E1 Operation within an EAGLE
The introduction of this feature brings complete product support for the E1 line interface into the EAGLE, thereby concluding the E1 effort begun during Release 22.2. Along with V.35, the E1 interface is a primary interface used outside of North America. Thus, this large market base is a large market potential for an EAGLE with an E1 interface.
The E1 cards are provisioned and operate in a fashion very similar to the current DS0/OCU/V.35 signaling links:
-
E1 cards and links must be configured in the EAGLE in a manner similar to how existing signaling links are configured. These configuration activities include entering cards, entering links, assigning links to link sets, and activating cards and links, in addition to entering E1 parameters. Changes to existing EAGLE commands, and new EAGLE commands, to perform these configuration activities are required.
-
Two new card types, 'LIME1' and 'LIMCH', are used to define the E1 card and Channel cards, respectively, in the EAGLE.
-
A set of E1-specific interface parameters must be maintained on a per-E1 basis. These parameters include:
-
which E1 port is used (either #1 or #2)
-
CRC4, CAS/CCS, HDB3/AMI, master/slave clocking options
-
signaling bits settings
-
-
A set of E1-specific interface parameters must be maintained on a per-signaling link basis. These parameters include:
-
which E1 card is the card dropping timeslots
-
which timeslots are being used
-
-
The current E1 implementation provisions E1 cards as either DS0 or OCU, based on master/slave timing. This feature provisions the cards as E1 or channel with either master or slave timing.
-
Building Integrated Timing System (BITS) clock alarms must be supported when E1 cards with master timing are provisioned in the EAGLE. Currently, this is the reason that E1 cards are provisioned as DS0 cards.
The TST-SLK command will continue to support local transceiver loopback using the ISCC, just like the DS0/OCU/V.35 cards; no changes are necessary.
EAGLE Application Support for E1
Currently the SS7 application software initializes the hardware completely based on DIP switch values. With the new E1 Administration and Alarms feature allowing E1 cards to be provisioned, the SS7 application software needs to only initialize the hardware to a benign state until provisioning information is provided. This initial hardware state is similar to the other link interface module (LIM) cards' initial state.
Hardware Requirements
This feature is dependent upon the EAGLE E1 hardware, consisting of the LIM E1 backplane kit (P/N 890-1037-01), which allows connectivity between the E1 LIM card(s) and the corresponding E1 channel card(s) (both P/N 870-1379-01).
Upgrade Considerations
-
The system release containing the E1 Administration and Alarms feature must be field-upgradable, with the EAGLE in an in-service mode.
-
The new current and backup tables for E1 link interface parameter values must be created.
-
A new phase is needed in the upgrade procedure to update the database with E1 information retrieved from the network cards after the network cards have been loaded with the latest GPL.
-
Prior to collecting E1 information, cards will be loaded with the latest GPL with data from the database, including link information. Cards containing existing E1 links must load and bring up their SS7 links using the DIP switches instead of downloaded E1 data in this case.
-
Card type field in the current and backup IMTA tables needs to be corrected from DS0/OCU based on information received from each card.
-
E1 parameter information needs to be updated in current and backup E1LINK tables.
-
E1 timeslot information needs to be updated in current and backup LINK and XLINK tables.
-
Since upgrade must be able to be performed remotely, there must be an automated way to map the E1/Channel card relationship via some method such as far-end loopback detection.
-
Since TS0 and TS16 (when CAS is enabled) may be assigned using the DIP switches, the upgrade must detect and report this condition. However, no change can be made to the timeslots.
Limitations
The E1 Administration and Alarms feature has these limitations:
-
The configuration of the various E1/channel cards via the E1 backplane is not validated with the E1 parameter set information.
-
There is no verification that the E1 and channel cards are connected to the E1 backplane.
2.111 E1 ATM High Speed Link (Release 28.1) (IP7 Release 6.0)
Description
International customers desire increased signaling bandwidth by utilizing Asynchronous Transfer Mode (ATM). This capability requires EAGLE software to support ATM, as well as some hardware modifications to the existing LIM-ATM card that currently supports ATM over T1. The existing HCAP design for the LIM-ATM, with some modifications to the appliqué, is being used to accommodate the E1 ATM connectivity to the EAGLE.
This feature provides a new E1 interface capability on the EAGLE. This new capability is provided using the existing LIM-ATM via an HCAP card, a new Applique' ATM (AATM) daughterboard, and a new GPL. A modified LIM-ATM supporting 2.048 Mb/sec is here referenced as an E1 ATM card. The E1 ATM capability supports a single ATM Virtual Channel Connection (VCC) at a line speed of 2.048 Mbps. The E1 ATM replaces the MTP layers 1 and 2, (ITU-T Q.702 and ITU-T Q.703) with an ATM-based protocol (ITU-T Q.2110, Q.2140 and Q.2144). ATM is used as the transport technology for carrying the signaling information via PDU's between network nodes.
Refer to the NSD Hardware Manual for detailed hardware information.
New Hardware
E1 ATM LIM provides one Asynchronous Transfer Mode over E1 Interface at 2.048 Mbps, (P/N 870-1293-xx). This module uses an E1 Asynchronous Transfer Mode Applique (E1 ATM) installed on a High Capacity Application Processor (HCAP) main assembly. The E1 ATM applique provides a new communications capability on the EAGLE, a High Speed Link (HSL) using ATM over E1. This capability is provided using the existing HCAP card, a new applique, and a new GPL (ATMITU).
Refer to the NSD Hardware Manual for detailed hardware information.
Limitations
OAM F5 Performance Monitoring
ATMANSI does not provide OAM F5 performance monitoring. This capability has not been added for this feature. Because the anticipated deployment of this feature is as a direct connection, performance monitoring of the network is not anticipated to supply any additional information that SAAL does not.
OAM F5 Fault Management
ATMANSI only provides OAM F5 fault management for OAM loopback. It does not provide support for alarm surveillance and continuity check. These capabilities have not been added for this feature. Because the anticipated deployment of this feature is as a direct connection, fault management of the network is not anticipated to supply additional functionality. Connection issues will be detected by the SAAL and the link will be deactivated if appropriate.
Traffic Size
Traffic size will have a definite impact on MSU throughput of the system; see table.
Table 2-27 Comparison of MSU Size to Throughput
| MSU Size | ATM Packet Overhead | Cells/MSU | Max MSU/Sec |
|---|---|---|---|
|
20 |
62% |
1 |
2000 |
|
30 |
43% |
1 |
2000 |
|
40 |
24% |
1 |
2000 |
|
50 |
52% |
2 |
1800 |
|
60 |
43% |
2 |
1800 |
|
70 |
33% |
2 |
1800 |
|
80 |
24% |
2 |
1800 |
|
90 |
43% |
3 |
1200 |
|
100 |
36% |
3 |
1200 |
|
150 |
29% |
4 |
900 |
|
200 |
24% |
5 |
720 |
|
250 |
21% |
6 |
600 |
AMI
AMI is not supported in this release. HDB3 is the only supported encoding option for the E1 ATM card.
OVERSIZE MESSAGES
Oversize messages (>272 octets) will not be supported in this release. This limitation is a holdover from ATMANSI.
A general purpose implementation of the ATM HSL protocol stack would allow for 'Large MSUs' to be transferred across the physical link. The SSCOP layer is capable of handling data from SSCF that is up to 4096 byes long. Since SSCF does not add a trailer to MTP3 data, this equates to an MTP3 packet of 4096 bytes.
However, the current implementation of the ATM HSL stack restricts the largest MSU size to 272 bytes of MTP3 data. This restriction will be used for this feature, and as in the ATMANSI gpl, a the same UIM will be generated with a Large MSU is received.
2.112 E1/T1 MIM on EPM (E5-E1T1 Card) (Release 35.0)
Description
The E1/T1 MIM on EPM feature provides a single-slot, high-density E5-E1T1 card for channelized E1 and T1 link solutions. This card can be operated with a 40 Amp frame-level power budget and does not require a fan.
The E5-E1T1 card can be assigned a maximum of 32 signaling links of configurable channelized T1 connectivity. The links on the card can operate in a linkset with other links running at different speeds. The total number of provisioned T1 links cannot exceed the allowed system maximum (the quantity shown for the Large System # Links entry in the rtrv-ctrl-feat command output).
The E5-E1T1 card terminates 8 E1/T1 ports (trunks) and routes them to the A and B ports of the EAGLE 5 ISS backplane. These ports can be configured to select which E1/T1 ports are active and which channels on each port are used for signaling links.
The E5-E1T1 card supports one SE-HSL signaling link on one of the eight ports. Channelized operation is not possible on any E5-E1T1 card that is provisioned for SE-HSL. SE-HSL requires a Feature Access Key on a system level basis. The E5-E1T1 card provides copying and time-stamping of MSUs for all provisioned signaling links (up to 32 LSLs or 1 SE-HSL) simultaneously when the EAGLE 5 Integrated Monitoring Support (E5IS) feature is turned on.
Note:
EAGLE 5 ISS Release 35.0 supports only the T1 functions on the card. The E1 functions will be available in EAGLE 5 ISS Release 35.1.Modes of Operation
The E5-E1T1 card can be provisioned to operate in the E1 or T1 mode. The mode of operation defines the trunk format for the 8 ports on the card.
Along with the T1 mode, the E5-E1T1 card provides a Channel Bridging function that allows users to utilize T1 bandwidth that is not used by EAGLE 5 ISS signaling links. T1 ports 1, 3, 5, and 7 (master ports) can be independently channel bridged with their adjacent even-numbered (slave) T1 ports 2, 4, 6, and 8 to allow non-signaling data pass-through.
In T1 mode, the E5-E1T1 card generates an idle code in idle (unused) time slots. If the Channel Bridging function is used, idle codes are inserted into timeslots on even ports corresponding to the reflected signaling channels on the odd port.
EAGLE 5 ISS supports the Channel Bridging function for all combinations of master/line timing modes invoked by the adjacent equipment. Internal clock selection criteria ensure synchronous data paths through the bridged channels.
Thermal Management
The E5-E1T1 card includes and alarming provisions to protect the card from damage if environmental conditions hinder thermal stability. The EAGLE 5 ISS responses to increasing temperatures are as follows:
- Temp1 Exceeded—Major alarm raised
- Temp2 Exceeded—Critical alarm raised; failover initiated, traffic rerouted
- Temperature abated. Normal operation restored
Hardware Requirements
The E1/T1 MIM on EPM feature has the following hardware requirement::
- HIPR cards are required on each shelf that contains E5-E1T1 cards.
Limitations
The E1/T1 MIM on EPM feature has the following limitation:
- The E1 functions are not supported in EAGLE 5 ISS Release 35.0.
2.113 E1/T1 MIM on EPM (Release 35.1)
Description
The E1/T1MIM on EPM feature enhances the E1/T1 MIM on EPM feature from Release 35.0 by adding EAGLE 5 ISS support for E1 functionality and SE-HSL links. This Feature Notice documents only these enhancements. Refer to the EAGLE 5 ISS 35.0 Feature Notice for a detailed discussion of the E1/T1 MIM on EPM feature.
With support for the E1 functionality, the E5-E1T1 card can terminate 8 E1/T1 ports (trunks) and route them to the A and B ports of the EAGLE 5 ISS backplane. These ports can be configured to select which E1/T1 ports are active and which channels on each port are used for signaling links.
The E5-E1T1 card supports one SE-HSL signaling link on one of the 8 ports. Support for SE-HSL requires a system-level Feature Access Key.
The E5-E1T1 card provides copying and time-stamping of MSUs for all provisioned signaling links (up to 32 low-speed links ) simultaneously when the EAGLE 5 Integrated Monitoring Support (E5IS) feature is turned on.
Modes of Operation
The E5-E1T1 card can be provisioned to operate in the E1 or T1 mode. The mode of operation defines the trunk format for the 8 ports on the card.
In T1 mode, a port represents a time-division-multiplexed data stream of 24 channels with an aggregate data rate of 1.544 Mbps. In E1 mode, a port represents a time-division-multiplexed data stream of 32 channels with an aggregate data rate of 2.048 Mbps.
E1 and T1 port configurations cannot be mixed on a single card. The E5-E1T1 card provides a Channel Bridging function that allows use of E1T1 bandwidth that is not used by EAGLE 5 ISS signaling links. E1 and T1 ports 1, 3, 5, and 7 (master ports) can be independently channel bridged with their adjacent even-numbered (slave) E1 and T1 ports 2, 4, 6, and 8 to allow non-signaling data pass-through.
In the E1 or T1 mode, the E5-E1T1 card generates an idle code in idle (unused) time slots. If the Channel Bridging function is used, idle codes are inserted into timeslots on even ports corresponding to the reflected signaling channels on the odd port.
EAGLE 5 ISS supports the Channel Bridging function for all combinations of master/line timing modes invoked by the adjacent equipment. Internal clock selection criteria ensure synchronous data paths through the brIdged channels.
Note:
Channelized operation cannot be performed on any E5-E1T1 card that is provisioned for SE-HSL.
Hardware Requirements
The E1/T1 MIM on EPM feature requires HIPR cards on each shelf that contains E5-E1T1 cards.
Limitations
The E1/T1 MIM on EPM feature has the following limitations:
-
E1 and T1 port configurations cannot be mixed on a single card.
-
Channelized operation cannot be performed for any E5-E1T1 card that supports SE-HSL links.
2.114 E1/T1 Multi-Channel Interface Module (Release 28.0) (IP7 Release 6.0)
The E1/T1 Multi-Channel Interface Module (MIM) provides increased E1 signaling connectivity and a channelized T1 connection to the EAGLE STP.
The MIM increases the number of SS7 links (ports) the EAGLE handles per E1 card. This allows the EAGLE to interact in larger SS7 networks, as well as decreases the footprint of an EAGLE (i.e. previously 250 cards were required to support 500 links; now only 63 cards are required). The E1/T1 MIM can be used in systems equipped with either the IPMXor the HMUX board. The MIM also provides a new channelized T1 connection to the EAGLE. The MIM can replace an existing LIME1/LIMCH card (as an E1 terminating card or E1 channel card), with no reprovisioning required. E1 MIM is hot-swappable with LIM-E1.
Note:
For existing E1 customers, the E1 Administration feature will be activated after upgrading to Release 28.0, unless the source release is 26.3.
The E1/T1 Multi-Channel Interface Module (MIM) card has 2 physical backplane port connections, as other LIM cards do. These are referred to here as interface A and interface B. For the E1/T1 MIM, as with the existing LIM-E1 card, interface A has 2 ports of E1/T1 connectivity. These 2 ports are referred to as port #1 and port #2. Interface B provides the expansion port to service channel cards.
Refer to the Database Administration Manual - SS7 for detailed and configuration information.
Hardware Requirements
No new hardware other than the new MIM card itself (870-2198-01) is needed to support this feature.
For detailed information on hardware, refer to the NSD Hardware Manual.
2.115 E5-APP-B Card (ELAP 10.0)
The E5-APP-B card is designed to be integrated with applications that run on a Signal Transfer Point (STP). E5-APP-B cards are installed as a pair in an EAGLE shelf along with Ethernet communication equipment. For more information about EAGLE shelves, refer to EAGLE Hardware Manual.
The E5-APP-B card is a general-purpose application server (AS) that offers high transaction rates with low latency. The E5-APP-B card is a scalable computing platform constructed with state-of-the-art components packaged on a double-width card designed to fit into two slots of an EAGLE shelf. Each E5-APP-B card has two field-replaceable hard disk drives for data storage. Each E5-APP-B card is delivered pre-loaded with platform software and application software. E5-APP-B cards are installed as a pair for redundancy and high availability. DSM Service Module cards (870-1984-xx) are not supported with E5-APP-B based applications.
For more information about the E5-APP-B card, refer to the new manuals which fully describe the card and its installation, operation, and maintenance:
- E5-APP-B Hardware and Installation Manual
- ELAP Alarms and Maintenance on the E5-APP-B Platform
2.116 E5-APP-B Card (EPAP 15.0)
The E5-APP-B card is designed to be integrated with applications that run on a Signal Transfer Point (STP). E5-APP-B cards are installed as a pair in an EAGLE shelf along with Ethernet communication equipment. For more information about EAGLE shelves, refer to EAGLE Hardware Manual.
The E5-APP-B card is a general-purpose application server (AS) that offers high transaction rates with low latency. The E5-APP-B card is a scalable computing platform constructed with state-of-the-art components packaged on a double-width card designed to fit into two slots of an EAGLE shelf. Each E5-APP-B card has two field-replaceable hard disk drives for data storage. Each E5-APP-B card is delivered pre-loaded with platform software and application software. E5-APP-B cards are installed as a pair for redundancy and high availability. DSM Service Module cards (870-1984-xx) are not supported with E5-APP-B based EPAP systems.
For more information about the E5-APP-B card, refer to the new manuals which fully describe the card and its installation, operation, and maintenance:
- E5-APP-B Hardware and Installation Manual
- EPAP Alarms and Maintenance on the E5-APP-B Platform
2.117 E5-ATM Card (Release 38.0)
The E5-ATM card supports both ANSI and ITU implementations for SS7 signaling information. This card can be used to replace the LIM-ATM and E1-ATM cards: however, the LIM-ATM and the E1-ATM cards are still supported and can co-exist with the E5-ATM card in the same node.
The E5-ATM card supports a new atmhc GPL.
The E5-ATM card can support 2 ATM signaling links, operating at 1 Erlang. The card can be configured for either E1 (ITU) or T1 (ANSI). Both links must be either E1 or T1.
If the B signaling link is provisioned, then the card slot is no longer compatible with the LIM-ATM or E1-ATM cards. Inserting one of these cards after provisioning the B link causes the card to auto-inhibit.
2.117.1 Feature Control Requirements
There are no feature control requirements identified for this feature.
2.117.2 Hardware Requirements
HIPR cards must be installed in the shelf where the E5-ATM card is installed.
The E5-ATM card provides connectivity for two E1/T1 ports on the Port A backplane connector, allowing the two links to be provisioned. These ports can be accessed with a 2-port or 4-port cable. An interface adapter (P/N 830-1342-05) allows the two ports to be physically split to two different cables/patch panels. If it is desired to move the second E1/T1 port to the Port B backplane connector, then an adapter and another cable (1-, 2-, or 4-port) must be used.
2.118 E5-ATM-B (Release 44.0)
A new E5-ATM-B card (Part Number 870-2972-01) is introduced. This card is based on the EPM-B module. See EPM-B Based Cards(Release 44.0) for information common to all cards based on the EPM-B.
E5-ATM-B cards can be inserted in slots that are provisioned for ATMANSI or ATMITU applications. The card is provisioned using the ent-card command with type=limatm and appl=atmansi for ANSI or type=lime1atm and appl=atmitu for ITU.
2.118.1 Feature Control Requirements
Message Flow Control (MFC) and the Fan feature must be on before an E5-ATM-B card can be brought into service. See Message Flow Control Replacement for TVG (Release 44.0) for more information.
If MFC and the Fan feature are on, then E5-ATM-B cards can co-exist with and be used to replace E5-ATM cards (Part Numbers 870-1872-XX) without configuration changes. If MFC or the Fan feature is off, then the E5-ATM-B cards will auto-inhibit.
When the EAGLE contains B-series cards which include E5-ENET-B, E5-ATM-B, E5-SM8G-B, and E5-E1T1-B, the following cards are not supported in EAGLE Release 44.0 except during migration to the B-series cards:
- DCM card (870-1945-xx)
- DSM card (870-1984-xx)
- EDCM card (870-2372-xx) used for SLAN or STC functionality
- EDCM-A card (870-2508-xx) used for SLAN or STC functionality
2.119 E5-E1T1-B (Release 45.0)
The E5-E1T1-B card (Part Number 870-2970-01) is a single slot card based on the EPM-B module and can be inserted in slots provisioned for SS7ANSI or CCS7ITU applications.
The E5-E1T1-B card is provisioned using the ent-card command with the type=lime1 or type=limt1 parameter. The appl=ss7ansi parameter is used for ANSI, and the appl=ccs7itu parameter is used for ITU.
The E5-E1T1-B card provides eight E1 or T1 termination ports, processing up to 32 signaling links of configurable channelized E1 or T1 connectivity. The eight ports reside on backplane connectors A and B. All ports on a single E5-E1T1-B card must operate in the same carrier scheme of E1 or T1. An EAGLE node can have a mix of E1 and T1 signaling links with some E5-E1T1-B cards operating in E1 mode and other E5-E1T1-B cards operating in T1 mode.
The maximum provisionable links for the E5-E1T1-B card is 32 links. Total system signaling link capacity depends on other cards in the system and the enabled features, and must not exceed the provisioning limit of the EAGLE.
Channelized Mode
The E5-E1T1-B card provides access to eight E1 or T1 ports residing on backplane connectors A and B. Each data stream consists of 24 T1 or 31 E1 signaling links assigned according to a Time-Division Multiplex (TDM) scheme. Each channel occupies a unique timeslot in the data stream and can be selected as a local signaling link on the interface card. Each card can select up to a total of 32 signaling links.
Channel Bridging
Channel Bridging is the processing of signaling channels that are intermixed on trunks with voice or data channels. The E5-E1T1-B card provides Channel Bridging which allows for better utilization of bandwidth without dedicating entire trunks to signaling. Non-signaling channels are bridged to an adjacent E1 or T1 port for transport to other network devices. Signaling channels are merged to non-signaling data for transmission to the mixed network.
2.119.1 Hardware Requirements
- Fan trays must be installed on shelves that contain E5-E1T1-B cards.
- The IMT bus must contain at least one HIPR or HIPR2 card before an E5-E1T1-B card can connect with the bus. If HMUX cards are used, then the cards cannot access the IMT bus. If the shelf contains both HMUX and HIPR/HIPR2 cards, then the E5-E1T1-B card connects with the HIPR/HIPR2 cards only. HMUX cards with HIPR/HIPR2 cards on the same shelf are supported only during migration to the E5-E1T1-B cards.
- Dual 60A power feeds are recommended for all frames that host E5-E1T1-B cards.
- The BLMCAP GPL must be flashed on E5-E1T1-B cards before the card can be initialized.
2.120 E5-E1T1-B Increased Throughput (Release 46.0)
The E5-E1T1-B Increased Throughput increases the number of supported low speed links per E5-E1T1-B card from 32 to 64.
2.121 E5-ENET SLAN to ECAP (Release 41.1)
The E5-ENET SLAN to ECAP feature allows the ECAP server to interface with E5-ENET cards. EDCM and EDCM-A cards continue to be supported.
2.122 E5-ENET-B (Release 44.0)
A new E5-ENET-B card (Part Number 870-2971-01) is introduced. This card is based on the EPM-B module. See EPM-B Based Cards(Release 44.0) for information common to all cards based on the EPM-B.
The E5-ENET-B card can be used with the EROUTE, IPGW, IPLIM, IPLIMI, IPS, IPSG, SS7IPGW, and STPLAN applications.
E5-ENET-B with EROUTE
E5-ENET-B cards can be used in slots that are
provisioned for the EROUTE application. The card is
provisioned using the ent-card command with type=stc and appl=eroute.
E5-ENET-B with IPGWx, IPLIMx, SS7IPGW
E5-ENET-B cards can be used in slots that are
provisioned for the IPGWI, IPLIM, IPLIMI, or SS7IPGW
application. The card is provisioned using the
ent-card command
with type=dcm and
appl=ipgwi/iplim/iplimi/ss7ipgw.
E5-ENET-B with IPS
See IPS Application on E5-ENET-B (Release 44.0) for information on the E5-ENET-B card running the IPS application.
E5-ENET-B with IPSG
E5-ENET-B cards can be used in slots that are
provisioned for the IPSG application. A new ENETB
card type is introduced for use with the E5-ENET-B
card and IPSG application. The card is provisioned
using the ent-card
command with type=enetb and appl=ipsg.
An E5-ENET-B card with the IPSG application has a capacity of 6500 TPS. If E5-ENET-B cards are installed in slots that are provisioned for E5-ENET cards, then the E5-ENET-B cards process at 5000 TPS. If an E5-ENET card is installed in a slot provisioned for an E5-ENET-B card, then the E5-ENET card auto-inhibits.
