3 Downloading and Installing Oracle Key Vault
You must download the Oracle Key Vault application software, and then you can install or upgrade Oracle Key Vault.
- Downloading the Oracle Key Vault Software for Fresh Installation
To install Oracle Key Vault, download the Oracle Key Vault appliance software from Oracle Software Delivery Cloud. - Downloading the Oracle Key Vault Software for Upgrade
Perform the following steps to upgrade Oracle Key Vault. - Installing the Oracle Key Vault Appliance Software
The Oracle Key Vault installation process installs all the required software components onto a dedicated server or virtual machine. - Performing Post-Installation Tasks
After you install Oracle Key Vault, you must complete a set of post-installation tasks.
3.1 Downloading the Oracle Key Vault Software for Fresh Installation
To install Oracle Key Vault, download the Oracle Key Vault appliance software from Oracle Software Delivery Cloud.
Parent topic: Downloading and Installing Oracle Key Vault
3.2 Downloading the Oracle Key Vault Software for Upgrade
Perform the following steps to upgrade Oracle Key Vault.
Parent topic: Downloading and Installing Oracle Key Vault
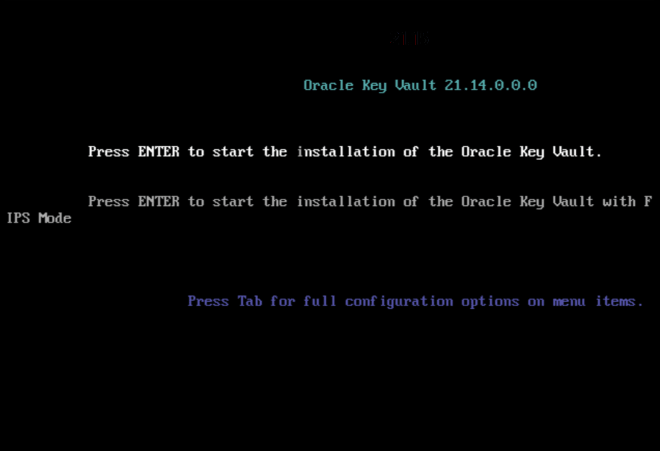
3.3 Installing the Oracle Key Vault Appliance Software
The Oracle Key Vault installation process installs all the required software components onto a dedicated server or virtual machine.
If you are installing Oracle Key Vault on VMware, then set the VMX configuration parameter disk.EnableUUID to TRUE. In addition, you must set your virtual machine to use EFI boot. In some versions of VMware this is done by selecting the VM Options tab, then expanding Boot Options, and then setting the firmware to EFI. You must disable secure boot. Without this setting, the Oracle Key Vault installation on VMware will fail.
Caution:
The Oracle Key Vault installation wipes the server, repartitions the disk, and installs a hardened Oracle Linux 8. The installation erases existing software and data on the server.
Ensure that you meet the following prerequisites.
-
Ensure that the server meets the recommended requirements.
-
Request a fixed IP address, network mask, and gateway address from your network administrator. You will need this information to configure the network.
To install the Oracle Key Vault appliance:
- Requirements for root and support User Passwords
Ensure that you meet these requirements forrootandsupportuser passwords.
Related Topics
Parent topic: Downloading and Installing Oracle Key Vault
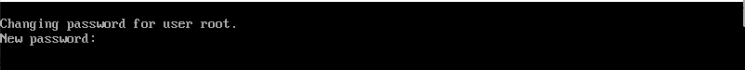
3.3.1 Requirements for root and support User Passwords
Ensure that you meet these requirements for root and
support user passwords.
- The password must have at least 15 characters.
- The password must contain at least one uppercase letter, one lowercase letter, one digit, and one special character.
- The same character cannot repeat consecutively more than 3 times in the password.
- Characters from the same class cannot repeat consecutively more than 4 times in the password. For example, more than 4 lowercase letters in a row.
- The new password must have at least 8 characters that are different from the old password.
