19 Managing Authentication and Shared Policy Components
This chapter describes how Administrators can manage shared policy components in the following topics:
-
Understanding Authentication and Shared Policy Component Tasks
-
Understanding Authentication Methods and Credential Collectors
-
Orchestrating Multi-Step Authentication with Plug-in Based Modules
-
Deploying and Managing Individual Plug-ins for Authentication
19.1 Prerequisites
Oracle recommends that you review information in Chapter 18, "Understanding Single Sign-On with Access Manager" before performing activities in this chapter. Additionally, the Oracle Access Management Console and at least one OAM Server must be installed and running within a WebLogic Server domain, and Access Manager must be running with at least two registered Agents.
19.2 Understanding Authentication and Shared Policy Component Tasks
This section introduces the tasks that must be performed to configure shared policy components required for use in Access Manager authentication policies that protect resources and enable single sign-on.
Task overview: Configuring shared policy components
-
Confirm that the desired resource type is defined, as described in this chapter:
-
Confirm that a host identifier definition named for the agent was created during agent registration, (or create one yourself), as described in:
-
Gain comprehension about credential collection with Access Manager:
-
Learn about and use the authentication plug-ins that enable multi-step authentication:
-
Create and manage authentication schemes that you can add to authentication policies, as described in:
-
Set up your own global password policy for either the default embedded or optional detached credential collector (unless specified, tasks apply to both ECC and DCC, with minor changes noted in the discussion):
-
Proceed to Chapter 20 to set up authentication policies.
19.3 Managing Resource Types
This section includes the following topics:
19.3.1 About Resource Types and Their Use
When adding a resource to an Application Domain, Administrators must choose from a list of defined Resource Types. Oracle-provided resource types include:
-
HTTP
-
wl_authen
-
TokenServiceRP
Administrators can configure additional resource types, and define operations on both Oracle-provided and custom resource types. A particular resource can be defined to use a subset of the declared operations, or all of them (which includes any new operators defined on the resource's type subsequently.Administrators cannot remove custom resource types or operations for which resources have been created. Oracle-provided resource types and operations are marked as read-only within the policy store and cannot be removed.
Note:
Changes to the operation list of a resource type is not allowed if a resource of that type exists.Table 19-1 compares resource types and operations.
Table 19-1 Comparison: Resource Types for Access Manager versus 10g
| Access Manager 11g | Oracle Access Manager 10g |
|---|---|
|
HTTP: The default resource type used with HTTP and HTTPS protocols. When adding an HTTP type resource to an Application Domain, Administrators must choose from a list of existing host identifiers and add the resource URL. This resource type is read-only. Default operations associated with the HTTP resource type need not be defined by an Administrator. Instead, policies developed and applied to the resource apply to all operations: Operations: Oracle-provided resource types are read-only; associated operations are pre-defined. Policies developed and applied to HTTP type resources apply to all operations.
See Also: "About the Resource Type Page". |
HTTP: The HTTP resource type is read-only. Operations: Oracle-provided resource types are read-only; associated operations are pre-defined. Policies developed and applied to the resource apply to all operations.
|
|
wl_authen: Resources for representing WebLogic Authentication schemes is also read-only (default operations cannot be modified or deleted.) This non-HTTP resource type is available to use with resources deployed in a WebLogic container in a domain that does not include Access Manager. The protected resource is accessed through its URL on the Oracle WebLogic Server. Type wl_authen resources, require a custom Access Client. |
N/A |
|
TokenServiceRP: Resources for representing Token Service Relying Party. The Operation for this resource type is Issue. |
N/A |
|
Custom Resource Types: Have no associated host identifier. A custom "EJB" resource type can be created on demand for use in SSO integrations. |
EJB: A custom resource type used in SSO integrations with WebLogic and WebSphere for authenticating the user. During authentication, the user's groups were fetched and populated in the Subject Principal as roles. Subsequent authorization was executed inside the application server based on user roles. No authorization calls were made using resource operations. |
|
Non-HTTP resource types have no associated host identifier. When adding non-HTTP resources to an Application Domain, Administrators must enter the Type name into the Resource URL field as a pointer. The name cannot match any host Identifier (and vice versa). This is not a relative HTTP URL. |
19.3.2 About the Resource Type Page
In the Oracle Access Management Console, resource types are organized with other Components under the Policy Configuration tab. The navigation tree shows Oracle-provided resource types: HTTP, wl_authen, and TokenServiceRP.
Note:
Pre-defined resource types cannot be deleted. Pre-defined operations are shown with a lock icon and cannot be deleted. Additional operations can be created, edited, or deleted as needed.The HTTP resource type, shown in Figure 19-1, is used for Web applications protected by Access Manager and accessed using internet protocols (HTTP or HTTPS).
Figure 19-1 Default HTTP Resource Type Definition
Description of "Figure 19-1 Default HTTP Resource Type Definition"
The wl_authen resource type is shown in Figure 19-2. It is used for Fusion Middleware applications that use one of the following Access Manager Identity Assertion Provider configurations described in the Oracle Fusion Middleware Application Security Guide:
-
Identity Asserter
-
Identity Asserter with Oracle Web Services Manager
-
Authenticator function
The TokenServiceRP resource type represents the Token Service Relying Party, as shown in Figure 19-3. The operation for this resource type is Issue. For more information, see "Managing TokenServiceRP Type Resources".
Figure 19-3 Default Resource Type TokenServiceRP Resource Type
Description of "Figure 19-3 Default Resource Type TokenServiceRP Resource Type"
Table 19-2 describes the elements in each resource type definition.
Table 19-2 Resource Type Definition
| Element | Description |
|---|---|
|
Name |
Required. A unique name of up to 30 alpha or numeric characters. Note: A non-HTTP Resource Type name cannot match a Host Identifier (and vice versa). |
|
Description |
Optional. Use this field to describe the purpose of this resource type using up to 200 alpha or numeric characters. For example: Resources representing WebLogic Authentication schemes. |
|
Operations |
Optional. Policies that govern a particular resource apply to all specified operations defined for the resource. Add (or remove) operations for this resource type as a string and the operations will be available when you define a resource of this type within an Application Domain. There is no limit to the number of operations that can be added to the resource type.
Remote Registration: During automatic policy creation, specified operations are supported. During automatic policy creation with no operations specified, then All operations defined for that type are supported. Migration: During an upgrade to Access Manager 11.1.2 (from 10g or from 11.1.1.3 or from 11.1.1.5), resource definitions and HTTP default operations are handled automatically. However, you must create any custom resource types to replace 10g-provided EJB custom resource types which are no longer provided by Oracle. See See Also: "About Resource Types and Their Use" and "Defining Resources in an Application Domain". |
Following topics describe how to create, modify, and delete a resource type.
19.3.3 Searching for a Specific Resource Type
Users with valid Administrator credentials can use the following procedure to locate a defined resource type.
See Also:
"Conducting A Search"-
From the Oracle Access Management Console, click Resource Types.
-
From the search type list, choose Resource Type, enter the name of the Resource Type you want to find (with or without a wild card (*)), and click Search. For example:
h*Alternatively: Go to the desired Application Domain, open the Resources node to display controls for that domain, choose a Resource Type from the list, and click Search.
-
Click the Search Results tab to display the results table, and then:
-
Edit or View: Click the Edit button in the tool bar to display the configuration page.
-
Delete: Click the Delete button in the tool bar to remove the instance; confirm removal in the Confirmation window.
-
Detach: Click Detach in the tool bar to expand the table to a full page.
-
Reorder Columns: Select a View menu item to alter the appearance of the results table.
-
-
Click the Browse tab to return to the navigation tree when you finish with the Search results.
19.3.4 Creating a Custom Resource Type
Users with valid Administrator credentials can use the following procedure to create a defined resource type. For instance, you can define a custom resource type that applies to as few as one or two (or more) operations. Any defined custom resource type is listed with default resource types when adding resources to an authentication or authorization policy.
To create a custom resource type
-
From the Oracle Access Management Console, click Resource Types.
-
Click the Add + button.
-
Enter the following information:
-
Name: A unique name that identifies this resource type.
-
Description: Optional.
-
Operations: Click + in the Operations table, type the operation name into the field provided. Repeat as needed to define all operations for this resource type.
-
Reconfigure Table: Select a View menu item to alter the appearance of the results table.
-
-
Click Apply to submit this custom resource definition.
-
Add this resource definition to an Application Domain as described in "Adding and Managing Policy Resource Definitions".
19.4 Managing Host Identifiers
This section describes host identifiers and their use as well as how to create, modify, or remove a host identifier. Topics here include:
19.4.1 About Host Identifiers
Access Manager policies protect resources on computer hosts. Within Access Manager, the computer host is specified independently using a host identifier.
Table 19-3 illustrates the different host names under which a Web server might be accessible to employees. Creating a single Host Identifier using all of these names allows you to define a single set of policies to appropriately protect the application, regardless of how the user accesses it.
Table 19-3 Host Identifiers Examples
| Sample Host Identifier | Description |
|---|---|
|
hrportal.intranet.company.com |
A friendly name employees can remember. This is a load-balanced proxy, and requests to this could actually utilize one of several servers hosting the HR application. |
|
hr-sf-02.intranet.company.com |
A single machine hosting the application, which can be accessed directly. |
|
hrportal.company.com |
The same application is also accessible externally to the corporate firewall, primarily for use by ex-employees to check benefits, 401k info, and so on. This is also a load-balanced reverse proxy. |
Based on a defined host identifier, Administrators can add specific resources to an Application Domain and apply policies to protect those resources.
Registered Agents protect all requests that match the addressing methods defined for the host identifier used in a policy. A request sent to any address on the list is mapped to the official host name and Access Manager can apply the policies that protect the resource and OAM can apply the policies that protect the resource.
A host identifier is automatically created when an Agent (and application) are registered using either the Oracle Access Management Console or the remote registration tool. Administrators can manually add a host identifier if an application and resources exist on a host that does not have a mapped host identifier. Also, Oracle Access Management Administrators can modify an existing host identifier to add in the new host name variations. For instance, adding another proxy Web server with a different host name requires a new host name variation.
For more information, see:
19.4.1.1 Host Identifier Usage
At design time, the host identifier can be used while defining which resources belong to a specific Application Domain. Resources are scoped using their host identifier (HTTP) or type (non-HTTP). This combination uniquely identifies them across Access Manager.
Note:
Each resource should be unique across all Application Domains; each resource and host identifier combination must be unique across all Application Domains.At run time, Web server host information in the access query from an OAM Agent is mapped to a host identifier and associated with the resource that is being accessed by a user. The OAM Agent obtains the Web server host information in one of two ways:
-
If the Preferred Host parameter is configured for virtual Web hosting support (see"About Virtual Web Hosting"), Web server host information for the given request is obtained from the Web server.
-
If the Preferred Host parameter directly specifies the Web server host information, it is always used irrespective of the Web server's own host information.
This allows for the Resources to be specified in terms of logical host names in their Host Identifiers, instead of the host names matching the present deployment of the Web server.
For instance, a user accessing aseng-wiki, would enter:
http://example-wiki.uk.example.com/wikiexample
Here, wikiexample is the resource URL and example-wiki.uk.example.com is the host. Matching this host and port (port is 80) provides the host identifier.
Web server host information is generally acquired by setting the Preferred Host string of the OAM Agent. If the Agent is actively protecting multiple virtual hosts, this string can be set to server_name to ensure that the actual request hostname is correctly picked up from the Web server's request object. For more information, see "About Virtual Web Hosting"
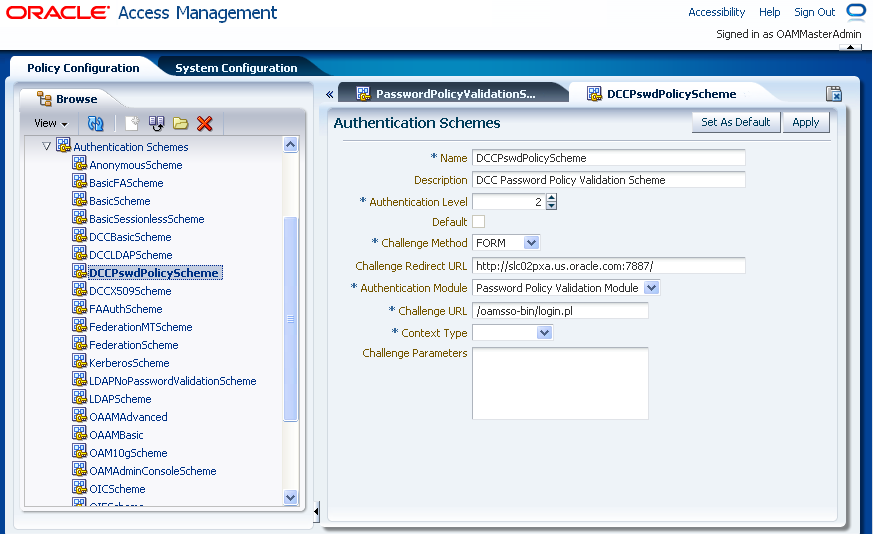
Authenticating Hosts and Challenge Redirect in Authentication Schemes
When a user attempts to access a protected resource URL, she is redirected to the server specified in the Challenge Redirect field of the authentication scheme. If the authentication challenge is to be processed by another host, the name of that host must be defined to be available in the Host Identifiers list. For example, if a user is redirected to an SSL-enabled server for authentication, that server must be defined as a host identifier.
Note:
If you enter a host name in the Challenge Redirect field of an authentication scheme, it must be defined as a Host Identifier.19.4.1.2 Host Identifier Guidelines
Each host identifier can be defined to represent one or more Web server hosts. Following are several important guidelines for host identifiers:
-
Each host name must be unique.
-
Each host name:port pair must be unique.
-
Each host name:port pair must belong to only one host identifier.
-
Each host name:port pair must match the end user's entry exactly.
-
A Host Identifier name cannot match a non-HTTP Resource Type name (and vice versa).
-
Each resource and host identifier combination must be unique across all Application Domains.
For more information, see "Host Identifier Variations".
19.4.1.3 Host Identifier Variations
Host identifiers are used to simplify the identification of a Web server host by defining all possible hostname variations. Host identifiers consist of a list of all URL addressing methods. A host identifier must be configured for each Web site or virtual Web site that you want to protect with Access Manager.
You can identify Web server hosts to Access Manager in various ways, for example, by providing a computer name or an IP address. The following are examples of how the same host can be addressed:
-
example.com
-
example.com:80
-
www.example.com
-
www.example.com:80
-
216.200.159.58
-
216.200.159.58:80
19.4.2 About Virtual Web Hosting
You can install a Webgate on a Web server that contains multiple Web site and domain names. The Webgate must reside in a location that enables it to protect all of the Web sites on that server.
Note:
The information here is the same for both 11g and 10g Webgates.The virtual Web hosting feature of many Web servers enables you to support multiple domain names and IP addresses that each resolve to their unique subdirectories on a single virtual server. For example, you can host abc.com and def.com on the same virtual server, each with its own domain name and unique site content. You can have name-based or IP-based virtual hosting.
A virtual host referees the situation where the same host has multiple sites being served either based on multiple NIC cards (IP based) or multiple names (for example, abc.com and def.com resolving to same IP).
Consider a case where you have two virtual hosts configured on an OHS Server acting as reverse proxy to OAM Server, as follows:
-
One virtual host is configured in two-way SSL mode
-
One virtual host configured in non-SSL mode
Suppose there are two resources protected with different authentication schemes and Application Domains:
-
/resource1 is protected by a X509Scheme with a Challenge URL (to define the credential collection URL) of https://sslvhost:port/
When the user accesses /resource1 he is redirected to the OHS Server on the SSL port for authentication and is asked for the X.509 Certificate.
-
/resource2 is protected by a LDAPScheme on the second virtual host with a Challenge Redirect of http://host:port/
When user accesses /resource2 he is redirected to second virtual host which is in non-SSL mode (or in one way SSL mode if required). The Login form for LDAP authentication is displayed.
Note:
Your deployment can support X.509 and Form authentication with 10g mod_osso. However, mod_osso can be configured for only one SSO Server. In this case, the Agent redirects to Access Manager on the non-SSL virtual host. The credential collector checks the Authentication Scheme's Challenge URL parameter for the resource and redirects back to the HTTPS virtual host for X509 authentication.19.4.2.1 Placing a Webgate Behind a Reverse Proxy
You can use 10g Webgates with reverse proxies for Access Manager. This topic discusses benefits and pitfalls of this strategy.
Benefits:
-
All Web content can be protected from a single logical component as long as all requests go through the proxy.
This is true even for platforms that are not supported by Access Manager. If you have different types of Web servers (for example, iPlanet, Apache, and so on) on different platforms (for example, Windows XP, Linux, and so on), all content on these servers can be protected. A reverse proxy can be a workaround for unsupported Web servers, eliminating the need to write custom Access Clients for unsupported Web servers and on platforms that do not have Webgate support, for example, MacOS.
-
A reverse proxy offers architecture flexibility.
Reverse proxies can allow deployments to expose an application that is available on the intranet to the extranet. Or applications that are available on the extranet can be exposed to the intranet. This can be done without any changes to the application that is already deployed.
-
You only need to install a separate Webgate on the reverse proxy, rather than on every Web server.
This allows for a single management point and can help with manageability of the system. You can manage the security of all of the Web servers through the reverse proxy without establishing a footprint on the other Web Servers.
Pitfalls: The main pitfall of using a proxy is the extra work involved in setup. If you deploy the Webgate on a Web server that is behind a reverse proxy, the following are configuration requirements:
-
Ensure that any Web server that uses the reverse proxy for authentication only accepts requests from the reverse proxies.
