1 Oracle SDM Cloud Security Overview
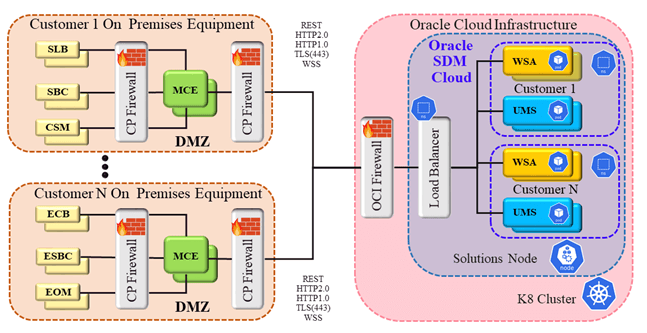
Oracle® Session Delivery Management Cloud (Oracle SDM Cloud) is a service to manage and monitor Oracle Session Delivery portfolio products residing on customer premises. The management and intelligence needed to provide this offering is maintained in the Oracle SDM Cloud micro-services hosted on the Oracle Cloud Infrastructure. For a Network Function (NF) to communicate with the Oracle SDM Cloud, the Management Cloud Engine (MCE) component must be installed on the customer premises.
The MCE component, once installed and started, registers with Oracle SDM Cloud and establishes a bi-directional web socket channel with Oracle SDM Cloud. MCE acts primarily as a protocol converter to allow REST communication to cloud to be converted to legacy protocols that the NF understand.
In the following high-level diagram of an Oracle SDM Cloud deployment integrated with the MCE, the MCE resides on premises, while the Oracle SDM Cloud micro-services reside in the Cloud.
Oracle deploys the Oracle SDM Cloud in the Oracle Cloud Native Environment, a highly secured Platform as a Service (PaaS) environment in the Oracle Cloud Infrastructure (OCI). As a result, the Oracle SDM Cloud Software as a Service (SaaS) can provide a highly secured Cloud service. The Oracle SDM Cloud solution provides high quality, highly secure Podman images for the MCE. The MCE are deployed in the customer network running on customer’s platforms (Operating Systems, file systems). Such a deployment model makes security a joint effort between the customer and Oracle to ensure that the MCE runs in a secured environment. Oracle recommends that the customer ensure that their Operating System is securely hardened and that access to the customer’s Operating System where the MCE runs is well managed. Unauthorized access to the MCE environments can lead to exposure of the configuration. Oracle recommends the user reserve proper resources such as memory, CPU, and network bandwidth for the MCE. For more information on these resources, see the Oracle SDM Cloud Getting Started Guide.
The Oracle SDM Cloud CI and CD pipeline routinely rotate client secrets for enhanced security operations. All logs, including security logs, are collected and monitored in a centralized application to detect any security violation in time.
Oracle recommends deploying the MCE in your DMZ because the MCE needs to reach out to Oracle SDM Cloud micro services (bidirectional) and IDCS for authentication. The MCE also communicates with the Session Delivery NF portfolio. It is likely that security gateways (or firewalls) are deployed before DMZs in private networks, which means that you need to configure gateways properly to allow traffic to the MCE. The MCE installation documents list the default ports, which you can modify. The port configuration is needed to configure security gateways.
For information about securing the Oracle® Session Delivery products, see the Oracle Communications Session Border Controller Security Guide.
Traffic Flow and Firewall Port Recommendations
The following table provides traffic flow and firewall port recommendations for all Oracle® Session Delivery Management Cloud (Oracle SDM Cloud) components. All components use TCP and HTTPS.
| Component | FQDN/IP | Port | Component Interface | Port | Notes | Communication Flow |
|---|---|---|---|---|---|---|
| IDCS | idcs-<Tenant Slice> .identity.oraclecloud.com | 443 | MCE WAN | * | MCE initiates TLS connections to IDCS | Ground-to-Cloud |
| Oracle SDM Cloud Load Balancer | osdmc.<region>.ocs.oraclecloud.com | 443 | MCE WAN | * | MCE initiates TLS connections to Oracle SDM Cloud load balancer using the Oracle SDM Cloud FQDN | Ground-to-Cloud |
MCE Defaults
The Management Cloud Engine (MCE) server port, 7070, is hardcoded in a properties file and not configurable using the setup script. To change the value, you must manually edit the properties file.
- TRAP Receiver: 162
The TRAP receiver port value, 162. can be changed using the setup script.
Validate Connectivity
- From Management Cloud Engine (MCE) to
IDCS
curl -i --noproxy "*" -X POST -u "<MCE IDCS client ID>:<MCE IDCS client secret>" -c "grant_type=client_credentials&scope=osdmc:premtocloud" <IDCS_FQDN>/oauth2/v1/token
- From MCE to
LB
curl -kvL4 --noproxy "*" https://osdmc.us-ashburn-1.ocs.oraclecloud.com:443
Accessing the Application
Oracle's Identity Cloud Service (IDCS) supports federation/SSO external authentication, with many different Identity Providers (IDP)s. For more information, see https://docs.cloud.oracle.com/en-us/iaas/Content/Identity/Concepts/federation.htm.