If the E5-ENET-B IPSG High Throughput (Release 44.0) feature is turned on, then the E5-ENET-B cards process at rates up to 9500 TPS.
E5-ENET-B with STPLAN
E5-ENET-B cards can be used in slots that are
provisioned for the STPLAN application. The card is
provisioned using the ent-card command with type=dcm and appl=stplan.
2.122.1 Feature Control Requirements
Message Flow Control (MFC) and the Fan feature must be on before an E5-ENET-B card running the EROUTE, IPGW, IPGWI, IPLIM, IPLIMI, or IPSG application can be brought into service. See Message Flow Control Replacement for TVG (Release 44.0) for additional information on MFC.
Note:
The E5-ENET-B card running the IPS application does not require MFC. See IPS Application on E5-ENET-B (Release 44.0) for additional information.If MFC and the Fan feature are on, then E5-ENET-B cards can co-exist with and be used to replace E5-ENET cards (Part Numbers 870-2212-XX), EDCM cards (Part Numbers 870-2372-XX) and EDCM-A cards (Part Numbers 870-2508-XX) without configuration changes. If MFC or the Fan feature is off, then the E5-ENET-B cards will auto-inhibit.
When the EAGLE contains B-series cards which include E5-ENET-B, E5-ATM-B, E5-SM8G-B, and E5-E1T1-B, the following cards are not supported in EAGLE Release 44.0 except during migration to the B-series cards:
- DCM card (870-1945-xx)
- DSM card (870-1984-xx)
- EDCM card (870-2372-xx) used for SLAN or STC functionality
- EDCM-A card (870-2508-xx) used for SLAN or STC functionality
2.123 E5-ENET-B IPSG High Throughput (Release 44.0)
The E5-ENET-B IPSG High Throughput feature allows an E5-ENET-B (Release 44.0) card running the IPSG application to have a capacity of up to 9500 TPS.
If the feature is not turned on, then an E5-ENET-B card running the IPSG application continues to have a capacity of 6500 TPS.
Turning on the E5-ENET-B IPSG High Throughput feature impacts the baseline configuration for the E5-ENET-B card running the IPSG application as shown in Table 2-28.
Table 2-28 Baseline Configuration Changes for the E5-ENET-B IPSG High Throughput Feature
| E5-ENET-B Card Baseline Configuration | E5-ENET-B IPSG High Throughput feature OFF | E5-ENET-B IPSG High Throughput feature ON |
|---|---|---|
| Maximum TPS for the card | 6500 | 9500 |
| Average MSU size (bytes) | 0-272 | 0-120 |
| Max RTT (ms) | 120 | 50 |
| Max number of links/associations | 16 | 4 |
| Protocol | M2PA and M3UA | M2PA |
Note:
Standard de-rating considerations apply.2.124 E5-MCPM-B (Release 44.0)
A new E5-MCPM-B card (Part Number 870-3089-01) is introduced. This card is based on the EPM-B module and is used to replace the EDSM-2G cards (Part Numbers 870-2372-XX). See EPM-B Based Cards(Release 44.0) for information common to all cards that are based on the EPM-B.
EDSM-2G and E5-MCPM-B cards are referred to collectively as MCPM cards.
The E5-MCPM-B card is used to perform Measurements Collection Processor and E5-OAM Integrated Measurements functionality for nodes with a link capacity greater than 2,400 (1,200 if the 15 Minute Measurements feature is enabled). E5-OAM Integrated Measurements is used for nodes with a link capacity of 2400/1200 or less.
E5-MCPM-B cards can be inserted in slots that are provisioned for the MCP application. The card is provisioned using the ent-card command with type=mcpm and appl=mcp. A new MCPHC GPL is introduced to run the Measurements Platform feature on the E5-MCPM-B cards.
2.124.1 Feature Control Requirements
The Fan feature must be turned on before an E5-MCPM-B card can be brought into service.
If the Fan feature is turned on, then E5-MCPM-B cards can co-exist with and be used to replace EDSM-2G cards (Part Numbers 870-2372-XX) without configuration changes. If the Fan feature is off, then the E5-MCPM-B cards will auto-inhibit.
2.125 E5-OAM Cards (E5-MASP and E5-MDAL) (Release 40.1)
The existing set of EAGLE 5 ISS OA&M cards (GPSM-II, TDM, and MDAL cards) is replaced by an E5-OAM card set. This set contains an E5-MASP assembly (870-2903-01) and an E5-MDAL card (870-2900-01).
The E5-MASP assembly consists of an E5-MCAP card and an E5-TDM card. These cards are physically attached to each other and must always be used or replaced together. The E5-MASP assembly can be inserted into slots 1113/1114 or 1115/1116.
The E5-MDAL card can be inserted into slot 1117.
Two E5-MASP assemblies and an E5-MDAL card comprise an E5-OAM set.
Legacy GPSM-II, TDM, or MCAP cards cannot exist in the system with any of the new cards. All of the relevant cards must be legacy or all of the cards must be new. The only exception is during a hardware migration from a legacy system to a new system.
A new blmcap flash GPL is used to maintain a tar image of the code that is required for the E5-MCAP cards. A new oamhc GPL is used to perform OAM functions on the E5-MCAP cards.
The drive configuration for the E5-OAM card set significantly differs from the OAM card set. The E5-MDAL card does not contain an optical drive. The E5-TDM contains a hard drive. The E5-MCAP card contains two USB ports, a latched port, which replaces the existing MO drive as the removable drive, and a flush mount port. After the E5-OAM card set is introduced, activities for those cards can be performed on either the hard drive or the removable drives.
2.126 E5-OAM Integrated GLS (Release 44.0)
The E5-OAM Integrated GLS feature (Integrated GLS) migrates Generic Loading Services (GLS) functionality for the Gateway Screening feature from the TSM (Part Numbers 870-1289-XX, 870-1291-XX, and 870-1292-XX) and E5-TSM (Part Number 870-2943-03) cards to the E5-OAM.
The Integrated GLS feature supports all TSM and E5-TSM card functionality. The feature can exist in mixed mode with TSM-based and E5-TSM-based GLS during migration.
2.127 E5-OAM Integrated Measurements (Release 42.0)
The E5-OAM Integrated Measurements (Integrated Measurements) feature allows the Measurements subsystem on the E5-OAM MASP to provide full support for the collection and reporting for all collectible measurement entities for nodes configured with up to 1200 links. Systems with more than 1200 links must install the Measurements Control Platform (MCP) for full measurement support.
The Integrated Measurements feature obsoletes the use of the File Transfer Area (FTA) for measurements, and replaces the FTA functionality with FTP functionality. The E5-OAM/IP Ethernet Support enhancement is used to provide Ethernet support for FTP.
This feature requires the Measurements Subsystem to transition to the Integrated Measurements. The transition is performed by provisioning the oamhcmeas option in the chg-measopts command. Provisioning this parameter also turns on the Integrated Measurements collection function.
Note:
The Integrated Measurements collection function cannot be turned off after it has been turned on.If the MCP is enabled prior to the transition, then the transition sequence transfers all historical measurements data from the MCP to the OAM. The MCP does not collect and report measurements during transition.
After the transition is complete, the OAM takes control of the Measurements Subsystem and is responsible for collection and reporting. The MCPM cards are set to IS-ANR - Restricted state, and the MCP is turned off.
2.128 E5-OAM SNMP Support (Release 45.0)
The E5-OAM SNMP Support feature allows the EAGLE to communicate directly with a Network Management System (NMS) without requiring an intermediary Element Management System (EMS). After this feature is enabled and turned on, the SNMP traps for alarms are sent to an NMS or a set of NMSs specified by the ent/chg/rtrv-snmp-host commands. Configured NMSs can request a resynchronization for all of the existing UAMs. Each provisioned NMS receives a heartbeatTrap at a rate determined by the NMS declaration. The heartbeatTrap indicates to the NMS that the network connection is intact during periods of low UAM/UIM activity.
For each NMS, a host name and IP address must be specified with the ent-snmp-host command. Optional parameters allow the SNMP command and trap port numbers to be changed, as well as allow the TRAP community string to be specified for the traps sent to the NMS, and set the heartbeatTrap interval. After a host is provisioned, the optional parameters may be changed with the chg-snmp-host command. The system-wide SNMP options can be changed with the chg-snmpopts command. The chg-snmpopts command enables the GET and SET community strings to be changed, and enables or disables sending UIM as traps to the NMS.
2.129 E5-SLAN Throughput Throttle for ECAP Connection (Release 41.1)
The E5-SLAN Throughput Throttle for ECAP Connection feature allows the TPS on E5-ENET cards to be restricted to avoid overloading the ECAP server, which can handle a maximum of 5000 TPS.
2.130 E5-SM4G Card (Release 37.0)
Description
The E5-SM4G card enhances the EAGLE 5 ISS support for the EPAP and ELAP-based features by providing performance improvement over the DSM cards that currently run the vsccp application. DSM cards will continue to be supported, but are being replaced with E5-SM4G cards for new initial and extension shipments.
The E5-SM4G card requires the E5-SM4G Throughput Capacity feature to be enabled to achieve maximum processing. A FAK is required to enable the E5-SM4G Throughput Capacity feature.
The new E5-SM4G card running the sccphc GPL and the vsccp application performs the same functions as the current DSM card for EPAP-based and ELAP-based features.
The E5-SM4G card is provisioned with card type dsm and the vsccp application, allowing the E5-SM4G card to replace a DSM card in the control or extension frame without re-provisioning.
The E5-SM4G Throughput Capacity feature performs the following functions:
- Allows each E5-SM4G card to operate at a rate of 5,000 TPS for SCCP traffic that is processed entirely by GTT.
- Allows each E5-SM4G card to operate at a rate of 3,125 TPS if part of the SCCP traffic is processed by EPAP-based features.
- Allows achievement of the maximum system TPS capacity provided by the 150,000 GTT TPS feature and the 75,000 EPAP TPS feature. See “150,000 GTT TPS and 75,000 EPAP TPS” on page FN-8.
If the E5-SM4G Throughput Capacity feature is not enabled, then the E5-SM4G card continues to operate at the DSM-equivalent capacities:
- GTT only mode=1700 TPS per E5-SM4G card
- EPAP-based feature node if the 1100 TPS/DSM feature is not enabled = 850 TPS per E5-SM4G card
- EPAP-based feature node if the 1100 TPS/DSM feature is enabled = 1100 TPS per E5-SM4G card
HIPR cards must be installed in any shelf that contains an E5-SM4G card. HIPR cards must be installed in all shelves in the system before the E5-SM4G Throughput Capacity feature can be enabled to increase the card and system TPS capacity.
The E5-SM4G card cannot be inserted into a node that is provisioned to process more than 192 million LNP numbers. If the E5-SM4G card is inserted into a node that can process more than 192 million LNP numbers, the card auto-inhibits.
The E5-SM4G card can co-exist with DSM cards and operate at a capacity of 5,000 TPS. The E5-SM4G card can co-exist with TSM cards that are used for GTT and GLS only, and can co-exist with two channel LIM cards per node.
The E5-SM4G card provides two physical 10/100 Mbps Ethernet ports.
The E5-SM4G card supports thermal management and alarming provisions.
Feature Control Requirements
If the E5-SM4G Throughput Capacity feature is used, then the following feature control requirements apply:
- A FAK for part number 893-0191-01
- A temporary key cannot be used to enable the feature.
- After the feature has been turned on, it cannot be turned off.
- The feature cannot be enabled if any of the following features or options is turned on:
- E5IS (EAGLE 5 Integrated Monitoring Support) feature
- LNP feature
- ANSIGFLEX STP option
Hardware Requirements
The E5-SM4G card requires HIPR cards in card locations 9 and 10 in the shelf in which it is installed.
Limitations
The E5-SM4G card provides 3.1 GB of memory while the DSM card provides approximately 3.6 GB of memory. This reduction in memory limits the number of entries to a maximum of 84 million for EPAP applications and 192 million for LNP. Additional E5-SM4G cards may be required to match the processing capacity of DSM for these applications.
2.131 E5-SM8G-B (Release 44.0)
A new E5-SM8G-B card (Part Number 870-2990-01) is introduced. The E5-SM8G-B card is a dual-slot card with a dual-core processor.
The E5-SM8G-B card can be inserted in slots that are provisioned for the VSCCP application. The card is provisioned using the ent-card command with type=dsm and appl=vsccp.
As of Release 44, references to Service Module cards include E5-SM8G-B cards.
A new performance key is introduced for the E5-SM4G Throughput Capacity feature. This key (Part Number 893-0191-03) is supported only on the E5-SM8G-B card and allows the card to run at 10,000 TPS. The E5-SM8G-B card also supports the existing E5-SM4G Throughput Capacity performance keys at their associated TPS levels.
2.131.1 Feature Control Requirements
Message Flow Control (MFC) functionality and the Fan feature must be on before an E5-SM8G-B card can be brought into service. See Message Flow Control Replacement for TVG (Release 44.0) for more information.
If MFC and the Fan feature are on, then E5-SM8G-B cards can co-exist with and be used to replace DSM (Part Numbers 870-1984-XX) and E5-SM4G (Part Numbers 870-2860-XX) cards without configuration changes. If MFC or the Fan feature is off, then the E5-SM8G-B cards will auto-inhibit.
The new E5-SM4G Throughput Capacity performance level (Part Number 893-0191-03) must be enabled before the E5-SM8G-B card can run at 10,000 TPS.
When the EAGLE contains B-series cards which include E5-ENET-B, E5-ATM-B, E5-SM8G-B, and E5-E1T1-B, the following cards are not supported in EAGLE Release 44.0 except during migration to the B-series cards:
- DCM card (870-1945-xx)
- DSM card (870-1984-xx)
- EDCM card (870-2372-xx) used for SLAN or STC functionality
- EDCM-A card (870-2508-xx) used for SLAN or STC functionality
2.131.2 Hardware Requirements
- Fan trays must be installed on shelves that contain E5-SM8G-B cards.
- The IMT bus must contain at least one HIPR or HIPR2 card before an E5-SM8G-B card can connect with the bus. If HMUX cards are used, then the cards cannot access the IMT bus. If the shelf contains both HMUX and HIPR/HIPR2 cards, then the E5-SM8G-B card connects with the HIPR/HIPR2 cards only.
Note:
HMUX cards with HIPR/HIPR2 cards on the same shelf are supported only during migration to the EPM-B based cards.
2.132 EAGLE Alarm Modifications for Synchronization with Harris (Release 31.5)
Description
There is an issue between the Harris monitoring system and the alarm generation/clearing shown by the EAGLE. There are multiple instances where the EAGLE will either silently clear an alarm, or silently refresh an alarm to a different alarm. Since the Harris system is relying on the EAGLE output to set or clear alarms on EAGLE devices, the two systems alarming counts are frequently out of sync.
Limitations
If a customer is only using a normal KSR terminal for monitoring, there is a potential to drop alarms from the terminals output if the output buffers fill up with data such as hourly reports, IMT reports, Measurements reports, excessive UIM output, etc. There are ways to minimize this extra output to significantly reduce the likelihood of such a buffer overflow:
-
Turn off Traffic output group (TRAF) for the terminal used by Harris
-
Use UIM thresholding
Note:
using the new EMSALM terminal solves this limitation
Due to the sheer number of Alarms that are potentially generated during link alignments for an EAGLE with a large number of signaling links, the multiple signaling link alarm states continue to be done without output. The first Signalling Link alarm is output but subsequent alarms for that device transition silently. This suppression of output is OK for signaling links, in that all the signaling link silent alarm transitions are within the same alarm level, MAJR. When the signaling link alarms are cleared, there is an appropriate clearing alarm issued for each affected link. To cycle through and issue each overtaking signaling alarm for every link over an "init-sys" on a large system output overwhelms the output buffer, and alarms would be lost.
In the event that the Harris system's alarms get out of Sync with the EAGLE's alarms, it is up to the Harris system both to detect and correct its alarm counts to match that of the EAGLE.
2.133 EAGLE Collector Application Processor (ECAP) on the T1200 Platform (ECAP 41.1)
ECAP release 41.1 will support a new T1200 server, along with the existing support for the T1100 server. All existing ECAP functionality (from prior releases 1.0 and 40.1) supported on the T1100 will now be supported on the T1200. Also, new ECAP functionality introduced in release 41.1 will be supported on both the T1100 and the T1200 servers. For more information, refer to the Feature Manual - ECAP.
Operating System
The ECAP server operates on the Tekelec Platform Development (TPD) 3.3 32-bit (i686/i386) Linux distribution operating system.
TPD 3.3
TPD 3.3 provides a method for trapping platform Alarm conditions. ECAP installation turns on the TPD snmpAgent, and enables configuration of the agent via the platcfg menu.
In addition to ecapadm, ECAP installation provides an ecapuser account. This is a limited account that can NOT control or configure the ECAP application via ecapcfg.
For additional information regarding the ECAP server's architecture, processor type, and node name, execute the uname -a command on each server to generate output such as this example:
Output Example
# uname –a
Linux ECAP 2.6.18-1.2849prerel3.3.0_63.1.0 #1 SMP Thu Nov 13 02:48:50 EST 2008 i686 i686 i386 GNU/Linux
2.133.1 Hardware Requirements
Hardware requirements for the ECAP on the T1200 platform are as follows:
-
T1200 AS Frame
Note:
EAGLE 5 ISS supports a single ECAP Frame. -
Power Distribution breaker panel
-
Two or four Telco switches
Note:
Two switches (one pair) must be configured if 12 ECAP servers or less are configured. Four switches (two pair) must be configured if more than 12 ECAP servers are configured. -
A T1200 server , running the Integrated Q.752 MTP/SCCP Accounting Feed feature.
-
The number of T1200 ECAP Servers per frame is two to eighteen.
-
The EAGLE 5 ISS system used with the ECAP must be equipped with SSEDCM or E5-ENET card types running the SLAN application. The SLAN application cards must be provisioned with 100 Mbps links in order to achieve 10000 MSUs/sec.
The ECAP Servers are configured in an N+1 configuration based on the maximum expected traffic rate as shown in Table 2-29.
Table 2-29 MSU to T1200 Server Mapping
| MSU per Second | T1200 Servers |
|---|---|
|
<= 10000 |
2 |
|
10001 to 20000 |
3 |
|
20001 to 30000 |
4 |
|
30001 to 40000 |
5 |
|
40001 to 50000 |
6 |
|
50001 to 60000 |
7 |
|
60001 to 70000 |
8 |
|
70001 to 80000 |
9 |
|
80001 to 90000 |
10 |
|
90001 to 100000 |
11 |
|
100001 to 110000 |
12 |
|
110001 to 120000 |
13 |
|
120001 to 130000 |
14 |
|
130001 to 140000 |
15 |
|
140001 to 150000 |
16 |
|
150001 to 160000 |
17 |
|
160001 to 170000 |
18 |
Memory and Disk Space
The ECAP application can be installed on either of these hardware platforms:
- T1100 server consisting of two mirrored 250 GB hard drives
- T1200 server consisting of three mirrored 146 GB hard drives
Memory and disk requirements for the ECAP application are due to the massive amounts of data that can be collected from the EAGLE 5 ISS. The ECAP installation take about 10-12 MB of disk space.
2.134 EAGLE Database Increase to 480M DN + 600M Flexible IMSI/IMEI Allocation (Release 46.7)
In cooperation with the EPAP eXtreme (EPAPX) DB Expansion feature, the EPAP is able to support 480M individual DN entries, 600M individual IMSI entries or 600M individual IMEI entries. The EPAPX feature is supported only for 64-bit flash running on an EAGLE system for SLIC cards. The EPAPX feature cannot be turned on if the system is equipped with SM8G-B cards to run EPAP-based features.
When the EPAP is running on Release 16.3 with its full capacity, DN-based SLIC-SCCP cards are able to load 480M individual DN entries. IMSI-based SLIC-SCCP cards are able to load 480M individual IMSI entries or 600M individual IMEI entries. This is applicable when the EPAP Split DB feature is ON. DB allocation to EAGLE EPAP-based cards is flexible, as per the configurations done on the EPAP side.
If the EPAP Split DB feature is OFF, then the DN & IMSI tables are loaded onto a single EPAP card. In this case the DN + IMSI entries must be less than 480M. The exact allowed combinations are listed in the Table 2-30.
Table 2-30 EAGLE Feature and EPAPX DB Capacity Combinations
| EPAP Split DB Feature | STPOPTS: EPAX | Max Ind. DNs | Max Ind. IMSIs | Max Ind. DNs = Ind. IMSIs | Max Ind. IMEIs | Max RTDB Size (DN=IMSI=IMEI) supported on Ind. SLIC |
|---|---|---|---|---|---|---|
| OFF | OFF, EPAP240M OFF | 120M | 120M | 120M | 48M | 120M (DN)
135M (IMSI) |
| ON | OFF, EPAP240M OFF | 120M | 120M | 240M | 48M | 120M (DN)
135M (IMSI) |
| ON | OFF, EPAP240M ON | 240M | 240M | 480M | 48M | 240M (DN)
288M (IMSI) 528M (EPAP) |
| OFF | ON | 480M | 480M | 480M | 480M | 480M (DN + IMSI + IMEI) |
| ON | ON | 480M | 600M | 1080M | 600M | 480M DN
600M IMSI |
To enable the 480M DN & 480M IMSI/600M IMEI capacity expansion on
EAGLE, the epapx parameter is introduced in the STPOPTS table. The SLIC-SCCP
cards on EAGLE are able to load 480M DN entries only when the
stpopts:epapx parameter is ON. Similarly,
SLIC-SCCP cards on EAGLE are able to load 480M IMSI or 600M IMEI entries only
when the
STPOPTS: EPAPX parameter is ON.
See "Activating the EPAPX DB Expansion Feature" in Database Administration - GTT User's Guide for more information.
2.135 Eagle Eyes OAM Friendly Commands (Release 46.0)
The Eagle Eyes OAM Friendly Commands feature allows users to configure and perform Eagle Eyes traffic captures using OAM commands.
2.136 EAGLE Frame Power Budget Alarm (Release 35.0)
Description
The EAGLE Frame Power Budget Alarm feature issues an alarm if the power consumption of cards in a frame nears the frame-level power capacity. The power capacity value can be provisioned in the Frame Power Threshold (FPT) table or a default value of 30 Amps can be used.
Note:
The value in the FPT table would be provisioned based on FAP configuration and power feed.The feature identifies the type of cards in a frame, calculates potential power consumption based on the frame-level population of cards, compares calculated power consumption to a frame-level power capacity figure, and raises alarms based on provisioned thresholds.
The new rtrv-stp command can be used to display the power consumption and power threshold values for all frames or a specific frame in the system.
Hardware Requirements
None
Limitations
The EAGLE Frame Power Budget Alarm feature has the following limitation:
- During initialization and switchover, frame power consumption is calculated using information from the various cards; therefore, the correct power consumption value is calculated only after information from all of the cards have been processed by the Frame Power Budget Alarm task.
2.137 EAGLE Initiated OAP User Interface (Release 24.0)
Description
In Release 24.0, the OAP configuration information is entered from the EAGLE terminals into the EAGLE database. When the configuration of an OAP needs to be updated, the OAP configuration data in the EAGLE database is sent to the specified OAP.
OAP Commands
The EAGLE uses these commands to configure and display the OAP data in the database and send this data to the OAP. Refer to the Commands Manual for current usage information.
-
chg-oap-config -
chg-oap-lkeys -
act-oap-config -
rtrv-oap-config
This feature can be used to configure and update the Texas Micro OAPs currently being used or the Embedded OAPs introduced in Release 24.0. This feature cannot be used to upgrade the OAP software. Upgrading the OAP software must be performed by a terminal connected directly to the OAP.
CHG-OAP-CONFIG
The chg-oap-config command is used to configure the EAGLE database with the OAP configuration information. This information is sent to the specified OAP with the act-oap-config command.
