Understanding Trusted Host Forwarding with P-Asserted-Identity
The P-Asserted-Identity header is honored only within a
trusted domain. In a Converged Application Server system, trusted domains are purely
configuration-based. To enable use of the header, you must configure one of two
available P-Asserted Identity Assertion providers as described in "Configuring a P-Asserted-Identity Assertion Provider". The P-Asserted-Identity assertion
providers expose the trusted domain configuration for
P-Asserted-Identity headers. If you do not configure a provider,
the header considers no IP addresses as being “trusted."
When Converged Application Server receives a message having the
P-Asserted-Identity header from a trusted host configured with the
provider, it logs in the user specified in the header to determine group membership and
other privileges. The value contained in the P-Asserted-Identity header
must be a SIP address (for example, sipuser@oracle.com). By default,
Converged Application Server removes the domain portion of the address
(@oracle.com) and uses the remainder as the user name. If you must
support overlapping usernames from different names (for example,
sipuser@oracle.com and sipuser@cea.com), you can
create and use a custom user-name mapper to process the header contents into a unique
username (for example, sipsuser_b and sipuser_c).
Using a custom user name mapper also enables you to support WebLogic user names that
contain an "@" character, such as @oracle.com.
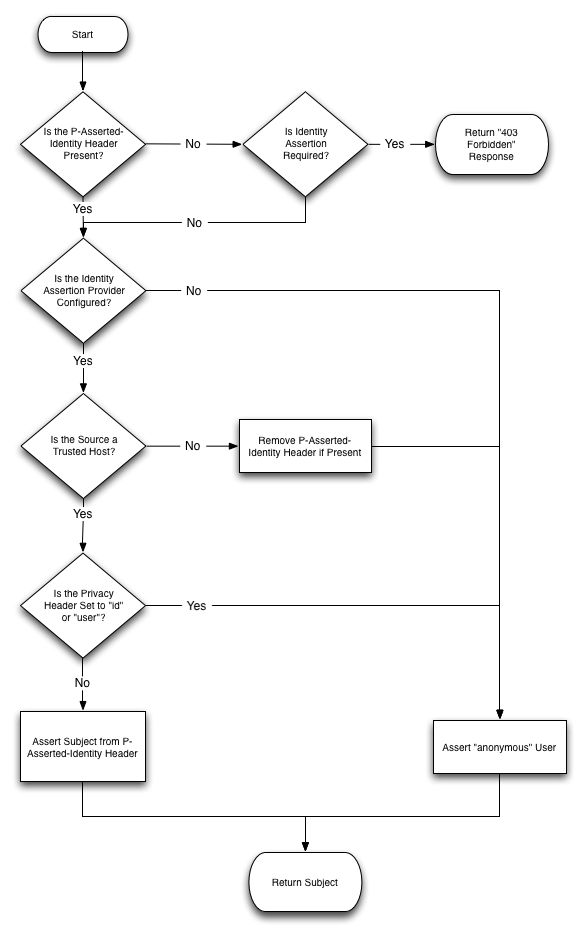
The presence of a P-Asserted-Identity header combined with
the Privacy header also determines the way in which Converged
Application Server proxies incoming requests. The value of the
@SipLogin annotation is also considered.
Figure 5-1 Managing Inbound Requests Having P-Asserted-Identity and Privacy Headers
The following diagram describes the standard security check procedure that
Converged Application Server uses when an asserted user name is not authorized to access
a requested resource. The standard security check is performed according to the
auth-method defined in the login-config element of
the sip.xml descriptor for the current application.
Figure 5-2 Standard Security Check Procedure
The presence of a P-Asserted-Identity header or a
P-Preferred-Identity header also affects the processing of outbound
SIP requests.
Figure 5-3 Managing Outbound Requests Having P-Asserted-Identity or P-Preferred Identity