This will also require that Webgates deployed on this Web server be configured to not enforce IP validation for requests from the reverse proxy server that front-ends the Webgate. This is done by configuring the known IP addresses of the reverse proxy server or servers in the IP Validation list. Note that while you can achieve the same effect by turning IP validation off for the Webgate, this is not a recommended approach due to security risks.Ensuring that the Web server only accepts requests from reverse proxies is typically done by adding an ACL statement in the server. This prevents users from bypassing the reverse proxy and directly accessing restricted content.
-
Update the virtual hosts that are configured in the Policy Manager so that the Access System intercepts requests that are sent to the reverse proxy.
-
Prevent people from circumventing the proxy by entering URLs that point directly to the back-end system.
You can prevent this problem through the use of Web Server Access Control Lists or firewall filters.
-
Since all user requests are processed by the proxy, you must deploy enough proxy servers to enable the system to handle the load.
-
Redirect all existing URLs to the host name and port number of the reverse proxy server.
This often requires configuring the reverse proxy to perform content inspection and rewriting to prevent any absolute HTML links, for instance, to prevent broken link. This is achievable with most reverse proxies, and this is something you can configure independently of the Access System,.
-
It is a best practice that URL links exposed to the front-ended applications rely on only relative URLs (../../sub-path/resource) rather than absolute URLs (http://example.com:[port]/path/resource).
Absolute URLs can break links on the end user's browser when deployed behind a reverse proxy.
19.4.2.2 Configuring Virtual Hosting for Non-Apache Web Servers
Ensure that the Virtual Host box is checked on the 10g Webgate registration page.
On most Web servers, other than Apache-based servers, you must set the Preferred Host value to HOST_HTTP_HEADER. This ensures that, when user's browser sends a request, the Webgate sets the value of the Preferred Host to the host value in the request. For example, suppose a user enters the string example2 in a URL:
http://example2
On the Web server, if one of the Web sites has a host named example2, the request is served by the matching virtual site.
In the Preferred Host field of the expanded 10g Webgate registration page, enter the following:
HOST_HTTP_HEADER.
IIS Virtual Hosting: From the IIS console, you must configure each virtual Web site to contain the following fields:
-
Host Header Name
-
IP address
-
Port
19.4.2.3 Associating a Webgate for Apache with Virtual Hosts, Directories, or Files
Ensure that the Virtual Host box is checked on the 10g Webgate registration page.
On Apache-based Web servers (Apache, Apache 2, IBM HTTP Server, Oracle HTTP Server, and so on), the Preferred Host value must be set to SERVER_NAME.
Note:
The SERVER_NAME value is not supported for any host other than an Apache-based server. If you set this value for a non-Apache-based server, users will be unable to access any resources that are protected by Webgate on that Web server. Users will, instead, receive an error that the Webgate configuration is incorrect.The ServerName directive must be explicitly set with 7777 along with the hostName. This is irrespective of the Listen directive is set correctly. The Server sometimes requires this value explicitly to identify itself, most often it can identify itself automatically.
When using an Apache-based reverse proxy for single sign-on, in the Web server configuration file (httpd.config, for example) file you specify the Web sites to run on the Apache server. The settings can be global across all Web sites or local to a Web site. You can restrict the Access Manager loading references in the httpd.config file to be associated with a specified site, with virtual hosts, specific directories or even files.
To associate the Webgate with specific targets, you move the following directives the the http.conf file:
AuthType Oblix require valid-user
You can put these directives in a block that tells Apache to use Webgate for every request. You can also move the directives to a block that limits when the Webgate is called. The following is an example of putting the LocationMatch directive after a VirtualHost directive:
DocumentRoot /usr/local/apache/htdocs/myserver ServerName myserver.example.net AuthType Oblix require valid-user
After you move the LocationMatch block to the VirtualHost directive, the Webgate will only work for that virtual host. You can add the LocationMatch block to as many virtual hosts as you want. The following examples shows how you could protect one virtual server:
ServerAdmin webmaster@example.net
DocumentRoot "Z:/Apps/Apache/htdocs/MYsrv"
ServerName apps.example.com
ProxyRequests On
SSLEngine on
SSLCACertificateFile Z:/Apps/sslcert_exampleapps_ptcweb32/intermediateca.cer
SSLCertificateFile Z:/Apps/sslcert_exampleapps_ptcweb32/sslcert_myapps_ptcweb32.cer
SSLCertificateKeyFile Z:/Apps/sslcert_exampleapps_ptcweb32/sslcert_myapps_ptcweb32.key
ErrorLog logs/proxysite1_log
CustomLog logs/proxysite1_log common
ProxyPass /https://apps.example.com/
ProxyPassReverse /https://apps.example.com/
ProxyPass /bkcentral https://apps.example.com/bkcentral
ProxyPassReverse /bkcentral https://apps.example.com/bkcentral
ProxyPass /NR https://apps.example.com/NR
ProxyPassReverse /NR https://apps.example.com/NR
AuthType Oblix
require valid-user
#*** BEGIN Oracle Access Manager Webgate Specific ****
LoadModule obWebgateModule Z:/apps/Oracle/WebComponent/access/oblix/apps/webgate/bin/webgate.dll
WebgateInstalldir Z:/apps/Oracle/WebComponent/access
WebgateMode PEER
SetHandler obwebgateerr
SSLMutex sem
SSLRandomSeed startup builtin
SSLSessionCache none
SSLLog logs/SSL.log
SSLLogLevel info
# You can later change "info" to "warn" if everything is OK
19.4.3 About the Host Identifier Page
A host identifier is automatically created when an Agent (and application) are registered using either the Oracle Access Management Console or the remote registration tool. In the Application Domain that is registered with the Agent, the host identifier is used automatically.
Administrators can use the console to create and manage host identifiers. Within the Oracle Access Management Console, host identifiers are organized under Shared Components, on the Policy Configuration tab navigation tree. Administrators can manually create a new host identifier definition, modify a definition, delete a definition, or copy an existing definition to use as a template. The name of the copy is based on the original definition name. For example, if you copy a definition named host3, the copy is named copy of host3.
Figure 19-4 illustrates a typical Host Identifier configuration page in the console, where you enter the canonical name for the host, and every other name by which the same host can be addressed by users.
Note:
Each host identifier must be unique. You cannot use the same host name and port in any other host identifier definition.Table 19-4 describes the host identifier definition.
Table 19-4 Host Identifier Definition
| Property | Description |
|---|---|
|
Name |
A unique name for this definition. Use only upper- and lower-case alpha characters. No punctuation or special characters are allowed. |
|
Description |
The optional description, up to 200 characters, that explains the use of this configuration. |
|
Host Name Variations |
|
19.4.4 Creating a Host Identifier
Users with valid Administrator credentials can use the following procedure to create a host identifier definition manually. This is needed if an application and resources were manually added to a host that has no mapped host identifier. When you choose Auto Create Policies when registering an Agent, this is done automatically.
Note:
If you copy an existing definition to use as a template, you must modify all unique identifiers in the copy.To manually create a Host Identifier
-
From the Oracle Access Management Console, click Host Identifiers.
-
Click the Create Host Identifier button in the upper-right corner of the Search Host Identifiers page.
Alternatively: Open the Host Identifiers node, click the Create (+) button above the Search Results table.
-
On the fresh Host Identifier page, fill in the:
-
Name
-
Description
-
Host Name Variations: Add (or remove) host name and port variations in the Operations list.
Add: Click the Create (+) button, then enter a new host name and port combination to identify variables that map to the Host Identifier Name.
Remove: Click a host name, then click the Delete button to remove it.
-
-
Repeat step 3c as needed to identify all variations of this host that users can access.
-
Click Apply to submit the new definition (or close the page without applying changes).
-
Close the Confirmation window, and confirm the new definition is listed in the navigation tree.
19.4.5 Searching for a Host Identifier Definition
Users with valid Administrator credentials can perform the following task to search for a specific host identifier.
Note:
During Delete, if the Host Identifier is associated with a resource, you are prompted with an alert. Without any association, the Host Identifier is deleted successfully.See Also:
"Conducting A Search"-
From the Oracle Access Management Console, click Host Identifiers.
-
In the Search Host Identifiers page Name field, enter a name (or a partial name with wild card (*)), or leave the Name field blank to show all Host Identifiers. For example:
my_h* -
Click the Search button to initiate the search and display results in a table, then:
-
View or Edit: Double-click the name in the Search Results table to display the configuration page, then add or edit as usual.
-
Delete: Click the Delete button in the tool bar to remove the selected item in the results table; confirm removal in the Confirmation window.
-
Detach: Click Detach in the tool bar to expand the Search Results table to a full page (or from the View menu, click Detach).
-
Reorder Columns: From the View menu, select reorder Columns and use the arrows provided to reorder the columns.
-
19.4.6 Viewing or Editing a Host Identifier Definition
Users with valid Administrator credentials can use the following procedure to modify a host identifier definition. This can include adding, changing, or removing individual host identifiers from the definition. For instance, when adding another proxy Web server with a different host name, you might need to modify an existing host identifier definition to add the new host name variation.
Prerequisite: Inventory Application Domains that refer to the host identifier and
Note:
After viewing settings, you can either close the page or modify settings as needed.See Also:
"About the Host Identifier Page"To view or modify a Host Identifier
-
Locate the desired host identifier and view it as described in "Searching for a Host Identifier Definition".
-
On the Host Identifier page, modify information as needed (Table 19-4):
-
Name
-
Description
-
Host Name Variations: In the table provided:
Add (+) Host Name Variations: Click the Add (+) button, then enter a new host name and port combination to identify variables that map to the Host Identifier Name.
Delete (X) Host Name Variations: Click a host name, then click the Delete button to remove it.
-
-
Repeat step 3c as needed to add or remove variations.
-
Click Apply to submit the changes (or close the page without applying changes).
-
Dismiss the Confirmation window, and close the page when you finish.
19.4.7 Deleting a Host Identifier Definition
Users with valid Administrator credentials can use the following procedure to delete an entire host identifier definition. A validation error occurs if you attempt to delete the host identifier that is being used in a resource.
Note:
If the Host Identifier is associated with a resource, you are alerted. Without any association, the Host Identifier is deleted.Each resource in an Application Domain is associated with a specific host identifier. If you intend to delete a host identifier you must first modify any resource definitions in an Application Domain that uses this host identifier.
See Also:
"Viewing or Editing a Host Identifier Definition" if you want to remove a single host identifier from an existing definition.-
Locate and modify related resource definitions in any application domains that uses this host identifier. See "Searching for a Resource Definition".
-
Locate the desired host identifier as described in "Searching for a Host Identifier Definition".
-
View: Double-click the name in the results table to display the configuration page, and confirm this can be removed.
-
Delete: Click the Delete button in the tool bar to remove the selected item in the results table; confirm removal in the Confirmation window.
19.5 Understanding Authentication Methods and Credential Collectors
With Access Manager, authentication involves redirecting the requester (user) to a centralized component that performs authentication (known as the Credential Collector).
This section provides the following topics:
19.5.1 About Different Authentication Methods
Authentication is the process of proving that a user is who he or she claims to be. Authenticating a user's identity with Access Manager refers to running a pre-defined set of processes to verify the digital identity of the user.
Using Access Manager, a resource or group of resources can be protected by a single authentication process known as an authentication scheme. Authentication schemes rely on pre-defined authentication modules or plug-ins.
This section describes multi-level authentication and other authentication methods supported by Access Manager.
Access Manager enables Administrators to assign different authentication levels to different authentication schemes, and then choose which scheme protects which application. Every authentication scheme requires a strength level. The lower this number, the less stringent the scheme. A higher level number indicates a more secure authentication mechanism.
SSO capability enables users to access more than one protected resource or application with a single sign in. A user who is authenticated to access resources at level 2, is eligible to access resources protected at levels less than or equal to 2. However, if the user is authenticated to access resources at level 2 and then attempts to access resources protected by level 3, the user is asked to re-authenticate (this is known as step-up authentication).
For more information, see "About Multi-Level and Step-Up Authentication".
See Also:
"Multi-Step Authentication"Multi-step authentication requires a custom authentication module composed of two or more authentication plug-ins that transmit information to the backend authentication scheme several times during the login process. All information collected by the plug-in and saved in the context will be available to the plug-in through the authentication process. Context data can also be used to set cookies or headers in the user's login page.
See "Comparing Simple Form and Multi-Factor (Multi-Step) Authentication".
Integrated Windows Native Authentication is supported for both OSSO and Webgate protected applications. This form of authentication relies on the Kerberos authentication module. For more information, see Chapter 50, "Configuring Access Manager for Windows Native Authentication".
Authentication features required by Oracle Fusion Middleware applications are supported, including:
-
Weak authentication, typically a user name and password, no certificates
-
Auto-login with third-party self-service user provisioning
-
HTTP header support for user context information. For instance, host identifiers are used to create a host context for the resource. This is useful when adding resources that have the same URL paths on different computers.
If you use different authentication schemes for two WebGates, users can go from a higher authentication scheme to a lower one without re-authentication, but not from a lower level to a higher level.
Note:
During single sign-on, users might pass the authentication tests but might fail authorization tests when attempting to access a second or third resource. Each resource in the domain might have a unique authorization policy.For details about configuring and using authentication schemes with Access Manager, see "Managing Authentication Schemes".
19.5.2 Comparing Embedded Credential Collector with Detached Credential Collector
Access Manager 11.1.2 supports the embedded credential collector (ECC) by default and also enables you to configure the latest Webgate to use as a detached credential collector (DCC, also known as an Authenticating Webgate).
The DCC is considered more secure than the default embedded credential collector (ECC). The centralized DCC presents the login page, collects user credentials (userID and password, for example), and sends these to the OAM Server using the back channel Oracle Access Protocol (OAP). Additional credentials can be requested using the DCC.
When OAM Server is configured to use the DCC, the ECC and its HTTP endpoints are disabled. The only HTTP communication is to the Oracle Access Management Console hosted by the WebLogic AdminServer in the domain where the OAM Server is deployed. Connectivity to the AdminServer can be controlled at the network level, for example, to disallow administration requests from outside the internal network.
-
Allowing both the ECC and DCC to co-exist enables you to use authentication schemes and policies configured for use with either the ECC or the DCC. This enables a fallback mechanism for resources that rely on the ECC, which includes the Oracle Access Management Console.
-
Disabling (turning off) the ECC entirely prohibits access to resources that rely on the ECC mechanism, including the Oracle Access Management Console.
While the embedded and detached credential collectors (ECC and DCC, respectively) are essentially the same, compare the two in Table 19-5.
Table 19-5 Comparing the DCC and ECC
| DCC | ECC | |
|---|---|---|
|
Deployment |
The Detached Credential Collector remains a logical part of the server and acts as a front channel communication endpoint of the OAM Server. However, the DCC also:
|
The Embedded Credential Collector is deployed with, and integral to, the OAM Server and part of the protocol binding layer. The ECC supports RSA SecurID passcode verification, get next token, create new pin workflows. |
|
DMZ Deployment |
Yes. The main benefit of a deployment using DCC in the DMZ is the termination of the end-user network connections within the public network, and the use of Oracle Access Protocol (Oracle's proprietary application network protocol) over mutually authenticated connections reaching the OAM Server. This offers a complete isolation of the OAM Server from the establishment of any unauthenticated network connection. Unauthenticated users cannot send malformed requests to the OAM Server. |
No. |
|
Communication channel |
DCC consumes HTTP/HTTPS requests from the user, then communicates with the OAM Server across the Oracle Access Protocol (back channel), which can be SSL-enabled. |
ECC communicates with both the user and the OAM Server across HTTP/HTTPS. |
|
DCC login, error, and password pages |
Dynamic pages general login/logout and password policy with the DCC are excluded automatically through the OHS httpd.conf/webgate.conf file--you do not need to configure a policy to exclude these. See the Webgate host in $
Note: Update the Perl location in the first line of the login, logout, and securid scripts in See Also: Table 19-31, "Credential Collector Password Pages". Chapter 49, "Integrating RSA SecurID Authentication with Access Manager" for details about login pages for this implementation. For details about customizing pages and messages, see the Oracle Fusion Middleware Developer's Guide for Oracle Access Management. |
Pages where the user enters her credentials arrive out of the box on the OAM Server and require no additional settings or changes.
|
|
Perl Scripts for DCC-based Login and Logout The path name of the Perl executable must be updated in Oracle-provided Perl scripts on the Webgate host Unix: The which perl /usr/bin/perl However, Perl scripts themselves point to: /usr/local/bin/perl Windows: The default Perl Interpreter specified in Oracle-provided Perl scripts will not be available. You must update the Perl Interpreter path in these scripts to actual path to Perl on your system. |
N/A |
|
|
Password policy enforcement |
Yes. |
Yes |
|
Authentication scheme collection methods |
DCC supports only Form Based Authentication. |
ECC supports all challenge methods. The ECC collects user credentials based on the challenge method of the Authentication Scheme and sends it back to OAM Server for validation. |
|
Custom Authentication Plug-ins and Challenge Methods |
Yes; same as ECC. |
All challenge methods and multi-step authentication (Password Policy and other custom authentication plugins) are supported. |
|
Single Step (Simple Form) Authentication |
Yes; same as ECC. |
Yes. Both the DCC and ECC handle this, where:
|
|
Multi-Step Authentication |
Yes. Both the DCC and ECC handle complex multi-factor (multi-step, iterative, and variable) Authentication processing. In this case:
|
Yes. Both the DCC and ECC handle complex multi-factor (multi-step, iterative, and variable) Authentication processing. |
|
Authentication Processing |
The DCC does not restrict authentication functionality of the OAM Server in any way as compared to the ECC. The DCC:
|
During authentication:
|
|
Overriding the ECC |
To deploy the DCC and override the ECC, an Administrator must perform the following tasks to specify the relevant DCC URLs and forms.
|
N/A |
|
Logout Configuration |
See "Configuring Logout When Using Detached Credential Collector-Enabled Webgate" |
|
|
Cookie/Token |
|
|
19.5.3 Authentication Event Logging and Auditing
Authentication Success and Failure events are audited, in addition to administration events. Auditing covers creating, modifying, viewing, and deleting authentication schemes, modules, and policies. Information that is collected about the user who is authenticating includes:
-
IP address
-
User Login ID
-
Time of Access
During logging (or auditing), user information, user sensitive attributes are not recorded. Secure data (user passwords, for example) are removed to avoid misuse.