CHG-OAP-LKEYS
The chg-oap-lkeys command is used to enter the license keys of the DSET APLI, DSET DSGRuntime, Solstice OSI, and Solstice X.25 third party OAP software into the EAGLE database. The license keys are not sent to the OAP with the act-oap-config command, but are used when auditing the OAP and EAGLE configuration data.
ACT-OAP-CONFIG
The act-oap-config command is used to update the OAPs with the configuration data entered into the EAGLE database with the chg-oap-config command.
RTRV-OAP-CONFIG
This command displays the OAP configuration information in the EAGLE database that has been configured with the chg-oap-config and chg-oap-lkeys commands.
CHG-SID
When the EAGLE’s CLLI has been entered into the database or changed with the chg-sid command, the OAP configuration must be changed to include the new CLLI value. When this change to the EAGLE’s CLLI has been made, the following warning message is displayed in the scroll area of the terminal display, reminding the user that the OAP configuration must be updated with the act-oap-config command.
LNP Service Commands
When the LNP feature is on, the LNP services CLASS, CNAM, LIDB, and ISVM must be in the OAP configuration in the EAGLE database. When these services are added to the database (with the ent-lnp-serv command), removed from the database with the dlt-lnp-serv command, or changed with the chg-lnp-serv command, the OAP configuration must be updated with the act-oap-config command. When any of these changes to the LNP services have been made, the following warning message is displayed in the scroll area of the terminal display, reminding the user that the OAP configuration must be updated with the act-oap-config command.
Auditing the OAP Database
In order to keep OAP database synchronized with the EAGLE, a checksum is created using all of the OAP configuration data stored on the EAGLE. The OAP also calculates this checksum based on the data it has. This checksum is returned by the OAP with every forced maintenance poll allowing the EAGLE to compare and act on the result. If the checksum values do not agree, the EAGLE generates a minor alarm (UAM 0364) within 10 seconds:
UAM 0364 is cleared within five seconds after the EAGLE detects that the databases are synchronized again, and the checksum values of the databases agree, with UAM 0365:
2.138 EAGLE Measurement Reports (Release 20.0)
EAGLE STP measurements provide support for STP performance management, SS7 traffic monitoring and engineering, and Specific feature performance analysis (STPLAN).
Refer to the Maintenance Manual for current EAGLE measurement information.
2.139 EAGLE MNP Data Base support for 240M DN (Release 46.3)
This feature expands the capacity of the EPAP and EAGLE Data Base to support 240M individual DN entries, 240M individual IMSI entries and 48 million individual IMEI entries.
Table 2-31 EAGLE Feature and EPAP DB Capacity Combinations
| EPAP Split DB Feature | STPOPTS: EPAP240M | Max Individual DNs | Max Individual IMSIs | Max Individual DNs + Individual IMSIs | Max Individual IMEIs | E5-SM4G Allowed |
|---|---|---|---|---|---|---|
| OFF | OFF | 120M | 120M | 120M | 32M | Yes |
| ON | OFF | 120M | 120M | 240M | 32M | Yes |
| OFF | ON | 240M | 240M | 240M | 48M | No |
| ON | ON | 240M | 240M | 480M | 48M | No |
To enable the 240M DN & 240M IMSI + 48M IMEI capacity expansion on EAGLE, a new parameter EPAP240M is introduced in the STPOPTS table. The E5-SM8G-B cards on EAGLE are able to load more than 120M DN entries only when the STPOPTS: EPAP240M parameter is ON.
2.139.1 Hardware
The EAGLE MNP Data Base support for 240M DN feature is supported on E5-SM8G-B cards.
This feature has a dependency on 64-bit GPLs. The E5-SM8G-B cards must be running 64-bit GPLs in order to support the larger RTDB data from the EPAP. If the E5-SM8G-B cards are not already running 64-bit GPLs, then the flash GPLs on the E5-SM8G-B cards need to be manually converted to 64-bit. Refer to the Notes section for the init-flash command in Commands User's Guide for detailed instructions for converting to 64-bit GPLs.
E5-SM4G cards are unable to load more than 120M DN or 120M IMSI entries. If E5-SM4G cards in the EAGLE system are in IS-NR/ACTIVE state, the STPOPTS: EPAP240M option will not be turned ON. If STPOPTS: EPAP240M is ON, the E5-SM4G cards will be auto-inhibited if present or hot-swapped with E5-SM8G-B cards.
2.140 EAGLE OA&M IP Security Enhancements (EAGLE Releases 30.0, 30.2, IP7 Secure Gateway Release 8.0)
Description
The EAGLE OA&M IP Security Enhancements feature provides tools to securely pass data across an otherwise non-secure network. Once the EAGLE OA&M IP Security Enhancements Feature is turned on, the EAGLE allows only secure connections from approved clients, and protects sensitive passwords and information while in transit between the EAGLE and a host.
The EAGLE OA&M IP Security Enhancements feature uses a software package called Secure Shell. Secure Shell (SSH) is a protocol for secure remote login and other network services over an insecure network. SSH encrypts and authenticates all EAGLE IPUI traffic, incoming and outgoing (including passwords) to effectively eliminate eavesdropping, connection hijacking, and other network-level attacks.
SSH consists of several component applications, two of which are relevant for IPUI enhancements: SSH client program for secure remote login (an enhancement for telnet), and SFTP, the secure file transfer protocol (which replaces FTP); refer to the bold components in the following figure.
Figure 2-16 The Secure Shell Package

Both applications support strong encryption of passwords and data, using widely accepted cipher routines. In addition, they provide authentication to reliably determine the source of any connection attempt. Lastly, SSH provides a guarantee of data integrity, which ensures data cannot be tampered with, even while in transit over the network. These security features, once implemented, are transparent to the users.
IP Network Security
A non-secure network is vulnerable to several types of electronic attacks. IP protocol itself provides limited inherent capability for confidentiality or security. Because of this, networks that depend on IP are subject to relatively simple attacks; these include eavesdropping on an IP transmission, recording or even modifying data. A protocol analyzer, for instance, can record network traffic, and then the packet's data contents are open to view. Another type of IP attack involves a third-party taking over a session and masquerading as one of the original parties involved in the communication.
IP-based security vulnerabilities include:
-
Snooping, or eavesdropping on a connection, which is especially damaging while passwords are being transmitted (see next figure).
Figure 2-17 Example of Snooping
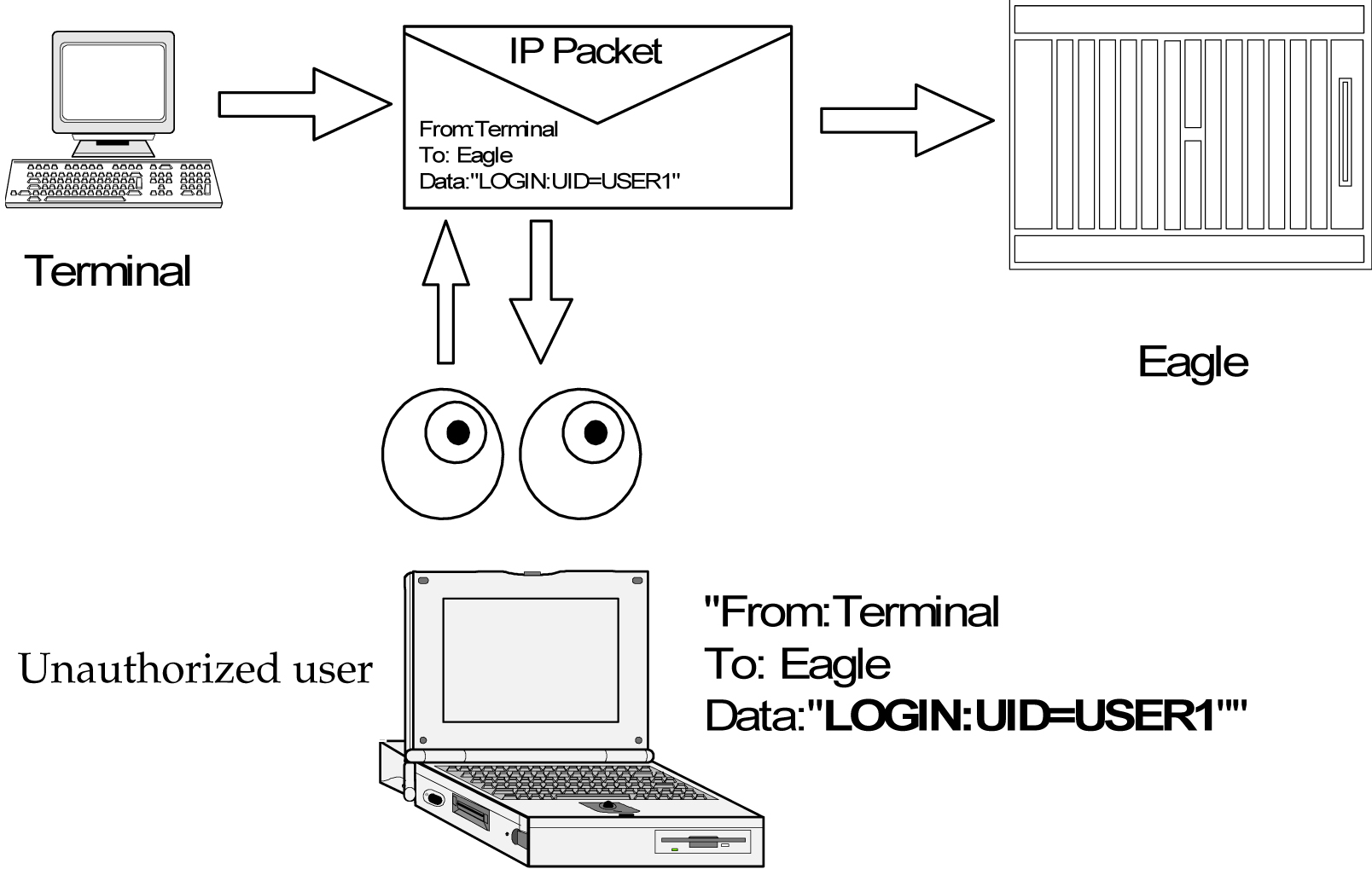
-
IP spoofing, in which an intruder tries to gain access by changing a packet's IP address to make it appear that the packet came from another, trusted host (see next figure).
Figure 2-18 Example of Spoofing
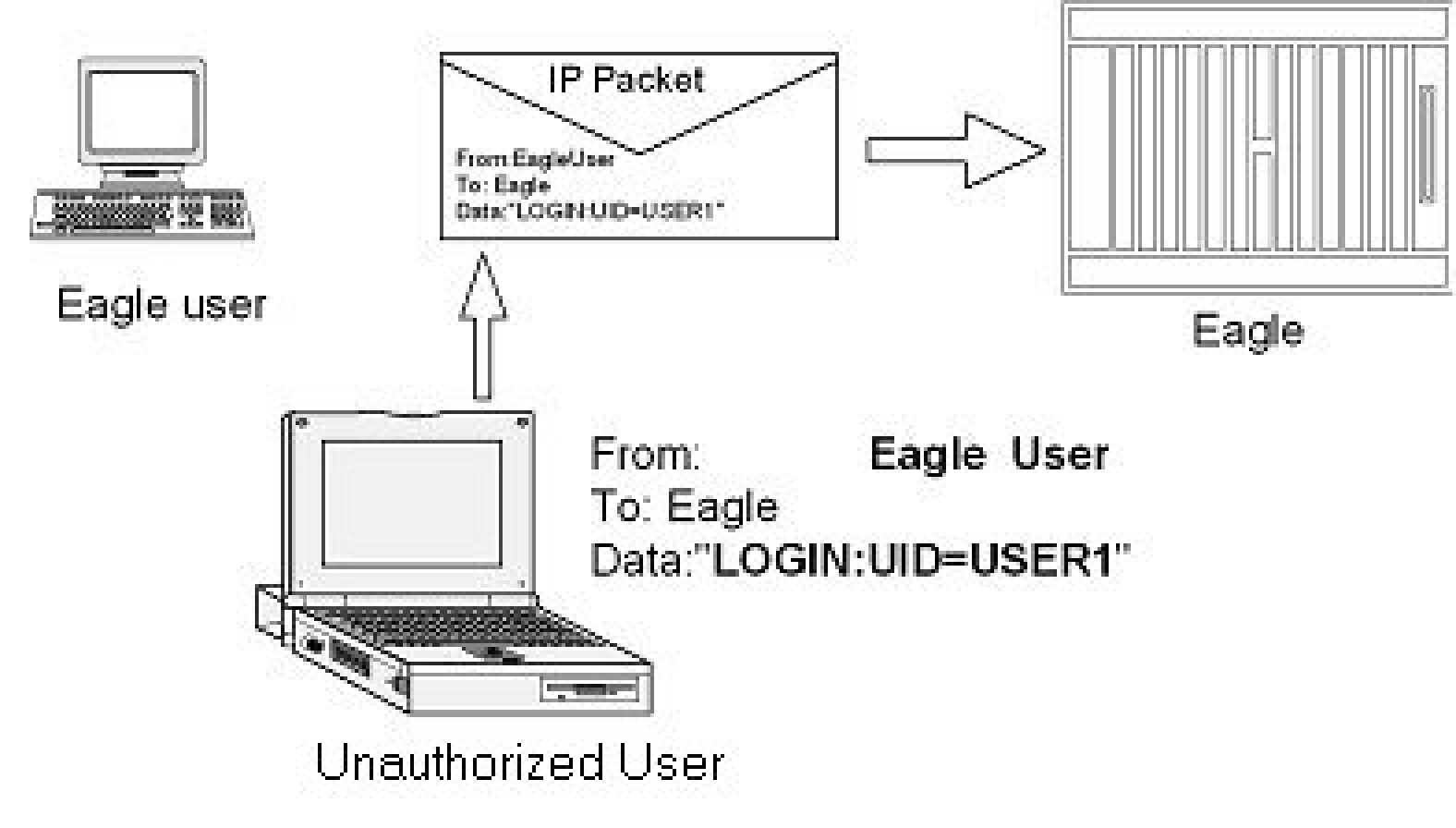
-
IP source routing, where a host can pretend that an IP packet comes from another, trusted host
-
DNS spoofing, where an attacker forges name server records
-
Interception of clear text passwords and other data by intermediate hosts
-
Manipulation of data by people in control of intermediate hosts
-
Attacks based on listening to authentication data and spoofed connection to the server.
Addressing IP Security
The EAGLE Secure Shell package developed for this feature addresses the network vulnerabilities as follows:
Identification
Identification occurs on many levels during a telnet or FTP terminal session. User identification is not only via username, but also through the originating IP address, and also by the Secure Shell client session ID. During the establishment of a secure connection, the host and client go through a process of key exchange and verification, to firmly establish a session identity. Secure Shell is in effect, providing a secure pipe between the client and host for the duration of that connection. All subsequent messages can be verified as originating from that known and established source.
Authentication
Authentication, at the user level, is provided for by the EAGLE login (username and password). This establishes the users identity. Secure Shell provides for authentication at the message level, to ensure incoming messages have originated from a known and verified source, while the session is in effect. This prevents network attacks based on spoofing or modifying the IP packets addressing headers, or originator ID.
Confidentiality
Confidentiality is enforced via message encryption. The Secure Shell tools encrypt each packet of data, before being exchanged in the process of either file transfer, or an interactive session. This encryption prevents snooping-type LAN attacks, where a hostile party intercepts and attempt to read messages in transit.
Data Integrity
Encryption also protects the data contained in the message or the message header from being altered or modified (either maliciously or accidentally) while in transit. Any message that fails an integrity test would be discarded, and the protocol would request the originator to resend the lost message. Data integrity is protected by including a Message Authentication Code (MAC) with each packet. The MAC is computed from a shared secret (key), packet sequence number, and the contents of the packet. The message authentication algorithm and key are negotiated when the connection is established.
Encryption
The secure connection and data encryption is established before the password or other authentication is ever sent, so all data remains protected. The client determines the encryption cipher; one of several is used, such as 3DES, IDEA, or Blowfish. Once the cipher has been determined (generally within the client preferences), the client and server exchange encryption keys.
Strong Authentication
Strong authentication on a per-user basis would entail the use of public/private key pairs, generated at runtime and distributed to each user's client, along with a pass code that was user specific. These keys could not be pre-generated and stored in a table (with user names and passwords), since that would compromise any security advantage they were meant to impart. This would also entail an administrator account on each IPSM or MCPM card, along with a key server agent, to track user keys. Neither the IPSM nor MCPM platform currently supports administrator shell access, or a file system to store keys generated at runtime. This feature does not address Strong Authentication.
Secure Shell Summary
The top drawing in the following figure depicts a standard IP packet traveling over a LAN connection to the server. A packet header contains the destination address, the sender's address, etc. The packet contains data. An IP sniffer could open this packet from the IP stream, examine the contents, change the source or destination address, or change the contents. Security tools prevent the originator's address from being altered, the destination address from being altered, and the data is both unreadable, and protected from modification while in transit.
Figure 2-19 IP Network Security

EAGLE Secure Shell Solution
The EAGLE communicates over IP using two methods: Telnet and File Transfer. Telnet is the remote interactive terminal session. FTP Retrieve and Replace and Measurements Platform use file transfer, for performing bulk data transfer to remote servers.
Secure Shell uses encryption and authentication to protect sensitive data as it passes from one system to another in either scenario. SSH, a terminal connection program, and SFTP, a file transfer program, use an encryption algorithm for protecting all data transmitted over a session, including initial login and password, files and commands sessions.
All data passed through a Secure Shell session is secure: Secure Shell encrypts and authenticates all traffic, incoming and outgoing (including passwords) to effectively eliminate eavesdropping, connection hijacking, and other network-level attacks.
Secure Shell works through three fundamental stages:
-
Integrity - Guarantees the data traveling over a network arrives unaltered.
-
Encryption - Scrambles data to render it unintelligible, except to the intended recipients. A network sniffer could not read the enclosed data, as it cannot be decrypted without the key.
-
Authentication - A secure protocol authenticates the source and destination addresses, as well as encrypts and data contained. Authentication protects against several security problems, e.g., IP spoofing, fakes routes, and DNS spoofing. Nor could false data be substituted, since authentication would reject any but known client's packets.
Applying Secure Shell to EAGLE
This feature applies Secure Shell Version 2.0 to EAGLE OA&M IP Interfaces. Secure Shell defines a protocol for secure remote login and other secure network services over any non-secure network. It provides an encrypted terminal session with authentication of both the server and client. It provides authentication and secure communications over unsecured channels. In other words, Secure Shell never trusts the net; somebody hostile who has taken over the network can only force Secure Shell to disconnect, but cannot decrypt or play back the traffic, or hijack the connection. Secure Shell contains two separate utilities for IP OA&M connections: SSH and SFTP.
-
SSH is the terminal session utility of the Secure Shell package. SSH is a secure replacement for telnet clients.
-
SFTP is the file transfer utility that is part of the Secure Shell package.
SSH and SFTP share the same security features, which include:
-
A variety of data authentication methods.
-
A secure session established between clients and hosts.
-
Support for data encryption.
-
EAGLE IP Features
The EAGLE OA&M IP Security Enhancements feature affects these features:
-
IPUI User Interface (Telnet), introduced in EAGLE Release 29.0/IP7 Secure Gateway Release 7.0
-
FTP Retrieve and Replace, introduced in EAGLE Release 29.0/IP7 Secure Gateway Release 7.0
-
Measurements Platform (EAGLE Release 28.0)
Hardware Requirements
No new hardware is needed to support this feature.
Upgrade Considerations
FTRA (FTP-based Table Retrieve Application) software must be upgraded to support the EAGLE OA&M IP Security Enhancements feature.
Limitations
Security is a process, not a product. EAGLE OA&M IP Security Enhancements will not assist any activity that compromises a host's security in some other way. This feature provides secure access to the EAGLE IPUI terminals, and while the EAGLE is transferring data off-board to remote SFTP servers. Vigilance still is required in protecting username/password combinations, and in controlling system access to EAGLE commands (via the configurable command class feature) to prevent violation of access privilege. This feature does not provide the remote Secure Shell client or server applications (SSH, SFTP).
If this feature is enabled with a temporary key, the key can expire while telnet (SSH) or FTP (SFTP) connections are up and in progress. In this scenario, all existing (legacy) connections remain up, and new connections follow the state of the feature: ON or OFF. Both secure and non-secure connections are possible for the duration of the 'legacy' connection.
2.141 EAGLE OA&M Password Security Enhancements (Release 42.0)
The EAGLE OA&M Password Security Enhancements feature increases the security measures used by the EAGLE 5 ISS Password Management facility.
New Security Measures:
- More restrictive password measures
- Prevention of password re-use
- Prevention of bypassing password re-use rules
- Prevention of a common password pattern
- Access to the EAGLE 5 ISS for a specified period without requiring a password change
- Enhanced notification to the user that passwords have expired or are about to expire
2.141.1 Feature Control Requirements
The EAGLE OA&M IP Security Enhancements feature (Part Number 893-4000-01) must be turned on before passwords can be created or modified from a Telnet terminal (terminal IDs 17 - 40). If the feature is not turned on, then passwords must be created or modified from a Serial terminal (terminal IDs 1 - 16).
2.142 EAGLE - Obsolete OAM Measurements (Release 46.3)
This enhancement removes the support of OAM Measurements and FTA Zone. From EAGLE 46.3 and later, basic OAM measurements are not supported. For measurement collection to happen, either the Integrated Measurements Feature (ctrl-feat) or MCPM Based Collection Feature (measplat=on) should be enabled.
2.143 EAGLE Support for Integrated Sentinel (Release 28.0)
Description
The EAGLE STP and the Sentinel Network Maintenance and Diagnostics tool are both existing Tekelec products. Without the EAGLE Support for Integrated Sentinel feature, the Sentinel requires physical, clamp-on connections to the EAGLE's SS7 signaling links, in order to monitor SS7 traffic. This monitoring method involves costs for cable installation and maintenance for each SS7 link that is to be monitored.
The EAGLE Support for Integrated Sentinel feature eliminates the need for intrusive hardware for each link to be monitored; instead, monitoring is via an Ethernet connection. Message Signaling Units (MSUs), alarms and events can be copied to the ESP over the Ethernet link to provide the same network traffic monitoring.
For more information on the EAGLE Support for Integrated Sentinel feature, refer to the Database Administration Manual - Features.
Hardware Requirements
The EAGLE Support for Integrated Sentinel feature requires GPSM-II cards in place of MCAP cards. Also, the EAGLE Time Synchronization feature (TSC Sync) must be active in conjunction with this feature. In addition, the timing requirements include the use of an external nits clock.
Caution:
The EAGLE Support for Integrated Sentinel feature also requires the STC cards (870-1945-xx) and HMUX (870-1965-01 Rev A). For EAGLE 28.0, DCM cards (870-1945-xx) will serve as STC cards.
Note:
The TSC feature requires GPSM-II; the EAGLE Support for Integrated Sentinel feature requires the TSC feature.
For detailed hardware information, refer to the NSD Hardware Manual.
2.144 EAGLE Query Server on COTS Hardware (Release 1.0)
The EAGLE Query Server is developed and deployed on commercial off the shelf (COTS) hardware platform.
The EAGLE Query Server is compatible with version 6.7 or later of the x86-64 Red Hat Enterprise Linux 6 (RHEL)/ Oracle Linux Operating System.
2.144.1 Hardware
The EAGLE Query Server is installed on a virtual machine environment. The Master and Slave EAGLE QS supports the following minimum hardware requirements:
Table 2-32 Hardware Setup Detail
| Server Type | OS | Release | Arch | Processor | Number of Core | Available Disk Space for Application | Memory Size |
|---|---|---|---|---|---|---|---|
| VM | Oracle Linux/RHEL | 6.7 or later | X86_64 | Intel® Xeon® CPU L5410 @2.33GHz | 16 | 500 GB | 16 GB |
2.145 EAGLE Query Server Support EPAP (Release 1.0)
This feature enhances the current EPAP architecture and performance through an external query server, providing offline query support for EPAP databases. This feature offers standard query interfaces, including SQL and access to MNP data.