Parent topic: Installing the Oracle Key Vault Appliance Software
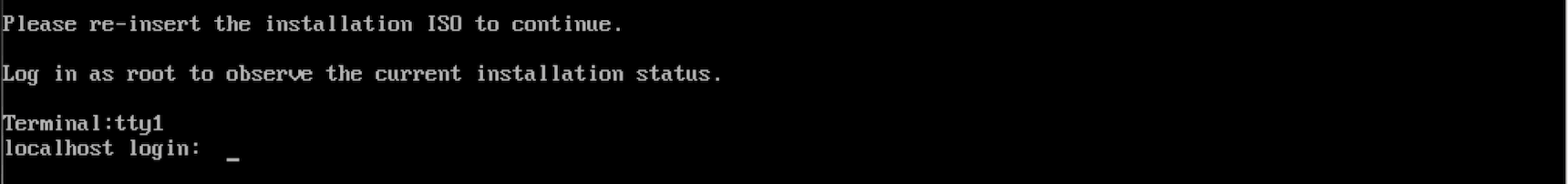
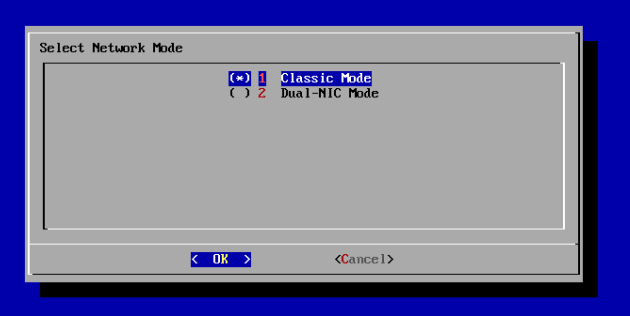
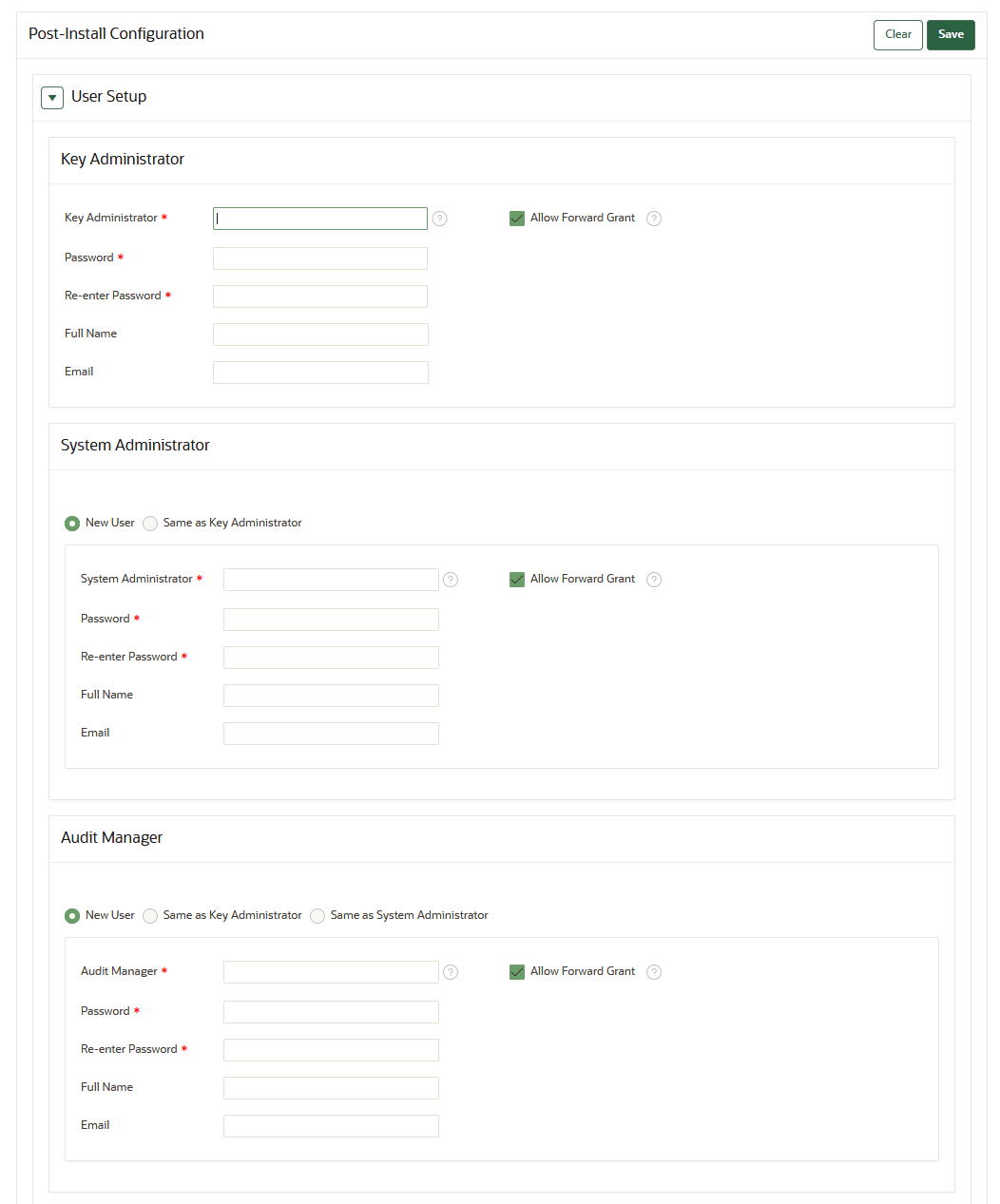
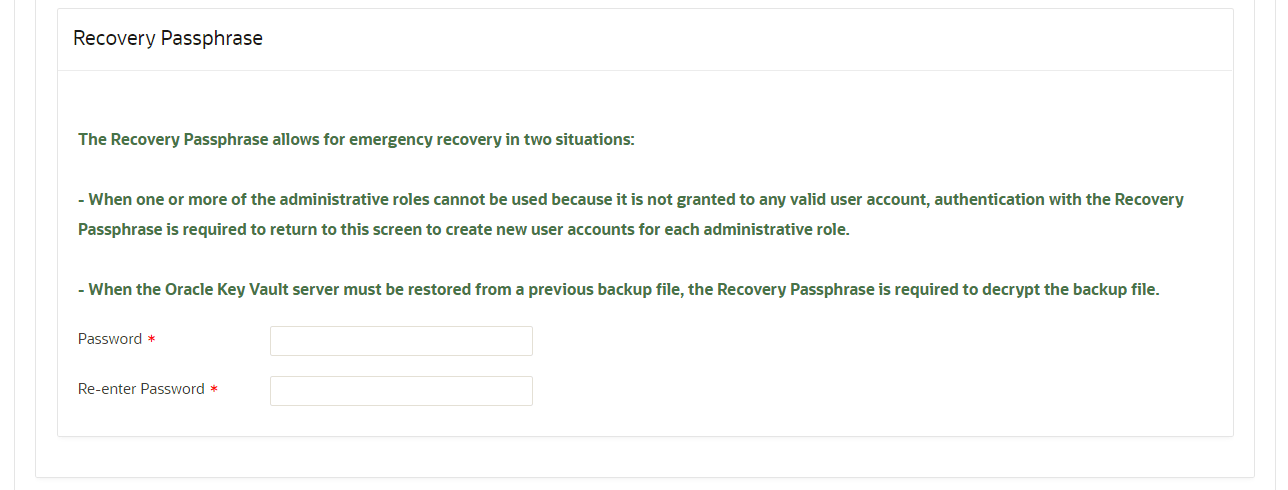
3.4 Performing Post-Installation Tasks
After you install Oracle Key Vault, you must complete a set of post-installation tasks.
These tasks include configuring the administrative user accounts and their one-time passwords, the recovery passphrase, as well as DNS and NTP settings.
Related Topics
Parent topic: Downloading and Installing Oracle Key Vault