19.6 Managing Native Authentication Modules
In Access Manager, each authentication scheme requires an authentication module.
Note:
Native authentication modules lack the flexibility to orchestrate two or more plug-ins to meet specialized authentication needs. Therefore, native authentication modules are targeted for deprecation in future releases. Oracle strongly recommends using plug-in based authentication modules as described "Orchestrating Multi-Step Authentication with Plug-in Based Modules".This section provides the following information:
19.6.1 About Native Access Manager Authentication Modules
Table 19-6 lists the Native Access Manager Authentication Modules.
Table 19-6 Native Authentication Modules
| Module Name | Description |
|---|---|
|
LDAP |
Matches the credentials (username and password) of the user who requests a resource to a user definition stored in an LDAP directory server. An LDAP module is required for Basic and Form challenge methods. See Also: "Native LDAP Authentication Modules". |
|
LDAPNoPasswordAuthModule |
Matches the credentials (username and password) of the user who requests a resource to a user definition stored in an LDAP directory server. An LDAP module is required for Basic and Form challenge methods. See Also: "Native LDAP Authentication Modules". |
|
Kerberos |
Identifies the key tab file and krb5.configuration file names and Principal. Use this plug-in when configuring Access Manager for Windows Native Authentication, as described in Chapter 50. See Also: "Native Kerberos Authentication Module". |
|
X509 |
Similar to the LDAPPlugin with additional properties that indicate which attribute of the client's X.509 certificate should be validated against the user attribute in LDAP. See Also: "Native X509 Authentication Module". |
|
Custom Authentication Modules |
This type of module relies on bundled plug-ins (or those that are developed using the Access Manager Authentication Extensibility Java API). This type of module generally uses more than one plug-in that you can orchestrate to ensure that each one performs a specific authentication function. Depending on the success or failure action defined for each plug-in, another authentication plug-in is called. See Also: "About Plug-in Based Modules for Multi-Step Authentication", and Oracle Fusion Middleware Developer's Guide for Oracle Access Management for details about developing and deploying plug-ins, custom authentication modules, and schemes that use custom modules. |
See Also:
-
Oracle Fusion Middleware Developer's Guide for Oracle Access Management for details about creating custom authentication plug-ins
19.6.1.1 Native Kerberos Authentication Module
The pre-configured Kerberos authentication module is illustrated in Figure 19-5. Additional details follow the figure.
Figure 19-5 Native Kerberos Authentication Module
Description of "Figure 19-5 Native Kerberos Authentication Module"
Table 19-7 describes the definition of the native Kerberos authentication module. You can use the existing, pre-configured Kerberos authentication module or create one of your own.
Table 19-7 Native Kerberos Authentication Module Definition
| Element | Description |
|---|---|
|
Name |
The unique ID of this module, which can include upper and lower case alpha characters as well as numbers and spaces. |
|
Key Tab File |
The path to the encrypted, local, on-disk copy of the host's key, required to authenticate to the key distribution center (KDC). For example: /etc/krb5.keytab. The KDC authenticates the requesting user and confirms that the user is authorized for access to the requested service. If the authenticated user meets all prescribed conditions, the KDC issues a ticket permitting access based on a server key. The client receives the ticket and submits it to the appropriate server. The server can verify the submitted ticket and grant access to the user submitting it. The key tab file should be readable only by root, and should exist only on the machine's local disk. It should not be part of any backup, unless access to the backup data is secured as tightly as access to the machine's root password itself. |
|
Principal |
Identifies the HTTP host for the principal in the Kerberos database, which enables generation of a keytab for a host. |
|
Krb Config File |
Identifies the path to the configuration file that controls certain aspects of the Kerberos installation. A krb5.conf file must exist in the /etc directory on each UNIX node that is running Kerberos. krb5.conf contains configuration information required by the Kerberos V5 library (the default Kerberos realm and the location of the Kerberos key distribution centers for known realms). |
19.6.1.2 Native LDAP Authentication Modules
Oracle provides two LDAP authentication modules:
-
LDAP
-
LDAPNoPasswordAuthModule
Both modules have the same requirements (Name and User Identity Store), as illustrated in Figure 19-6. Additional details follow the figure.
Figure 19-6 Native LDAP Authentication Module
Description of "Figure 19-6 Native LDAP Authentication Module"
Table 19-8 describes the elements in an LDAP authentication module. The same elements and values are also used in LDAPNoPasswordAuthnModule.
Note:
These standard LDAP Authentication Modules are targeted for deprecation. Future enhancements will not be available in standard modules. Oracle strongly recommends using plug-in based modules.Table 19-8 Native LDAP Authentication Modules Definition
| Element | Description |
|---|---|
|
Name |
A unique name for this module. |
|
User Identity Store |
The designated LDAP user identity store must contain any user credentials required for authentication by this module. The LDAP store must be registered with Access Manager. See Also: "Managing OAM Identity Stores". Multiple identity store vendors are supported. Upon installation, there is only one User Identity Store, which is also the designated System Store. If you add more identity stores and designate a different store as the System Store, be sure to change the LDAP module to point to the System Store. The authentication scheme See Also: "Setting the Default Store and System Store" and "Administrator Lockout". |
19.6.1.3 Native X509 Authentication Module
Access Manager provides a pre-configured X509 authentication module as a default. Administrators can also create new X509 authentication modules. In cryptographic terms, X.509 is a standard for digital public key certificates used for single sign-on (SSO). X.509 specifies standard formats for public key certificates, certificate revocation lists, and attribute certificates among other things.
With X.509 digital certificates you can assume a strict hierarchical system of certificate authorities (CAs) issuing the certificates. In the X.509 system, a CA issues a certificate that binds a public key to a particular Distinguished Name, or to an Alternative Name such as an e-mail address or a DNS-entry.
The trusted root certificates of an enterprise can be distributed to all employees so that they can use the company PKI system. Certain Web browsers provide pre-installed root certificates to ensure that SSL certificates work immediately.
Access Manager uses the Online Certificate Status Protocol (OCSP) Internet protocol to maintain the security of a server and other network resources. OCSP is used for obtaining the revocation status of an X.509 digital certificate. OCSP specifies the communication syntax used between the server containing the certificate status and the client application that is informed of that status.
When a user attempts to access a server, OCSP sends a request for certificate status information. OCSP discloses to the requester that a particular network host used a particular certificate at a particular time. The server returns a response of "current", "expired," or "unknown." OCSP allows users with expired certificates a configurable grace period, during which they can access servers for the specified period before renewing.
OCSP messages are encoded in ASN.1 and are usually transmitted over HTTP. The request and response characteristic of OCSP has led to the term "OCSP responders" when referring to OCSP servers. With Access Manager, the computer hosting the Oracle Access Management Console is the OCSP responder.
An OCSP responder can return a signed response signifying that the certificate specified in the request is 'good', 'revoked' or 'unknown'. If OCSP cannot process the request, it can return an error code.
Figure 19-7 Native X509 Authentication Module
Description of "Figure 19-7 Native X509 Authentication Module"
Table 19-9 describes the requirements of the native X509 authentication module.
Note:
This standard Authentication Module is targeted for deprecation. Future enhancements will not be available in standard modules. Oracle strongly recommends using plug-in based modules.Table 19-9 X509 Authentication Module Definition
| Element | Description |
|---|---|
|
Name |
Identifies this module definition with a unique name. |
|
Match LDAP Attribute |
Defines the LDAP distinguished name attribute to be searched against given the X509 Cert Attribute value. For example, if the certificate subject EMAIL is me@example.com and it must be matched against the "mail" LDAP Attribute, an LDAP query must search LDAP against the "mail" attribute with a value "me@example.com (cn). Default: cn |
|
X509 Cert Attribute |
Defines the certificate attribute to be used to bind the public key (attributes within subject, issuer scope to be extracted from the certificate: subject.DN, issuer.DN, subject.EMAIL, for example). See Also. Match LDAP Attribute earlier in this table. |
|
Cert Validation Enabled |
Enables (or disables if not checked) X.509 Certificate validation. When enabled, the OAM Server performs the certificate validation (rather than having the WebLogic server intercept and validate the certificate before passing it to the OAM Server). Access Manager performs the entire certificate path validation. |
|
OCSP Enabled |
Enables (or disables when not checked) the Online Certificate Status Protocol. Values are either OCSP Enabled: true Note: OCSP Server Alias, OCSP Responder URL and OCSP Responder Timeout are required only when OCSP Enabled is selected. |
|
OCSP Server Alias |
An aliased name for the OSCSP Responder pointing to CA certificates in .oamkeystore file--a mapping between the aliased name and the actual instance name or the IP address of the OSCSP Responder instance. |
|
OCSP Responder URL |
Provides the URL of the Online Certificate Status Protocol responder. For example, OpenSSL Responder URL: http://localhost:6060 |
|
OCSP Responder Timeout |
Specifies the grace period for users with expired certificates, which enables them to access OAM Servers for a limited time before renewing the certificate. |
19.6.2 Viewing or Editing Native Authentication Modules
Users with valid Administrator credentials can use the following procedure to modify an existing authentication module. This includes changing the name of an existing module as well as changing other attributes.
Modify each authentication scheme that references the module you will change, to use another authentication module if needed.
Note:
By default, theLDAP module is used in the authentication scheme that protects the Oracle Access Management Console. To ensure Administrator access, the LDAP module must point to the User Identity Store that is designated as the System Store. If you change the designated System Store, be sure to change the LDAP Module to reference the newly designated System Store.To find, view, or edit an authentication module
-
From the Oracle Access Management Console, click Authentication Modules.
-
Open the desired Authentication Modules page.
-
On the Authentication Modules page, modify information as needed:
-
Kerberos Module: See Table 19-7
-
LDAP Module: See Table 19-8
-
X509 Module: See Table 19-9 and Table 19-15
-
-
Click Apply to submit the changes and close the Confirmation window (or close the page without applying changes).
-
Add the updated authentication module to authentication schemes (or change to another authentication module in each authentication scheme that references this module), as described in "Managing Authentication Schemes".
19.6.3 Deleting a Native Authentication Module
Users with valid Administrator credentials can use the following procedure to delete an authentication module.
The following procedure is the same whether you are deleting a custom authentication module or a native module.
In each authentication scheme that references the module to be deleted, specify another authentication module.
To delete an authentication module
-
From the Oracle Access Management Console, click Authentication Modules.
-
Optional: Open the module to verify this is the module to remove, then close the page.
-
Click the desired module name, then click the Delete button.
-
Confirm removal (or dismiss the confirmation window to retain the module).
19.7 Orchestrating Multi-Step Authentication with Plug-in Based Modules
Authentication involves determining which credentials a user must supply when requesting access to a resource, gathering credentials, and returning a response that is based on the results of credential validation. All authentication processing relies on an authentication module to define the rules governing requirements and transmission of information to the backend authentication scheme. All information collected by the plug-in and saved in the context is available to the plug-in through the authentication process. Context data can also be used to set cookies or headers in the user's login page.
Note:
Oracle strongly recommends using authentication plug-ins to create custom authentication modules.This section provides the following topics:
-
Comparing Simple Form and Multi-Factor (Multi-Step) Authentication
-
Example: Leveraging SubjectAltName Extension Data and Integrating with Multiple OCSP Endpoints
-
Creating and Orchestrating Plug-in Based Multi-Step Authentication Modules
See Also:
Oracle Fusion Middleware Developer's Guide for Oracle Access Management if you want to create custom authentication plug-ins.19.7.1 Comparing Simple Form and Multi-Factor (Multi-Step) Authentication
Simple form-based authentication relies on the default embedded or optional detached credential collector and Web forms that process user logins with Access Manager authentication mechanisms. Simple form-based authentication is the default and does not require additional configuration unless you want to customize forms. With simple form-based authentication:
-
All credentials are supplied in one simple form.
-
Upon credential validation and authentication, either success or failure status is returned.
-
Authentication can be retried upon failure.
See Also:
Oracle Fusion Middleware Developer's Guide for Oracle Access Management for details about customizing login pages and formsFor dynamic, multi-step authentication, Access Manager provides a number of plug-ins with which you can design and orchestrate your own customized authentication modules. Authentication plug-ins provide processing that meets your specific needs.
Also, Administrators can install multiple user identity stores for Access Manager. Each identity store can rely on a different LDAP provider. Each authentication plug-in can be configured to use a different user identity store.
Both the ECC and DCC handle complex multi-factor (multi-step, iterative, and variable) Authentication processing, where:
-
Not all required credentials are supplied at once.
-
Depending on the authentication status, PENDING state, expected credentials and context data are returned, expecting those credentials to be supplied in the next round.
-
Each intermediate step, submit required credentials and context data for the authentication engine, until a success or failure status returned.
-
The Authentication plug-in can have multiple steps configured.
Note:
If using multi-factor authentication, the UserIdentificationPlugin should be invoked in the last pass during the authentication process.Table 19-10 provides more information about these two forms of authentication.
Table 19-10 Simple Form versus Multi-Step Authentication
| Authentication Method | Description |
|---|---|
|
Simple form-based authentication |
Simple form-based authentication relies on Credential Collectors (both ECC and DCC) and Web forms that process user logins using Access Manager authentication mechanisms. This is the default and does not require additional configuration unless you want to customize forms. See Also: Oracle Fusion Middleware Developer's Guide for Oracle Access Management for details about customizing login pages and forms |
|
Multi-Step Authentication |
Multi-step authentication requires a custom authentication module composed of two or more authentication plug-ins that transmit information to the backend authentication scheme several times during the login process. All information collected by the plug-in and saved in the context will be available to the plug-in through the authentication process. Context data can also be used to set cookies or headers in the user's login page. Multi-Step authentication relies on:
See Also: "Adding PasswordPolicyValidationScheme to Authentication Policy for DCC" "Creating and Managing Step-Up Authentication" Oracle Fusion Middleware Developer's Guide for Oracle Access Management for details about custom authentication plug-ins |
19.7.2 About Plug-ins for Multi-Step Authentication Modules
You can create custom plug-in based authentication modules using existing Access Manager as described in this chapter. You can also create your own plug-ins, as described in the Oracle Fusion Middleware Developer's Guide for Oracle Access Management.
Plug-ins operate with either the default embedded credential collector (ECC) or the optional detached credential collector (DCC-enabled Webgate). Each authentication plug-in provides an individual piece of functionality that you can use alone or string together into a series of steps. The lifecycle of a plug-in centers around the ability to add and use the plug-ins to build features and work flows that act as extensions to the OAM Server. Each plug-in is deployed as a JAR file and each plug-in's configuration requirements must be given in XML format.
Note:
Standard (native) Authentication Modules are targeted for deprecation; future enhancements will not be available in the standard modules. Oracle strongly recommends using plug-in based modules as described in "Orchestrating Multi-Step Authentication with Plug-in Based Modules".Figure 19-8 shows out of the box plug-ins available from the Common Configuration section of the System Configuration tab on the Oracle Access Management Console. These plug-ins, and any that you create using the SDK and import, appear in a list when you add steps to build a custom authentication module.
The Name generally defines the component that relies on the plug-in. The Description is optional. The Type column indicates the purpose of the plug-in. Activation Status lets you know if this is active and ready to use.
See Also:
Oracle Fusion Middleware Developer's Guide for Oracle Access Management for details about building your own custom plug-ins. You can import new plug-ins, distribute, activate, deactivate, and remove custom plug-ins.Whether you use an Oracle-provided plug-in or create one of your own, adding a plug-in when you create a custom authentication module is the same.
Each custom module requires the following types of information:
-
General identifies the unique name and optional description for the individual plug-in.
-
Steps identify the specific plug-ins to use, and their execution order, based on the configuration details of each plug-in (including the user identity store to use).
-
Step Orchestration specifies the action to be taken on success or on failure or on error.
Additionally, when multi-factor authentication is used, the UserIdentificationPlugin should be invoked in the last pass during the authentication process.
Figure 19-9 shows a Custom Authentication Module within the Access Manager section of the System Configuration tree. Each module provides three subtabs where you enter information for the module.
Figure 19-9 Creating Custom Authentication Modules: General
Description of "Figure 19-9 Creating Custom Authentication Modules: General "
Table 19-11 describes the content of the General tab.
| Element | Description |
|---|---|
|
Name |
A unique name up to 60 characters. |
|
Description |
Optional; up to 250 characters. |
Clicking the Steps tab opens a fresh page where you can add a new step. When you add a new Step, the following dialog box appears. Information that you enter is used to populate the table and Details sections of the page.
Figure 19-10 Adding a Step and Associating a Plug-in
Description of "Figure 19-10 Adding a Step and Associating a Plug-in"
Table 19-12 describes the information required when adding a new step. Each step requires a plug-in and each plug-in requires specific details for proper operation.
