Control Network Access
To control network access, you protect the usability and integrity of your network and data by routing and restricting traffic appropriately. Network access control for Oracle Integration is primarily oriented around restricting the IP addresses that can access Oracle Integration and its related resources.
Types of Traffic
Inbound traffic originates outside an Oracle Integration instance, and outbound traffic originates in an Oracle Integration instance.
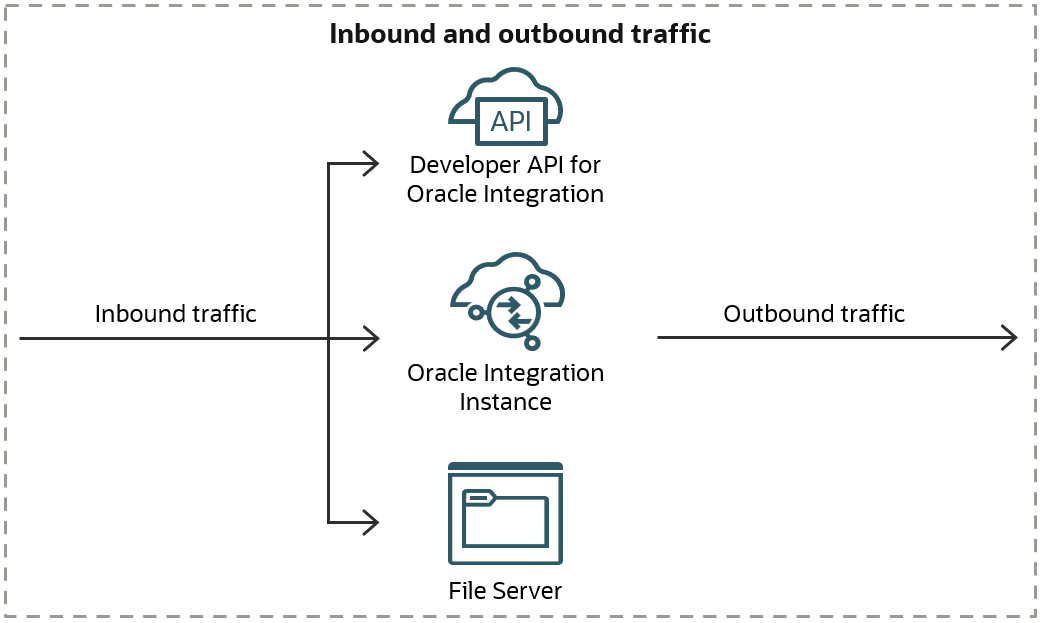
Oracle routes and restricts traffic according to its type. The following table provides a quick overview of the routing and restrictions for inbound and outbound traffic.
| Type of traffic | Definition |
|---|---|
|
Inbound traffic |
Also called ingress traffic, this traffic originates outside Oracle Integration and goes to:
To restrict the traffic, create an allowlist for the Oracle Integration instance. The allowlist applies to traffic from the service gateway and the public internet. Keep reading for more details and links to step-by-step instructions. |
|
Outbound traffic |
Also called egress traffic, this traffic originates in an Oracle Integration instance and goes to a target system. |
Inbound and outbound traffic is routed in the following ways.
| Type of traffic | How the traffic is routed |
|---|---|
|
Traffic across Oracle Cloud Infrastructure services that are in the same region |
Traffic within a region is routed through a service gateway:
|
|
Traffic across Oracle Cloud Infrastructure services that are in different regions |
Cross-region traffic is routed through a NAT gateway or the internet gateway. |
|
Traffic that comes through the public internet |
Inbound and outbound traffic that comes through the public internet doesn't require any configuration. |
|
Traffic that comes through either (1) the connectivity agent over the public internet or (2) FastConnect and VPN |
Inbound and outbound traffic that comes through an on-premises connectivity agent goes over the public internet. Inbound and outbound traffic that comes through FastConnect and VPN goes through the FastConnect link. |
|
Outbound traffic that comes through a private channel |
If your organization configures a private endpoint to connect to private resources that are in your virtual cloud network (VCN), outbound traffic to these resources goes through a private channel that is set up within Oracle Cloud Infrastructure. |
Control Inbound Network Access
After you create an Oracle Integration instance, access to the Developer API for Oracle Integration 3, the integration endpoints, and File Server is open by default. However, you can use allowlists to control the inbound access to the APIs and File Server.
An allowlist restricts access based on the source system or source networks and creates a stronger security posture.
