Assess the Vulnerability of your Databases
To asses the vulnerability of your database use the Vulnerability Detection navigation dashboard.
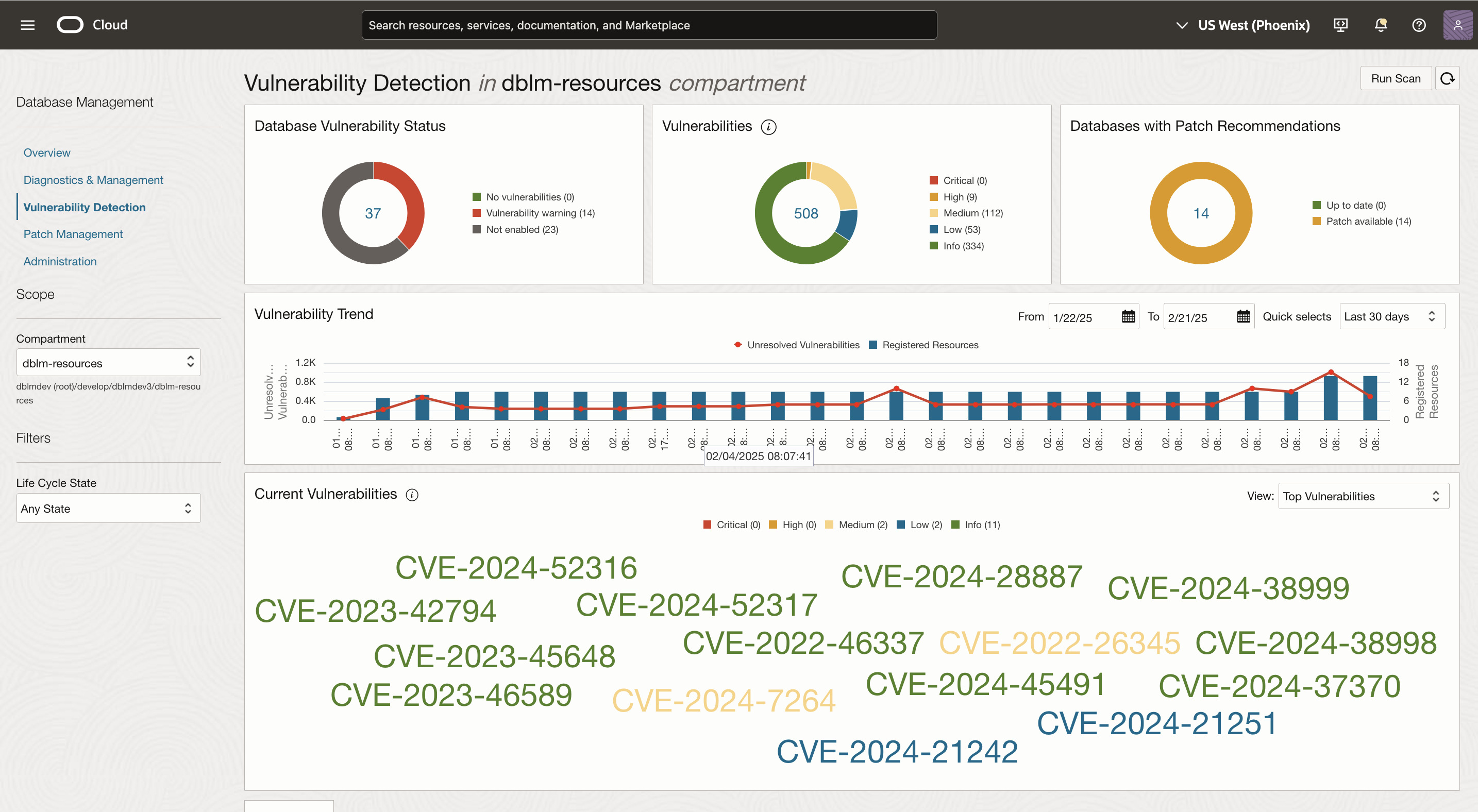
Database Management collects metrics for all enabled databases using the Management Agent, these metrics include Configuration and Vulnerability information for all your databases. They are automatically collected every 24 hours by default. Additionally, you can initiate an ad-hoc collection, as well using the Run Scan option.
Vulnerabilities at a Glance
- Critical Patch Update status: Every new Critical Patch Update is shown as a banner message. You can click on the link in the banner to view more details about the update. This banner can be dismissed so it doesn't appear again in the page.
- Run Scan section: Once the database is enabled for Vulnerability Detection, it takes up to 30 minutes for the Run Scan button to get enabled. Automatic Vulnerability scans run nightly but you can choose to run the scans manually by clicking the Run Scan button.
- Vulnerabilities by Status: This chart breaks down the vulnerabilities based on the status of the databases. You can see the number of databases with vulnerabilities, and the number of databases that are not registered with the Vulnerability Detection service.
- Vulnerabilities by Severity: This chart shows the total number of CVEs across all enabled databases broken down based on their severity levels. Based on industry standards, the CVEs are categorized into five different severity levels. The severity is based off of the Common Vulnerability Scoring System (CVSS) v3.0 ratings as shown in the following table:
Label Value Info 0.0 Low 0.1-3.9 Medium 4.0-6.9 High 7.0-8.9 Critical 9.0-10.0 - Databases with Patch Recommendations: This chart breaks down the number of Vulnerability Detection enabled databases based on whether they are up to date or if they still have patch recommendations that could be applied.
- Vulnerability Trends: The vulnerability trends chart provides context on how the number of vulnerabilities have changed over a period of time. The default time period for the chart is 30 days but this can be changed by changing the From and To dates, or by selecting one of the options from the Quick selects menu. Every bar represents the number of databases scanned and their corresponding red dot represents the number of unresolved vulnerabilities found for that scan. Hover over the red dots for more information. Clicking on the individual item, opens up a window with detailed information.
- Most Vulnerable Databases: The graph represents up to 50 of the most vulnerable databases and top vulnerabilities by database. The color of the CVE represents the severity level, and the size of the CVE represents the number of databases impacted by those vulnerabilities.
For example:
- The bigger the CVE number, the larger the number of databases affected.
- The larger the item, the more vulnerabilities found for the database.
- Databases Table: This section lists all the Container Databases (CDBs) and non-container databases enabled for vulnerability detection. Under each CDB is a link to open a window with all their Pluggable Databases (PDBs), in the Metric Collection Date column a warning icon will show if there are metric collection errors; click to open a new window listing all the errors. The Columns CVEs and Patch Recommendations also open windows with additional details for their corresponding items.
You may filter the databases by Status and Vulnerability Severity Level. Additionally you can search using the database name.
Click the Update button to proceed to the Patching flow.
- Vulnerabilities Table: This section lists all the vulnerabilities found for every registered database. The table can be filtered based on Severity Level, or whether Patch Recommendations are available. Additionally you can search using the database name.
Click the Update button to proceed the Patching flow.
The column, Number of Databases, opens a new window with a list of databases impacted by that particular CVE. In this window, the Patches column opens a new child window with all the patch recommendations available for that CVE. You can list all available patches or just recommended patches.
Oracle recommends that you to apply mandatory recommended security patches as well as evaluate and apply recommended alternate patches as well.