Table 19-12 Add New Step Entries, Steps Results Table, and Details Section
| Element | Description |
|---|---|
|
Step Name |
The unique name you enter to identify this step, up to 60 characters. |
|
Description |
The optional description for this step, as entered when adding the step (up to 250 characters). |
|
Plugin Name |
The plug-in that you select for a particular step from the list of imported and activated plug-ins. See Also: Oracle Fusion Middleware Developer's Guide for Oracle Access Management for details about creating custom plug-ins. |
|
Step Details |
Plug-in configuration details must be specified to ensure proper operation. Details might differ depending the chosen plug-in and its requirements. See Also: Table 19-13. |
Table 19-13 describes the Plug-in Parameter Details required by Oracle-provided plug-ins. Absent from this table are the plug-in exceptions (those plug-ins with no initial parameters): KerberosTokenIdentifier, FedAuthnRequestPlugin, and FedUserAuthenticationPlugin.
Table 19-13 Parameter Details for Various Plug-ins
| Plug-in Parameter | Display Name | Description |
|---|---|---|
|
KEY_IDENTITY_STORE_REF |
Identity Store Name |
Most plug-ins require this attribute to ensure that the appropriate user identity store is called during authentication. The following plug-in uses only this property:
For additional Details required by plug-ins that employ this property, see:
|
|
CredentialCollectorPlugIn |
CredentialCollectorPlugIn |
This plugin allows the administrator to configure which credentials will be collected for authentication. Credentials to be collected are configured as step parameters. The plugin validates these parameters and renders the UI to collect the credentials. After user input, the plugin parses the credential parameters and builds the user context with credential objects. NOTE: Plugin error responses are set to the context if the credentials are invalid and the plugin returns failure. The plugin supports the collection of 4 credentials as step level parameters.
The following example illustrates how to collect a username and password.
CRED_PARAM_1=
{ID=KEY_USERNAME},{DISPLAY_NAME=KEY_USERNAME},{TYPE=text}
{ID=KEY_PASSWORD},{DISPLAY_NAME=KEY_PASSWORD},{TYPE=password}
Where ID, DISPLAY_NAME and TYPE are constants. |
|
Actiontype |
Action Type |
Indicates if the plugin wants to REDIRECT or FORWARD to the login page to collect credentials. |
|
loginPageURL |
Login Page URL |
The URL to which the user will be forwarded or redirected for credential collection. |
|
NO_OF_CREDENTIALS |
The number of credentials provided for the plugin instance. If the number of instances is more than 4, the user must update the oam-config file to add additional CRED_PARAMS as plugin parameters. |
|
|
UserIdentificationPlugIn |
UserIdentificationPlugIn |
This native plug-in maps the user to a specific LDAP user record. |
|
KEY_LDAP_FILTER |
LDAP Filter |
The search filter required to identify the user. Only standard LDAP attributes can be used when defining an LDAP search filter. |
|
KEY_SEARCHBASE_URL |
LDAP Searchbase |
The search base required for the query. The node in the directory information tree (DIT)) under which user data is stored; the highest possible base for all user data searches. |
|
UserAuthenticationPlugIn |
UserAuthenticationPlugIn |
This native plug-in authenticates the supplied username/password credentials against an LDAP directory. |
|
KEY_PROP_AUTHN_EXCEPTION |
Propagate LDAP errors |
Enables (or disables) propagation of LDAP errors. UserAuthenticationPlugIn employs this attribute. |
|
UserAuthnLevelCheckPlugin |
UserAuthnLevelCheckPlugin |
This native plugin shall determine if the user has been authenticated to the authentication level X - where the value of X is provided by the plugin parameter AUTHN_LEVEL_FOR_PLUGIN. For example, it checks the current Authentication Level of the user with the value specified. In addition, the plug-in specifies a list of parameters to collect depending on whether the Authentication Level check succeeded or failed. |
|
AUTHN_LEVEL_FOR_PLUGIN |
AUTHN_LEVEL_FOR_PLUGIN |
Specify the authentication level as an integer. Multiple steps can use UserAuthnLevelCheckPlugin. However, each Step must have a unique name and AUTHN_LEVEL_FOR_PLUGIN. |
|
UserPasswordPolicyPlugin |
UserPasswordPolicyPlugin |
|
|
PLUGIN_EXECUTION_MODE |
Mode of Operation |
The execution mode of plug-in (UserPasswordPolicyPlugin). Depending upon the configuration, this plug-in can operate either alone or with other default plug-ins. Values are one of the following:
|
|
POLICY_SCHEMA |
Policy Schema To Use |
Specifies the schema for the password service (used with UserPasswordPolicyPlugin). Only OAM10G is supported. Default: OAM10G |
|
NEW_USERPSWD_BEHAVIOR |
Force Password Change on First Login |
Configures retroactive behavior of the new-user password-policy. Used with UserPasswordPolicyPlugin.Values are either:
Default: FORCECHANGEPASSWORD |
|
DISABLED_STATUS_SUPPORT |
Disabled Account Status Support |
Specifies whether the disabled status is to be supported and acted upon in this password service. Valid values are either True or False. Default: TRUE |
|
URL_ACTION |
Password Management Action URL |
Specifies the URL to which the user is sent for password management. The type of servlet action needed for redirecting the user to the specific password page for expiry and warning pages. Values can be either:
Default: REDIRECT_POST |
|
FedUserProvisioningPlugin |
||
|
KEY_USER_RECORD_ATTRIBUTE_LIST |
List of User Attributes |
For Federation. Comma-separated list of assertion attributes required to create the user record. |
|
KEY_PROVIDERID_ATTRIBUTE_NAME |
Partner Attribute Name |
For Federation. The attribute name of the LDAP user record whose value will be set to the Partner's Identity Provider ID when provisioning the user. This field is optional and if empty, the Partner's Identity Provider ID will not be set in the LDAP user record. |
|
KEY_USERID_ATTRIBUTE_NAME |
User UserID Attribute |
For Federation. Name of the attribute in the assertion attributes that is used as the LDAP UserID. |
|
TAPIdentifyPlugIn |
||
|
KEY_TAP_RETURN_ATTRIBUTE |
Username Mapping Attribute |
Name of the attribute used for account linking by TAPIdentifyPlugIn. |
|
SequentialPlugInExecutionStrategy |
||
|
StrategyName |
Orchestration Strategy |
Name of the plugin orchestration strategy required by SequentialPlugInExecutionStrategy. |
|
KerberosTokenAuthenticator |
||
|
KEY_KEYTAB_FILE |
Location of Keytab file |
Name of the file containing Kerberos principals and encrypted keys required by KerberosTokenAuthenticator |
|
KEY_PRINCIPAL |
OAM Service Principal |
Your OAM Account SPN, required by KerberosTokenAuthenticator. |
|
KEY_KRB_CONFIG_FILE |
Location of Kerberos Configuration file |
Location of the Kerberos configuration properties file, required by KerberosTokenAuthenticator. |
|
KEY_DOMAIN_DNS2DN_MAP |
AD Domain DNS Names to DN Mapping |
Comma-separated list of Active Directory DNS Domains to DN mappings required by KerberosTokenAuthenticator. |
|
X509CredentialExtractor |
||
|
KEY_CERTIFICATE_ATTRIBUTE_TO_EXTRACT |
User Mapping Attribute |
X509 certificate Attribute to be used for user mapping required by X509CredentialExtractor. |
|
KEY_IS_CERT_VALIDATION_ENABLED |
Certificate Validation |
Enable or disable X.509 certificate validation, required by X509CredentialExtractor. |
|
TAPRequestPlugin |
||
|
TAPS2PVersion |
Integration Protocol Version |
Token version for Integration. |
|
TAPPartnerId |
Integration PartnerId |
Integration Partner Identifier. |
|
TAPChallengeURL |
Partner Integration Endpoint URL |
Remote Partner End Point URL. |
|
TAPUserAuthenticationPlugin |
||
|
KEY_USERNAME_ATTRIBUTE |
Username Mapping Attribute |
Name of the attribute used for account linking required by TAPUserAuthenticationPlugin |
|
KEY_CHECK_TOKEN_EXPIRY |
Enable Token Expiration Checking |
Enable or disable Integration token expiration. |
|
TenantDisambiguationPlugin |
||
|
KEY_FEDERATED_TENANTS |
FederatedTenantNames |
Optional names of tenants (comma separated) for whom federated authentication is enabled. Plugin will check with Federation engine if tenant names are not mentioned. |
|
RSA SecurID Plugin |
||
|
username |
Username Parameter |
Name of the username plugin parameter required by RSA SecurID Plugin. |
|
passcode |
Passcode Parameter |
Name of the passcode plugin parameter required by RSA SecurID Plugin. |
|
nexttoken |
Next Token Parameter |
Name of the next token plugin parameter required by RSA SecurID Plugin. |
|
newpin |
New PIN Parameter |
Name of the new pin plugin parameter required by RSA SecurID Plugin. |
|
confirmnewpin |
Confirm New PIN Parameter |
Name of the confirm new pin plugin parameter required by RSA SecurID Plugin. |
|
HTTPTokenExtractor |
||
|
KEY_HEADER_PROPERTY |
HTTP Header Names |
Comma separated list of HTTP Headers. See Section 19.7.7, "Configuring an HTTPToken Extractor Plug-in." |
|
KEY_COOKIE_PROPERTY |
HTTP Cookie Names |
Comma separated list of Cookies. See Section 19.7.7, "Configuring an HTTPToken Extractor Plug-in." |
Figure 19-11 illustrates the Steps subtab and Details section for a custom authentication module. When adding Steps, there is no data to display in the table. However, when you add one or more Steps the table the Details sections are populated.
Figure 19-11 Plug-in Based Authentication Module Steps and Details
Description of "Figure 19-11 Plug-in Based Authentication Module Steps and Details"
Figure 19-12 illustrates the Steps Orchestration subtab of a custom authentication module, which is populated by information for each defined step (and the action you choose for each operational condition).
Figure 19-12 Steps Orchestration for Plug-in Based Authentication Modules
Description of "Figure 19-12 Steps Orchestration for Plug-in Based Authentication Modules"
Table 19-14 describes the elements on the Steps Orchestration subtab. The lists available for OnSuccess, OnFailure, and OnError include the following choices:
-
success
-
failure
-
StepName (any step in the module can be selected as the action for an operational condition)
Table 19-14 Steps Orchestration Subtab
| Element | Description |
|---|---|
|
Initial Step |
Choose the starting step from those listed. The list includes only those steps defined for this module. |
|
Name |
Each step added to this module is listed by the name that was entered when the step was added. |
|
Description |
The optional description for this step, entered when this step was added. |
|
OnSuccess |
The action selected for successful operation. A list provides actions you can choose:
|
|
OnFailure |
The action selected for failure of this step. A list provides actions you can choose:
|
|
OnError |
The action selected for an error when executing this step. A list provides actions you can choose:
|
19.7.3 About Plug-in Based Modules for Multi-Step Authentication
Figure 19-13 lists the currently available native plug-in based Authentication modules.
Following topics describe several of the native Custom modules provided with pre-populated plug-ins. You can use these to orchestrate your own custom authentication modules:
See Also:
Use this plug-in when configuring Access Manager for Windows Native Authentication, as described in Chapter 50.
Figure 19-14 shows the KerberosPlugin module that is bundled with Access Manager 11g. This is a credential mapping module that matches the credentials (username and password) of the user who requests a resource to the encrypted "kerberos ticket".
Figure 19-15 shows the default steps and details. Figure 19-16 shows the orchestration of the steps and conditions.
Figure 19-15 Default KerberosPlugin Steps and Details
Description of "Figure 19-15 Default KerberosPlugin Steps and Details"
Figure 19-16 Default KerberosPlugin Steps and Orchestration
Description of "Figure 19-16 Default KerberosPlugin Steps and Orchestration"
Figure 19-17 shows the LDAPPlugin module that is bundled with Access Manager. By default, LDAPPlugin has 2 steps, shown in Figure 19-18. Figure 19-19 shows the default orchestration of steps for LDAPplugin.
Figure 19-18 Default LDAPPlugin Steps and Details
Description of "Figure 19-18 Default LDAPPlugin Steps and Details"
Figure 19-19 Default Orchestration of Steps for LDAPplugin
Description of "Figure 19-19 Default Orchestration of Steps for LDAPplugin"
Figure 19-20 shows the X509Plugin module that is bundled with Access Manager 11g. The X509Plugin is similar to the LDAPPlugin with additional properties that indicate which attribute of the client's X.509 certificate should be validated against the user attribute in LDAP. Figure 19-21 shows default steps and details for this plug-in. Figure 19-22 shows the default orchestration of steps for the X509Plugin.
Figure 19-21 X509Plugin Default Steps and Details
Description of "Figure 19-21 X509Plugin Default Steps and Details"
With this plug-in, the root and sub CA certificates must be added to the $DOMAIN_HOME/config/fmwconfig/amtruststore because the X509CredentialExtractor plug-in loads certificates from this location.
Table 19-15 lists the stepX509 values for Subject and Subject Alternative Names. Such processing is only supported when the X509Plugin is used.
See Also:
Table 19-15 X509 Step Details (KEY_CERTIFICATE_ATTRIBUTE_TO_EXTRACT)
| issuer.D | Subject |
|---|---|
|
subject. |
EDIPI Note: EDIPI refers to the Electronic Data Interchange Personal Identifier. |
|
subjectAltName. |
OTHER_NAME (FASC-N) Note: FASC-N refers to the Federal Agency Smart Credential Number. |
|
subjectAltName. |
RFC822_NAME |
|
subjectAltName. |
UNIFORM_RESOURCE_IDENTIFIER |
Figure 19-22 Default Orchestration for X509Plugin Steps
Description of "Figure 19-22 Default Orchestration for X509Plugin Steps"
See Also:
"Example: Leveraging SubjectAltName Extension Data and Integrating with Multiple OCSP Endpoints"Password Policy Validation Module and Plug-ins
Oracle provides a Password Policy Validation Module that employs the following plug-ins as individual steps in the authentication process:
-
User Identification Step
-
User Authentication Step
-
User Password Status Step
Figure 19-23 shows the Steps tab. Additional details follow the figure.
Figure 19-24 shows the Steps Orchestration page for the Password Policy Validation Module plug-ins, which is self explanatory.
19.7.4 Example: Leveraging SubjectAltName Extension Data and Integrating with Multiple OCSP Endpoints
Access Manager 11g support for personal identity verification (PIV) cards (a United States Federal smart card), is to use FASC-N and EDIPI attributes from the SubjectaltName extension to map the user during X.509 authentication. While multiple OCSP providers are not supported, you can use an OCSP Gateway or write a custom authentication plug-in that uses the OSDT OCSP APIs to validate against multiple OCSP providers.
The following functionality is available only with the X.509 Plug-in (not the X.509 Authentication module). The Plug-in configuration specifies the LDAP attribute to which the extracted attribute from the X.509 client certificate will be mapped.
Example: How to leverage the SubjectAltName extension data and integrate with multiple OCSP Endpoints
-
From the Oracle Access Management Console, click Authentication Modules, Custom Authentication Modules and X509plugin.
General Tab:
-
Name: CustomX509Plugin.
-
Description: Custom Plug-in for X509.
Steps Tab:
-
Click + to add a step to the plug-in.
-
Enter a Name and Description, then select the X509CredentialExtractor plug-in.
Step Details:
-
KEY_IS_CERT_VALIDATION_ENABLED
true. -
KEY_CERTIFICATE_ATTRIBUTE_TO_EXTRACT (Table 19-15):
subject.EDIPI, subjectAltName.OTHER_NAME (FASC-N), subjectAltName.RFC822_NAME, subjectAltName.UNIFORM_RESOURCE_IDENTIFIER -
Click the Save button.
Add Another Plug-in:
-
Click + to add a different plug-in.
-
Enter the Name, Description, and select UserIdentificationPlugin
Step Details for Second Plug-in:
-
Set KEY_IDENTITY_STORE_REF to the required identity store.
-
Add the LDAP filter to the KEY_LDAP_FILTER attribute. For example:
(&(uid= Unknown macro: {subject.CN} )(mail= Unknown macro: {subject.E} )) -
Add the user search base, if required, to the KEY_SEARCH_BASE_URL attribute.
-
Click the Save button.
-
Proceed to Step Orchestration tab (Step2).
-
-
Orchestrate Steps:
-
Initial Step: Select the X509CredentialPlugin Step from the drop down.
-
On Success: X509CredentialPlugin step, select the UserIdentificationPlugin Step from the drop down list.
-
On Success: UserIdentificationPlugin step, select
Successfrom the drop down list. -
On Failure: Select
Failurefor both X509CredentialPlugin and UserIdentificationPlugin steps. -
On Error: Select
Failurefor both X509CredentialPlugin and UserIdentificationPlugin steps. -
Click the Apply button and review the confirmation window stating that the plug-in has been created successfully.
-
-
Set up the Certificate Validation Module for Certificate Validation and Revocation using OCSP.
-
From the Oracle Access Management Console, click Certificate Validation.
-
In the Certificate Revocation list section, confirm that Enabled is checked, then click Save.
-
In the OCSP/CDP section, enable OCSP, enter the OCSP URL and the Subject of the OCSP Server's certificate, then click Save.
-
On the command line, use the Java keytool application to import the trusted certificates into the $DOMAIN_HOME/config/fmwconfig/amtruststore keystore, as trusted certificate entries.
Note:
Initially the keystore is empty; its password is set the first time the Java keytool application is used.
-
19.7.5 Creating and Orchestrating Plug-in Based Multi-Step Authentication Modules
Users with valid Administrator credentials can use the following procedure to create custom authentication plug-in module that uses one or more authentication plug-ins.
