DNS ALG
The Oracle Communications Session Border Controller’s DNS Application Layer Gateway (ALG) feature provides an application layer gateway for DNS transactions on the Oracle Communications Session Border Controller. With DNS ALG service configured, the Oracle Communications Session Border Controller can support the appearance of multiple DNS servers on one side and a single DNS client on the other.
Overview
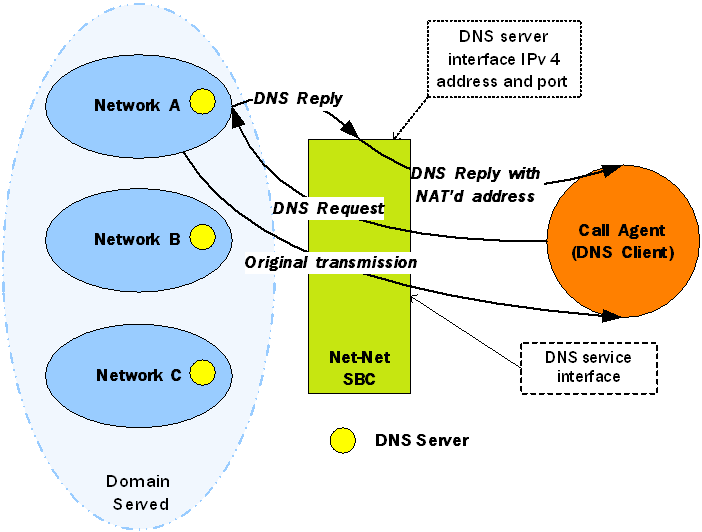
DNS ALG service provides an application layer gateway for use with DNS clients. DNS ALG service allows a client to access multiple DNS servers in different networks and provides routing to/from those servers. It also supports flexible address translation of the DNS query/response packets. These functions allow the DNS client to query many different domains from a single DNS server instance on the client side of the network.
The Oracle Communications Session Border Controller’s DNS ALG service is commonly used when a DNS client (such as a call agent) needs to authenticate users. In this case, the DNS client that received a message from a certain network would need to authenticate the endpoint in a remote network. Since the DNS client and the sender of the message are on different networks, the Oracle Communications Session Border Controller acts as an intermediary by interoperating with both.
In the following diagram, the DNS client has received a message from an endpoint in Network A. Since the DNS client is in a different realm, however, the DNS client receives the message after the Oracle Communications Session Border Controller has performed address translation. Then the DNS client initiates a DNS query on the translated address. The Oracle Communications Session Border Controller forwards the DNS request to the DNS server in Network A, using the domain suffix to find the appropriate server. Network A’s DNS server returns a response containing its IPv4 address, and then the Oracle Communications Session Border Controller takes that reply and performs a NAT on the private address. The private address is turned into a public one that the DNS client can use to authenticate the endpoint.
Configuring DNS ALG Service
This section tells you how to access and set the values you need depending on the configuration mechanism you choose. It also provides sample configurations for your reference.
Configuring DNS ALG service requires that you carry out two main procedures:
- Setting the name, realm, and DNS service IP interfaces
- Setting the appropriate parameters for DNS servers to use in other realms
Before You Configure
Before you begin to configure DNS ALG service on the Oracle Communications Session Border Controller, complete the following steps.
- Configure the client realm that you are going to use in the main DNS ALG profile and note its name to use in this chapter’s configuration process.
- Configure the server realm that contains the DNS servers and note its name to use in this chapter’s configuration process.
- Determine the domain suffixes for the network where the DNS servers are located so that you can enter them in the domain suffix parameter.
- Devise the NAT scheme that you want to use when the DNS reply transits the Oracle Communications Session Border Controller.
DNS ALG Service Name Configuration
This section explains how to configure the name of the DNS ALG service you are configuring and set its realm.
To add DNS ALG service:
DNS Transaction Timeout
To provide resiliency during DNS server failover, you can now enable a transaction timeout for DNS servers. If you have endpoints that are only capable of being configured with a single DNS server, this can allow DNS queries to be sent to the next configured server—even when contacting the Oracle Communications Session Border Controller’s DNS ALG on a single IP address. So when the first server in the list times out, the request is sent to the next server in the list.
The Oracle Communications Session Border Controller uses the transaction timeout value set in the dns-server-attributes configuration (part of the dns-config).
DNS Server Operation States
After the first failed attempt to reach a DNS server, The Oracle Communications Session Border Controller places it in a Time Out state. The server stays in Time Out state for 30 seconds. The Oracle Communications Session Border Controller does not send DNS queries to a server in Time Out state. Instead, it directs queries to the next DNS server in the server-address-list. After 30 seconds, the DNS server goes back to an In Service state and the Oracle Communications Session Border Controller sends queries to it.
If a DNS server fails to respond to 5 consecutive queries, it goes into Out of Service (OOS) state. The Oracle Communications Session Border Controller directs all subsequent queries to the first In Service server. The Oracle Communications Session Border Controller returns OOS DNS servers to In Service state after 600 seconds and repeats the cycle above. If, for any given call, all configured DNS servers are OOS, the Oracle Communications Session Border Controller fails the call.