The Provisionable EPAP (either Active or Standby PDB) is be able to connect to one "master" EAGLE Query Server. The Provisionable EPAP can be either Standalone PDB or Mixed EPAP.
See Query Server User's Guide for more information.
2.146 EDCM Support (IP7 Release 4.0)
As the IP7 SG applications add new features and their throughput increases, more memory storage and CPU performance is required from the hardware platform. The Enhanced-Performance DCM (EDCM) is a new version of the DCM that includes more main memory and better processing performance. Additional memory is added, doubling the amount of application SRAM. Some memory is replaced with higher performance chips. The following list highlights the changes embodied by the EDCM:
-
The application processor is the AMD K6-IIIe+, which is an embedded version of the AMD K6-III high-performance processor that is used on the DCM 870-1945-xx. This processor consumes less power and produces less heat, leading to increased reliability.
-
The application processor operates with an internal clock frequency of 396MHz rather than the 298MHz of the DCM, thereby increasing application performance and reliability.
The following elements of the EDCM are unchanged from the DCM:
-
The EDCM requires two frame slots, like the DCM.
-
The communication processor is unchanged.
-
The amount of communication processor main memory is unchanged (2MB).
Refer to the NSD Hardware Manual for current hardware information.
2.147 EIR Expansion 50K to 100K (Release 45.0)
The EIR Expansion 50K to 100K feature expands the EIR Block capacity to allow storage of 100,000 IMEI range entries in the Range IMEI Tables. A single EIR range can be present in multiple lists. For example, one range can be in both BL (Blacklist) and WL (Whitelist).
2.148 EIR Expansion of IMEI Block from 50k to 100k (EPAP 15.0)
The IMEI Block capacity for Equipment Identity Register (EIR) is expanded from 50,000 to 100,000 entries. This feature must be trurned on at both the EAGLE and the EPAP. As a permanently-on feature, the feature cannot be turned off after it is turned on. The capacity of the IMEI Range entries in the IMEI Range Tables remains 50,000. A single EIR IMEI Range can be present in multiple lists. For example, an IMEI Range can be in both Black List (BL) and White List (WL).
2.149 EIR S13/S13' Interface Support (Release 45.1)
Equipment Identity Register (EIR) is a database containing records of all mobile stations that are allowed or banned in a network. Generally, the banned mobile stations have been declared lost or stolen. Each mobile station is identified by its International Mobile Equipment Identity (IMEI). When a mobile station is detected by the network, the Mobility Management Entity (MME) or Serving GPRS Support Node (SGSN) requests the IMEI of the mobile station, which is sent to the EIR for authorization.
The EIR S13/S13' Interface Support feature allows EIR to support the S13 and S13' Diameter interfaces for these messages. By supporting the S13/S13' interfaces, Diameter requests can be received by an EAGLE card and processed by EIR, and then a response transmitted back to the requester.
2.149.1 Feature Control Requirements
- The feature Part Number is 893-0424-01.
- A temporary Feature Access Key (FAK) cannot be used to enable the feature.
- The feature cannot be turned off after it is turned on.
- The feature appears as
S13/S13' Int for EIRin thertrv-ctrl-featoutput.
2.149.2 Hardware Requirements
- The E5-SM8G-B card is the only Service Module card which supports the DEIRHC application for the EIR S13/S13' Interface Support feature.
- A maximum of 16 E5-SM8G-B cards running the DEIRHC application can be configured in one EAGLE 5.
- A maximum of 32 Service Module cards running a combination of the SCCPHC, SIPHC, and DEIRHC applications can be configured in one EAGLE 5.
2.150 ELAP Backup Enhancements (ELAP 10.0)
The ELAP Backup Enhancements feature allows users to schedule customized automatic ELAP RTDB backups based on their individual needs. Currently, automatic ELAP RTDB backups are scheduled for 6:00 AM daily in the Active Server. For many users, 6:00 AM is outside their normal maintenance windows or off-peak provisioning hours.
The ELAP Backup Enhancements feature allows users to schedule automatic ELAP RTDB backups using the menu option of the ELAP GUI on the Active ELAP server only. The Automatic RTDB Backup menu option is available after initial installation and does not require feature activation. Only the elapdev user can execute the action in the cron entry.
Figure 2-20 Automatic RTDB Backup Menu Option
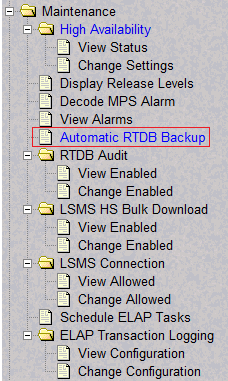
After selecting the Automatic RTDB Backup menu option, the screen shown in Figure 2-21 is displayed to configure the Automatic RTDB Backup schedule. Refer to ELAP Administration and LNP Feature Activation for additional information about the configuration options.
Figure 2-21 Automatic RTDB Backup screen
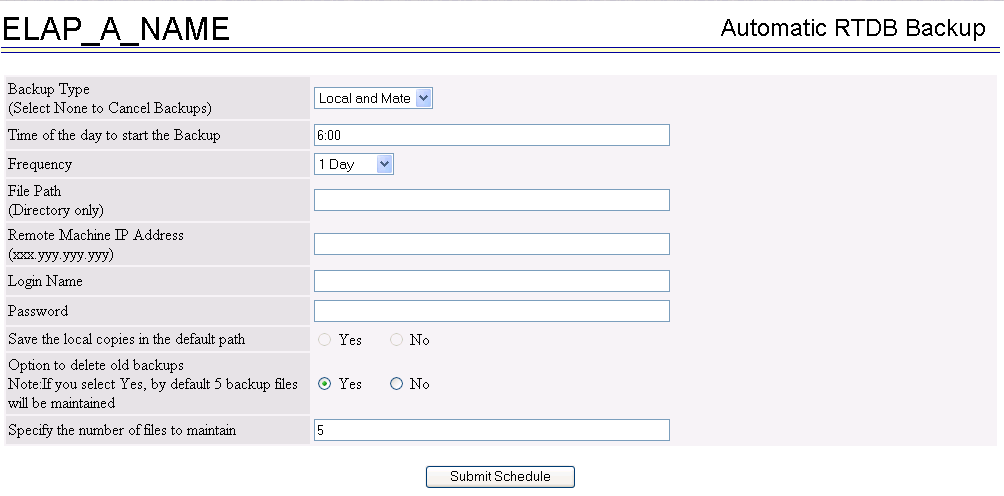
2.151 ELAP Logging Enhancements (ELAP 10.0)
The ELAP Logging Enhancements feature moves the existing logging function from the LSMS to each ELAP server to maintain logging history for LNP provisioning records, while offering more distributed log architecture. Moving the logging function from the LSMS to the ELAP servers also provides more storage capability (approximately 40 GB) which allows for logs to be retained for a longer period.
The ELAP Logging Enhancements feature can be set to on or off. When the ELAP Logging Enhancements feature is on, provisioning of LNP transactions are logged on the ELAP server. The initial status of the feature is off.
The ELAP Logging Enhancements feature is configured from the Change Configuration selection under the menu option of the ELAP GUI for the Active ELAP server only. An example screen displayed after selecting Change Configuration is shown in Figure 2-23. The Remote system fields can be accessed only when Log files export to remote machine is set to Enabled. Refer to ELAP Administration and LNP Feature Activation for additional information about the configuration options.
Figure 2-22 ELAP Transaction Logging Menu Option
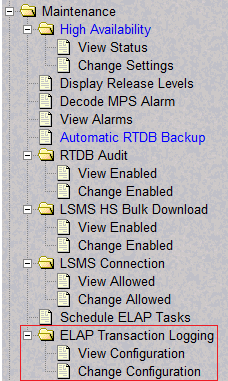
Figure 2-23 Change Configuration (Logging feature = On; Log files export to remote machine = Enabled)
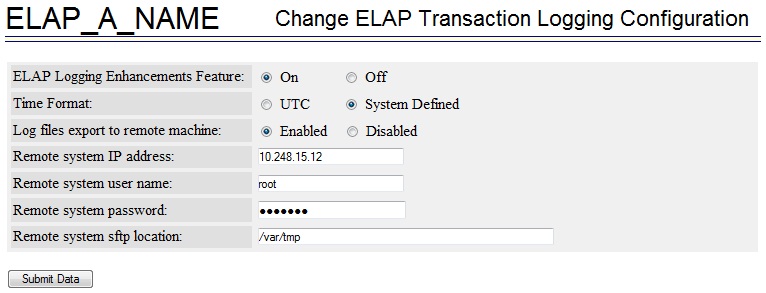
From the menu option, the View Configuration selection displays the current configuration. The configuration determines which properties are displayed.
Figure 2-24 ELAP Logging Enhancements Feature = OFF
Figure 2-25 ELAP Logging Enhancements Feature = ON; Log files export to remote machine = Disabled
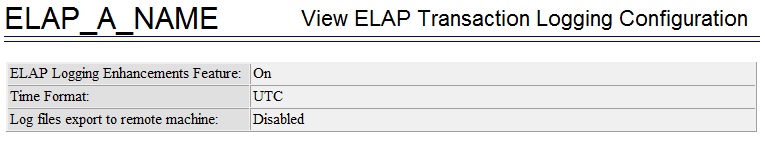
Figure 2-26 ELAP Logging Enhancements Feature = ON; Log files export to remote machine = Enabled
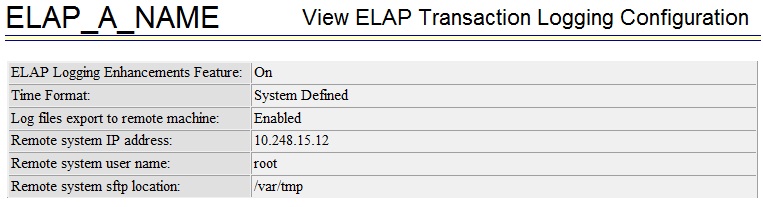
In addition, the Debug menu of ELAP GUI for the Active ELAP server has a new option LNPTRANS under View Logs. Selecting this option allows the user to view the latest LNPTRANS logs.
2.152 ELAP Network Address Translation (NAT) (EAGLE Release 30.0/IP7 Secure Gateway Release 8.0)
Note:
The ELAP NAT feature is only available at the preproduction level.
Description
Customers need to support communication between an ELAP system and a remote browser that may be on the public side of an IP firewall or router that employs Network Address Translation (NAT).
With the ELAP Network Address Translation (NAT) feature, the MPS platform (ELAP/EPAP) supports communications on networks where Network Address Translation (NAT) is employed. This means that the two MPS systems (A and B) can intercommunicate using IP addresses on a private network, yet also support IP addressing and communication with a remote browser that may be on the public or "other" side of a firewall or router employing NAT that is performing the IP address translation.
Network Address Translation (NAT) on MPS
The MPS supports two types of network address translation (NAT), Port Forwarding and Static Address Mapping. In both cases, the MPS will have private IP addresses that are not available outside of the firewall-protected internal network. The firewall will translate particular addresses and port numbers to the internal addresses for the MPS.
The addresses in the following figure are examples. Addresses are not restricted to particular classes/ranges.
Figure 2-27 Network Address Translation on MPS

Port Forwarding
Port forwarding allows a single external address to be used for multiple internal systems. The port forwarding firewall maintains a list of services (basically port numbers) and corresponding internal addresses.
Although the MPS has two individual internal IP addresses, external clients are only allowed to reach the internal network using one external address. The MPS servers must use different port numbers for each externally available service in order to distinguish MPS A from MPS B to external clients.
Caution:
Do not change the default values for these ports.
Static Address Mapping
Static address mapping makes systems that are behind the firewall appear to have public addresses on the external network. A one-to-one mapping exists between internal and external addresses.
An external address must be assigned to the NAT firewall for each MPS side. For the Web UI to be fully functional, the external addresses must be entered into the MPS database.
Hardware Requirements
No new or additional hardware is required to support this feature.
Enhancements to the ELAP Text-Based Interface
This section describes the enhancements to the text-based ELAP Configuration interface made to accommodate this feature. For more information, see the ELAP Administration Manual.
ELAP Configuration Menu
Entering '1' from the ELAP Configuration Menu provides a configuration report of the ELAP. The following figure illustrates an example configuration that includes NAT Address information (see arrows):
Figure 2-28 Display Configuration

Configure Network Interfaces Menu
This menu allows for the configuration of all of the possible network interfaces for the ELAP. When this menu item is selected, the menu shown in the following figure is displayed (see arrows).
Figure 2-29 Configure Network Interfaces Menu

Configure Forwarded Ports
Entering a choice of '5' from the Configure Network Interfaces Menu provides the functionality to configure ELAP ports for the Web UI and PDBI interfaces. When this menu item is selected, the menu shown in the following figure is displayed.
Figure 2-30 Configure Forwarded Ports Menu

Each numbered item on the Configure Forwarded Ports menu allows the user to specify a port number used for remote access to the MPS.
Configure Static NAT Addresses
Entering a choice of '6' from the Configure Network Interfaces Menu provides the functionality to configure the static NAT addresses of the ELAP. When this menu item is selected, the menu shown in the following figure is displayed.
Figure 2-31 Configure Static NAT Addresses Menu

Each numbered item of the Configure Static NAT Addresses menu allows the user to specify an IP Address used outside of the firewall for remote access to the MPS. The values entered here must match the configuration of the firewall.
2.153 ELAP Support for more than Nine E5-SM4G Cards for the LNP Feature (ELAP 9.0)
ELAP has been updated to support the connection to and loading of more than 9 and up to 18 E5-SM4G Service Module cards on the EAGLE 5 ISS with the LNP feature.
- With the EAGLE 5 ISS E5-SM4G Throughput Capacity feature quantity of 5000 TPS enabled, the system TPS for 17+1 E5-SM4G cards in the EAGLE 5 ISS is 85,000 TPS.
- With the EAGLE 5 ISS E5-SM4G Throughput Capacity feature quantity of 6800 TPS enabled, the system TPS for 17+1 E5-SM4G cards in the EAGLE 5 ISS is 115,600 TPS.
Refer to ELAP Administration Manual - 9.0 of the EAGLE 5 ISS Release 42.0 documentation set for more information.
2.154 ENUM Mobile Number Portability and Tier One Address Resolution (Release 46.2)
The ENUM Mobile Number Portability and Tier One Address Resolution (ENUM) feature of the Oracle Communications EAGLE enhances the ability of EAGLE to access the Number Portability database (RxDB) using ENUM protocol. Using the ENUM interface supported on UDP, EAGLE is able to process a destination number lookup in an IP-based addressing scheme in the Number Portability database and provide a routing solution to the originating carrier.
2.155 Embedded OAP (Release 24.0)
Description
The OAP is a stand alone processor that acts as an interface between the EAGLE and operation support system (OSS) devices using standard interfaces and converting the communications to the EAGLE proprietary serial interface. The OAP can be used as an interface between the EAGLE and the SEAC (Signaling Engineering and Administration Center), for the SEAS feature, and as an interface between the EAGLE and the SMS (Service Management System), for the LNP feature. The OAP is installed in the OAP frame of the EAGLE.
When used as an interface between the SEAC and the EAGLE, the OAP processes SEAS commands into EAGLE commands and EAGLE commands into SEAS commands.
When used as an interface between the SMS and the EAGLE, the OAP receives LNP data and commands from the SMS and converts the SMS commands into EAGLE commands and the LNP data is loaded onto the EAGLE.
The Embedded OAP (EOAP) replaces the existing Texas Micro OAP with a modular unit with field replaceable components which meet or exceed all of the OAP's current capabilities. In addition, the EOAP provides for the future enhancement of the OAP's responsibilities.
There are two EOAPs in the system, EOAP-A and EOAP-B. The EOAP is in the EOAP shelf which is located in the OAP frame. Each EOAP in the dual configuration consists of a processor card, an interface card, a power supply card, and a center bay containing a removable hard drive and a CD-ROM drive for each EOAP. Figure Embedded OAP illustrates the layout of the system. For a functional block diagram, see figure Functional Block Diagram of the EOAP.
Figure 2-32 Embedded OAP
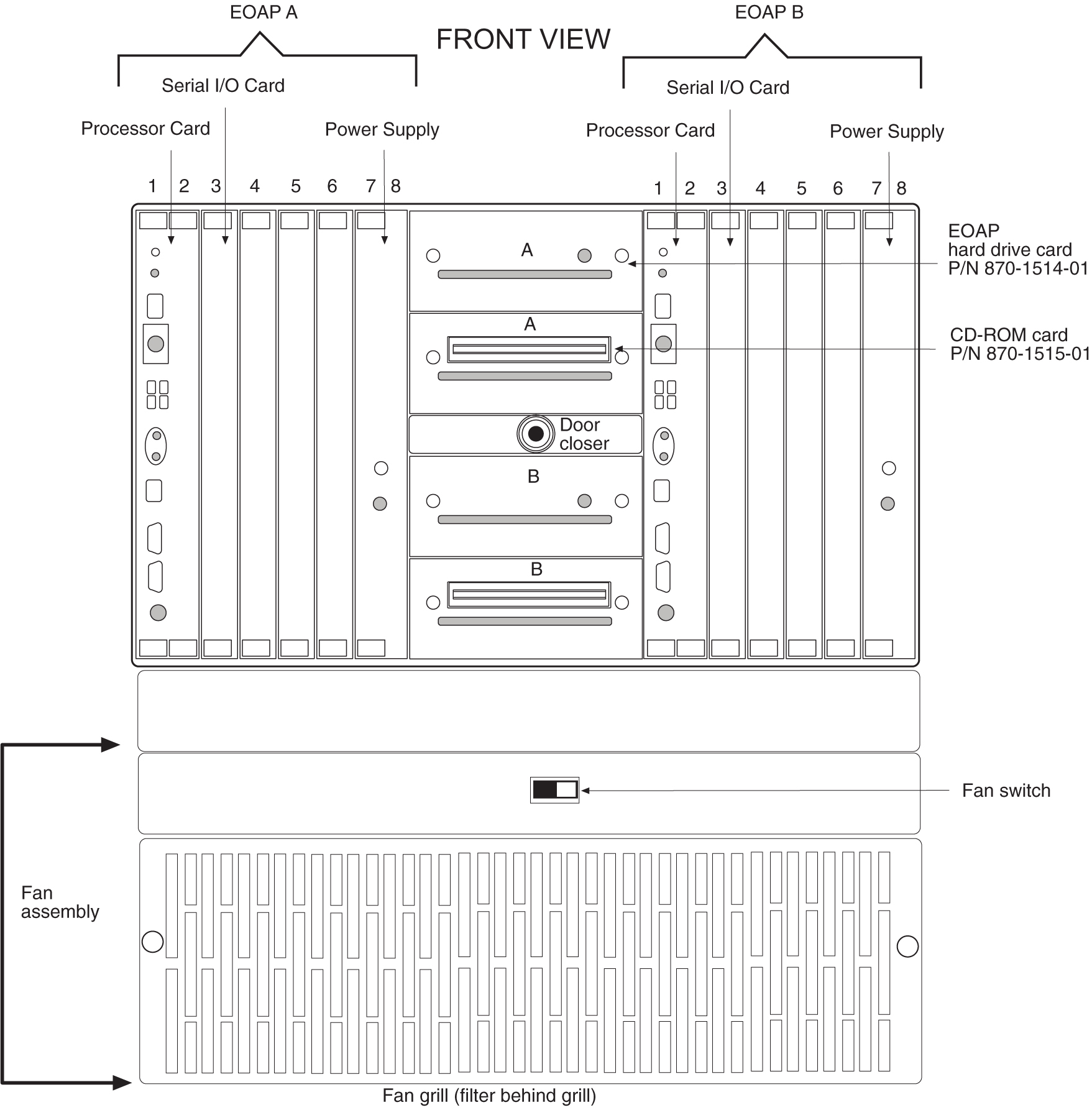
The following figure shows a functional block diagram of the EOAP.
Figure 2-33 Functional Block Diagram of the EOAP
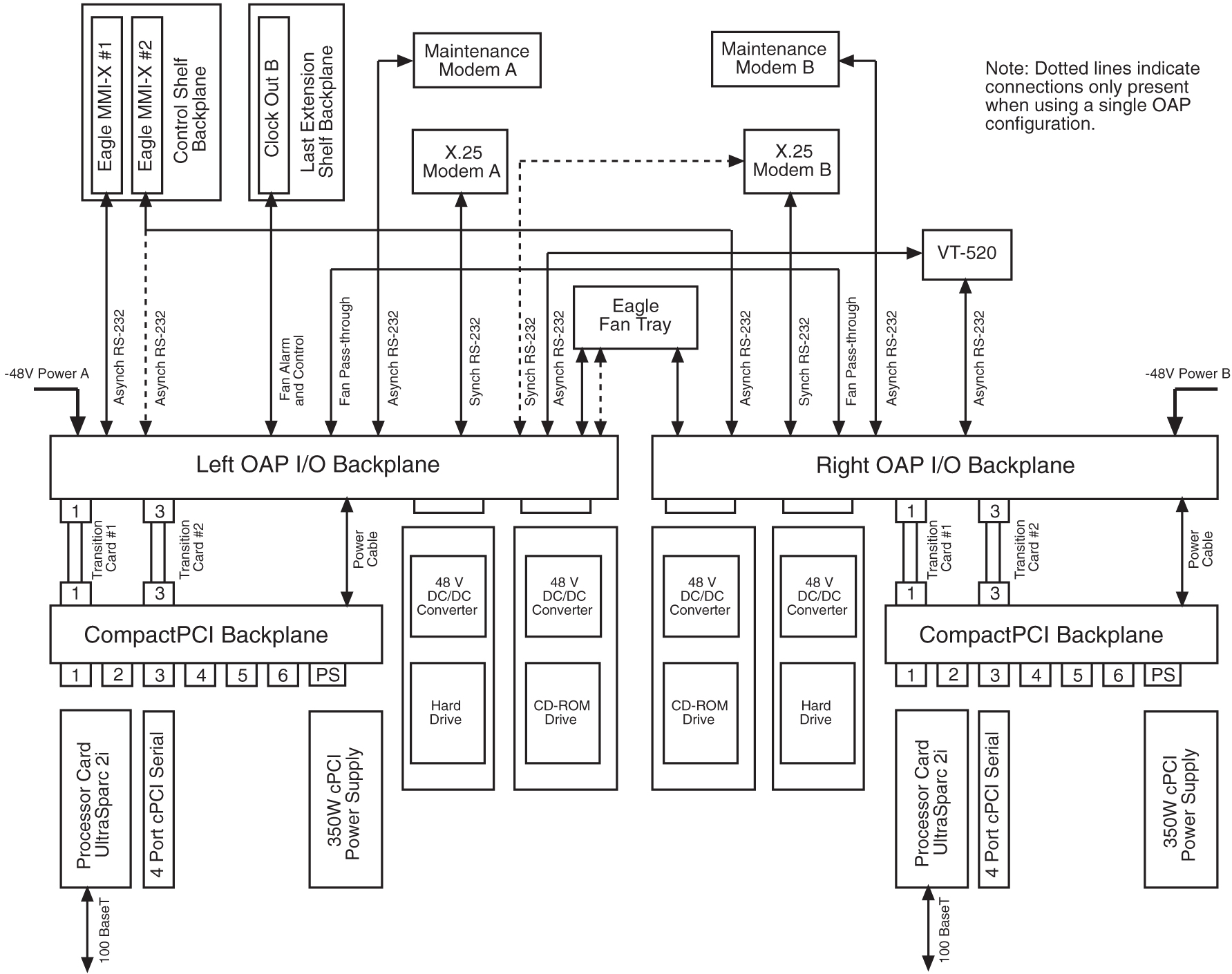
The following table shows the hardware components of the EOAP.
