Multi-system Selective SRTP Pass-through
Prior to Release S-CX6.3F1, Oracle Communications Session Border Controller provided a single Secure Real-time Transport Protocol (SRTP) operational mode, referred to as SRTP Media Proxy Mode. In this original processing mode, each Oracle Communications Session Border Controller in the SRTP media path served as a proxy for the media — always decrypting inbound traffic, and encrypting outbound traffic.
Release S-CX6.3F1 introduces support for a new, alternative processing mode, referred to as Multi-system Selective SRTP Pass-through Mode. In this new mode encryption and decryption of SRTP media is handled by the SRTP endpoints, the calling and called parties. Off-load of the processor-intensive encryption/decryption provides the Oracle Communications Session Border Controller with the ability to handle a larger number of simultaneous SRTP sessions.
Note:
hair-pinned calls are those calls where the calling and called parties are within the same realm and/or within the same sub-network.Operational Overview
To set up Multi-system Selective SRTP Pass-through, the ingress and egress Oracle Communications Session Border Controllers (which can, in fact, be a single Oracle Communications Session Border Controller) exchange the SDES keying material that they receive from their respective endpoint so that the Oracle Communications Session Border Controller peer can pass the material to its adjacent endpoint. The endpoint to endpoint exchange of keying material enables the endpoints themselves to generate encryption/decryption keys.
The actual exchange of keying material takes place in SIP messages (specifically, INVITE, 200 OK, and ACK) that carry offer or answer SDPs. Encrypted keying material is conveyed within a media attribute for each SRTP session. The name of the media attribute is configurable.
When either Oracle Communications Session Border Controller receives the encrypted keying material sent by its remote peer, it decrypts the media attribute and passes the plaintext attribute to its endpoint. Consequently, subsequent SRTP packets from the endpoints pass through the Oracle Communications Session Border Controllers without being decrypted and encrypted because both endpoints (now is possession of each others keying material) are able to decrypt the SRTP packets received from the other.
Call Flows
The following three sections describe call signalling for common scenarios.
Call Setup
A: The calling party sends an INVITE with SDP to SBC-A. The offer SDP contains an SDES crypto attribute within the SRTP media line.
B: Since Multi-system Selective SRTP Pass-through is enabled within the ingress realm, SD-A adds an a=X-acme-srtp-msm media attribute. The a=X-acme-srtp-msm attribute contains a cookie that includes an encryption of the SDES crypto attribute present in the SDP. The encryption is done using the shared secret configured for encrypting SRTP Pass-through information.
C: SBC-B receives the offer SDP that has the cookie sent by SBC-A. It is assumed that the proxies that forward the offer SDP sent by SBC-A preserve and forward the cookie added by SBC-A.
D: SBC-B checks if the egress realm has Multi-system Selective SRTP Pass-through enabled. If so, SBC-B decrypts the cookie using the shared secret to retrieve the SDES crypto attribute. SBC-B adds the SDES crypto attribute retrieved from the cookie to the offer SDP sent to UA-B.
E: The called party sends an answer SDP with a SDES crypto attribute on the SRTP media line to SBC-B.
F: SBC-B checks if it has received a cookie in the offer SDP and adds the cookie to the answer SDP. The cookie contains an encryption of the SDES crypto attribute received in the answer SDP from UA-B. SBC-B does not install any SA or media policy so that SRTP packets from/to UA-B can pass through SBC-B without any decryption/encryption.
G: SBC-A receives the answer SDP that has the cookie sent by SBC-B.
H: SBC-A decrypts the cookie using the shared secret to retrieve the SDES crypto attribute. SBC-A adds the SDES crypto attribute retrieved from the cookie to the answer SDP. SBC-A does not install any SA or media policy so that SRTP packets from/to UA-A can pass through SBC-A without any decryption/encryption.
Music on Hold
After a call is established, one of the endpoints can put the other endpoint on hold. An application server might intercept the re-INVITE from one endpoint (for putting the other on hold) and implement MoH as follows.
A: Endpoint UA-A sends an offer SDP for hold to SBC-A.
B: SBC-A forwards offer SDP without any cookie since there will be no media going from/to UA-A.
C: SBC-B receives an offer SDP that is addressed to the MS without any cookie.
D: Because there is no cookie in the ingress offer SDP, SD-B generates its own SDES crypto attributes for the egress offer SDP sent to UA-B.
E: SBC-B receives am answer SDP from UA-B.
F: SBC-B sends its answer SDP without any cookie and encrypts SRTP packets going to UA-B. Note that there will be no SRTP packets going from UA-B to SBC-B.
As a result, MoH is heard by UA-B as it decrypts SRTP packets encrypted by SBC-B. When UA-A resumes, the steps to establish media between UA-A and UA-B will be the same as the steps used for call setup.
Once the media is reestablished between UA-A and UA-B media travelling between the two UAs will not be decrypted by either SBC.
Call Transfer
A call transfer can also happen after a call is established. For example, endpoint UA-B can transfer UA-A to another endpoint, UA-C. UA-B can make a blind transfer or an attended transfer. The following diagram describes a blind call transfer with SRTP Pass-through enabled. Note it does not show the SIP message exchange between UA-B and the Application Server to facilitate the call transfer (i.e. the INVITE from UA-B to put the call on hold and the REFER/NOTIFY message exchange between UA-B and the Application Server). After UA-A is put on hold and the transfer target (that is, UA-C) is received from UA-B, the Application Server attempts to establish a call to UA-C. After the call to UA-C is established, the Application Server takes UA-A off hold and connects its media session to that of UA-C.
A: SBC-B receives an INVITE (from the Application Server to invite UA-C) without an offer SDP.
B: SBC-B sends an INVITE without an offer SDP to UA-C.
