Set Up Oracle SOA Suite to Use CA-Verified SSL Certificates (without load balancer)
You can replace the identity and trust of Oracle SOA Suite with custom identity and custom trust and register the Oracle SOA Suite server with digital certificates procured from public certificate authorities like digicert or any other third party authority.
As a prerequisite, register Oracle SOA Suite domain
with the public DNS for CA verification. For the documentation purposes, the public
IP of the Oracle SOA Suite domain is registered
with mydomain.com and takes the CA signed certificates from
mydomain.
The Enterprise Manager (EM) console needs to be accessible using the public domain name.
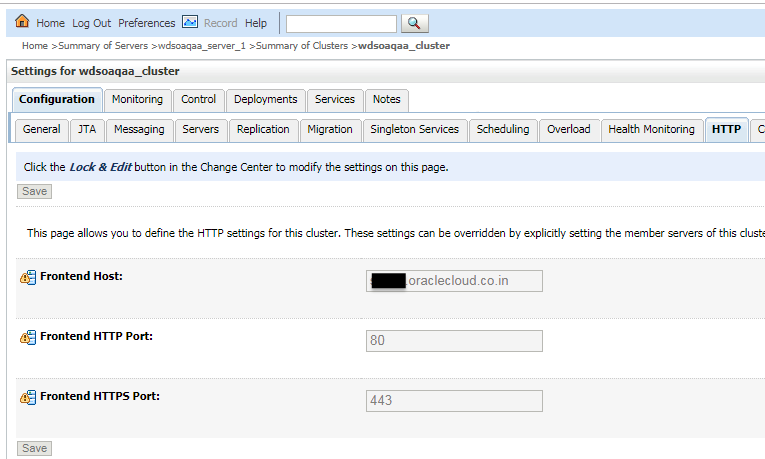
Register a Domain Name for Oracle SOA Suite
To register a domain name for Oracle SOA Suite:
- Register a domain for Oracle SOA Suite
server with a public DNS server. You can register
your domain with any public DNS Server of your
choice, mapping it to the public IP of Oracle SOA Suite. For
example register
soacs.oraclecloud.co.indomain inmydomain.com, mapping to the public IP of Oracle SOA Suite server. - Test access to the Enterprise Manager (EM) Console and the WebLogic Server Console through the domain name registered.
Create Custom Identity and Custom Trust Keystores and Generate a CSR
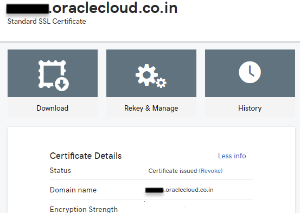
Share the CSR with CA to Get CA-Signed Certificates
To share the CSR with CA to get CA-signed certificates:
Import CA Certificates
Certificate Authority (CA) certificates must be imported in the following order: first the signed server certificate, then the intermediate certificate, and then the root certificate.
To import CA certificates:
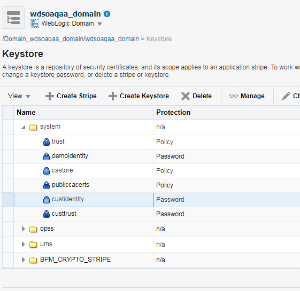
Synchronize the Local Keystore with the Security Store
Synchronize keystores to synchronize information between the domain home and the Oracle Platform Security Services (OPSS) store in the database.
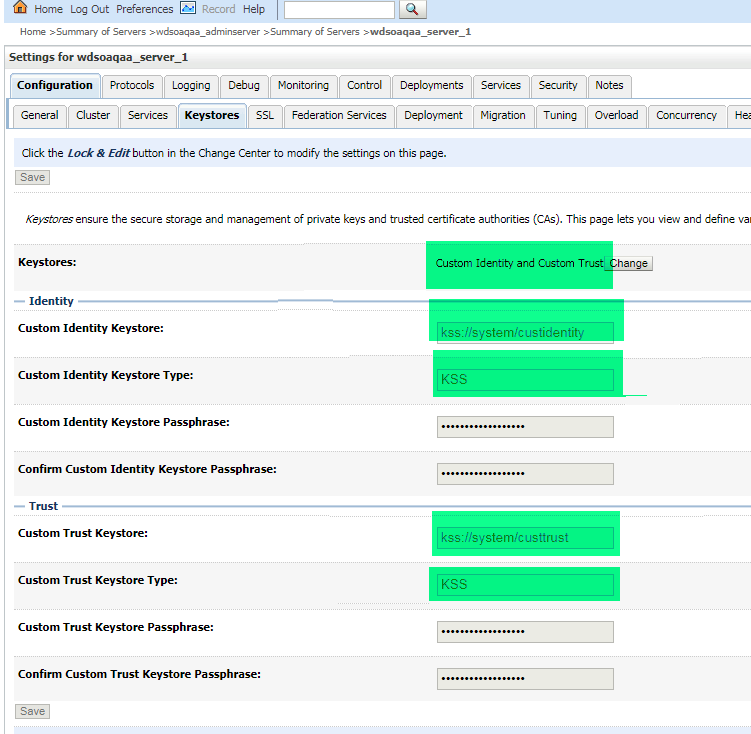
To synchronize keystores:Update WebLogic Keystores with Custom Identity and Trust
Update the Node Manager and boot.properties File
boot.properties
file:
The JAVA_OPTIONS for a 12.2.1.4 environment is as follows: JAVA_OPTIONS="${JAVA_OPTIONS}
-Doracle.security.jps.config=/u01/data/domains/TPLSOADE_domain/config/fmwconfig/jps-config-jse.xml
-Dcommon.components.home=/u01/app/oracle/middleware/oracle_common -Dopss.version=12.2.1.2
-Dweblogic.nodemanager.sslHostNameVerificationEnabled=false -Djava.security.egd=file:/dev/./urandom"
Verify the Environment
When you restart the environment, the Aministration Server and Managed Server user interface shows the certificates as trusted:
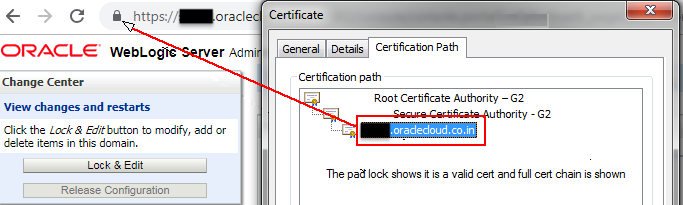
Description of the illustration verify_environment.png
To verify the environment:
-
Deploy a HelloWorld composite and verify that the client endpoint URL can be opened on https host and port.
The valid certificate chain is present on the client endpoint URL:
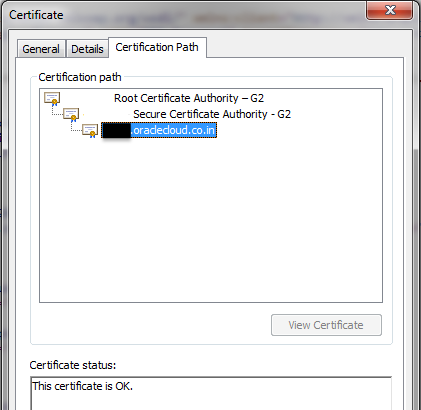
Description of the illustration verify_certificate.png -
To invoke the client end point from any other composite, import all the certificates (signed server, intermediate, and root) present in the WSDL into the truststore of the server from where the parent composite is deployed.