Table 2-33 Hardware Requirements of the EOAP
| Component | Part Number |
|---|---|
|
Processor Card with the UltraSparc 2I processor and 64 MB of RAM (expandable to 1 GB) |
800-0271-01 |
|
4-Port Serial I/O Card |
800-0272-01 |
|
350W 48V DC/DC Power Supply |
800-0274-01 800-0267-01 |
|
CompactPCI Backplane |
850-0489-01 |
|
Tekelec APC SCSI Hard Drive - 4 GB minimum |
870-1514-01 |
|
Tekelec APC 32X SCSI CD-ROM Drive |
870-1515-01 |
|
Tekelec Right OAP I/O Backplane |
850-0487-01 |
|
Tekelec Left OAP I/O Backplane |
850-0488-01 |
|
Tekelec Transition Card - Processor Card to the OAP I/O Backplane |
850-0496-01 |
|
Tekelec Transition Card - Serial I/O Card to OAP I/O Backplane |
850-1514-01 |
EOAP Processor Card - P/N 800-0271-01
Slots 1 and 2 of the EOAP contains the processor card using the UltraSparc 2i processor. This card provides two serial ports, A and B, for connecting the EOAP to the EAGLE. Serial port A is accessible from the EOAP backplane and from an RS232C mini-DIN8 serial interface on the front panel. Serial port B is accessible from the EOAP backplane. Both serial ports provide RS232 asynchronous modem support.
Caution:
The front panel interface on serial port A is provided for monitor output. However, no provision has been made to safeguard the processor card against data entry from the front panel interface. Data input through the front panel serial port is allowable so long as serial port A is not accessed from the rear panel while this occurs. Unpredictable events will occur on the processor card if data is simultaneously input on serial port A through the front panel and back panel connectors.
An RJ-45 Ethernet port on the front of the card provides a negotiated 10/100BaseT network access for LNP support using the LSMS.
The processor card also contains a seven-segment LED, a system status LED, a user configurable alarm LED, and abort and reset capabilities through both manual and software intervention.
The seven segment LED displays the numeric values 0 through 9 and the alphabetic values A through F and H. If the seven-segment LED is displaying a number zero, the processor has been halted. If the seven-segment LED is displaying a number one, the processor is operating normally. If the seven-segment LED is blank, the processor is being reinitialized. The other values for the seven-segment LED have not been defined in Release 24.0.
The processor card is a field replaceable unit. If the processor card is replaced, new license keys must be installed on the hard drive through the EAGLE initiated OAP user interface. This is due to the change in the Host ID that will occur with the new processor card.
The processor card is equipped with 64 MB of RAM, and is expandable to 1 GB of RAM.
4-Port Serial I/O Card - P/N 800-0272-01
Slot 3 of the EOAP contains the 4-port serial I/O card, which supplies four RS-232C serial ports. These ports are accessible from the backplane. Two of these ports are used for interfacing the EOAP with SEAS. The other two ports are used to connect the EOAP to a VT-520 console or to an RS232C asynchronous modem. The 4-port serial I/O card is a field replaceable unit.
350W Power Supply - P/Ns 800-0274-01 and 800-0267-01
The power supply for the EOAP is a field replaceable unit that occupies slots 7 and 8 of the EOAP. One of two power supplies can be used on the EOAP. P/N 800-0274-01 is the preferred power supply to use with the EOAP. This power supply is a DC-DC switcher-style power supply. Power supply P/N 800-0276-01 is an alternate power supply that can be used on the EOAP and is based on Astec DC-DC converters.
Two LEDs are located on the front of the power supply. The POWER GOOD LED (a green LED) should be on when input voltage falls within the allowable range of -48 to -72 VDC. The FAULT LED (a red LED) indicates than an internal fault has occurred. These faults include over-voltage, input DC fail warning, loss of output power, and temperature exceeding set limits.
The following table shows the specifications of both power supplies.
Table 2-34 Power Supply Specifications
| Specification | Power Supply P/N 800-0274-01 | Power Supply P/N 800-0267-01 |
|---|---|---|
|
Input Range |
36VDC - 72VDC |
40VDC - 72VDC |
|
Efficiency |
75% Typical, derated 2.5% per degree above 40 degrees C |
75% typical, derated 10W per degree over 50 degrees C |
|
Ripple/Noise |
greater of 1% peak-peak or 50mV |
50mV max. for all outputs, peak-peak, dc to 20MHz with coaxial probe and 0.1uF/22uF capacitors at the connector |
|
Connector |
Positronics P/N PCI38M 400A1 |
Positronics P/N PCI38M 400A1 |
|
Outputs |
+3.3 V - 40A maximum * +5.0 V - 50A maximum * +12.0V - 12A maximum -12.0 V - 2A maximum * - Combined 3.3V and 5.0V current not to exceed 50A |
+3.3 V - 25A maximum +5.0 V - 50A maximum +12.0V - 9A maximum -12.0 V - 2A maximum |
|
Inrush Current |
60 A maximum @ 72V 40 A maximum @ 48V 20 A maximum @ 36V |
15 A maximum |
|
Internal Fuse |
15A replaceable fuse |
15 A replaceable fuse |
Hard Drive and CD-ROM Drive
The center section of the dual EOAP system contains four individual drive bays. The first and third drive bays contain a SCSI hard drive (P/N 870-1514-01) with a minimum capacity of 4 GB, and is a field replaceable unit. The first drive bay is hardwired to EOAP-A and the third drive bay is hardwired to EOAP-B. If the hard drive is replaced, all site specific information must be reloaded on the EOAP from the EAGLE.
The second and fourth drive bays contain a 32X SCSI CD-ROM drive (P/N 870-1515-01). The second drive bay is hardwired to EOAP-A and the fourth drive bay is hardwired to EOAP-B. The CD-ROM drive is a field replaceable unit.
EOAP Connectors
The cards in slots 1 through 8 for each EOAP are connected to the CPCI backplane (P/N 850-0489-01) as shown in figure Functional Block Diagram of the EOAP. The interface from the EOAP to the EAGLE is provided through another set of backplanes, the left and right backplanes (P/Ns 850-0488-01 for the left backplane and 850-0487-01 for the right backplane). The layout of the left and right backplanes is shown in figure EOAP Backplane and Connectors. The hard disk and CD-ROM drive for each EOAP connect directly to the left and right backplanes. The CPCI backplane connects to the right and left backplanes with the APC Transition Cards, one for the processor card - P/N 850-0496-01, and one for the serial I/O card - P/N 850-1514-01. The transition cards only provides an electrical connection between the CPCI backplanes and the left and right backplanes for the EOAP assembly. The transition cards do not perform any processing of the signals from either backplane.
Figure 2-34 EOAP Backplane and Connectors
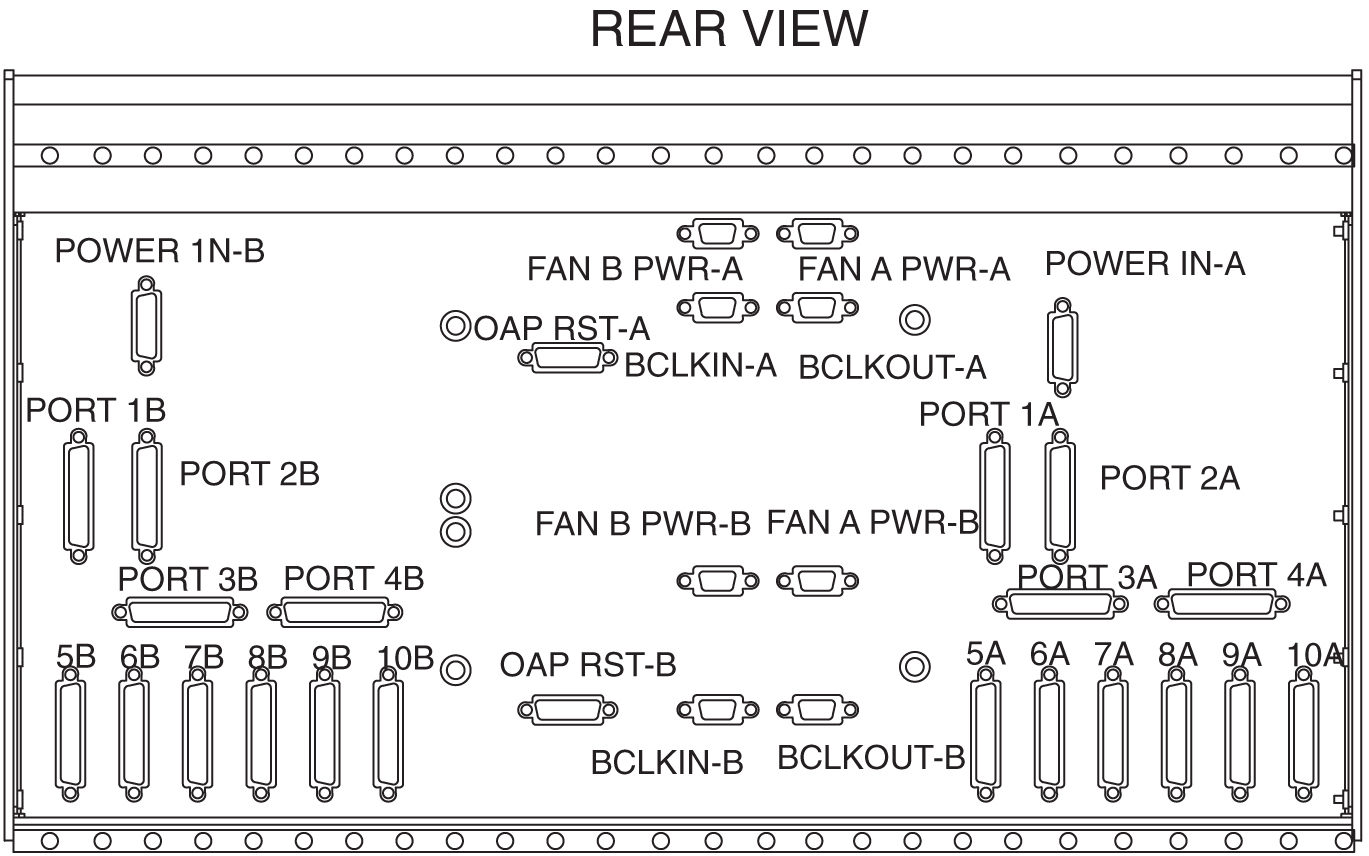
External Interface Descriptions
The next two tables show the connectors used on the backplanes of the EOAP and on the front of the processor card.
Table 2-35 External Interfaces - OAP A
| Connector (Silkscreen Label) | Signal | DESCRIPTION (Software name in parenthesis) | TYPE | Usage/Destination |
|---|---|---|---|---|
|
POWER IN-A |
System Power |
-48VDC, CHASSIS GND, -48VDCRTN |
N/A |
From Fuse Panel |
|
FAN A-PWR-A |
Fan A Power |
FAN POWER, ALARM, CONTROL |
N/A |
To Fan Assembly |
|
FAN B-PWR-A |
Fan B Power |
Fan Power, Alarm, Control |
N/A |
To Fan Assembly |
|
OAP RST-A |
Oap Reset |
OAP Hard Reset Lines |
N/A |
Currently Unused |
|
BCLKIN-A |
B Clock Input |
Provides Fan Alarm/Control From EAGLE to Fan A |
N/A |
From Last Extension Shelf Backplane |
|
BCLKOUT-A |
B Clock Output |
Provides Fan Alarm/Control to Fan B |
N/A |
To System B BCLKIN |
|
1A |
RS-232 |
Processor Card - Slots 1 and 2 (/dev/term/a) |
Asynchronous |
EAGLE Terminal Port |
|
2A |
RS-232 |
Processor Card - Slots 1 and 2 (/dev/term/b) |
Asynchronous |
EAGLE Terminal Port |
|
3A |
RS-232 |
Serial I/O Card - Slot 3 (/dev/term/0) |
Asynchronous |
VT-520 Terminal |
|
4A |
RS-232 |
Serial I/O Card - Slot 3 (/dev/term/1) |
Asynchronous |
Maintenance Modem |
|
5A |
RS-232 |
Serial I/O Card - Slot 3 (hih0) |
Synchronous |
X.25 Port |
|
6A |
RS-232 |
Serial I/O Card - Slot 3 (hih1) |
Synchronous |
X.25 Port |
|
7A |
RS-232 |
Reserved for future expansion through Slot 4 |
Asynchronous or Synchronous |
Currently Unused |
|
8A |
RS-232 |
Reserved for future expansion through Slot 4 |
Asynchronous or Synchronous |
Currently Unused |
|
9A |
RS-232 |
Reserved for future expansion through Slot 4 |
Asynchronous or Synchronous |
Currently Unused |
|
10A |
RS-232 |
Reserved for future expansion through Slot 4 |
Asynchronous or Synchronous |
Currently Unused |
|
Front Ethernet Port (RJ-45) |
100BsT |
LAN Connection |
10/100BaseT |
Connection to LSMS via LAN |
|
Front Serial A/B Port |
RS-232 |
Not used, CANNOT be used while rear serial ports are in use. |
Asynchronous |
Not to be used in standard configuration |
|
RESET Switch |
POR |
Mechanical reset key, when enabled and toggled, generates a push-button Power On Reset (POR) to the UltraSPARC-2I. Same affect as a Power On Reset from the power supply, except set status bit B_POR in the Reset_Control Register. |
Mechanical Switch |
To be used when a hard reset is required. System must be halted prior to execution to ensure disk integrity. |
|
ABORT Switch |
XIR |
Mechanical abort key, when enabled and toggled, generates XIR (externally initiated reset) without resetting the whole system. Sets B_XIR in Reset_Control register. |
Mechanical Switch |
To be used when abort is required. System must be halted prior to execution to ensure disk integrity. |
|
Front SCSI Port |
SCSI-2 |
Auto-terminating narrow SCSI-2 |
SCSI-2 |
Reserved for use by manufacturing |
|
Front Keyboard Port |
Sun Keyboard and Mouse |
8-pin mini-DIN |
Asynchronous |
Supports Sun Keyboard and Mouse (Unused) |
Table 2-36 External Interfaces - OAP B
| Connector (Silkscreen Label) | Signal | DESCRIPTION (Software name in parenthesis) | TYPE | Usage/Destination |
|---|---|---|---|---|
|
POWER IN-B |
System Power |
-48VDC, CHASSIS GND, -48VDCRTN |
N/A |
From Fuse Panel |
|
FAN A-PWR-B |
Fan A Power |
FAN POWER, ALARM, CONTROL |
N/A |
To Fan Assembly |
|
FAN B-PWR-B |
Fan B Power |
Fan Power, Alarm, Control |
N/A |
To Fan Assembly |
|
OAP RST-B |
Oap Reset |
OAP Hard Reset Lines |
N/A |
Currently Unused |
|
BCLKIN-B |
B Clock Input |
Provides Fan Alarm/Control From EAGLE to Fan A |
N/A |
From Last Extension Shelf Backplane |
|
BCLKOUT-B |
B Clock Output |
Provided for future expansion of additional Fan Assemblies |
N/A |
Currently Unused |
|
1B |
RS-232 |
Force Processor - Slot 1 (/dev/term/a) |
Asynchronous |
EAGLE Terminal Port |
|
2B |
RS-232 |
Force Processor - Slot 1 (/dev/term/b) |
Asynchronous |
EAGLE Terminal Port |
|
3B |
RS-232 |
Aurora Serial I/O - Slot 3 (/dev/term/0) |
Asynchronous |
VT-520 Terminal |
|
4B |
RS-232 |
Aurora Serial I/O - Slot 3 (/dev/term/1) |
Asynchronous |
Maintenance Modem |
|
5B |
RS-232 |
Aurora Serial I/O - Slot 3 (hih0) |
Synchronous |
X.25 Port |
|
6B |
RS-232 |
Aurora Serial I/O - Slot 3 (hih1) |
Synchronous |
X.25 Port |
|
7B |
RS-232 |
Reserved for future expansion through Slot 4 |
Asynchronous or Synchronous |
Currently Unused |
|
8B |
RS-232 |
Reserved for future expansion through Slot 4 |
Asynchronous or Synchronous |
Currently Unused |
|
9B |
RS-232 |
Reserved for future expansion through Slot 4 |
Asynchronous or Synchronous |
Currently Unused |
|
10B |
RS-232 |
Reserved for future expansion through Slot 4 |
Asynchronous or Synchronous |
Currently Unused |
|
Front Ethernet Port (RJ-45) |
100BsT |
LAN Connection |
10/100BaseT |
Connection to LSMS via LAN |
|
Front Serial A/B Port |
RS-232 |
Not used, CANNOT be used while rear serial ports are in use. |
Asynchronous |
Not to be used in standard configuration |
|
RESET Switch |
POR |
Mechanical reset key, when enabled and toggled, generates a push-button Power On Reset (POR) to the UltraSPARC-2I. Same affect as a Power On Reset from the power supply, except set status bit B_POR in the Reset_Control Register. |
Mechanical switch. |
To be used when a hard reset is required. System must be halted prior to execution to ensure disk integrity. |
|
ABORT Switch |
XIR |
Mechanical abort key, when enabled and toggled, generates XIR (externally initiated reset) without resetting the whole system. Sets B_XIR in Reset_Control register. |
Mechanical Switch |
To be used when abort is required. System must be halted prior to execution to ensure disk integrity. |
|
Front SCSI Port |
SCSI-2 |
Auto-terminating narrow SCSI-2 |
SCSI-2 |
Reserved for use by manufacturing |
|
Front Keyboard Port |
Sun Keyboard and Mouse |
8-pin mini-DIN |
Asynchronous |
Supports Sun Keyboard and Mouse(Unused) |
Asynchronous Maintenance Modem
Although not provided with the EOAP, a Hayes compatible modem can be connected to the EOAP to provide connectivity for remote monitoring and maintenance. This allows access to the EOAP as required by Tekelec Technical Services. The modem is connected to the EOAP through the 4-Port Serial I/O Card through connectors 4A or 4B on the EOAP backplanes. The modem must be configured as shown in table Modem Configuration. See tables External Interfaces - OAP A, External Interfaces - OAP B, and figure EOAP Backplane and Connectors for the designation and location on the backplanes of each connector.
Table 2-37 Modem Configuration
| Modem Parameter | Value |
|---|---|
|
Baud Rate |
9600 bits per second |
|
Data Bits |
7 |
|
Parity |
Even |
|
Stop Bits |
1 |
EOAP User Console
The user console for the EOAP is provided by a Digital Equipment Corporation VT520 terminal. The VT520 is connected to the EOAP using an RS232C terminal cable attached to connectors 3A or 3B on the EOAP backplanes. See tables External Interfaces - OAP A, External Interfaces - OAP B, and figure EOAP Backplane and Connectors for the designation and location on the backplanes of connectors 3A or 3B. This terminal allows for monitoring and direct interfacing capabilities to the EOAP and must be set up for VT100 emulation.
Fans
To help keep the EOAP cool, the EAGLE fan assembly is mounted underneath the EOAP. The fan assembly consists of eight fans, two LEDs, and a three-way switch. The fan assembly is powered from the A and B power sources on the EOAP backplanes (connectors FAN A-PWR-A, FAN A-PWR-B, FAN B-PWR-A, and FAN B-PWR-B2, see tables External Interfaces - OAP A, External Interfaces - OAP B, and figure EOAP Backplane and Connectors.
The three-way switch allows the user to specify how the fans are controlled. The normal position of the switch allows the system software to control when the fans are turned on and off. The ON and OFF positions of the switch turns the fans on and off and overrides any control by the system software.
One of the LEDs shows whether the fans are on (LED is green) or off (LED is off). The second LED (see table Fan Alarm Status) shows the alarm status of the fans.
Table 2-38 Fan Alarm Status
| LED | Alarm Status |
|---|---|
|
Green |
No Fan Alarm |
|
Red |
Fan Alarm |
|
Off |
No Power |
UAMs
If there is a failure of any of the fans, or if the three-way switch is in the OFF position, the alarm status LED is red, and a minor alarm (unsolicited alarm message 302) is generated at the EAGLE.
RLGHNCXA03W 99-01-07 00:57:31 EST Rel 24.0.0
* 0055.0302 * SYSTEM Cooling Fan Failure
When the fan failure is cleared, or when the three-way switch is placed in either the ON or normal position, the fan alarm is cleared, the alarm status LED is green, and unsolicited alarm message 303 is generated at the EAGLE.
RLGHNCXA03W 99-01-07 00:57:31 EST Rel 24.0.0
0056.0303 SYSTEM Cooling Fans Normal
The fan alarm and control input and output are obtained from the Clock Out B connector on the last EAGLE extension shelf and connected to the BCLKIN-A, BCLKIN-B, BCLKOUT-A, and BCLKOUT-B connectors on the EOAP backplanes. See tables External Interfaces - OAP A, External Interfaces - OAP B, and figure EOAP Backplane and Connectors for the designation and location on the backplanes of each connector.
Third Party Software
The following table shows the third party software and the versions of the software required by the EOAP.
Table 2-39 Third Party Software for the EOAP
| Product | Vendor | Embedded OAP Version |
|---|---|---|
|
DSET APLI |
DSET |
4.1.3f compiled for Solaris version 2.5.1 |
|
DSET DSGRuntime |
DSET |
4.1.3f compiled for Solaris version 2.5.1 |
|
Solstice OSI |
Sun |
8.1.1 |
|
Solaris |
Sun |
2.5.1 |
|
SunLink HSI/S |
Sun |
2.0 |
|
Solstice X.25 |
Sun |
9.1 |
|
NetPilot UAL Software |
Bellcore |
8.2 |
|
Performance Technologies Driver |
Performance Technologies |
810P027930 |
EOAP to EAGLE Interface
The EOAP is connected to the EAGLE through the EOAP backplane. The two serial ports on the processor card are used for this connection. The cables are connected to any two of the terminal ports (MMI 0-MMI 15) on the EAGLE control shelf backplane.
The EOAP connected to the lower numbered terminal port is considered by the EAGLE to be OAP A, and the EOAP connected to the higher numbered terminal port is considered by the EAGLE to be OAP B.
The terminal port being used by the EOAP must be configured in the EAGLE with the type=oap parameter of the chg-trm command. When the type=oap parameter is specified with the chg-trm command, none of the communication attribute parameters, baud (the baud rate of the terminal port), prty (the parity of the terminal port), sb (the number of stop bits for the terminal port’s RS-232 connection), and fc (the type of flow control for the terminal port’s RS-232 connection) can be specified. These parameters are defaulted to the values shown in the following table.
Table 2-40 EAGLE Terminal Port Configuration for the EOAP
| Terminal Port Parameter | Value |
|---|---|
|
Baud Rate ( |
19200 bits per second |
|
Parity ( |
even |
|
Stop Bits ( |
1 |
|
Flow Control ( |
hw - hardware flow control |
To allow the user to reset the EOAP from the EAGLE terminal, an alarm/reset cable connects to the EOAP at the OAP RST-A and OAP RST-B connectors and on the EAGLE at the OAPALM connector on the control shelf backplane. The EAGLE init-oap command is used to initiate the reset of the EOAP. The init-oap command uses the parameters oap and force.
-
oap– Specifies which OAP is being initialized, as considered by the EAGLE.-
a– OAP A -
b– OAP B -
both– Both OAPs
-
-
force– Forces the reset of the specified OAP if that OAP is operational (its state is either IS-NR, in-service normal, or IS-ANR, in-service abnormal) and it is the only operational OAP. The values for this parameter are eitheryesorno. If the specified OAP is not operational, theforce=yesparameter is not required. The default value for theforceparameter isno.
If the specified OAP is the only operational OAP and the force=yes parameter is not specified for the init-oap command, the init-oap command is rejected with this message.
E2813 Cmd Rej: FORCE=YES must be specified to initialize the last OAP
The init-oap command requires that the SEAS feature is on, or the init-oap command is rejected with this message.