This procedure outlines general steps for any authentication module (with sample information to configure an authentication X509 module for use with the Online Certificate Status Protocol (OCSP) to maintain the security of a server and other network resources).
See Also:
Ensure that any user identity store associated with the module is running and includes the required user population.
To create a custom authentication module using bundled plug-ins
-
From the Oracle Access Management Console, click Authentication Modules.
-
Create New:
-
Click the Custom Authentication Module node.
-
Click the Create (+) button.
-
Add General Information: Name and optional Description. For example: CustomX509Plugin and Plugin for X509, respectively.
Click Apply to save general information.
-
-
Add Steps:
-
Click the Steps subtab.
-
Click the Add (+) button above the Steps table.
-
In the Add New Step dialog box, enter a unique Step Name and optional Description.
-
Browse for and select the desired plug-in name (X509CredentialExtractor, for instance) and click OK.
-
Confirm information in the results table.
-
Repeat b through e to add other steps until you have listed all required plug-ins for your module.
-
-
Define Step Details: Use appropriate values for requested parameters (Table 19-12, Table 19-13, Table 19-17, "Managing Custom Plug-ins Actions" and "Example: How to leverage the SubjectAltName extension data and integrate with multiple OCSP Endpoints"):
-
Click a StepName in the table to reveal required details, enter appropriate values for the requested details.
-
Validate User Cert using OCSP:
Confirm that KEY_IS_CERT_VALIDATION_ENABLED is set to
true.Add the certificate attributes to be extracted with KEY_CERTIFICATE_ATTRIBUTE_TO_EXTRACT (Table 19-15):
subject.EDIPI subjectAltName.OTHER_NAME (FASC-N) subjectAltName.RFC822_NAME subjectAltName.UNIFORM_RESOURCE_IDENTIFIER
-
Click the Save button.
-
Repeat to configure each step appropriately.
-
Ensure that users are provisioned in any user identity stores assigned in the steps.
-
-
Orchestrate Steps: See Table 19-14 as you perform following steps.
-
Click the Steps Orchestration subtab.
-
From the InitialStep list, choose the name of the first step to be used.
-
Select a StepName in the table.
-
From the OnSuccess List, choose a condition (success or failure) or a step name.
-
From the OnFailure List, choose the desired condition or a StepName.
-
From the OnError List, choose the desired condition or a StepName.
-
Repeat Steps c through f to orchestrate operations for each plug-in this module.
-
Review your orchestration.
-
-
Initiate Strategy Validation: Click Apply to initiate validation of your orchestration strategy:
-
Successful Strategy: The orchestration strategy is applied and the module is ready to include in an authentication scheme. Continue with Steps 9 and 10.
-
Invalid Strategy: Click OK in the Error box, then edit your OnSuccess, OnFailure, OnError strategies (or add or remove plug-ins) to correct the problem. Repeat this step until your strategy is successful.
-
-
In the navigation tree, confirm the new Custom Authentication Module is listed, and then close the page when you finish.
-
Use your custom module in an authentication scheme, as described in "Managing Authentication Schemes".
19.7.6 Creating and Managing Step-Up Authentication
This section describes how to define step-up authentication using plug-ins within a customized module. In this example, there are users who need standard level access to pages on the corporate portal and those who need access to sensitive information. For standard applications, authentication credentials include username and password. For sensitive applications, credentials include username, password, and a security code (the later obtained with a custom plugin that validates the code).
Figure 19-25 shows the steps within Step-up-Authn_Module. The processing that occurs with this customized step-up authentication module is driven by the steps and plug-ins described in Table 19-16. For more information, see Table 19-13.
Table 19-16 Steps and Plug-ins in a Customized Step-up Authentication Module
| Step # | Step Name | Plug-in Name | Description |
|---|---|---|---|
|
1 |
StandardLevelCheck-2 |
UserAuthnLevelCheckPlugin |
Configurable with the LevelCheck Rule and credentials parameters associated with the SUCCESS or FAILURE outcome resulting from the check. This plugin communicates with the authentication engine to determine the current authentication level of the user and compares it with the plugin level parameter AUTHN_LEVEL_FOR_PLUGIN. It interacts with a custom credential collector and checks the current Authentication Level of the user against the value specified. For example, if 2 is specified for X:
Specifies parameters to collect depending on whether the Authentication Level check succeeded or failed:
|
|
2 |
CollectUserNamePassword |
CredentialCollectorPlugin Flow must start with the Plug-in communicating the credential parameters to collect. The Action must support allowing the Server to mark parameters as immutable. |
This plugin interacts with the credential collector (CustomReadServlet) to allow the administrator to configure the credentials collected for authentication. Credentials to be collected are configured as step parameters. The plugin validates these parameters and renders the UI to collect them. The user provides the credentials that need to be collected in the step parameter. In this example, since in previous step user was not authenticated to level 2, he will be prompted to enter a user name and password.
Credentials to be collected should be specified in this format only for the credential collector to render the UI interface. Also specifies action on:
|
|
3 |
UserIdentificationProcess |
UserIdentificationPlugIn |
Out of the box plug-in that maps the user to a specific LDAP user record:
|
|
4 |
UserAuthenticationStep |
UserAuthenticationPlugin |
Out of the box plug-in that authenticates the supplied username and password credentials against an LDAP directory.
|
|
5 |
SensitiveLevelCheck-6 |
UserAuthnLevelCheckPlugin |
This plugin communicates with the authentication engine to determine the current authentication level of the user and compares it with the plugin level parameter AUTHN_LEVEL_FOR_PLUGIN. It interacts with a custom credential collector and checks the current Authentication Level of the user against the value specified. Specifies parameters to collect depending on whether the check succeeded or failed:
|
|
6 |
CollectSensitiveLevelCreds |
CredentialCollectorPlugin |
This plugin renders the UI for collecting credentials for level 6 authentication. This is similar to CollectUserNamePwd.
|
|
7 |
ValidateSensitiveLevelCreds |
SubjectSetPlugin |
This custom developed plug-in validates the security code against the server.
|
After defining and orchestrating plug-ins in an authentication module, you can use the module in an authentication scheme and use the scheme in a policy.
Task overview: Configuring Step-up Authentication
-
Create or edit a custom authentication module for step up authentication:
-
Define your custom authentication module based on the Steps shown here.
-
Orchestrate your Steps and Plug-ins as shown here and described in Table 19-16.
-
Sensitive Scheme: Create or edit an Authentication Scheme for sensitive applications that uses your customized step-up authentication module . For example:
See Also:
"Managing Authentication Schemes"
-
Lower-Level Scheme: Create or edit an Authentication Scheme for the lowest level applications using your customized step-up authentication module F.or example:
-
Sensitive Policy: Create or edit an Authentication Policy for sensitive-level resources using your customized step-up Authentication Scheme. For example:
-
Lower-Level Policy: Create or edit an Authentication Policy for the lowest level resources using your customized step-up Authentication Scheme. For example:
-
Verify: Verify your resources and the policies that protect them. For example:
19.7.7 Configuring an HTTPToken Extractor Plug-in
The following process should be followed to configure an HTTPToken Extractor plug-in.
-
Create a sample plug-in that will re-direct the user to the authenticating application.
The authenticating application will authenticate the user and set the user name in the HTTP header or cookie.
-
Create a custom authentication module that will access any applicable plug-ins.
For example, if you add the plug-in created in the previous step and the HTTPToken Extractor and User identification plug-ins, successful authentication occurs when the process for all three plug-ins has been successfully completed.
-
Add values for the header name and the user search filter properties.
The KEY_HEADER_PROPERTY is set in the HTTPToken Extractor plug-in while KEY_LDAP_FILTER is set in the UI plug-in. For example:
-
KEY_HEADER_PROPERTY =
cookieorheadername -
KEY_LDAP_FILTER = (uid={
cookieorheadername})
Note:
The user should be present in the data store which is being used. -
19.7.8 Configuring a JSON Web Token Plug-in
Use this plug-in when you need to protect REST or Web services using standard tokens. The JSON Web Token Plug-in issues both an OAM token and a Mobile and Social JWT token that can be used for Web services access. Oracle API Gateway and Oracle Web Services Manager can use this JWT token for Web services protection.
19.7.8.1 Understanding the JSON Web Token Plug-in
The following flow describes how this authentication plug-in can be used in deployments:
-
Configure the Oracle Access Management WebGate to use both OAM authentication and the JSON Web Token Plug-in.
-
When a user accesses a resource protected by the WebGate, the WebGate redirects the user to authenticate with Access Manager.
-
Upon authentication, the plug-in identifies which OAuth service end point should generate the JWT token. (OAuth service end points are unique and can be configured to point to a specific OAuth service profile within a specific Identity Domain.) Oracle Access Manager Mobile and Social creates the JWT token and the plug-in returns it as a cookie. (The cookie name can be configured in the plug-in configuration.)
-
The Web application intercepts the response and accesses the cookie so that it can be used later for Web service access. Depending on how the web application is deployed, there may be other options to retrieve the JWT token. The user can now access the Web resource.
-
When the Web resource needs to access a Web service, it extracts the OAM Mobile and Social JWT token and sends it to the Oracle API Gateway.
-
The Oracle API Gateway uses the Oracle OAuth Service REST API to validate the token. It then grants access to the Web service. The Oracle API Gateway can also validate the JWT token locally without making a remote call to the OAuth service.
Notes:
Currently there is not a mechanism to pass scope to the OAuth service while issuing a JWT token with OAM authentication. Consequently, the token should be considered to have global scope.Both the OAM token timeout and the JWT token timeout can be set to the same value to have the same validity. The OAM tokens and JWT token are not linked, so they cannot be terminated using single logout.
19.7.8.2 Configure the JSON Web Token Plug-In
Use these steps to configure the JSON Web Token (JWT) plug-in. You will be creating a custom authentication module.
-
Click Authentication Modules from the Launch Pad.
The Search Authentication Modules screen is displayed.
-
Click Create Authentication Module and from the drop down select Create Custom Authentication Module.
The General tab is displayed.
-
Enter a name (and optional description) for the custom authentication module.
For this example, we name the module JWTToken AuthnModule.
-
Click the Steps tab and the + (plus sign) to add a new step.
The Add New Step dialog is displayed. Three new steps will be added.
-
Specify a step name (and optional description), select an activated plug-in from the Plug-in name drop down list and click OK.
For this example, the values are StepUI and UserIdentificationPlugin. The flow parameters for that plug-in can be edited after it is added to the step
-
Enter values for the UserIdentificationPlugin parameters and click Save.
-
Click the + (plus sign) to add a second step, enter the name StepUA, select UserAuthenticationPlugin from the drop down list and click OK.
-
Enter values for the UserAuthenticationPlugin parameters and click Save.
-
Click the + (plus sign) to add a third step, enter the name StepOAuth, select OAuthTokenResponsePlugin from the drop down list and click OK.
-
Enter values for the OAuthTokenResponsePlugin parameters and click Save.
-
Click the Steps Orchestration tab to configure the orchestration of the steps in the following order.
-
StepUI
-
StepUA
-
StepOAuth
-
-
Click Apply and close the Custom Authentication Module tab.
-
Click Authentication Schemes from the Launch Pad.
-
Select LDAPScheme and click Duplicate.
A Copy of LDAPScheme screen displays.
-
Change the value of Name to JWTToken AuthnScheme and the value of Authentication Module to JWTToken AuthnModule.
-
Click Save.
-
Configure an Authentication policy with the newly defined JWTToken AuthnScheme Authentication Scheme.
19.8 Deploying and Managing Individual Plug-ins for Authentication
This section provides the following topics:
19.8.1 About Managing Your Own Authentication Plug-ins
Using information in the Oracle Fusion Middleware Developer's Guide for Oracle Access Management, custom authentication plug-ins can be created and used to define customized multi-step authentication modules.
After development, the plug-in must be deployed on the AdminServer, as a JAR file, which is validated automatically. After validation, an Administrator can configure and distribute the plug-in using the Oracle Access Management Console.
The server processes the XML configuration file within the plug-in JAR file to extract data about the plug-in. After the plug-in is imported, an Administrator can see and modify the various plug-in states based on information available from the AdminServer.
Figure 19-26 illustrates the Plug-ins Node under the Common Configuration section of the System Configuration tab, and the Plugins page. This Plugins page includes a tool bar with command buttons, most of which operate on the plug-in that is selected in the table. The table provides information about the existing custom plug-ins and their state. The Plugin Details section at the bottom of the page reflects configuration details for the selected plug-in the table.
Administrators control plug-in states using the command buttons across the table at the top of the Plugins page, as described in Table 19-17.
Table 19-17 Managing Custom Plug-ins Actions
| Action Button | Description |
|---|---|
|
Import Plugin... |
Adds the plug-in JAR file to the AdminServer $DOMAIN_HOME/oam/plugins and begins plug-in validation.
On Success: Status is reported as "Uploaded" (even if an OAM Server is down). If all registered OAM Servers report "Uploaded", then the status on AdminServer is also "Uploaded". On Failure: Status is reported as "Upload Failed" See Also: "About the Custom Plug-in Life Cycle" in the Oracle Fusion Middleware Developer's Guide for Oracle Access Management |
|
Distribute Selected ... |
On Success: Status is reported as "Distributed" (even if an OAM Server is down). If all registered OAM Servers report "Distributed", then the status on AdminServer is also "Distributed". On Failure: Status is reported as "Distribution Failed" |
|
Activate Selected ... |
After successful distribution the plug-in can be activated on all registered OAM Servers. Activation:
On Success: Status is reported as "Activated" (even if an OAM Server is down). If all registered OAM Servers report "Activated", then the status on AdminServer is also "Activated". On Failure: Status is reported as "Activation Failed" Following activation on all OAM Servers, the plug-in can be used and executed in any authentication module construction or orchestration. |
|
Deactivate Selected ... |
Following plug-in activation, an Administrator can choose to deactivate the plug-in: if the plug-in is not used in any authentication module or scheme, for example. The selected plug-in from all registered OAM Servers. Deactivate:
On Success: Status is reported as "De-activation" (even if an OAM Server is down). If all registered OAM Servers report "De-activation", then the status on AdminServer is also "De-activation". Plug-in configuration is removed from oam-config.xml. Note: After deactivation, the plug-in cannot be used or executed in any authentication module or orchestration. On Failure: Status is reported as "De-activation Failed" |
|
Remove Selected ... |
Following plug-in deactivation, an Administrator can delete the selected plug-in. During this process, Access Manager: Delete:
On Success: Status is reported as "Removed" (even if an OAM Server is down). If all registered OAM Servers report "Removed", then the status on AdminServer is also "Removed". Plug-in configuration is removed from oam-config.xml. On Failure: Status is reported as "Removal Failed" |
Table 19-18 describes elements in the Plugins status table.
Table 19-18 Plugins Status Table
| Element | Description |
|---|---|
|
Plugin Name |
Extracted from the Plugin name element of the XML metadata file. |
|
Description |
Extracted from the description element of the XML metadata file. |
|
Activation Status |
Reported activation status based on information from AdminServer. |
|
Type |
Extracted from the type element of the XML metadata file. |
|
Last Updated on |
Extracted from the creation date element of the XML metadata file. |
|
Last Updated by |
Extracted from the author element of the XML metadata file. |
In the Plugin Details section of the page, the Activation Status is maintained by the AdminServer, as shown in Table 19-18.
Depending on your plug-in, various configuration details are extracted from the configuration element of the XML metadata file to populate Configuration Parameters in the Plugin Details section. Examples are shown in Table 19-19; see also, Table 19-13.
Table 19-19 Example of Plugin Details Extracted from XML Metadata File
| Configuration Element | Description |
|---|---|
|
DataSource |
- <configuration>
- <AttributeValuePair>
<Attribute type="string" length="20">DataSource</Attribute>
<mandatory>true</mandatory>
<instanceOverride>false</instanceOverride>
<globalUIOverride>true</globalUIOverride>
<value>jdbc/CISCO</value>
<AttributeValuePair>
<configuration>
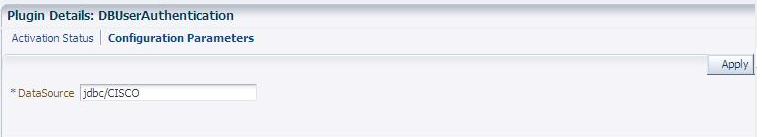 |
|
Kerberos Details |
Defines Kerberos details for this plug-in to use.  |
|
User Identification Details |
Defines the User Identity Store and filter details for this plug-in to use. 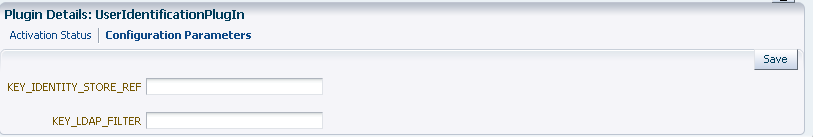 |
|
User Authentication Details |
Defines the User Identity Store for this plug-in to use. 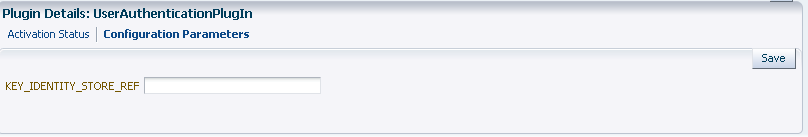 |
|
X.509 Details |
Defines the certificate details for this plug-in to use. 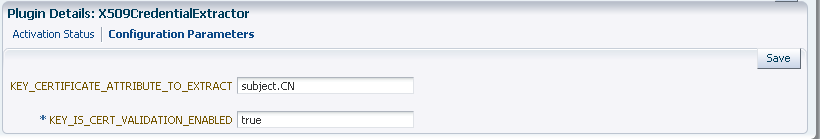 |
19.8.2 Making Custom Authentication Plug-ins Available for Use
Users with valid Administrator credentials can perform the following task to add, validate, distribute, and activate a custom plug-in.