C: SBC-B receives a 200 OK response with an offer SDP that has a SDES crypto attribute on the SRTP media line from UA-C.
D: Since Multi-system Selective SRTP Pass-through is enabled within the ingress realm, SBC-B adds a cookie to the egress offer SDP that is sent to the core realm.
E: SBC-A receives a re-INVITE to UA-A with the offer SDP that has the cookie sent by SBC-B.
F: Since Multi-system Selective SRTP Pass-through is enabled within the ingress realm, SBC-A adds the SDES crypto attribute retrieved from the cookie to the offer SDP sent to UA-A.
G: SBC-A receives an answer SDP that has a SDES crypto attribute on the SRTP media line from UA-A.
H: SBC-A checks if it has a cookie in the offer SDP and adds the cookie to the answer SDP that is sent to the core realm. The cookie contains an encryption of the SDES crypto attribute received in the answer SDP from UA-B. SBC-A stops the encryption of any SRTP packets going to UA-B (set up for MoH) so that SRTP packets from/to UA-B can now pass through SBC-A without any decryption/encryption.
I: SBC-B receives the answer SDP that has the cookie sent by SBC-A.
H: SBC-B decrypts the cookie using the shared secret to retrieve the SDES crypto attribute. SBC-B adds the SDES crypto attribute retrieved from the cookie to the answer SDP.
After the call to UA-C is established and the call to UA-A is resumed (with the resulted media going between UA-A and UA-C) the Application Server disconnects the call with UA-A. Note that steps C-J are essentially the same steps as steps A-H in the Call Setup example. The difference is that the offer SDP from C comes to SD-B in a 200 OK response and the answer SDP sent by SBC-B to C is in the ACK.
Early Media
Different application servers may implement early media in different ways. In general, the SBC supports early media in the following way.
If the SBC receives an SDP without any cookie in a provisional response, the SBC generates its own SRTP crypto context and exchanges it with the caller via the SDP included in the provisional response. The SBC continues to decrypt and encrypt early media packets going to and from the caller. The SBC stops decrypting and encrypting only if it receives a final response with an answer SDP that signals that SRTP Pass-through should be enabled.
Multi-system Selective SRTP Pass-through with Media Release
When SRTP Pass-through is allowed, the hair-pinned media can also be released to the network if media release is configured — that is, if realm-config parameters msm-release is enabled, mm-in-realm is disabled, or mm-in-network is disabled. If SRTP Pass-through is not allowed, media release will not be allowed either.
Multi-system Selective SRTP Pass-through Configuration
Use the following procedure to enable Multi-system Selective SRTP Pass-through within a specific realm.
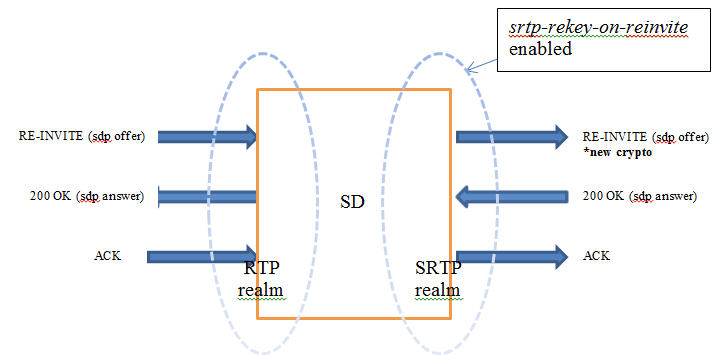
SRTP Re-keying
Initialization of SRTP re-keying is supported by the Oracle Communications Session Border Controller.
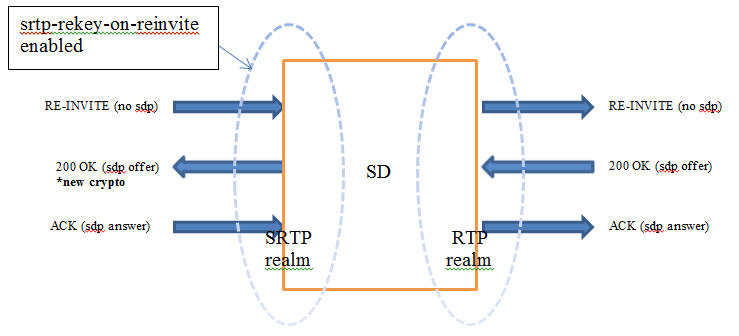
The Oracle Communications Session Border Controller can generate a new outbound crypto attribute in the SDP offer in a SIP re-INVITE when the srtp-rekey-on-reinvite parameter is set to enabled. The system generates the attribute regardless of the state of the flow, active or not.
This capability is important for some clients that reside on the SRTP side in a single SRTP termination mode configuration. Any media changes that happen in the RTP side are hidden by the Oracle Communications Session Border Controller. This concealment may cause issues in some configurations, where media servers are involved. When the media changes from media server to called phone, the SRTP endpoint is not aware the media source changed because the SDP offer from the Oracle Communications Session Border Controller is the same as original invite. The result is that some devices drop packets because of Synchronization Source Identifier (SSRC) values mismatch, unexpected jumps in sequence number, sequence number reversions back to 1 triggering replay attack defense, and so forth. In certain environment is has been found that re-keying on every re-invite eliminates all these issues especially in customer setups that use Microsoft Lync products.
The processing of standard RE-INVITES (those containing an SDP offer) and offerless RE-INVITES is shown below.
With SDP:
No SDP:
If the re-invite message is a refresh and srtp-rekey-on-reinvite is enabled, the outbound crypto will change but the SDP version will not be incremented on the outgoing invite. If this scenario causes incompatibility issues with customer equipment then add the unique-sdp-id option to media-manager, option configuration so the Oracle Communications Session Border Controller increments the SDP version in the outgoing invite.