E2812 Cmd Rej: SEAS feature or LNP feature is not configured
EOAP to SEAS Interface
The EOAP is connected to the SEAC using these connectors on the EOAP backplanes: 5A, 5B, 6A, and 6B. From one of these ports, an RS232C cable is connected to a 9600 bps synchronous modem, which in turn is connected to the SEAS system. If only a single EOAP is being used, both ports on that EOAP are connected to two separate modems. If both EOAPs are being used, only one port on each EOAP is connected to a modem that is connected to the SEAS system. See tables External Interfaces - OAP A, External Interfaces - OAP B, and figure EOAP Backplane and Connectors for the designation and location of each connector on the backplanes.
EOAP to LSMS Interface
The EOAP is connected to the LSMS through the Ethernet port (an RJ-45 connection) located on the front of the Processor Card using a 10/100BaseT cable.
The EOAP handles eight messages from the LSMS at a time (process and respond to the LSMS), although multiple messages may be sent to the EOAP. No more than eight messages should be sent from the LSMS to the EOAP without a response being returned by the EOAP. If more than one message is sent to the EOAP without the LSMS waiting for a response, the LSMS must manage retries and the sequencing of messages.
The EOAP must be configured locally with the LSMS OSI-Address information necessary for association establishment. The EOAP will initiate association connections with the LSMS.
2.156 End Office Support (IP7 Release 5.0)
Description
Customers see the IP7 Secure Gateway product as a means by which they can take advantage of next generation network technology by migrating existing signaling end points from the PSTN to the IP network. The fact that the SG is a signaling transfer point and has its own point code, however, presents a significant network management issue for them. Some customers do not want to obtain a new point code and reconfigure their network in order to introduce the SG and an IP end office node. This feature provides such customers the means to perform the migration without using a new point code or reconfiguring their network.
Refer to the Database Administration Manual - Features for current information on this feature.
Upgrade Considerations
The upgrade of fielded SG software will take into account the changes introduced by End Office Support, and no degradation of system capability will occur from such an upgrade. This feature adds the new Remote Application Table.
Limitations
-
The APC assigned to an IPGW linkset should not be used as an IPC for an EO Node. The IPGWx application is to be used as a redundant pair of cards. Proper use would involve having equal cost routes to each linkset of a pair of IPGWx cards. This scheme prevents the use of the IPGWAPC since only one route should exist to that point code. In addition, the IPGWx application currently expects to receive only SNMs for the IPGWAPC. All messages received for the IPGWAPC are discarded, though SNMs may generate MTP primitives. This feature will not prevent the IPGW APC being provisioned as an IPC, but IPGWx will discard the traffic destined to the IPC for this configuration.
-
A third point code, the IPC, must be assigned to the EO Node, in order to allow two equal cost routes to be provisioned.
-
The End Office Support feature allows one or more IP network elements to share the SG's true and secondary point codes. IP nodes having their own point code are also supported, but not as end office nodes. This feature eliminates one and only one point code for a given network type.
-
This feature provides no method for a mated pair of SGs to share an End Office Node. An End Office Node shares the true or secondary point code of the SG. Each SG of a mated pair continues to require a unique true point code. There are no benefits of redundancy if mated SGs share an IPNE operating as two EO Nodes.
-
This feature prevents an IP end office node from receiving through-switched messages having SI=0, SI=1, and SI=2, with the exception of UPUs. If such messages are desired, then the IP network element cannot be configured as an end office node.
-
An end office node cannot share a SCCP subsystem other than SCMG with the SG. An end office node's SCCP subsystem takes priority over the SG's local SCCP subsystems.
-
An end office node must not generate non-UPU, non-TFC, and non-RCT network management messages having OPC=TSPC or CPC=TSPC. The IPGWx application will discard such messages that it receives.
-
There are no new measurements specific to the End Office feature. Existing per-socket measurements can be used to see the number of MSUs going to and received from each socket.
-
Messages arriving at the SG from the network and having DPC=IPC shall be routed, just as if the message had arrived having DPC=TSPC and an assigned remote application. Such a message will bypass the new discrimination algorithm and be immediately forwarded to the EO Node.
-
This feature shall not prevent a user from provisioning a routing key having DPC=IPC. The IPGWx will not generate network management when such a routing key changes states. Messages arriving at the IPGWx cards with DPC=IPC are changed to have DPC=TSPC prior to routing key lookup, and so a routing key having DPC=IPC will never be a match for a message. If no matching routing key having DPC=TSPC is available, then MSUs with DPC=IPC arriving at the IPGWx for transmission will be silently discarded with private pegs.
2.157 Enhance GSM MAP Screening to add TC_Continue and End (Release 35.1)
Description
The Enhance GSM MAP Screening to add TC_Continue and End feature enhances the GSM MAP Screening, Enhanced GSM MAP Screening, and MTP-based GSM Screening features by enabling MAP screening to be performed on non-segmented TC_Continue and TC_End messages.
In order for MAP screening to occur, the messages must meet the following requirements:
-
TCAP-CONT messages must have an Invoke component type.
-
TCAP-END messages must have a Return-Result (Test) type.
Screening is not performed on messages that do not meet these requirements.
Hardware Requirements
The Enhance GSM MAP Screening to add TC_Continue and End feature has no hardware requirements.
Limitations
The GSM Map Screening feature must be on before the Enhance GSM MAP Screening to add TC_Continue and End can be enabled.
2.158 Enhance RTRV-LOG (Release 31.3)
This enhancement will allow the customer to customize RTRV-LOG output. The following list contains examples of customized reports of the logs:
-
Filtered for a particular Output Group
-
Separated between UIMs and Alarms and further separated by Output Group
-
Filtered by a given alarm number or range of numbers.
In addition, this command is modified to become a cancelable command, allowing a user or sysadmin to stop the processing of the command at any time during its execution.
The RTRV-LOG enhancement feature also includeds a new command (rtrv-trbltx) that allows the craftsperson to display information from the trbltx table, which contains all of the UIMs and Alarms for each EAGLE release. The information displayed for each entry of the trbltx table will be the MRN, alarm severity (for Alarms), Output Group and text. Optional parameters for rtrv-trbltx allow the craftsperson to display a subset of the information available to them. The optional parameters for rtrv-trbltx allow an Output Group or TYPE to be specified or a range of MRN numbers to be specified. Additionally, all Output Groups may be displayed with a list of MRNs that match each Output Group.
2.159 Enhanced Bulk Download (Release 25.0)
The EAGLE Enhanced Bulk Download (EBD&A) feature adds “infrastructure” to the EAGLE that supports the implementation of higher functionality at the LSMS.
For current details of this feature, refer to the LNPDatabase Synchronization Manual.
Hardware Requirements
As previously stated, this feature requires the following additional EAGLE hardware, which is devoted to the EBD&A function:
-
One (1) DCM card and FANS.
-
One (1) BLM card. This BLM card must be equipped with enough applique memory cards to be able to load the entire LNP DB. Specifically, the applique requirements for the EBD&A BLM card are exactly the same as the memory requirements for a TSM card running the SCCP application.
Additional memory is required on the SCCP cards to support the addition of 12 million ported numbers. Memory may be added in 256 MByte increments to the TSMs, up to a maximum of 1024 Mbytes of memory.
The following TSM configurations are supported:
-
TSM256: TSM with 256 MB populated memory. Maximum number of ported numbers supported: 2,000,000.
-
TSM512: TSM with 512MB populated memory. Maximum number of ported numbers supported: 4,000,000.
-
TMS768: TSM with 768MB populated memory. Maximum number of ported numbers supported: 6,000,000.
-
TSM1024: TSM with 1024MB populated memory. Maximum number of ported numbers supported: 8,000,000 without optional software feature, 12,000,000 with optional software feature. In addition, the parameter
lnp12mil=onmust be set.
Refer to the NSD Hardware Manual for current hardware information.
Serviceability
LSMS↔DCM Ethernet Security
Security of the LSMS↔DCM ethernet connection is the customer's responsibility. Neither the EAGLE nor the LSMS will provide any type of security to thwart unauthorized attempts to access the EAGLE and/or LSMS by “hijacking” the connection.
If the customer is concerned about security (e.g. a hacker who gains access to the EAGLE by masquerading as an LSMS, and downloading a faulty database to EAGLE via the bulk download facility), he should take steps to ensure that security is not compromised. One such method would be to provide the LSMS↔DCM connection totally within the customer's own internal network, and install a firewall between the customer's internal network and the "outside world,", as illustrated in the following figure.
Figure 2-35 LSMS↔DCM Connection with Firewall

Administration of the EBD&A Feature
Provisioning of Necessary BLM and DCM Components
For the EBD&A feature to operate, a dedicated BLM and DCM must be present and running the new GPLs developed for this feature.
-
Associating the new EBD&A GPLs with the DCM and BLM card types is accomplished by the existing
ent-card:appl=command to accept new GPL types (EBDADCM, EBDABLM). -
Other commands that could affect the loading or monitoring of these BLM and DCM components of EBD&A have been modified to accommodate the new GPL types as necessary.
Provisioning of EBD&A DCM Ethernet Details
Provisioning of this information is performed by new commands. The following scenario shows the minimum number of steps required to configure the DCM card, so that it is functional for EBD&A purposes:
-
chg-ip-card:loc=xxxx:This command provides little information for the EBD&A DCM, but is a pre-requisite for the command to follow. Since the EBD&A DCM card will be acting as a sockets server, additional parameters that this command provides (such as domain name server IP address) are not needed.
-
ent-ip-host:host=dcm_name:ipaddr=a.b.c.dThis command tells the DCM card what hostname is associated with the DCM card's IP address. The value for the
host=parameter is required in order to associate the TCP/IP port (specified in the next step) with the TCP/IP address (specified on the previous step), but its value is unimportant to the EBD&A DCM: specify any unique value. Theipaddr=value must be the same value that was specified on thechg-ip-lnkcommand. -
chg-ip-lnk:loc=xxxx:port=x:ipaddr=a.b.c.d:submask=x.x.x.x:…This command tells the DCM card at
loc=to assign the IP address (ipaddr=) to the indicated port (port in this context is the physical port 'A' or 'B' on the DCM card: it does not refer to the TCP/IP port number). The DCM card now knows what its IP address is for the indicated physical port. Additional parameters available for this command can be used if necessary to configure the operational parameters of the DCM's ethernet link (e.g. link speed).
Note:
The EBD&A feature is designed to use only the 'A' port of the DCM card. Be sure to attach the physical ethernet connection (i.e. the wire) only to the 'A' port, and then configure the 'A' port accordingly. The 'B' port is ignored by the EBDADCM GPL, even if provisioned via the CHG-IP-LNK command. The 'B' port can be configured and used to allow source-level debugging of the DCM card via the VxWorks "Tornado" debugging tool.
Selection of DCM Card Slot
The DCM card currently takes up 2 slots in the EAGLE shelf card cage due to the large heat sink on the top of the DCM card. Because of this, the DCM cannot be provisioned in any arbitrary slot. Certain slots in the card cage are adjacent to the cage sides, and/or are adjacent to metal supports welded into the card cage. These slots cannot be used to house a DCM card.
Also, the DCM card requires a substantial amount of power. Due to the way the EAGLE fuses power pairs of card slots, the DCM should always be provisioned into an odd-numbered card slot. For example, fuse 1A provides power to both slots 1101 and 1102. The combined current draw for both of these slots must not exceed 3A, or the fuse may blow. Inserting a DCM into slot 1102 when there is another card in 1101 could cause the total current requirements for both of these slots to exceed 3A.
Additionally, the shelf equipped with the DCM card must be equipped with fans in order to keep the card from overheating.
Minimum LSMS↔EAGLE Ethernet Facility
The customer is responsible for selecting and providing a connection between the EAGLE and LSMS locations so that the LSMS and DCM components may communicate via ethernet.
Unless the speed of the communications line is very poor, the maximum processing speed of the EBD&A feature will most likely be limited by the performance of the BLM card, which has a maximum rate of » 400 DB inserts/second as previously stated; providing communications facilities of very high capacity will not make the EBD&A feature perform its work any faster.
However, selection of an extremely slow communications line will result in EBD&A performance degradation.
Assuming the following:
-
Maximum BLM DB insert rate = 400 entries/second.
-
Average size of a DB record passed from LSMS à DCM over ethernet = 95 bytes/entry (Note: maximum size would be 120 bytes/entry ).
-
LSMS is able to extract DB entries from its database (Versant) and present them across the ethernet connection to the EAGLE as fast as the BLM can process them.
In order to keep the BLM card 100% busy during bulk download, the ethernet connection must have a transmission rate of:
400 entries/second * 95 bytes/entry = 38,000 bytes/second
During high-speed audit, it is estimated that the BLM can extract and present 3400 TN/checksum pairs/second. The LSMS, however, has a measured maximum performance of 1,666 extracts from its database/second, therefore the LSMS will most likely be the limiting bottleneck during audits:
1666 entries/second * 9 bytes/entry = 14,994 bytes/second
Therefore, Tekelec recommends that the LSMS↔EAGLE communications link installed for the EBD&A feature have a transmission capacity of » 38,000 bytes/second.
Upgrade Considerations
New EBD&A GPLs
The EBD&A feature introduces two new GPL types to Release 25.0. However, upgrades from previous releases to Release 25.0 need not include steps to create these new GPLs on the system being upgraded, since Release 25.0 introduces functionality to create feature-specific GPLs at the time the feature is installed at the customer site.
Modifications to EAGLE LNP Subscription Records on Disk
A new 4-byte field has been added to each LNP subscription record in the EAGLE LNP DB. This field is created from unused pad area already present in the record. This new field holds the CRC-32 checksum for the record, enabling the high-speed audit of the subscription record contents by the LSMS. There is no need to obsolete existing LNP DB tables, or create new ones, in order to accommodate the new checksum.
2.160 Enhanced Database Status Reports (Release 20.0)
The database level (resident on every card in the system) and the “coherency” indicator are displayed with this feature. The coherency indicator identifies corrupt database files, which can be corrected using database management commands.
2.161 Enhanced GPL Management (Release 25.0)
Description
This feature minimizes the effort required to add new GPLs (applications) to EAGLE by updating a table of GPL attributes. The table makes each application available to all existing commands which contain the "appl = <xyz>" parameter. Likewise, all commands that display an application also have the parameter available.
All commands that use an appl= parameter, as well as the commands that administer GPLs, must check the existence of the GPL definition in the table as part of their semantic validation.
All commands that display an APPL as part of their output must retrieve the application name from the new table.
All processes that download applications must retrieve the GPL DOS filename from the new table.
Upgrade Considerations
In order to provide access to new GPLs, the APPL Definitions Table must be updated. Most of this table is filled in at compile time, which means that an updated OAM GPL must be provided in order to support new GPLs. During the upgrade process, new GPLs are available once the updated OAM is running.
The feature does not change any DCBs or maintenance blocks; thus no on-the-fly conversion of data structures is required.
There are no new DMS tables defined by the feature, and no existing DMS tables are modified; therefore, no database conversion is required.
2.162 Enhanced GSM MAP Screening (Release 31.4, 39.2)
The existing Enhanced GSM MAP Screening (EGMS) feature is updated as follows:
- Messages can cross between ITUI and ITUN domains and spare domains. Messages remain restricted from crossing between ANSI and ITU domains.
If the ANSI ITU SCCP Conversion feature is not turned on, then the domain crossing is performed by altering the message transfer part (MTP) portion of the message. If the ANSI ITU SCCP Conversion feature is turned on, then the domain crossing is performed using point code conversion on the point codes for the SCCP called party (CdPA) and calling party (CgPA).
- The translation type (TT) of an outgoing message can be modified per EGMS ruleset.
The MAP SCRN table is searched for a provisioned TT value. If a match is found, then this value is used to set the TT value for the CdPA of the outgoing message. If a match is not found, then the OPCODE table is searched. If a match is not found in either table, then the TT value is not modified, and the outgoing message uses the TT value that existed after global title translation (GTT) was performed.
- Non-segmented XUDT and XUDTS messages are supported for GT-routed and MTP-routed GSM messages.
2.162.1 Feature Control Requirements
No additional feature control requirements are associated with the updates to the EGMS feature.
2.163 Enhanced GTT (Release 26.0)
Description
EGTT is an enhancement to the existing GTT function. EGTT provides the following main enhancements to EAGLE's current GTT:
-
Increased number of selectors:
-
Relaxed GTT rules:
-
Deletion of GT:
-
Inclusion of SSN in the CDPA:
-
Inclusion of OPC in the CGPA:
Refer to the Database Administration Manual - Features for current details of this feature.
Upgrade Considerations
After the upgrade and the EGTT feature is enabled, any ITU selectors added with GTI=4 that match any pre-upgraded entries will be an exception to the numbering plan and/or nature of address indicator of the pre-upgraded entry. The pre-upgrade entry will now match on any set of numbering plan-nature of address combinations, other than the added post-EGTT-enabled entries.
2.164 Enhanced Link Diagnostics (Release 22.0)
Enhanced Link Diagnostics provides improved information reporting to aid in the investigation of link failures. SS7 Level 2 status information is buffered before and after a link failure has occurred. This feature provides the capability to loop the internal transmit and receive data on the ISCC chip. Link failures can occur on the near end node, far end node or the wire connecting the two nodes. This capability either confirms or eliminates a portion of the near end node as the reason for the link failure.
2.165 Enhanced Load Distribution (Release 21.0)
This feature improves the load distribution of traffic on a combined linkset when a signaling link in one of the linksets in the combined linkset fails.
Before Release 21.0, if a signaling link in a combined linkset fails, the traffic is redistributed to the other links in the same linkset. With this feature, the traffic is redistributed over the signaling links in the combined linkset. This feature applies to both ANSI and ITU signaling links.
Traffic is distributed over the combined linkset using the signaling link selection (SLS) values assigned to the signaling links in each linkset. When a signaling link in the combined linkset fails, the system uses the SLS values assigned to the signaling links, the number of signaling links in each linkset, and the number of failed signaling links in the combined linkset to determine which of the remaining signaling links in each linkset will carry the failed signaling link traffic.
To evenly distribute the traffic on all the signaling links in a combined linkset, each linkset in the combined linkset must contain the same number of signaling links.
2.166 Enhanced Routing Key Support (IP7 Release 2.0)
Release 2.0 offers several enhancements for the routing key table that the IP7 Secure Gateway uses to route SS7 Message Signaling Units (MSUs) over the IP network. The routing table is used for SCCP/TCAP-over-IP, ISUP-over-IP, and non-SCCP/non-ISUP connectivity, each of which uses the ss7ipgw application.
Understanding the Routing Key Table Used in Release 1.0
The routing key table maps SS7 Routing Keys to TCP/IP socket names, as illustrated by the example in table Example SS7 Routing Key Table. MSUs that match the parameters in a given row are sent over one of the sockets shown for that row (up to 16 socket associations can be defined for a single routing key). Multiple sockets for a given row allow load sharing. In addition, multiple routing keys can be used to send traffic to a single socket.
Table 2-41 Example SS7 Routing Key Table
| SS7 Routing Keys | TCP/IP Sockets that carry traffic for that Routing Key | |||||
|---|---|---|---|---|---|---|
| SS7 DPC | SS7 SI | SS7 SSN | SS7 OPC | CIC START | CIC END | Socket Name |
|
DPC-SI-SSN routing key for SSCP/TCAP-over-IP connectivity |
||||||
|
5-5-5 |
03 |
6 |
- |
- |
- |
KC_HLR1_1201 KC_HLR2_1201 KC_HLR1_1203 KC_HLR2_1203 |
|
ISUP-CIC rouiting key for ISUP-over-IP connectivity |
||||||
|
5-5-6 |
05 |
- |
4-4-4 |
1 |
100 |
DN_MSC1_1201 DN_MSC2_1201 DN_MSC1_1203 DN_MSC2_1203 |
|
DPC-SI routing key for non-SCCP/non-ISUP connectivity |
||||||
|
5-5-7 |
02 |
SF_HLR1_1204 |
||||
IP7 Secure Gateway release 1.0 required the user to use the ent-appl-rtkey and dlt-appl-rtkey commands to configure the routing key table, which could hold a maximum of 250 keys. For more information about using these commands, refer to the IP 7 Secure Gateway Database Administration Manual - Features.
Enhancements to the Routing Key Table in Release 2.0
IP7 Secure Gateway release 2.0 provides the following enhancements for routing keys:
-
Routing keys can be dynamically configured by the receipt of a TALI message from the IP network.
-
Routing keys that are statically defined (using the
ent-appl-rtkeycommand) can be changed by using a new commandchg-appl-rtkey. -
Up to 1000 routing key entries per DCM card are supported. The customer can specify the maximum number of static keys and dynamic keys to be supported, as long as the total is less than or equal to 1000.
Dynamic Routing Key Registration
This enhancement allows a socket to automatically direct traffic towards, or away from, itself by sending a message to the IP7 Secure Gateway. This enhancement allows customers to add IP7 routing key intelligence to their IP applications rather than requiring user entry of static routing keys.When transmitting Message Signaling Units (MSUs), the IP7 Secure Gateway routing code looks for a dynamic routing key before searching for a static routing key. When a socket fails, all dynamic entries associated with it are deleted. A dynamic routing key entry can have the same parameters as a static key entry.
Adjusting Static Routing Key Entries
IP7 Secure Gateway release 2.0 allows the use of the new chg-appl-rtkey command to make one of following adjustments to a routing key that has already been statically defined:
-
Any existing static entry’s socket associations can be overwritten by a new socket association. If the
chg-appl-rtkeycommand assigns a new socket name to a routing key has multiple socket associations, all socket associations are replaced with the new socket name. -
Any existing ISUP-CIC entry (an entry whose SI is equal to 05) can be split into two entries by naming a SPLIT value. One entry uses the original CIC START value and makes the CIC END value equal to one less than the SPLIT value. The other entry uses the SPLIT value as its CIC START value and the original CIC END value for its CIC END value. Each entry retains the OPC, DPC, SI, and socket name associations from the original entry.
-
Any existing ISUP-CIC entry (an entry whose SI is equal to 05) can have its CIC range extended and/or decreased as long as the new range does not overlap the range on any other key.
Only one of these changes can be made with each use of the chg-appl-rtkey command. If additional changes are needed, enter the command again for each change needed.
Support of Additional Routing Keys
IP7 Secure Gateway release 2.0 supports up to 1000 routing key entries (increased from the previous limit of 250) for each DCM card. These 1000 key entries may be either dynamic entries (added by receipt of a request from the IP network) or static entries (configured using the ent-appl-rtkey and dlt-appl-rtkey commands) or a combination of both. The user can specify the maximum number of static entries and dynamic entries allowed using the chg-sg-opts command.
An additional change is a parameter added to the rtrv-appl-rtkey command to allow the user to specify the maximum number of routing key entries to be displayed.
Understanding the Use of Dynamic and Static Routing Entries for ss7ipgw Routing
The IP7 Secure Gateway has two DCM cards, each of which contains a routing table of up to 1000 entries. The static entries in one table are identical to the static entries in the other table; the dynamic entries may differ depending on messages received from other IP nodes. The following table provides a summary of the characteristics of static and dynamic entries.
Table 2-42 Comparison of Static and Dynamic Entries in Routing Key Table
| Characteristic | Static Entries | Dynamic Entries |
|---|---|---|
|
Provisioned by: |
|
Receipt of message over socket; purged when socket fails or DCM card is reset |
|
Option of |
|
|
|
Same on both DCMs? |
Yes |
Not necessarily |
|
Used for routing: |
Used only if no matching dynamic entry exists |
Used first for routing |
2.167 Enhanced Software Loading (Release 20.0)
This feature reduces the EAGLE’s reload time during system initialization or restart to less than 5 minutes. To meet this requirement, the system is reloaded from the fixed disk drives on both the active and standby TDMs (terminal disk modules). Some subsystems are loaded from one fixed disk drive and other subsystems are loaded from the other fixed disk drive. The system operating software determines which subsystems are loaded from each fixed disk drive.
The following conditions are assumed.
-
That no cards fail during the loading process.
-
All cards remain aligned on the IMT bus which allows the clock to start (no bus transition).
-
The loading of gateway screening data is not included in the loading process.