Developing a custom plug-in as described in the Oracle Fusion Middleware Developer's Guide for Oracle Access Management
To make available for use a custom authentication plug-in
-
Import the Plug-in:
-
Log in to the Oracle Access Management Console.
https://hostname:port/oamconsole/
-
From the Oracle Access Management Console, click Plug-ins and then click Open from the Actions menu.
-
Click the Import Plugin button.
-
In the Import Plugin dialog box, click Browse and select the name of your plug-in JAR file.
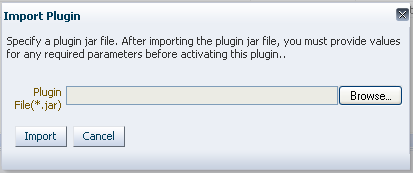
-
Review the message in the dialog box, then click Import.
The JAR file is validated as described in Oracle Fusion Middleware Administrator's Guide for Oracle Access Management.
-
-
Configure Parameters: Expand the Plugin Details section, click Configuration Parameters, and enter appropriate information as needed. For example:
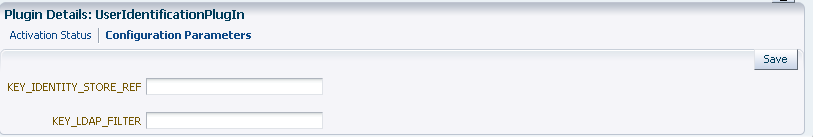
-
Distribute the Plug-in to OAM Servers:
-
In the Plugins table, click your plug-in name to select it.
-
Click the Distribute Selected button, then check its Activation Status.
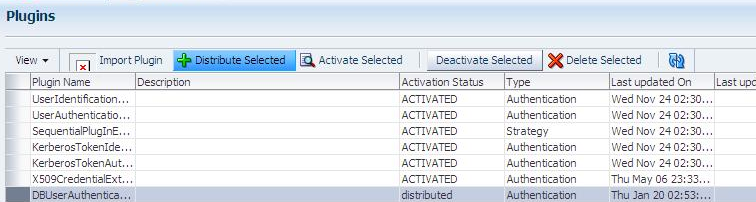
-
-
Activate the Plug-in (and the custom plugin implementation class) so it is ready to be used by OAM Server:
-
In the Plugins table, click your plug-in name to select it.
-
Click the Activate Selected button, then check its Activation Status.
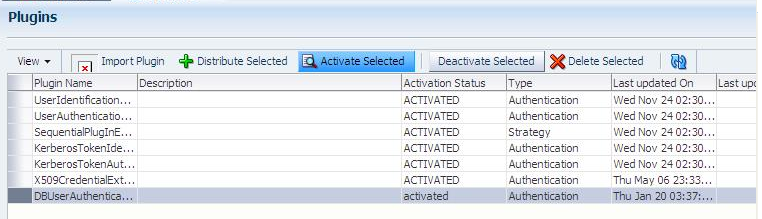
-
-
Perform the following tasks as needed:
19.8.3 Checking an Authentication Plug-in's Activation Status
Users with valid Administrator credentials can perform the following task to add, validate, distribute, and activate a custom plug-in.
Making Custom Authentication Plug-ins Available for Use
To check the activation status of a custom authentication plug-i
-
From the Oracle Access Management Console, click Plug-ins and then click Open from the Actions menu.
-
In the Plugins table, click the desired plug-in name to select it.
-
Server Instance Name: Expand the Plugin Details section and click Activation Status to display the location and status of the plug-in. For example:
-
Perform the following tasks as needed:
19.8.4 Deleting Your Custom Authentication Plug-ins
Users with valid Administrator credentials can use the following procedure to deactivate and then delete a custom plug-in.
When an Administrator deletes a custom authentication plug-in, its name is not removed from the list of plug-ins. To delete the plug-in (for the purpose of re-importing the same plug-in later), the Administration must stop the WebLogic Server and edit the oam-config.xml manually.
The plug-in must have been added and available in the console
To delete a custom authentication plug-in
-
Log in to the Oracle Access Management Console. For example:
https://hostname:port/oamconsole/
-
From the Oracle Access Management Console, click Plug-ins.
-
Deactivate the Plug-in: You must perform this before removing a plug-in.
-
In the Plugins table, click your plug-in name to select it.
-
Click the Deactivate Selected button, then check the plug-ins Activation Status.
-
-
Delete a Deactivated Plug-in:
-
In the Plugins table, click your plug-in name to select it.
-
Click the Delete Selected button.
-
Stop the WebLogic Administration Server, locate and edit oam-config.xml manually to remove the deactivated plug-in, and then restart the WebLogic Administration Server.
-
-
Perform the following tasks as needed:
19.9 Managing Authentication Schemes
Access to a resource or group of resources can be governed by a single authentication process known as an authentication scheme. An authentication scheme is a named component that defines the challenge mechanism required to authenticate a user. Each authentication scheme must also include a defined authentication module (standard or custom, as described in "Deploying and Managing Individual Plug-ins for Authentication").
When you register a partner (either using the Administration Console or the remote registration tool), the Application Domain that is created is seeded with a policy that uses the authentication scheme that is set as the default scheme. You can choose any of the existing authentication schemes as the default for use during policy creation.
You can also create a new authentication scheme, copy an existing definition to use as a template, modify a definition, or delete the definition. The copy uses a default name that is based on the original. For example, if you copy the scheme named KerberosScheme, the copy is named Copy of KerberosScheme.
This section is divided into the following topics:
19.9.1 About Authentication Schemes and Pages
All authentication schemes include the same elements with differing values. Figure 19-28 shows the default LDAPScheme page as an example. The Authentication Schemes navigation tree lists other default schemes that are delivered.
Table 19-20 provides information about each of the elements and values in any authentication scheme. Use the Set as Default button to make this the default scheme.
Table 19-20 Authentication Scheme Definition
| Element | Description |
|---|---|
|
Name |
The unique name for this scheme, which appears in the navigation tree. |
|
Description |
The optional description, up to 200 characters, that explains the use of this scheme. |
|
Authentication Level |
The trust level of the authentication scheme. This reflects the challenge method and degree of trust used to protect transport of credentials from the user. The trust level is expressed as an integer value between 0 (no trust) and 99 (highest level of trust). Note: Level 0 is unprotected. Only unprotected resources can be added to an Authentication Policy that uses an authentication scheme at protection level 0. For more information, see Table 20-1, "Resource Definition Elements". Note: After a user is authenticated for a resource at a specified level, the user is automatically authenticated for other resources in the same Application Domain or in different Application Domains, if the resources have the same or a lower trust level as the original resource. |
|
Default |
A non-editable box that is checked when the Set as Default button is clicked. |
|
Challenge Method |
One challenge method must be selected from those listed as available:
See Also: "About Challenge Methods" |
|
Challenge Redirect URL |
This URL declares the end point referencing the Credential Collector (ECC or DCC). For example: ECC: DCC: See Also: |
|
Authentication Module |
Identifies the pre-configured authentication module to be used to challenge the user for credentials. The module or plug-in specified here identifies the exact user identity store to be used.
See Also "Managing Native Authentication Modules" and "Orchestrating Multi-Step Authentication with Plug-in Based Modules". |
|
Challenge URL |
This URL is associated with the designated Challenge Method (FORM, for instance). FORM-based, out of the box authentication scheme (LDAPScheme and LDAPNoPasswordValidationScheme), Challenge URL is "/pages/login.jsp". The context type and context values are used to build the final URL. X509-based Challenge URL takes the form: Note: The default Challenge URL is based on the credential collector embedded with the OAM Server (ECC). If you are using detached credential collector-enabled Webgate and related DCC pages installed with Webgate, see "Configuring 11g WebGates and Authentication Policy for DCC". |
|
Challenge Parameters |
Supported challenge parameters are discussed in "About Challenge Parameters for Authentication Schemes". |
|
For schemes using Challenge Method FORM, X509, or DAP |
Only Schemes with the Challenge Method of FORM, X509, or DAP include the following additional elements. Other schemes use defaults that require no change. |
|
Context Type |
Used to build the final URL for the Embedded Credential Collector (ECC only, DCC does not use this) based on the following possible values:
|
|
Context Value |
Used to build the final URL for the credential collector. The default value is /oam. |
Only Schemes with the Challenge Method of FORM, X509, or DAP include additional elements described at the end of Table 19-20. All custom login pages must meet the following requirements:
-
Custom login pages require two form fields (username and password). Access Manager supports custom forms as described in Oracle Fusion Middleware Developer's Guide for Oracle Access Management.
-
CustomWar and external context types, require logic within the custom login page to perform the following two tasks:
-
Send back the request ID the page received from the Access Manager server. For example:
String reqId = request.getParameter("request_id"); <input type="hidden" name="request_id" value="<%=reqId%>"> -
Submit back to the OAM Server the end point, "/oam/server/auth_cred_submit". For example:
<form action="/oam/server/auth_cred_submit"> or "http://oamserverhost:port/oam/server/auth_cred_submit".
-
For more information, see the following topics:
See Also:
Oracle Fusion Middleware Developer's Guide for Oracle Access Management for details about customizing login pages and messages.19.9.1.1 Pre-configured Authentication Schemes
Table 19-21 identifies the pre-configured authentication schemes available with Access Manager and some specific details of each. For more information about challenge parameters, see Table 19-21.
Table 19-21 Pre-configured Authentication Schemes
| Scheme Name | Specifications | Purpose |
|---|---|---|
|
AnonymousScheme |
Authentication Level: 0 Challenge Method: None Authentication Module: AnonymousModule |
Leaves unprotected specific Access Manager URLs and allows users to access such URLs without a challenge. Users are not challenged and do not need to enter their credentials. Note: Authentication Level 0 is for public pages. Oracle recommends that you do not use Level: 0 in a custom authentication scheme. Also: When a resource is protected by AnonymousScheme, it is not displayed in a session search. |
|
BasicFAScheme Only for Oracle Fusion Applications |
For Fusion Applications |
For specific information about this authentication scheme, refer to the Oracle Fusion Applications Technology Library located on the Oracle Technology Network (OTN) web site: |
|
BasicScheme |
Authentication Level: 1 Challenge Method: Basic Authentication Module: LDAP |
Protects Access Manager-related resources (URLs) for most directory types. Note: Authentication Level 1 is only one step higher than 0 public pages. Oracle recommends that you do not use Level: 1 in a custom authentication scheme. |
|
BasicSessionlessScheme |
Authentication Level: 1 Challenge Method: Basic Authentication Module: LDAP |
Primarily used for clients that don't support URL redirect or cookies. Challenge Parameters: CookieLessMode=true Note: Authentication Level 1 is only one step higher than 0 public pages. Oracle recommends that you do not use Level: 1 in a custom authentication scheme. |
|
FAAuthScheme Only for Oracle Fusion Applications |
Authentication Level: 2 Challenge Method: FORM Authentication Module: LDAP Context: customWar Context Value: /fusion_apps |
For specific information about this authentication scheme, refer to the Oracle Fusion Applications Technology Library located on the Oracle Technology Network (OTN) web site: |
|
FederationMTScheme Only for Oracle Fusion Applications |
Authentication Level: 2 Challenge Method: FORM Authentication Module: FederationMTPlugin Context Type: customWar Context Value: /fusion_apps Challenge Parameters: initial_command=NONE is_rsa=true |
For specific information about this authentication scheme, refer to the Oracle Fusion Applications Technology Library located on the Oracle Technology Network (OTN) web site:
See Also: "About Challenge Parameters for Authentication Schemes". |
|
FederationScheme Only for Identity Federation 11.1.2. |
Authentication Level: 2 Challenge Method: FORM Authentication Module: FederationPlugin Context Type: customWar Context Value: /oam Challenge Parameters: initial_command=NONE is_rsa=true |
See Also: Part V, "Managing Oracle Access Management Identity Federation". Note: With Oracle Identity Federation 11.1.1, use OIFScheme as described in the Oracle Fusion Middleware Integration Guide for Oracle Access Manager. |
|
KerberosScheme |
Authentication Level: 2 Challenge Method: WNA Authentication Module: Kerberos Context Type: customWar Context Value: /fusion_apps |
Protects Access Manager-related resources (URLs) for most directory types based on a Windows Native Authentication challenge method and valid WNA credentials in Active Directory. |
|
LDAPNoPasswordValidationScheme |
Authentication Level: 2 Challenge Method: FORM Authentication Module: LDAPNoPasswordAuthModule Context Type: default Context Value: /oam Note: LDAPNoPasswordAuthModule is similar to the DAP (asserter) mechanism. See Also OAM10gScheme, later in this table. |
Protects Access Manager-related resources (URLs) for most directory types based on a form challenge method. Used with the Identity Asserter for SSO when you have resources in a WebLogic Container. For details, see the Oracle Fusion Middleware Application Security Guide. |
|
LDAPScheme |
Authentication Level: 2 Challenge Method: FORM Authentication Module: LDAP Context Type: customWar Context Value: /fusion_apps |
Protects Access Manager-related resources (URLs) for most directory types based on a form challenge method. |
|
OAAMAdvanced |
Authentication Level: 2 Challenge Method: FORM Authentication Module: LDAP Context Type: external |
Protects OAAM-related resources with an external context type. This authentication scheme is used when complete integration with OAAM is required. A Webgate must front ending the partner. |
|
OAAMBasic |
Authentication Level: 2 Challenge Method: FORM Authentication Module: LDAP Context Type: default Context Value: /oam Challenge Parameters oaamPostAuth=true oaamPreAuth=true |
Protects OAAM-related resources with a default context type. This scheme should be used when basic integration with OAAM is required. Here, advanced features like OTP are not supported. This is more of an integration when mod_osso is used as the agent. |
|
OAM10gScheme |
Authentication Level: 2 Challenge Method: OAM10G Authentication Module: LDAPNoPasswordAuthModule See Also LDAPNoPasswordValidationScheme, earlier in this table. enableCoexistMode and disableCoexistMode in the Oracle Fusion Middleware WebLogic Scripting Tool Command Reference. |
Facilitates integration and coexistence with Oracle Access Manager 10g. In the coexistence mode, Oracle Access Manager 10g is the authenticator and Access Manager 11g is the asserter. This scheme requires challenge mechanism OAM10G, specifically for OAM10g coexistence with OSSO as described in "OAM10G". |
|
OAMAdminConsoleScheme |
Authentication Level: 2 Challenge Method: FORM Authentication Module: LDAP Context Type: default Context Value: /oam |
Authentication scheme for Oracle Access Management Console. |
|
OICScheme |
Authentication Level: 2 Challenge Method: DAP Authentication Module: TAPModule Context Type: External Challenge Parameters: TAPPartnerId=RPPartner MatchLDAPAttribute=mail |
Access Manager uses this scheme to delegate authentication to Mobile and Social services and redirects the user to the Mobile and Social login page for authentication. See Also: Part V, "Managing Oracle Access Management Mobile and Social" |
|
OIFScheme Only for Oracle Identity Federation 11.1.1. For Identity Federation 11.1.2, use FederationScheme. |
Authentication Level: 2 Challenge Method: DAP Authentication Module: DAP Context Type: External |
This scheme delegates authentication to OIF, after which, Oracle Identity Federation sends back a token that is asserted by the OAM Server as described in the Oracle Fusion Middleware Integration Guide for Oracle Access Manager. The Delegated Authentication Protocol (DAP) challenge method is used to delegate authentication to a third-party (OIF in this case). Challenge Parameters: TAPPartnerId=OIFDAPPartner See Also: "About Challenge Parameters for Authentication Schemes". |
|
OIMScheme |
Authentication Level: 1 Challenge Method: FORM Authentication Module: LDAP Context Type: default Context Value: /oam |
Protects Oracle Identity Manager-related resources with a default context type. Note: When integrating OAM and OIM, OAM downgrades the user's authentication level when any of the following is detected: password expiry forced password change challenge setup not done This enables the user to access the pages only after performing necessary operations in the identity management (OIM) page to which the user is redirected. At Level 1, only public and OIM pages for the required operations can be accessed. Note: Authentication Level 1 is only one step higher than 0 public pages. Oracle recommends that you do not use Level: 1 in a custom authentication scheme. |
|
OSSOCoexistMigrateScheme |
Set as the Default authentication scheme for environments that have been migrated from OSSO 10g to Access Manager 11g. See Also: Oracle Fusion Middleware Upgrade Guide for Oracle Identity and Access Management. |
|
|
PasswordPolicyValidationScheme |
Authentication Level: 2 Challenge Method: FORM Authentication Module: Password Policy Validation Module Context: External |
Enables password policy evaluation. |
|
TAPResponseOnlyScheme |
Authentication Level: 2 Challenge Method: DAP Authentication Module: DAP |
|
|
TAPScheme |
Authentication Level: 2 Challenge Method: DAP Authentication Module: DAP Context Type: External |
To use TAPScheme for IDM product resources in the IAM Suite Application Domain, Protected HigherLevel Policy, the following configuration must be done in addition to changing the Authentication Scheme.