If you choose to control inbound network access, you are responsible for completing the required tasks.
| Security goal | Owner | More information |
|---|---|---|
|
Restrict traffic that comes from the same Oracle Cloud Infrastructure region as your Oracle Integration instance |
|
About this traffic By default, all inbound traffic coming from an Oracle Cloud Infrastructure Virtual Cloud Network (VCN) that is in the same region as an Oracle Integration instance is open. However, you can restrict the traffic using a service gateway. How to achieve this goal
Notes
|
|
Restrict traffic that comes from outside the Oracle Cloud Infrastructure region of your Oracle Integration instance |
|
About this traffic Inbound traffic to Oracle Integration comes from the following sources:
By default, this traffic comes over the internet. Restricting the traffic that comes in over the internet provides your organization with an additional level of security. Restrict this traffic by using a Classless Inter-Domain Routing (CIDR) block range. How to achieve this goal
|
|
Allow your network to access File Server |
|
Update the allowlist for File Server so that your organization's network can access File Server. This one-time task is required for every organization that uses File Server. See Create an Allowlist for Public IP Addresses in Using File Server in Oracle Integration 3. |
Control Outbound Network Access
Oracle Integration doesn't restrict outbound traffic from itself. However, Oracle Integration sends outbound traffic only as part of an integration that your organization configures.
The ways that you secure, enable, and allow this traffic depend upon the location of the external service that receives the outbound traffic. Keep reading for more details.
| Security goal | Owner | More information |
|---|---|---|
|
Secure outbound traffic to endpoints that are in either of the following locations:
|
|
Secure this traffic using a private endpoint A private endpoint ensures that an Oracle Integration instance can communicate with target applications using an allowlist, also known as an access control list (ACL). If the endpoint is public facing, you must also configure a private NAT gateway. If your tenancy uses Zero Trust Packet Routing (ZPR) and you need to connect to ZPR-secured OCI resources, you must also assign security attributes to your instance. Learn more about private endpoints To learn more about private endpoints, including the traffic that you can secure using a private endpoint and the differences between private endpoints and the connectivity agent, see Connect to Private Resources in Provisioning and Administering Oracle Integration 3. Your responsibilities
|
|
Enable outbound traffic to endpoints that are in your organization's on-premises network, also known as a private cloud |
Download the connectivity agent installer:
Instance users with the ServiceAdministrator role Complete all other tasks:
Other administrators complete these tasks in third-party applications and on virtual machines. |
Enable this traffic by using an agent-based configuration If an integration must connect to endpoints that are in your corporate network, use an agent-based configuration. You can use an on-premises connectivity agent, or an Oracle Cloud Infrastructure connectivity agent. You can use a FastConnect peering pattern with both options. Some adapters allow you to use a FastConnect peering pattern without installing the connectivity agent. With the connectivity agent, you don't need to relax any network conditions; for example, you don't need to open a port for Oracle Integration. The connectivity agent runs in your corporate network and polls Oracle Integration for work. The agent requires internet or Virtual Cloud Network (VCN) inbound access to the Oracle Integration instance. Organizations that must use an agent-based configuration Use an agent-based configuration if your organization has any of the following requirements:
Learn more about the connectivity agent To learn about the connectivity agent, including its components, functionality, compatible adapters, diagrams, and more, see About Connecting to On-Premises Applications with the Connectivity Agent in Using Integrations in Oracle Integration 3. Your responsibilities
|
|
Allow Oracle Integration to access endpoints that are outside the Oracle Services Network |
Obtain the IP address:
Instance users with the ServiceAdministrator, ServiceDeveloper, ServiceUser, or ServiceViewer role
Update the allowlist:
Other administrators work in third-party applications and on virtual machines. |
If a target application has an allowlist enabled, update the allowlist so that Oracle Integration has access by completing the following steps:
|
Transport Layer Security for Inbound Traffic
An application that connects to Oracle Integration negotiates the Transport Layer Security (TLS) for inbound traffic. Oracle Integration currently supports TLS 1.2 for inbound traffic.
For details about the ciphers that are supported, see TLS Cipher Suites Support in Provisioning and Administering Oracle Integration 3.
Transport Layer Security for Outbound Traffic
Oracle Integration negotiates the Transport Layer Security (TLS) automatically with the target applications in an integration. Oracle Integration supports TLS 1.3 and 1.2 for outbound traffic.
If a target application supports TLS 1.3, Oracle Integration negotiates and communicates using 1.3. If not, Oracle Integration attempts to negotiate with 1.2. If your organization's preferred network protocol is TLS 1.3, configure TLS 1.3 as the preferred protocol in each of the applications that you integrate with.