Caution:
All LIMs are of one application type. The 5 minute loading requirement does not apply if both the SS7ANSI and CCS7ITU applications are being used on the EAGLE.
2.168 Enhanced STC Card Performance (Release 35.0)
Description
The Enhanced STC Card Performance feature increases the capacity of the STC card to 4,800 TVG grants per second. This allows MSUs on IP, low-speed, and high-speed links to be monitored for data feed to the Integrated Message Feeder (IMF). This feature applies to both the K6-II and K6-III variants of the SSEDCM card.
Hardware Requirements
The Enhanced STC Card Performance feature has the following hardware requirements:
- A minimum of 2 STC cards must be provisioned in an EAGLE 5 ISS.
- A maximum of 32 STC cards can be provisioned in an EAGLE 5 ISS.
- A maximum of 3 STC cards can be provisioned in shelves that contain HMUX cards.
- The STC capacity of shelves that contain HMUX cards should be provisioned in adjacent shelves. Half of the STC capacity should be provisioned on the current shelf and the other half on either the previous or next shelf.
- Shelves where monitoring of IP links is performed must contain HIPR cards. The STC cards should be provisioned in the same shelf as the HIPR cards. If this does not occur, data feed is inhibited for IPLIMx/IPGWx, and an alarm is generated for each monitored link on the card.
Limitations
The Enhanced STC Card Performance feature has no limitations.
2.169 Enhancement to Backup TFR/TCR Procedures (Release 21.0)
TFR/TCR messages may be lost or not processed at a node due to a signaling link failure, congestion or other error conditions. Because of this, other nodes continue to send traffic over a restricted route. This results in C-link congestion. To help prevent this problem, the TFR/TCR procedures have been improved to send a second backup TFR/TCR once per linkset in response to messages received after the first TFR/TCR.
This feature is currently supported in the EAGLE (Release 3.3 and later) for TFRs with one exception.
When a TFR is generated because of internal congestion, as opposed to normal route failure, the EAGLE responds with one TFR for every 10 messages received. In Release 21.0, this has been changed so that after the first TFR/TCR is sent, the level 3 T18 timer is started. When the level 3 T18 timer expires, the EAGLE sends only one backup TFR/TCR.
This feature applies only to ANSI signaling links.
t a response being returned by the EOAP. If more than one message is sent to the EOAP without the LSMS waiting for a response, the LSMS must manage retries and the sequencing of messages.
The EOAP must be configured locally with the LSMS OSI-Address information necessary for association establishment. The EOAP will initiate association connections with the LSMS.
2.170 Enhancement to GSM ATI Query (Release 45.0)
The ATINP feature is enhanced to support ATI queries that request Location Information.
The chg-atinpqopts command is used to provision the functionality to process Location Information requests and to format the Visitor Location Register number (VLR-number) in the Location Information field of the ATI ACK response message.
2.171 Enhancement to GTT Failure Messages (Release 25.0)
Description
This feature enhances the current SEAS REPT-NOTRNS messages to include four optional parameters currently not supported in the EAGLE version of these messages.
-
c4- "Called Party Global Title Address" -
d1- "Calling Party Address Type" -
d2- "Calling Party Subsystem Number" -
d3- "Calling party Address Point Code"
Effect on Existing UIMs
Implementation of this feature involves a minor change to one of the existing EAGLE UIM formats. To add the CgPA information to the SEAS REPT-NOTRANS message, 6 bytes of the DATA field I16 have been deleted. The format before and after the change is shown below; changes are shown in bold.
xxxx.xxxx CARD cccc,p INFO 'test'
SIO=xx OPC=###-###-### DPC=###-###-###
CDPA LENGTH=### MSG TYPE=##
CDPA: AI=xx PC=###-###-### SSN=### TT=### ADDR=##########
DATA=xx xx xx xx xx xx xx xx xx xx xx xx
xx xx xx xx xx xx
LSN=[lnkset]
Format with new feature:
xxxx.xxxx CARD cccc,p INFO 'test'
SIO=xx OPC=###-###-### DPC=###-###-###
CDPA LENGTH=### MSG TYPE=##
CDPA: AI=xx PC=###-###-### SSN=### TT=### ADDR=##########
DATA=xx xx xx xx xx xx xx xx xx xx
xx xx xx xx xx xx
LSN=[lnkset]
Note:
The DATA field that is output begins with the CdPA part of the MSU. The CdPA part of the MSU is of variable length, but in most cases is organized as follows:
1st Byte - CdPA Length
2nd Byte - Address Indicator
3rd Byte - SSN
4th Byte - Translation Type
Last 11 Bytes - CdPA Address
The following table lists the UIMs affected by this change, and use UIM format I16.
Table 2-43 Affected EAGLE UIMs
| UIM # | Trouble Text |
|---|---|
|
1029 |
SCCP rcvd inv Cld Party - bad GT ind |
|
1033 |
SCCP rcvd inv Cld Party - bad network |
|
1034 |
SCCP rcvd inv Cld Party - no SSN |
|
1042 |
SCCP rcvd inv GT - bad Translation Type |
|
1043 |
SCCP did not route - bad translation |
2.172 Enhancement to the Prepaid IDP Query Relay Feature (Release 39.0)
The Prepaid IDP Query Relay (IDP Relay) feature is enhanced to provide a flexible configuration that allows:
- Modification of incoming calling party number (CgPN) and called party number (CdPN) digits for RTDB lookup
- The ability to request RTDB lookup for calling and called parties
- Flexible formatting of output numbers
The flexible configuration is achieved using the Numbering Plan Processor (NPP) to configure Services, Conditioning Actions, and Service Actions for the IDPR service.
2.172.1 NPP Modifications
The NPP modifications added to support the flexible configuration of the IDP Relay feature include:
- Services
The IDPRCDPN and IDPRCGPN services are added to provide CdPN and CgPN number conditioning and formatting for the flexible configuration of the IDP Relay feature.
- Conditioning Actions
The ACLAC Conditioning Action is added to update the AC and append the AC to the incoming digit string. This service action is supported by the IDPRCDPN service.
- Service Actions
The CDPNNP, LACCK, CCNCCHK, and CGPNNPRQD actions are supported by the IDPRCDPN service. The CGPNNP Service Action is supported by the IDPRCGPN service.
2.172.2 Feature Control Requirements
The IDP Relay feature has the following feature control requirements:
- A FAK for part number 893-0160-01.
- The GTT feature must be turned on before the IDP Relay feature can be enabled.
- If the LNP feature is enabled, then the IDP Relay feature cannot be enabled.
- The IDP Relay feature cannot be enabled if TSM cards running the SCCP application are present in the system.
- The IDPRCDPN NPP Service must be turned on before the IDP Relay feature can be turned on.
- Once the feature is turned on, it cannot be turned off.
- A temporary FAK cannot be used to enable the feature.
2.172.3 Hardware Requirements
The flexible configuration of the IDP Relay feature does not have any additional hardware requirements. The existing IDP Relay feature cannot be enabled if TSM cards running the sccp application are present in the system. If a TSM card is inserted after the feature is enabled, then the card auto-inhibits.
2.173 Enhancements to GWS Reject Messages (Release 25.0)
Description
This feature enhances the current SEAS REPT-SCRREJ message to include two optional parameters currently not supported in the EAGLE version of these messages. The two optional parameters are:
-
rec- "Rejection Error Code" -
z- "Supplier-Specific Parameter Text"
SEAS Compliance
The following table maps EAGLE rejection reasons to the SEAS rejection error codes.
Table 2-44 EAGLE-to-SEAS GWS Rejection Mapping
| EAGLE Gateway Screening Reject Reason (RPT_MRN_GWS_…) | EAGLE Supplier-Specific Parameter Text in the “z” Field | SEAS Code | SEAS Reject Code Meaning (per GR-778) |
|---|---|---|---|
|
OPC_NOT_ALLOWED OPC_BLOCKED |
”GWS rcvd OPC that is not allowed” ”GWS rcvd OPC that is blocked” |
ONNV |
OPC not valid |
|
DPC_NOT_ALLOWED DPC_BLOCKED |
”GWS rcvd DPC that is not allowed” ”GWS rcvd DPC that is blocked” |
DNNV |
DPC not valid |
|
SIO_FAILED |
”GWS rcvd SIO that is not allowed” |
SINV |
SI not valid |
|
No EAGLE Equivalent |
NINV |
NIC not valid |
|
|
PRIORITY_FAILED |
”GWS rcvd a priority that is not allowed” |
PRNV |
PRI not valid |
|
H0H1_FAILED |
”GWS rcvd H0/H1 that is not allowed” |
HCNV |
H0 or H1 not valid |
|
CLG_FAILED |
“GWS rcvd Clg Party that is not allowed” |
CGNV |
CgPA PC or SSN not valid |
|
No EAGLE Equivalent |
LGNV |
CgPA/link set combination not valid |
|
|
No EAGLE Equivalent |
RINV |
CdPA routing indicator not valid |
|
|
CLD_FAILED |
”GWS rcvd Cld Party that is not allowed” |
CDNV |
CdPA SSN or DPC not valid |
|
DESTFLD_NOT_ALLOWED |
”GWS rcvd AFTPC that is not allowed” |
DFNV |
Affected destination field not valid |
|
SCMG_APC_FAILED |
”GWS rcvd SCMG with not allowed AFTPC” |
AFNV |
Affected PC/SSN not valid |
|
No EAGLE Equivalent |
FINV |
SCMG format ID not valid |
|
|
GT_TYPE_FAILED ALLOWED_TT_FAILED |
”GWS rcvd Translation Type not allowed” ”GWS rcvd invalid GTI in TT Screening” |
TTNV |
TT not valid |
|
No EAGLE Equivalent |
ISNV |
ISUP message type not valid |
|
|
TFC_APC_FAILED RSP_APC_FAILED RSR_APC_FAILED TCA_APC_FAILED TCP_APC_FAILED TCR_APC_FAILED TFA_APC_FAILED TFP_APC_FAILED TFR_APC_FAILED UPU_APC_FAILED |
”GWS rcvd TFC, AFTPC not in routing tbl” ”GWS rcvd RSP, AFTPC not in routing tbl” ”GWS rcvd RSR, AFTPC not in routing tbl” ”GWS rcvd TCA, AFTPC not in routing tbl” ”GWS rcvd TCP, AFTPC not in routing tbl” ”GWS rcvd TCR, AFTPC not in routing tbl” ”GWS rcvd TFA, AFTPC not in routing tbl” ”GWS rcvd TFP, AFTPC not in routing tbl” ”GWS rcvd TFR, AFTPC not in routing tbl” ”GWS rcvd UPU, AFTPC not in routing tbl” |
OTNV |
Message rejected for a reason not identified by any of the other “rec” field values. |
2.174 Enlarged LNP SPID and NPANXX Support (Release 24.0)
The Enlarged LNP SPID and NPANXX Support increases the maximum number of service provider IDs (SPID) and NPANXXs that can be configured in the database.
The maximum number of service provider IDs is increased to 10,000. If you try to enter more than 10,000 service provider IDs with either the ent-lnp-sp, ent-lnp-sub, or ent-lnp-lrn commands, the attempt will be rejected with this message.
Error Messages
E3133 - LNP Service Provider Table is full
The maximum number of NPANXX entries is increased to 150,000. If you try to enter more than 150,000 NPANXXs with either the ent-lnp-npanxx, ent-split-npa, ent-lnp-sub, or ent-lnp-lrn commands, the attempt will be rejected with this message.
E3138 - LNP NPANXX Table is full
RTRV-LNP-SP Command
The parameters num, force, and sp have been added to the rtrv-lnp-sp command to control the number of entries in the service provider ID table that are displayed. Refer to the Commands Manual for current usage information.
2.175 ENT-CARD Enhancement (Release 46.0)
ENT-CARD Enhancement feature enhances the ent-card command to provision new applications for EAGLE cards.
2.176 Entering a Global Title Translation to a Non-Mated Application without Adding the Application as Mated Application (Release 22.0)
In Release 22.0, a global title translation can be entered to a non-mated (solitary) application, either through an EAGLE terminal or the SEAS interface, without requiring the application to be defined by the EAGLE’s ent-map command.
The force parameter (valid values yes or no) has been added to the EAGLE’s ent-gtt command that allows the user to override the rules that make sure that the application is defined in the mated application table. The default value for the force parameter is no for the EAGLE’s ent-gtt command. If a global title translation is being added from the SEAS interface, the default value for this parameter is yes. When a global title translation is entered on the SEAS interface, the EAGLE does not check to see if the specified application is defined in the mated application table.
If the global title translation is a final global title translation, the application being referenced by the global title translation must be in the mated application entity set. If the global title translation is being entered on an EAGLE terminal with the ent-gtt command, the force=yes parameter is not specified, and the mated application is defined the mated application table, the command is rejected with the following error messages.
E2450 Cmd Rej : PC/SSN does not exist as a mated application
E2419 Cmd Rej : Point code does not exist in the remote point code table
If the force=yes parameter is specified with the ent-gtt command and the specified application is required to be defined in the mated application table, the following warning messages are displayed.
CAUTION - DPC-SSN does not exist in the Mated Application table.
CAUTION - DPC does not exist in the Mated Application table.
If the final global title translation is entered on the SEAS interface, the rules checking the mated application table do not apply.
2.177 ENUM Enhancement to update ENUMPROF table
The ENUM feature has been enhanced to add another regular expression format to be sent to the ENUM client in the NAPTR response. The regular expression is modified as follows:
- The DEFCC and RN from the NPDB lookup are inserted before the called party DN, as “sip: +<DEFCC><RN from the NPDB lookup><Called Party DN>”
- The DEFCC and PREFIX parameter configured in the ENUM Profile Table are inserted after RN tag as “rn=+<DEFCC><PREFIX>”.
The resulting regular expression format will then be:
sip: +<DEFCC><RN from the NPDB lookup><Called Party DN>;npdi;RN=<+DEFCC><PREFIX configured in ENUM Profile Table>@<domain name defined in ENUM Profile Table>
This regular expression format will be used when the NAPTR service as configured in the ENUM Profile Table is PSTNSIP and the new INCPREFIX option as configured in the ENUM Options Table is YES.
The maximum number of entries allowed in the ENUM DN Block Profile Table has been increased from 2048 to 4096.
The chg/ent/rtrv-enum-prof and the
chg/rtrv-enumopts commands were updated to support this
enhancement.
See Feature Description in ENUM User's Guide for more information.
2.178 ENUM on SLIC Network Redundancy Enhancement (Release 46.5)
This feature introduces network communication redundancy on the SLIC card. Four network interfaces will support ENUM - two for EPAP communication and two interfaces for signaling. One SLIC card running the ENUM application can connect to two EPAPs and two signaling networks at the same time. Interface A/D is used for EPAP connectivity, and interface B/C is used for the signaling network.
Figure 2-36 ENUM on SLIC Network Redundancy Model
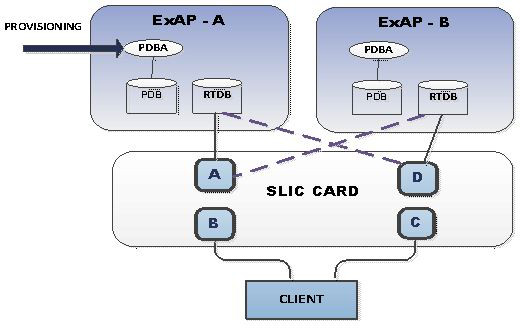
See ENUM User's Guide for more information.
2.179 EOAP/OAP Support of HSOP Protocol (Release 28.0)
The EOAP/OAP currently supports only the Q.3 interface to the LSMS. The ELAP supports the HSOP interface to the LSMS. From an internal perspective, it is advantageous for the LSMS to support a single interface to the EAGLE, regardless of the architecture deployed. This feature achieves a single interface by requiring the OAP/EOAP to support the HSOP protocol.
HSOP is a fast, reliable protocol developed by Tekelec. LSMS Release 5.0 will support one HSOP protocol to communicate with EAGLE release 28.0 and future EAGLE releases.
LSMS EAGLE Communication Overview
Prior to release 5.0, LSMS supported two different protocols to communicate with pre-28.0 EAGLE releases.
Figure 2-37 LSMS EAGLE Protocol Interface for Pre-5.0 LSMS Releases and pre-28.0 EAGLE Releases

The Q.3 protocol is used by LSMS to communicate with EOAP/OAP. HSOP protocol is used by the EBDA process to send information to DCM cards on EAGLE. Enhanced HSOP protocol is used to communicate with the ELAP when the 48 Million feature is enabled.
EOAP/OAP Overview
EOAP/OAP (OSS Application Processor) was developed to provide telephone company network management systems access to the EAGLE STP. SEAS (Signaling Engineering and Administration System) provides network management functionality. EOAP/OAP interfaces with SEAS using Telcordia standards and licensed code.
EOAP/OAP software consists of few a processes running on the Solaris 2.5.1 UNIX operating system. With the introduction of the LNP (Local Number Portability) feature, EOAP/OAP was extended to provide the communication channel for updates sent from LSMS to EAGLE LNP database using Q.3 protocol.
EOAP/OAP consists of 11 processes. Some processes provide SEAS access to EAGLE; others process LNP database updates sent from LSMS to EAGLE. LNP database updates are sent from LSMS using the Q.3 protocol to the EOAP/OAP emsAgent process.
The purpose of emsAgent process is to translate Common Management Information Protocol (CMIP) messages from the LSMS M-Actions into TL-1 commands that can be interpreted on the EAGLE by the UPL parser.
HSOP replaces the Q.3 protocol, and hsopAgent replaces the emsAgent (see figure). The hsopAgent process translates LSMS HSOP commands to TL-1 commands that can be interpreted on the EAGLE by the UPL parser. The new hsopAgent provides the same interface to the ysTTy process and the ysT1mnt process. It is seamlessly integrated with current EOAP/OAP software; it does not require special configuration to run properly.
New Hardware Required
No new hardware is required for this feature.
2.180 EPAP 2.0 Alarm Migration from ELAP (EAGLE 28.0)
This EAGLE 28.0 feature converts EPAP message notification and alarming from the type previously used in EPAP 1.0 to the type used in ELAP 2.0.
As revised, EPAP 2.0 employs different EAGLE UAMs, uses the MPS System Health Check (syscheck) utility to diagnose and report MPS/EPAP platform problems, and uses MPS LEDs more completely.
For additional details, refer to the EPAP Administration Manual and the Maintenance Manual.
2.181 EPAP Automated Database Recovery (EPAP 7.0)
Description
The EPAP Automated Database Recovery (ADR) feature is used to restore the EPAP system function and facilitate the reconciliation of PDB data following the failure of the Active PDBA.
The automated recovery mechanism provided by this feature allows 1 PDBA to become Active when 2 PDBAs think they are active and have updates that have not been replicated to the mate PDBA. The software selects the PDBA that received the most recent update from it's mate to become the Active PDBA (the PDBA that was the Standby most recently will become the Active). No automatic reconciliation is performed because the system has insufficient information to ensure that the correct actions are taken.
In order to return the system to normal functionality, a manual PDB copy from the PDBA the software picked to be Active to the PDBA that is in the replication error (ReplErr) state must be performed. However, provisioning can resume until a maintenance period is available to do this.
This feature uses a replication error list that consists of updates that exist as a result of a failure during the database replication process from the active-to-standby PDB. These updates have not been propagated (reconciled) throughout the system and require manual intervention to ensure the EPAP systems properly process the updates.
Limitations
-
The EPAP ADR feature can be turned on or off. The default setting is off.
-
The EPAP ADR feature must be turned on for both MPS-A boxes of an MPS pair.
-
The EPAP ADR feature requires Standby-homing to be active. If Active-homing is being used by the customer, DSM re-boots may be required if they have taken updates from the Active PDB that are different from what has been replicated to the Standby PDB.
-
Each EPAP can support a minimum of two replication error lists.
2.182 EPAP Command Response Enhancement (Release 31.6)
This feature provides users of the PDBI with the ability to retrieve information about the status of the DSMs in their network. This information includes, but is not limited to, the database level of each card. The DSM database level is of specific importance because the customer can use it to determine when a specific update has made its way to most or all of the DSM cards.
This new information will be made available to PDBI clients through new asynchronous notifications and synchronous requests/responses. New WebUI screens that utilize the new PDBI messages are also created for displaying the DSM information.
In order to propagate the DSM information up from the DSM to being available through the PDBI, the DSM code as well as several processes in the EPAP are changed.
2.183 EPAP DN Block Capacity Increase (Release 46.0)
The EPAP DN Block table capacity is increased from 100,000 DN Blocks to 200,000 DN Blocks. This table capacity increase is necessary to support large network requirements and the additional DN Blocks created by the Self Healing DN Block feature.
2.184 EPAP Expansion to 480M Database Entries (Release 16.1)
The Oracle Communications EAGLE Application Processor (EPAP) Expansion to 480M Database Entries feature allows an EPAP on an E5-APP-B with a 480G disk to support 240 million Directory Numbers (DNs) and 240 million International Mobile Subscriber Identities (IMSIs). In addition, the feature allows for the support of 48 million International Mobile Entity Identities (IMEIs). The combination of 240 million DNs, 240 million IMSIs, and 48 million IMEIs brings a maximum combination of 528 million data. This feature is supported on all EPAP configurations: Mixed EPAP, Standalone PDB, and Non-Provisioning EPAP.
Note:
For the feature to work, the 480M Capacity License must be purchased, with the license capacity manually set to 480M in the EPAP. See alarm " 6000000000400000 - License capacity is not configured" in Alarms and Maintenance Guide for potential failure of configuration information and recovery.Table 2-45 EPAP DB Capacity Combinations
| EPAP Split DB Feature | EPAP240M | Card Provisioned | Max Entries |
|---|---|---|---|
| OFF | OFF | SM4G | 135M |
| OFF | OFF | SM8G | 135M |
| ON | OFF | SM4G | 255M |
| ON | OFF | SM8G | 255M |
| OFF | ON | SM8G | 288M |
| ON | ON | SM8G | 528M (240M DN + 240M IMSI + 48M IMEI) |
2.185 EPAP Feed to External Query Server (EPAP 16.0)
The EPAP Feed to External Query Server feature allows the EPAP to provide a copy of the EPAP Provisioning Database (PDB) to an External Query Server to allow offline query support of the Number Portability database. The Query Server data is synchronized using MySQL 5.6 Replication. A Query Server can connect to only one EPAP. More than one Query Server can be deployed in the system in a master-slave relationship, also known as daisy-chained Query Servers.
2.186 EPAP on T1200 Application Server (EPAP 13.0)
The EPAP on T1200 Application Server feature provides the ability to run EPAP on both the T1000 and T1200 Application Servers. When running on T1000, hubs are used, and when running on T1200, Telco GigE switches are used.
When running on a T1200 AS, a minimum of two switches are needed to support up to 17 Service Module (SM) cards. A maximum of four switches are supported, which in turn support up to 32 SM cards per node.
Note:
EAGLE 5 ISS Release 41.1 supports 24 SCCP cards or less.EPAP to SM Card Network Support
This feature, when running on a T1000 AS, supports SM cards running at 100Mbps at half duplex on side A, and 10Mbps at half duplex on side B, regardless of the type of SM cards used.
- A T1200 AS running with only DSM Cards:
- On side A: 100 Mbps and half duplex
- On Side B: 10 Mbps and half duplex
- A T1200 AS running with only SM4G Cards
- On side A: 100 Mbps and full duplex
- On Side B: 100 Mbps and full duplex
- A T1200 AS running with a mixture of DSM and SM4G cards: (since each individual port on the switch is not configured, the switch is set to run at the DSM card's rate)
- On side A: 100 Mbps and half duplex
- On Side B: 10 Mbps and half duplex
Removal of Man-Machine Interface (MMI) Connectivity on T1200 AS
Due to the lack of serial ports on the T1200 AS, the MMI Connection shall be removed when the feature is running on a T1200 AS. The MMI connection is still available when the feature is running on a T1000 AS.
Hardware Requirements
Either a T1000 AS with hubs or a T1200 AS with switches is required.