Challenge Parameters: TAPPartnerId=TAPPartnerName |
|
X509Scheme |
Authentication Level: 5 Challenge Method: X509 Authentication Module: X509 |
This authentication scheme is a certificate-based user identification method. To use this method, a certificate must be installed on the user's browser and the Web server must be SSL-enabled. Note: This scheme relies on SSL to deliver the use's X.509 certificate to the OAM Server. |
19.9.1.2 About Challenge Methods
Authentication involves determining what credentials a user must supply when requesting access to a resource, gathering credentials over HTTP, and returning an HTTP response that is based on the results of credential validation. Access Manager provides the following credential challenge methods for use in an authentication scheme:
This authentication challenge uses an HTML form with one or more text input fields for user credentials. In a typical form-based challenge, users enter a user name and password in two text boxes on the form. The most common credential choices are user name and password; however, you can use any user attributes: for example, user name, password, and domain.
A Submit button posts the content of the form. When the user clicks the Submit button, the form data is posted to the Web server. OAM and OSSO Agents intercept and process the form data. Upon validation of the user credentials collected in the form, the user is authenticated.
Note:
This challenge method relies on an LDAP Authentication Module and the user identity store associated with that module.You might want to use form-based authentication challenge for reasons such as:
-
A consistent user experience: Using form-based login and a standardized logout means that the user experience for login and logout features will be consistent across browsers.
-
A Custom Form: You can apply your organization's look and feel in the authentication process.
For example, a custom form can include a company logo and a welcome message instead of the standard user name and password window used in Basic authentication.
-
Additional Information: You can gather additional information at the time of login.
-
Additional Functionality: You can provide additional functionality with the login procedure, such as a link to a page for lost password management.
This built-in Web server challenge mechanism requires a user to enter her login ID and password. The credentials supplied are compared to the user's definition in the LDAP directory server. Thus, a Basic challenge relies on the LDAP Authentication Module and user identity store associated with that module.
Note:
If a URL is protected by Access Manager using Basic Authentication with OID configured as the identity store, OID defined users can not log in. To resolve this, add the following line before the closing</security-configuration> tag in the config.xml file.
<enforce-valid-basic-auth-credentials>false </enforce-valid-basic-auth-credentials>
With the X509 certificate challenge method, a user's browser must supply an X.509 digital certificate over SSL to the OAM Server through the Agent to perform authentication.
Note:
X509 is the challenge method for the X509Scheme. The user's organization can determine how to obtain a certificate.The X.509 client certificate must be verified against the trusted CAs in the keystore used by OAM Proxy and OAM Servers to ensure the validity of X.509 Client certificate for authentication.
The following attributes of the X.509 certificate can be validated against the user identity store associated with Access Manager:
-
SubjectDN
-
SubjectUniqueID
-
Mail
-
CN
To acquire the user entry, the X509 Authentication Module takes the attribute name of the X.509 certificate to be validated and the LDAP attribute against which the search will be launched. The expected result is the single user entry matching the criteria. If the search returns no user entry, or more than one entry, authentication fails. Authentication scheme parameters are located in oam-policy.xml.
Note:
For X509 authentication, Administrators must configure the Oracle HTTP Server as a reverse proxy (or a server with the wl-proxy plug-in). The Oracle HTTP Server must be configured in two way SSL Mode to acquire X.509 certificate for authentication. Oracle HTTP Server can also be configured for CRL verification.The online certificate status protocol (OCSP) capabilities are also provided. Any certificate passed for X.509 certificate-based authentication is validated using an OCSP request. Administrators can configure the system to communicate with one or more OCSP servers to retrieve the certificate status.
The X509 Authentication Module configuration for the OCSP responder URL indicates whether OCSP validation is to be done. The value, if specified, indicates the URL for validation of the X.509 client certificate using OCSP. No value indicates no OCSP validation.
Uses Windows Native Authentication with Active Directory, and the Kerberos Authentication Module.
Note:
The KerbScheme relies on the WNA challenge method and Kerberos Authentication Module.See Also:
Chapter 50 for details about integration with Windows Native AuthenticationThe challenge method of None means that users are not challenged and do not need to enter their credentials. This is used in the AnonymousScheme authentication scheme, which allows users to access Access Manager-specific URLs that you do not want to protect.
The Delegated Authentication Protocol (DAP) challenge method is required for OIFScheme (Oracle Identity Federation 11.1.1 integration) with the DAP authentication module and external context type (Table 19-20). The DAP challenge mechanism indicates that Access Manager does an assertion of the token that it receives, which differs from the standard challenge "FORM" mechanism with the external option.
DAPModule is an assertion module, though it is specialized for this one application and does not appear in the list of Authentication Modules in the Oracle Access Management Console. This integration replaces OSSO 10g with Access Manager 11g, with no changes from the Identity Federation side.
The DAP challenge mechanism delegates authentication to a third party (Identity Federation in this case). The challenge_url points to the Identity Federation Server URL. When a resource is protected by this scheme, the OAM Server redirects to the Identity Federation Server URL for credential collection. OAM Server does not perform the credential collection or validation in this case. Identity Federation collects the credentials, authenticates the user against its identity store and returns an assertion token to the OAM Server consisting of the username. Access Manager receives and decrypts this token, checks whether the user is a valid user in the default identity store for Oracle Access Management. If the user is valid, Access Manager gives access to the resource.
The DAPToken is encrypted and decrypted with a key that is shared between Access Manager and Identity Federation. The DAPToken is built from the Access Manager side.
The Identity Federation Administration EM Console provides a way to generate the keystore containing the encryption keys that will be used to secure communications between the Access Manager and Identity Federation. Access Manager provides a WLST command (registerOIFDAPPartner), that takes the keystore location generated by the Identity Federation store and retrieves the keys and stores it on the Identity Federation side.
This mechanism is created for Oracle Access Manager 10g coexistence with OSSO 10g. The OAM10G method always acts as the authentication and authorization provider and is required for OAM10gScheme with the LDAPNoPasswordAuthModule to facilitate trust when you have Oracle Access Manager 10g protecting a domain that also includes an OSSO 10g integrated classic application (Portal, Disco, and so on).
OSSO10g is protected with OAM10G challenge method through Webgate; OAM10G always acts as the authentication and authorization provider.
Facilitating Integration: The OSSO 10g integrated classic applications can be upgraded to Access Manager, which then acts only as an asserter. Access Manager creates the tokens that mod_osso can consume so that access can be provided to these applications. The mod_osso applications are protected by the new "OAM10gScheme". There is a Webgate front ending the OAM Server and configured against the 10g Access Server.
Setup: When the resource is accessed, Webgate intercepts the request and sends it to the 10g Access Server for authentication. Oracle Access Manager 10g collects the credentials, validates it against its identity store, and sets the username as a header variable (OAM_REMOTE_USER). The request now goes to the OAM Server which uses the OAM10gScheme to locate the username in the header variable. Access Manager retrieves the header variable and asserts the presence of the user against the primary identity store. If present, the required cookies (OAM_ID) are generated and redirected to the resource.
See Also:
-
OAM10gScheme in Table 19-21
-
enableCoexistModeanddisableCoexistModein the Oracle Fusion Middleware WebLogic Scripting Tool Command Reference
19.9.1.3 About Challenge Parameters for Authentication Schemes
Challenge parameters are short text strings consumed and interpreted by Webgates and Credential Collector modules to operate in the manner indicated by those values.
The syntax for specifying any challenge parameter is:
<parmatername>=<value>
This syntax is not specific to any Webgate release (10g versus 11g). Authentication schemes are independent of Webgate release.
Table 19-22 identifies the pre-configured schemes with challenge parameters.
Table 19-22 Challenge Parameters in Pre-configured Schemes
| Pre-configured Schemes | Challenge Parameter |
|---|---|
|
BasicSessionlessScheme |
CookieLessMode=true Primarily used for clients that do not support URL redirect or cookies. |
|
FederationMTScheme |
initial_command=NONE Primarily used for Fusion Applications that support multiple factor authentication. is_rsa=true Used with RSA multi-step authentication, as described in Chapter 49, "Integrating RSA SecurID Authentication with Access Manager" and the Oracle Fusion Middleware Developer's Guide for Oracle Access Management. |
|
FederationScheme For Identity Federation 11.1.2.only. Use OIFScheme for Oracle Identify Federation 11.1.1. |
Primarily used for clients that do not support URL redirect or cookies. Context Value: /fusion_apps Challenge Parameters: initial_command=NONE is_rsa=true Primarily used for clients that do not support URL redirect or cookies. |
|
OAAMBasic |
oaamPostAuth=true oaamPreAuth=true Protects OAAM-related resources. These parameters should be used when basic integration with OAAM is required. |
|
OIFScheme For Oracle Identify Federation 11.1.1 only. Use FederationScheme for Identity Federation 11.1.2. |
TAPPartnerId=OIFDAPPartner This scheme delegates authentication to Oracle Identity Federation 11.1.1, after which, Federation sends back a token that is asserted by the OAM Server. |
|
TapScheme |
TAPPartnerId=TAPPartnerName |
An authentication scheme can collect context-specific information before submitting the request to the Access Server. Context-specific information can be in the form of an external call for information. Table 19-23 lists user-defined challenge parameters you can use in Authentication Schemes.
Table 19-23 User-Defined Challenge Parameters for Authentication Schemes
| Challenge Parameter | Definition |
|---|---|
|
initial_command=NONE |
Required to enable the plug-in to indicate which credentials are to be collected. For example, for Form-based authentication, the framework typically expects to collect "username" and "password" (submitted from the login page). However, you might want credentials from different fields of the login page; "form_username" and "form_password" for example. Setting this challenge parameter shifts initial control from the login page to the plug-in, which decides the parameters to collect from the login page then appropriately forwards or redirects to the page. Default: blank (not set) |
|
action= |
The actions parameter identifies the URL to which the HTML form is posting when you do not want to use the hard coded ECC default Note: ECC does not use the |
|
creds= DCC Only |
Supported by the detached credential collector (DCC) only. In the following 11g example, username and password are the names of relevant fields in the login form: creds=username password NOTE: Format of this challenge parameter has changed since the 10g release. The Web server source (server parameter) takes precedence over other sources. This prevents the request data, which is under control of the user, from overriding Web server data. For example, a remote_user cookie sent from a user will not override a remote_user variable set by the Web server Generally, when the user submits a login form that is protected by an authentication scheme with a Form-based challenge method, the DCC processes the credentials that were specified with this For forms using METHOD=POST processing, the browser sends a POST request to the Web server with the credential data from the form in the body of the request. If the form uses METHOD=GET, the browser sends a GET request with query string parameters with the same names as those specified on the creds parameter. Oracle recommends that you use POST processing, if possible. Note: You can specify the |
|
extracreds= DCC Only |
Supported by the DCC only. Specifies optional parameters which, if present, are made available to the authentication plug-in for collection during each iteration of a multi-step authentication using the DCC. The extracreds=[{any | cookie | header | server | query | post}:] <name> |
|
OverrideRetryLimit=0 |
The number of tries that can override the RetryLimit for login. The value must be a positive integer. A value of zero (0) disables this function. |
|
ChallengeRedirectMethod |
Authentication POST data preservation parameter for both the embedded credential collector (ECC) and the detached credential collector (DCC). Value: GET|POST|DYNAMIC Note: Preference is given first to the Authentication Scheme containing this parameter; second to the Webgate providing this user defined parameter. Otherwise, default behavior is Dynamic. |
|
MaxPreservedPostDataBytes |
Configure this Authentication Scheme challenge parameter (or user-defined Webgate parameter) for authentication POST-data preservation. Default: 8192 bytes Note: Preference is given first to the Authentication Scheme containing this parameter; second to the Webgate providing this user-defined parameter. Otherwise, default behavior is 8192 bytes. This parameter defines the maximum length of POST data that Webgate can preserve. If the size of inbound raw user POST data (or encrypted post data after processing), crosses this limit, POST data is dropped and the existing authentication flow continues. The event is logged as usual. |
|
MaxPostDataBytes= DCC Only |
Configure this Authentication Scheme challenge parameter to restrict the maximum number of bytes of POST data that is submitted as user credentials and sent to the OAM Server. Configure this challenge parameter for POST-data preservation by the DCC only to limit the maximum size of the POST data that can be posted as credentials on the form and sent to the OAM Server. DCC compares the value of the content-length header with the limit set. Default: 8192 bytes This challenge parameter requires a positive integer value. See Also: Table 16-2, "User-Defined WebGate Parameters" |
|
ssoCookie= |
Controls the OAMAuthnCookie cookie, as described in "Configuring Challenge Parameters for Encrypted Cookies". Default: ssoCookie=httponly ssoCookie=Secure Disable either setting: ssoCookie=disablehttponly ssoCookie=disableSecure Note: These parameters are configured differently depending on your credential collector configuration.
See Also: Table 19-30, "Challenge Parameters for 10g/11g Encrypted Cookies" |
|
miscCookies= |
Controls other miscellaneous Access Manager internal cookies. By default, httponly is enabled for all other (miscellaneous) cookies. Default: miscCookies=httponly miscCookies=Secure Disable either setting: miscCookies=disablehttponly miscCookies=disableSecure Note: These parameters are configured differently depending on your credential collector configuration.
See Also: Table 19-30, "Challenge Parameters for 10g/11g Encrypted Cookies" |
|
DCCCtxCookieMaxLength= DCC Only |
Defines the maximum length of the DCC cookie. Default: 4096 See Also: TempStateMode in this table for more information. |
|
TempStateMode= |
Controls how the DCC stores the OAM Server state (cookie or form) as specified with the parameter's value:
Note:
To update With ECC: The serverRequestCacheType dictates whether OAM Server stores its state in memory(BASIC) or not (FORM or COOKIE). serverRequestCacheType = COOKIE or FORM only makes difference when ECC is used. OAM Server stores its state in a request token, which ECC keeps in a cookie or hidden form field as specified with the parameter: serverRequestCacheType=COOKIE, for example. With DCC: There is no difference between serverRequestCacheType=COOKIE or FORM. TempStateMode controls how the DCC stores the OAM Server state (cookie or form) as specified with the parameter's value: TempStateMode=cookie, for example. With the DCC, POST data restoration with a Form-based Authentication Scheme requires the challenge parameter TempStateMode=form. See Also: |
19.9.2 Understanding Multi-Level and Step-Up Authentication
This section provides the following topics:
19.9.2.1 About Multi-Level and Step-Up Authentication
Every authentication scheme requires a strength level. The higher the number, the more more secure the authentication mechanism; the lower the number, the less stringent the scheme. For example:
-
LDAPScheme authLevel=1
-
KerbScheme authLevel=3
Note:
Multi-level authentication does not affect, negate, or alter X.509 certificate authentication.SSO capability enables users to access more than one protected resource or application with a single sign in. After a successful user authentication at a specific level, the user can access one or more resources protected by one or more Application Domains. However, the authentication schemes used by the Application Domains must be at the same level (or lower). When a user accesses a resource protected with an authentication level that is greater than the level of his current SSO token, he is re-authenticated. In the step-up case, the user maintains his current level of access even if failing the challenge presented for the higher level. This is "additional authentication".
Note:
A user who is authenticated to access resources at level 3, is eligible to access resources protected at levels less than or equal to 3. However, if the user is authenticated to access resources at level 2 and then attempts to access resources protected by level 3, the user is asked to re-authenticate (this is known as step-up authentication).Access Manager policies allow different resources of the same application to be protected with different authentication levels.
In such cases, the application must enforce the Level and send the Dynamic Directive to mod_osso for re-authentication. On receiving the Dynamic Directive, mod_osso will redirect to Access Manager for re-authentication at the appropriate level.
Both agent types redirect the user to the OAM Server to authenticate again. The challenge is presented according to the level of the authentication scheme configured in the policy for the resource.
Registered agents detect the authentication level as follows:
-
OAM Agents receive an insufficient level error message from the OAM Server, as described in "Detection of Insufficient Authentication Level by OAM Agent".
-
mod_osso detects the authentication level from dynamic directives, as described in Multi-Level Authentication Processing with 10g OSSO Agent.
Note:
mod_osso delegates authentication to Access Manager. Oracle recommends that mod_osso-protected resources be protected with Access Manager authentication levels. the mod_osso plug-in does not support two resources on the same application with a different trust level.
See Also:
Oracle Fusion Middleware Integration Guide for Oracle Identity Management Suite; for example, the chapter Integrating Access Manager and Oracle Adaptive Access Manager. The user was already authenticated when he accessed another resource with a lower authentication level using Access Manager. Oracle Adaptive Access Manager does not show the user name and password pages because the user is already authenticated. However, the flows that are executed in Oracle Adaptive Access Manager depend on whether the user was already logged in to Oracle Adaptive Access Manager.19.9.2.2 Detection of Insufficient Authentication Level by OAM Agent
When the user requests a resource that is protected with a higher level authentication scheme, the following process occurs.
Process overview: OAM Agent detects insufficient session level
No check of the authentication level is made on the server side. The following example refers to a 10g OAM Agent.
Note:
11g OAM Agents are associated with individual per-agent OAMAuthnCookies.-
The OAM Agent sends the request to the OAM Proxy to obtain the scheme details for the protected resource.
-
The OAM Agent sends the request for session information to the OAM Proxy.
-
The OAM Proxy returns details of the ObSSOCookie, including the authenticated level of the ObSSOCookie.
-
The OAM Agent compares the level of ObSSOCookie with that of the authentication scheme.
-
If insufficient, the agent invokes the authentication process again.
-
If sufficient, the access is granted access.
-
19.9.2.3 Multi-Level Authentication Processing with 10g OSSO Agent
In contrast to OAM Agents, all the resources protected by mod_osso on a host (or virtual host) are protected at the same level.