Limitations
This feature requires TPD version 3.3.2 and MySQL version 5.0.37.
T1200 AS will not function with hubs that are already in place with a T1000 setup.
2.187 EPAP PDB-RTDB Level Threshold (Release 31.6)
Currently, the amount of time used to determine if the RTDB is too slow on getting updates (alarm is raised) is configurable using the RTDB->Maintenance->Configure Record Delay menu. uiEdit or the cgi script interface can be used to change this value from the default value of 15 to any value between 1 and 300.
The mate PDBA is configurable via the new menu (PDBA->Maintenance->Configure PDBA Record Delay.) The PDBA threshold may also be changed (by development/cust service only) by using uiEdit to change the value of PDBA_MAX_STANDBY_DELAY - which is defaulted to 300.
2.188 EPAP Performance on E5-APP-B (EPAP 15.0)
For EPAP 15.0 on the E5-APP-B card, the performance of various provisioning commands is available in the EPAP Provisioning Performance section of EPAP Administration Manual.
2.189 EPAP Provisioning Blacklist (EPAP 7.0)
Description
TheEPAPProvisioning Blacklist feature helps prevent provisioning of protected address strings in the EPAP database. Provisioning a protected address string as a DN, DN Block, or IMSI may result in unintended and incorrect routing of messages by the EAGLE 5 ISS DSM. The EPAP Provisioning Blacklist feature allows the user to define a list of address strings that cannot be provisioned as DN, DN Block or IMSI address strings. The addresses of all HLRs must be provisioned in the provisioning blacklist in order for the EPAP Provisioning Blacklist feature to work as intended.
A maximum of 150 blacklist ranges is supported by EPAP. A blacklist range is defined by two address strings. The beginning and ending address strings used to define a blacklist range must be between 5 and 15 HEX digits. In addition, both address strings must be of the same length.
The ending address must be greater than or equal to the beginning address and must not conflict with DN, DN block, or IMSI values in the PDB.
Limitations
The EPAP Provisioning Blacklist feature has the following limitations:
-
The blacklist ranges are stored in the PDB database. Since modification of blacklist data is not supported via the PDBI (Provisioning Database Interface), support of PDBI export and import is not possible. In addition, modification of existing blacklist data is not supported.
-
If the blacklist does not include all protected address strings in a customer network, and one of the protected address strings is provisioned as a DN, DN Block, or IMSI, unintended message routing occurs, and may cause network outages.
2.190 EPAP Provisioning Performance Enhancements (Release 29.0)
Description
The Enhanced EPAP Provisioning Performance feature replaces FTS with an asynchronous replication scheme. FTS (Fault Tolerant Server) is a protocol used by Versant to achieve data synchronous replication.
EPAP 1.0 and 2.0 provided support for MPS provisioning databases spanning two sites, with each site hosting a database whose data is replicated synchronously to the other via FTS. To ensure synchronous replication of data, this transfer protocol requires that 8 messages be exchanged per update.
Messaging and data exchange must take place over potentially slow customer network. When the customer network is slow (that is, there exists a network latency issue between the two customer sites containing PDBs, such that the round trip delay between sites exceeds 4-5 ms.), the messaging overhead can cause provisioning rates to drop to unacceptable levels.
Asynchronous replication means that the database receiving an update, in this case the Active PDB, can commit and send the client a success or failure code prior to sending the update to the replicated database, in this case the Standby PDB. Note that only successful updates are replicated. Response turnaround on the Active PDB is thus shortened, and the overhead involved in keeping the databases in sync is spared.
With this feature, the round trip time between nodes may be up to 100 ms. without encountering active/standby lag problems.
Single Transaction Mode PDBI Connection
In EPAP 1.0 and 2.0, all PDBI provisioning commands had to be encapsulated in 'begin' and 'end' transaction statements. Many customers, however, wanted only to send one update per transaction. In such a case, the overhead involved in sending transaction boundary tags can become considerable.
In EPAP 3.0, a new PDBI connection type called 'single transaction mode’ is provided. When using this connection type, PDBI clients are allowed to send updates outside of 'begin' and 'end' transaction delimiters. The PDB treats each update as being its own transaction. However, transaction delimiters are not ignored in 'single mode'. If the PDBI client issues these delimiters, the series of updates encapsulated by them will be treated as one transaction, as they always have been under the default PDBI connection mode.
Hardware Requirements
No new hardware is required or introduced to support the software.
Enhancements to the User Interface
A new state has been added to the set of PDBA states displayed by the Web UI Banner. This state, entitled “REPLERR,” denotes the presence of alarm MAINT_ALARM_PDBA_REPL_FAILED. REPLERR may also appear on the View PDBA Status page, and the View RTDB Status page.
Upgrade Considerations
During upgrade, the Versant replica file, if present on the MPS, will be moved to a different location so that FTS will not be active in EPAP 3.0. Upon removal of the EPAP 3.0 application package, this file will be set back in its original location, so that the system may resume use of FTS following a backout. If updates have been made to the PDB following upgrade, however, backout will entail full PDB restoration. Otherwise, this feature will not affect the EAGLE 28.x/EPAP 2.x to EAGLE 30.0/EPAP 3.0 upgrade.
Limitations
These enhancements introduce an important change to the behavior of EPAP. PDBA switchover can no longer be forced while the PDBAs are able to communicate and the Standby is behind. Switchover now entails allowing some definable amount of time for the Standby PDB to be brought up to the level of the Active PDB. If it fails to obtain equal database level in the allotted time, switchover will not occur, and it will return with the number of levels still left to be replicated. This is a safeguard designed to prevent database inconsistency. However, if the Standby PDB cannot reach the Active PDB to determine its level, then the EPAP will allow PDBA switchover to be forced.
2.191 EPAP RTDB Level Auto Refresh (Release 31.6)
This feature provides a configurable auto refresh rate for the viewPDBAStatus.cgi and viewRtdbStatus.cgi screens. Users are able to halt the refreshing without losing the information displayed on the screen at the time (for debugging or capturing data).
A new field is added to the Modify Defaults screen that takes a value of 0 or 5-600 seconds. This determines if (0 means no refreshing) the PDBA and RTDB View Status pages are refreshed and how often. On the screen, this value can be modified, but reloading the screen using the left-most menu links causes the system default to be changed. The system default applies to both screens.
2.192 EPAP Security Enhancements (Release 29.0)
Description
The EPAP Security Enhancements feature implements a database table of IP addresses that can be added to, deleted from, and retrieved by an authorized user.
The Admin user or user possessing IP action privileges can at any time add, delete, and retrieve IP addresses. Deletion of an IP would cause that IP address to no longer reside in the IP table, and therefore would no longer be able to connect to the EPAP 3.0 GUI. While each of the IP action privileges can be assigned individually to a user, the IP action privileges of add and delete should only be granted to those users with knowledge of the customer network.
The functionality for addition, deletion, retrieval of client IP addresses, and toggling of IP authorization checking are individually assignable and accessible only through the EPAP 3.0 GUI. The IP mechanism implemented in this feature will provide a foundation for further enhancements in privilege control.
The new IP actions of add, delete, retrieval, and toggling of IP authorization checking are available only through the EPAP 3.0 GUI, and added initially to the Admin group only. The privilege of viewing IP addresses on the customer's network should be a security consideration made only by a user with Admin Group privilege. Privileged users can add a custom message in place of the standard 403 Forbidden site error.
Note:
The IP actions of this function that allow for adding, deleting, retrieving authorized IP Addresses, and the toggling of authorized IP checking are NOT accessible from the EPAP 3.0 text-based UI. They are accessible from the EPAP 3.0 GUI only. No IP addresses are restricted from accessing the EPAP 3.0 GUI until the Admin user toggles IP authorization to enabled. When IP authorization checking is enabled, all IP addresses not present in the IP authorization list will be refused access to the EPAP 3.0 GUI.
Hardware Requirements
No new hardware is needed to support this feature.
Upgrade Considerations
This feature will impact the EPAP 1.x/2.x to 3.0 upgrade.
Limitations
IP access and range constraints provided by web server and EPAP 3.0 IP address checking functionality will not protect against IP spoofing . The customer must rely on the security of the customer intranet network to protect against spoofing.
2.193 EPAP Support for HTTPS on GUI (EPAP 9.0)
Description
The EPAP Support for HTTPS on GUI feature allows users to configure whether the GUI can be accessed only by standard HTTP (Hypertext Transfer Protocol) or only by HTTPS (Secure Hypertext Transfer Protocol) or by both.
In previous releases of EPAP, the EPAP GUI used only standard HTTP protocol. The data transfer between the web server and the GUI is not encrypted with standard HTTP protocol; therefore, it can be captured by any network analyzer and viewed. Secure HTTP (HTTPS) supports encryption of data exchanged between the web server and the browser. This facilitates data privacy.
With the addition of this feature, the EPAP now allows the user to configure the use of either HTTP or HTTPS, or both, for the EPAP GUI. The user can disable HTTP. The ability to configure HTTP and HTTPS and the ability to disable HTTP can be limited to a specific user class or group.
When the HTTPS interface is used for the first time, the security certificate needs to be imported to the client machine. For information about importing the secure certificate, refer to the EPAP Administration Manual.
Hardware Requirements
None.
Limitations
None.
2.194 EPAP Support for SSH on PDBI (EPAP 9.0)
Description
The EPAP Support for SSH on PDBI feature provides support for Secure Shell (SSH) on the EPAP Provisioning Database Interface (PDBI) for customers who want additional security protection.
SSH is a robust, commercial-grade, and full-featured toolkit that implements security and network encryption.
In previous EPAP releases, the customer provisioning application (CPA) connected to the EPAP only through a non-secure TCP/ IP connection. Provisioning sent by the CPA was non-secure, because the data was not encrypted and could be seen by packet sniffers in the network.
To make the data transfer between the CPA and the PDBA (Provisioning Database Application) machine secure, SSH tunneling (also called remote port forwarding) is used to securely connect the PDBA machine to the CPA machine.
Figure 2-38 SSH Tunnel Between the CPA and PDBA Machines
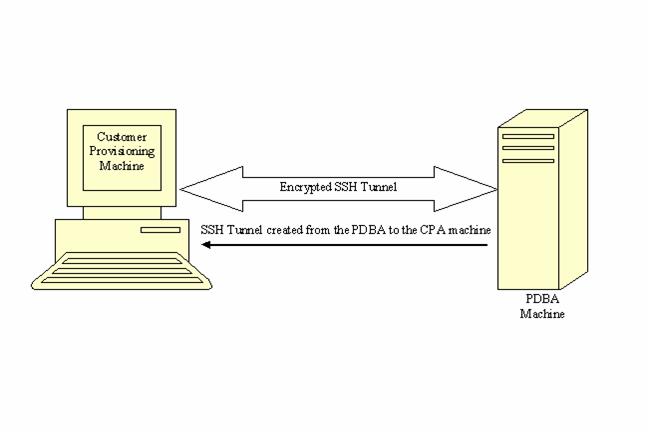
Remote Port Forwarding
Remote Port Forwarding refers to the SSH tunneling approach where the SSH tunnel is created from the client side of the tunnel towards the server side. In the EPAP implementation, the CPA machine is the server and the PDBA machine is the client.
The PDBA machine user specifies a particular port number (configurable from GUI) to be opened on the CPA machine. Any data received on this port on the CPA machine is forwarded to the PDBA machine's IP address and the port number, 5873, through the secured SSH tunnel.
Note:
To implement Remote Port Forwarding to work, the CPA machine must have the OpenSSH suite installed and the SSH daemon must be running.Request/Response Cycle in SSH Tunnel
- When an SSH tunnel is in use, a complete request and response cycle takes place as follows:
- The CPA sends a connect request to its local port number used for creating the tunnel.
- The SSH encrypts the request message and sends it to the PDBA machine's SSH client port.
- On the PDBA machine, the SSH client decrypts the message and forwards it to the PDBA port.
- The SSH client encrypts the response message and sends it to the SSH port on the CPA machine.
- On the CPA machine, the SSH daemon decrypts the message and forwards it to the CPA. The CPA receives the message unencrypted.
Hardware Requirements
None.
Limitations
This SSH tunneling feature works only for customer provisioning systems with 'Write' permissions. A system with 'Read' permissions is not allowed to use the SSH tunnel with the PDBA machine.
2.195 EPAP Support of EAGLE's ITU Duplicate Point Code (Release 29.0)
Description
The EAGLE's Duplicate Point Code feature allows point codes to be provisioned in the EAGLE using a two character "group code." For example, a point code of 1-1-1 could be provisioned 1-1-1-ab, where 1-1-1 is the true point code and ab is the group code. This allows the EAGLE to route between two nodes that have the same true point code. The EAGLE distinguishes between the two by the group code. The group code is only used internally to the EAGLE, and is assigned to an incoming message based on the linkset on which it was received.
Currently, the PDBI (Provisioning Database Interface) does not support entering point code with a group code. This presents a problem for some customers running the DPC feature and either G-Flex, G-Port, or INP.
The EPAP Support of EAGLE’s ITU Duplicate Point Code feature allows group codes to be entered for Network Entity (i.e. SP or RN) point codes via the PDBI.
The following components are affected by this feature:
-
Provisioning Database Interface. Messages related to Network Entity update, create and retrieve will have new optional name value pair called gc for group code.
-
Provisioning Database. EPAP database schema will change. New element gc for group code will be added
-
Provisioning Database Application. Parsing routines will change to accommodate group code.
-
PDBA-RTDB interface will change to accommodate new group code parameter.
-
Real Time Database. Parsing and storing of new data
-
EPAP User Interface PDB Network Entity screens will add new group code field.
-
EPAP 1.0/2.0 to 3.0 data base migration
Hardware Requirements
No new hardware is needed to support this feature.
Upgrade Considerations
Seamless database upgrade (Versant utility sch2db) path from EPAP 2.0 to 3.0 will be used if possible; otherwise, database migration procedure shall be provided. Migration procedure will not take more than 10 minutes with maximum of 50K entries in Network Entity class.
Limitations
This feature extends, and is dependent upon, EAGLE's ITU DPC feature.
2.196 EPAP Update Validation (EPAP 7.0)
Description
The EPAP Update Validation feature provides additional data checks (checksums) before applying updates from the EPAP RTDB to the DSM RTDB.
These additional checks are designed to prevent overwriting of existing data records with new data records when operators are provisioning new subscribers.
When update validation is triggered, the DSM card goes DB-DIFF not incoherent. DB-DIFF requires a reload of the DSM card. However, the DSM card will continue to process traffic until it is reloaded.
A checksum of the data about to be overwritten is compared with the old checksum (new data element) in the update about to be applied as well as the existing memory location check. If the checksums and location do not match, the update will not be applied to the DSM RTDB and the DSM will go incoherent.
To use this feature, the EAGLE 5 ISS will first need to be upgraded to Release 34.0.4. The DSM cards will continue to accept and process update records from the EPAP that do not contain the update validation information. After the EAGLE 5 ISS is upgraded, the respective EPAP is upgraded to provide the update validation information. The DSM cards will provide information to the EPAP that details whether or not it can accept and process update validation information (based on the EAGLE 5 ISS software level) from the EPAP.
2.197 EPAP with TPD 1.1 (Release 31.6)
MPS now uses Tekelec Platform Distribution (TPD) Release 1.1, which offers the following improvements over TPD Release 1.0:
-
An additional diagnostic service,
smartd, has been added. Thesmartdservice reads status information from the disk (produced according to the S.M.A.R.T. standard) and reports that status through thesyscheckutility. The standard S.M.A.R.T. (Self-Monitoring, Analysis and Reporting Technology) technology is implemented into all modern hard disks. According to this standard, a special program inside the disk constantly tracks the condition of a number of the vital parameters, such as driver, disk heads, surface state, electronics, etc. At the present time, S.M.A.R.T. technology is able to predict up to 70% of all hard disk problems. -
Various changes that make the platform easier for the EPAP application to use (these changes do not result in changes that are noticeable by the user).
2.198 EPAP/ELAP 2.0 Security and UI Enhancements (Release 28.0)
Description
This feature allows the customer to access ELAP and EPAP functionality from any computer workstation capable of supporting an Intranet connection and Microsoft's Internet Explorer 4 browser. This feature does not change major ELAP/EPAP functionality. It does, however, provide Client/Server architecture and a new menu interface to that functionality.
This feature provides a new user interface and presents no impact to the EAGLE. The old text-based UI is available for provisioning purposes.
For more information on the EPAP/ELAP Security and UI Enhancements, refer to the EPAP Administration Manual or the ELAP Administration Manual, and the Maintenance Manual.
Hardware Requirements
Customers need a PC that can connect to the LAN/WAN.
2.199 EPM-B Based Cards(Release 44.0)
A new Embedded Processor Module (EPM) is introduced. This module is referred to as the EPM-B and has a Part Number of 850-2037-01.
A series of new cards that run on the EPM-B is introduced. These cards are known collectively as EPM-B based cards and are discussed individually in their associated sections:
The EPM-B based cards are single slot cards with dual core processors.
2.199.1 Hardware Requirements
- Fan trays must be installed on shelves that contain EPM-B based cards.
- The IMT bus must contain at least one HIPR or HIPR2 card before an EPM-B based card can connect with the bus. If HMUX cards are used, then the cards cannot access the IMT bus. If the shelf contains both HMUX and HIPR/HIPR2 cards, then the EPM-B based card connects with the HIPR/HIPR2 cards only.
Note:
HMUX cards with HIPR/HIPR2 cards on the same shelf are supported only during migration to the EPM-B based cards. - Dual 60A power feeds are recommended for all frames that host EPM-B based cards. EAGLE 5 frames that host EPM-B cards may require dual 60 Amp power feeds, depending on frame configuration.
- The BLMCAP GPL must be flashed on EPM-B based cards before the card can be initialized.
2.200 Equipment Identity Register (EIR) (Release 31.0)
This feature is intended to reduce the number of GSM mobile handset thefts by providing a mechanism that allows the network operators to prevent stolen or disallowed handsets from accessing the network. This control is done by using the International Mobile Equipment Identity (IMEI) provided during handset registration and comparing it against a set of lists provided by the network operator. There are three lists: Black, Gray and White. Mobile Stations (MS) on the white list are allowed access to the network. MSs on the black list are denied access to the network. MS’s on the gray list are allowed on the network, but are logged.
This feature meets the mandate of European countries to provide EIR functionality by providing the network operators the ability to prevent stolen handsets from accessing their networks.
2.201 Error Message Reporting Enhancement (Release 21.0)
Before Release 21.0, the global title and gateway screening functions display a single error (unsolicited alarm message - UAM). This does not show all of the global title and gateway screening error messages that occur.
This feature allows more information about global title and gateway screening error messages to be reported to the user.
The number of global title error messages and gateway screening error messages displayed is increased to 5 messages/second/card. Each card can report up to 8 messages per second to the system. Any global title error messages and gateway screening error messages generated beyond the 8 messages/second/card rate are discarded, with the newest messages discarded first. Low priority messages are discarded when the transport buffer is full (8 total messages). High priority messages are discarded when the transport buffer is completely full with high priority messages.
2.202 Ethernet B Interface for IPGWx and IPLIMx (Release 28.1, IP7 Release 6.0)
Description
This feature activates the second Ethernet Interface (the B Interface) on the SSEDCM card types. This allows IP connection-oriented transports, such as TALI sockets and IETF SCTP associations, to utilize either of the card’s Ethernet A or B Interfaces when forming a connection. This feature provides direct access to two separate LANs, effectively doubling the connectivity of each SSEDCM card.
As part of this feature's implementation, multiple static IP routes are permitted for SSEDCM card types. Each unique static route can be configured to use a different gateway router to reach remote destinations. This provides the capability to utilize more network paths for IP connection-oriented transports to access remote IP networks.
The addition of Static IP Routes enables IP connection-oriented transports to be accessible through gateways other than the default router. By providing access to a greater number of IP gateways, more destinations can be reached in a more efficient manner. Also, more time efficient IP connections can be utilized.
Doubling the connectivity to local networks and providing a more diversified access to remote networks greatly increases the flexibility of the IP7 Secure Gateway and EAGLE STP. Enabling each SSEDCM card to directly access two Local Area Networks allows the arrangement of co-located IP7 SG's/EAGLEs in ways to provide a higher level of redundancy.
Allowing the SSEDCM to be used as a multi-homing host also allows the SCTP protocol to utilize the protocol's multi-homing capability and provide support for local association endpoints that are multi-homed. SCTP multi-homed endpoints are endpoints that may use both Ethernet interface A and B for SCTP connectivity. This SCTP protocol capability provides for SCTP connections to be established that are more reliable and robust than TCP socket connections.
Hardware Requirements
This feature is intended for SSEDCM cards. The assignment of IP7 connection-oriented transports to the Ethernet B Interface on DCM cards is not permitted.
Limitations
Limitations for the Ethernet B Interface for IPGWx / IPLIMx feature are listed below.
-
Only one default router can be assigned per card.
-
SSEDCM cards will act as follows:
-
uni-homing on the Ethernet A interface,
-
uni-homing on the Ethernet B interface, and
-
multi-homing on the Ethernet A and B interfaces.
-
-
A finite number of static IP routes per card exists; the limit is 50 per card per EAGLE.
-
There are per card and per system limits on the maximum number of static IP routes supported.
-
a maximum of 64 static IP routes per IPGWx / IPLIMx card, and
-
a maximum of 1024 static IP routes per system.
-
-
No additional database validations will be performed on upgrade.
-
No increased in load performance is provided.
-
Static IP routes can lead to unreachable hosts.
2.203 Expanded Terminal Output Groups (Release 31.3)
The output groups currently defined by the EAGLE allow the messages generated by the system to be selectively displayed on the various terminals connected to the EAGLE. The expansion adds 12 new output groups and reassigns messages from existing groups to be used exclusively for controlling the output destination of all UAMs and UIMs. Upgrade automatically assigns messages to the correct groups.
The upgrade will automatically change existing groups to the new groups and additional output may be seen post upgrade depending on which groups are activated.
2.204 Extended Bus Interface (Release 20.0)
Every two card locations, except for card locations 9 and 10 in all shelves, and 17 and 18 in the control shelf (1117 and 1118), are connected together through the shelf backplane by an extended bus interface (EBI). The EBI is a local bus and not connected to the IMT bus. This allows every two card locations to communicate with each other without going over the IMT bus. The MCAP card and the TDM are connected to each other through the EBI to form the MASP. This also eliminates the 10 Mb/s ethernet LANs with their outboard MAU units that connected the MCMs and PSMs in the EAGLE STP/1 MAS.
2.205 Extended EPAP DN Block Capacity (EPAP 16.0)
The EPAP DN Block capacity is extended from 100,000 ranges to 200,000 ranges. A new table is added to support this capacity increase.
2.206 Extension Shelf Backplane (Release 23.0)
A new extension shelf backplane has been introduced in Release 23.0 with these changes:
-
The extension shelf backplane now contains four -48VDC power and ground connections (DB-26 connectors). Two of these connectors are labeled A1 and B1 and are connected to the fuse and alarm panel. The other two are labeled A2 and B2 and are connected to another power source, allowing the EAGLE to remain in service when replacing the fuse and alarm panel.
-
The shelf address of the extension shelves has been expanded from four bits to six bits, increasing the number of addressable extension shelves from 15 to 64 and increasing the maximum number of addressable card slots from 250, or 500 signaling links, to a theoretical limit of 1018, or 2036 signaling links. The actual number of addressable card slots is limited by the system software and the hardware configuration of the EAGLE. In Release 23.0, the actual number of addressable card slots is 378, or 756 signaling links, but is limited by the system software to 250 cards, or 500 signaling links.
-
To enable the cards in the extension shelf to select one of two different types of IPMX cards that could be in the extension shelf, pin D53 of connector P9 transmits signal ABMUXIN- to pin D26 on connectors P1 to P8 and P10 to P17, and pin D53 of connector P26 transmits signal BBMUXIN- to pin D27 on connectors P18 to P25 and P27 to P34.