With mod_osso, multi-level authentication applies when user is already authenticated using one mod_osso host (or virtual host) at Level 2 and then tries to access another mod_osso protected host (or virtual host) at level 3.
Process overview: OSSO Agent multi-level authentication flow
-
The user tries to access a resource protected by mod_osso on host1 at level 2.
-
The OSSO Agent sends the request to the OAM Proxy to obtain the authentication scheme details for the protected resource.
-
The OAM_ID cookie for SSO Server and a host based cookie "HOST_port" for host1 are set and contain authentication level information.
-
After authentication, the user tries to access a resource on host2 that is protected with a higher level of authentication.
-
The user is redirected to the OAM Server for authentication because this is the first time accessing host2.
-
The OAM Server (OSSO Proxy) receives the OAM_ID cookie which has an insufficient level to access the resource on host2.
-
If the level is insufficient, the OAM Server (OSSO Proxy) triggers re-authentication.
-
If the level is sufficient, the access is granted access.
-
19.9.3 Creating an Authentication Scheme
Users with valid Administrator credentials can use the following procedure to add a new authentication scheme for use in an Application Domain.
The authentication module must be defined and ready to use as described in "Deploying and Managing Individual Plug-ins for Authentication".
See Also:
To create an authentication scheme
-
From the Oracle Access Management Console, click Authentication Schemes.
-
Click the Create button in the tool bar.
-
Fill in the fresh Authentication Scheme page (Table 19-20) by supplying information based on your deployment:
-
Name: LDAPSimpleFormScheme
-
Authentication Level
-
Challenge Method: FORM
-
Challenge Redirect URL: http://CredentialCollectorhost:port
-
Authentication Module: LDAP
-
Challenge URL: /CredentialCollector/loginform...
-
Challenge Parameters: Table 19-22, Table 19-23, Table 19-30
-
Context Type
-
-
Click Apply to submit the new scheme (or close the page without applying changes).
-
Dismiss the Confirmation window.
-
Optional: Click the Set as Default button to automatically use this with new Application Domains, then close the Confirmation window.
-
In the navigation tree, confirm the new scheme is listed (Refresh the tree, if needed).
-
Proceed to "Defining Authentication Policies for Specific Resources".
19.9.4 Searching for an Authentication Scheme
Users with valid Administrator credentials can perform the following task to search for a specific authentication scheme.
See Also:
"Conducting A Search"To search for an authentication scheme
-
From the Oracle Access Management Console, click Authentication Schemes.
-
In the text field, enter the desired scheme name (with or without wild card *). For example:
OA* -
Click the Search button to initiate the search.
-
Click the Search Results tab to display the results table, and then:
-
Edit: Click the Edit button in the tool bar to display the configuration page.
-
Delete: Click the Delete button in the tool bar to remove the instance; confirm removal in the Confirmation window.
-
Detach: Click Detach in the tool bar to expand the table to a full page.
-
View: Select a View menu item to alter the appearance of the results table.
-
-
Click the Browse tab to return to the navigation tree when you finish with the Search results.
19.9.5 Viewing, Editing, or Deleting an Authentication Scheme
Users with valid Administrator credentials can use the following procedure to view or modify an existing authentication scheme.
Note:
During a delete operation, if the Authentication Scheme is associated with any authentication policy, she is prompted with association details. Without policy associations, the scheme is deleted.To view or modify an authentication scheme
-
From the Oracle Access Management Console, click Authentication Schemes and find the desired scheme.
-
Edit:
-
On the Authentication Scheme page, modify values for your environment (Table 19-20).
Note:
In an upgraded deployment with OSSO Agents, change the Authentication Scheme and any Protected Resource Policies to use SSOCoExistMigrateScheme. -
Click Apply to submit the changes (or close the page without applying changes).
-
Dismiss the Confirmation window.
-
-
Set as Default: Click the Set as Default button to automatically use this scheme when creating policies in fresh Application Domains, then close the Confirmation window.
-
Delete:
-
Review any Application Domain using this authentication scheme and assign a different scheme.
-
Review the Authentication Scheme page to confirm this is the scheme to remove, then close the page.
-
In the navigation tree, click the name of the scheme and then click the Delete button in the tool bar.
-
Confirm removal (or dismiss the Confirmation window).
-
19.10 Extending Authentication Schemes with Advanced Rules
Advanced Rules have been added to allow for extending an existing authentication policy. Both Pre-Authentication and Post-Authentication rules can be applied.
Advanced Rules contain Boolean expressions. If there is more than one triggered Authentication Rule outcome, the lowest execution order outcome will be chosen as the final outcome. Table 19-24 documents the attributes that need be defined when creating an Advanced Rule.
Table 19-24 Advanced Rules Attributes
| Name | Description |
|---|---|
|
Name |
AuthnRule name. Name has to be unique within the checkpoint |
|
Description |
Description of the rule |
|
Execution Order |
Order in which the outcome will be executed in cases of more than 1 outcome |
|
Condition |
Script; the user can configure condition based on the HTTP request header's availability and set the desired outcome |
|
Outcome |
ID of the Authentication Scheme to which the rule applies. Access / Deny. |
Certain customers need the form-based authentication scheme to be extended to support non-browser clients. The requirement is that a form-based login page should be presented to the browser but allow a non-browser client to do a basic authentication based on credentials passed via header. See the following sections for details.
19.10.1 Using Pre-Authentication Advanced Rules
For user authentication, a form-based login page is presented through the browser for the user to complete. In some cases, a non-browser client (switches, routers and the like) might need to do basic authentication based on credentials passed via the request header. (This might arise when a particular resource protected by a form-based authentication scheme can be accessed by both users with a browser as well as switches, routers and other types of non-browser clients.) Non-browser client authentication support has been added (and can be configured) as one of the pre-authentication Advanced Rules. To support non browser client authentication, a user can configure the desired condition in an Authentication Rule (based on the HTTP request header's availability) and set a desired outcome.
Before executing the Authentication Condition, the Access Manager server prepares a request context using the available Request data (to construct a Boolean expression based condition). The following tables describe the various request context data details.
Table 19-25 Request Context Data
| Attribute Name | Description |
|---|---|
|
requestMap |
Map of all the request headers, parameters and post data values. This example can get the custom-header key from request header and compare it with value 'test'. str(request.requestMap['custom-header']).lower().find('test') > 0 |
|
resourceMap |
Map of matched resource details |
|
accept |
Returns 'Accept' header value |
|
acceptCharset |
Returns 'Accept-Charset' header value |
|
acceptEncoding |
Returns 'Accept-Encoding' header value |
|
acceptLanguage |
Returns 'Accept-Language' header value |
|
authorization |
Returns 'Authorization' header value |
|
connection |
Returns 'Connection' header value |
|
contentLength |
Returns 'ContentLength' header value |
|
cookie |
Returns 'Cookie' header value |
|
host |
Returns 'Host' header value |
|
ifModifiedSince |
Returns 'ifModifiedSince' header value |
|
pragma |
Returns 'Pragma' header value |
|
referer |
Returns 'Referer' header value |
|
userAgent |
Returns 'UserAgent' header value |
|
resourceHost |
Returns matched Resource's Host value |
|
resourcePost |
Returns matched Resource's Port value |
|
resourceOperation |
Returns matched Resource's Operation value |
|
resourceQueryString |
Returns matched Resource's QueryString |
|
resourceName |
Returns matched Resource's name |
|
resourceType |
Returns matched Resource's Type |
|
resourceURL |
Returns matched Resource's URL; for example, if 'landingPage' is in request.resourceURL, condition will evaluate to true if resourceURL has landingPage in it. |
Table 19-26 Location Context Data
| Attribute Name | Description |
|---|---|
|
locationMap |
Map of all the location data values; for example: location.locationMap['CLIENT_IP'] == '10.1.23.4' |
|
clientIP |
Returns client IP address; for example: location.clientIP.startswith('10.2') |
|
proxyIP |
Returns Proxy IP address |
19.10.2 Understanding Sample Advanced Rules
Table 19-29 contains sample Advanced Rules.
Table 19-29 Sample Advanced Rules
| Sample Rule | Sample Jython Script-based Condition | Notes |
|---|---|---|
|
Switching authentication scheme based on private or public IP rule |
location.clientIP.startswith('10.') or location.clientIP.startswith('172.16') or location.clientIP.startwith('192.168') |
This rule can be used in Pre and Post authentication checkpoints |
|
Black listed IP |
location.clientIP in ['130.35.50.115', '130.35.50.112', '130.35.50.113'] |
This rule can be used in Pre and Post authentication checkpoints |
|
Client Browser Type |
request.userAgent.lower().find('firefox') > 0 |
This rule can be used in Pre and Post authentication checkpoints |
|
Blocking access to user having user attribute 'description' equals 'test' |
user.userMap['description'] == 'test' |
This rule can be used only in Post authentication checkpoints |
|
Non browser client |
request.authorization.lower().startswith('basic') |
This rule can be used only in Pre authentication checkpoints |
|
Customer HTTP Header value |
request.requestMap['param'] == 'test' |
This rule can be used in Pre and Post authentication checkpoints |
19.11 Configuring Challenge Parameters for Encrypted Cookies
This section provides the following topics:
-
Configuring Challenge Parameters for Security of Encrypted Cookies
-
Setting Challenge Parameters for Persistence of Encrypted Cookies
19.11.1 About Challenge Parameters for Encrypted Cookies
In addition to the OAM Server cookie (OAM_ID), Access Manager implements single sign-on through an encrypted cookie:
-
11g Webgate, One per agent: OAMAuthnCookie_<host:port>_<random number> set by Webgate using the authentication token received from the OAM Server after successful authentication
Note: A valid OAMAuthnCookie is required for a session.
-
10g Webgate, One ObSSOCookie for all 10g Webgates.
Access Manager provides the ssoCookie challenge parameter that you can use within any authentication scheme to control how Webgates set the flags of the encrypted cookie. For example:
-
Securing Encrypted Cookie: Ensures that the encrypted cookie is sent only over an SSL connection and prevents the encrypted cookie from being sent back to a non-secure Web server.
-
Persisting Encrypted Cookie: Allows the user to log in for a time period rather than a single session. Persistent cookie functionality works with Internet Explorer and Mozilla browsers.
Note:
The value of the challenge parameter is note case sensitive. Syntax is the same regardless of your Webgate release. A single value is specified after the equal sign (=):ssoCookie=value
Multiple values must be separated by a semicolon (;). For example:
ssoCookie=value1;value2;...
-
For detached credential collector-enabled Webgates, set these parameters directly in the agent registration page (Table 16-2).
-
For non-DCC agents (Resource Webgates), these parameters are configured through Authentication Scheme challenge parameters (Table 19-30).
Table 19-30 describes specific challenge parameters that control how Webgates set encrypted cookie flags for single sign-on.
Table 19-30 Challenge Parameters for 10g/11g Encrypted Cookies
| 11g /10g Webgate Challenge Parameter Syntax for Encrypted Cookies | Description |
|---|---|
ssoCookie= |
Parameter that controls flags for the SSO cookie OAMAuthnCookie. |
miscCookies= |
Parameter that controls flags for all other Access Manager encrypted cookies. |
Secure
|
Ensures that the encrypted cookie is sent only when the resource is accessed through HTTPS. A secure cookie is required only when a browser is visiting a server using HTTPS. ssoCookie=Secure miscCookies=Secure |
|
|
Explicitly disables Secure cookies. ssoCookie=disableSecure miscCookies=disableSecure |
httponly
|
Enabled by default with 11g Webgate SSO OAMAuthnCookie and miscellaneous cookies. ssoCookie=httponly miscCookies=httponly |
disablehttponly
|
Explicitly disables ssoCookie=disablehttponly miscCookies=disablehttponly |
ssoCookie=max-age=time-in-seconds
|
Creates a persistent cookie in browsers, rather than one that lasts for a single session, and specifies the time interval in-seconds when the cookie expires. For example, to set the cookie to expire in 30 days (2592000 seconds): max-age=2592000 |
19.11.2 Configuring Challenge Parameters for Security of Encrypted Cookies
The challenge parameter is not case sensitive.
See Also:
"Creating an Authentication Scheme"To secure the encrypted cookie
-
Create an authentication scheme.
-
In the Challenge Parameter field, enter your specification for the desired encrypted cookies (Table 19-30).
-
Confirm that the OAM Servers and clients (OAM Agents) are communicating securely across the Oracle Access Protocol channel, as described in Appendix C.
19.11.3 Setting Challenge Parameters for Persistence of Encrypted Cookies
The challenge parameter is not case sensitive.
See Also:
"Creating an Authentication Scheme"To define encrypted cookie persistence
-
Define an authentication scheme.
-
In the challenge parameter for this scheme, add the following (Table 19-30):
Webgate
ssoCookie=max-age=time-in-seconds
19.12 Understanding Password Policy
This section provides the following topics:
19.12.1 Previewing Oracle-Provided Password Forms and Functionality
Access Manager provides several pages for user interactions during credential collection, as described in Credential Collector Password Pages. The location can be customized, depending on the desired topology of the authentication scheme being developed.
Table 19-31 Credential Collector Password Pages
| Credential Collector | Description |
|---|---|
|
ECC pages |
The default embedded credential collector jsp forms, by default, reside on the OAM Servers.
|
|
DCC pages |
Dynamic pages general login/logout and password policy with the DCC are excluded automatically through the OHS httpd.conf/webgate.conf file--you do not need to configure a policy to exclude these. See the Webgate host:
See Also: For details about customizing pages and messages, see the Oracle Fusion Middleware Developer's Guide for Oracle Access Management. |
Table 19-32 shows the password forms provided.The default pages can be customized for your enterprise, or replaced entirely with custom pages. For example, you can design, implement, and deploy a custom page that displays a different version of the login form for a mobile browser than is used for a desktop browser.
Table 19-32 Password Management Forms and Functions
| Form | Function |
|---|---|
|
Sign In Form |
The standard login form provides fields for userID and password. Clicking the Login button initiates authentication processing governed by the authentication module.
See: Oracle Fusion Middleware Developer's Guide for Oracle Access Management for details about customizing login forms. |
|
Sign In Error |
This standard login form appears when an error occurs. The text in red identifies the errors, which can be suppressed or displayed. 
See: Oracle Fusion Middleware Developer's Guide for Oracle Access Management for details about suppressing or displaying. |
|
Password Expiry Notification |
The following message appears to inform the user that her password will expire, based on the notification policy.  |
|
Change Password Form |
Based on password expiration policy configuration, the following window appears to enforce the policy and require user to change his password.  |
|
Password Change Success |
The following message appears to confirm the password change was successful.  |
|
Locked or Disabled User Account |
Based on the password policy, user account lockout occurs when supplied credentials fail during the maximum allowed login attempts.  |
19.12.2 Previewing the Password Policy Page in Oracle Access Management Console
Figure 19-29 shows the Password Policy page in the Oracle Access Management Console. Administrators use this page to define policy based on enterprise requirements.
Table 19-33 describes configurable password policy elements (as read from left to right in the console).These elements are used by both the ECC and DCC.
Table 19-33 Password Policy Elements
| Element | Description |
|---|---|
|
Minimum Uppercase Characters |
Defines the minimum number of uppercase characters required in a password. |
|
Minimum Lowercase Characters |
Sets the minimum number of lowercase characters required in a password. |
|
Minimum Alphabetic Characters |
Defines the minimum number of special characters allowed in the password. |
|
Minimum Numeric Characters |
Sets the minimum number of numeric characters required in a password. |
|
Minimum Alphanumeric Characters |
Defines the minimum number of alphanumeric characters required in a password. |
|
Minimum Special Characters |
Sets the minimum number of special characters required in a password. |
|
Maximum Special Characters |
Defines the maximum number of special characters allowed in a password. |
|
Minimum Unicode Characters |
Defines the minimum number of unicode characters required in a password. |
|
Maximum Unicode Characters |
Sets the maximum number of unicode characters allowed in a password. |
|
Minimum Password Length |
Sets the total minimum number of characters required in a password. |
|
Maximum Password Length |
Defines the total maximum number of characters allowed in a password. |
|
Characters Required |
Defines the specific characters that are required in a password. No delimiter is needed or allowed in this definition. |
|
Characters Not Allowed |
Sets the specific characters that cannot be used in a password. No delimiter is needed or allowed in this definition |
|
Characters Allowed |
Defines all allowed characters in a password. No delimiter is needed or allowed in this definition |
|
Substrings Not Allowed |
Specific character strings that are not allowed in a password. Use a comma as the delimiter in this definition. |
|
Start with alphabet |
Specifies that the first character in a password must be alphabetic, when checked. |
|
Allow last name |
Specifies that the user's last name is allowed in the password, when checked. |
|
Allow first name |
Specifies that the user's first name is allowed in the password, when checked. |
|
Allow User ID |
Specifies that the user's userID is allowed in the password, when checked. |
|
Warn after |
Defines when (in days) to warn a user before her password will expire. |
|
Maximum Attempts |
Identifies the maximum number of login attempts a user can make before a lockout. |
|
Expire after |
Defines the period of time (in days) that the password is valid. |
|
Lockout Duration |
Identifies the period of time the user is locked out (in minutes) after the designated number of failed login attempts. After this period, the user can attempt a fresh login. |
|
Permanent Lockout |
specifies permanent lockout after the designated number of failed login attempts. |
|
Disallow Last |
Defines the number of previous passwords that cannot be used when the user changes her password. |
|
Password Dictionary File |
Identifies the physical file on OAM Servers that contain the list of restricted words that can not be specified in a password. |
|
Password File Delimiter |
Defines the delimiter used in the Password Dictionary file to separate various words. For example, if the file contains |
|
Password Service URL |
The location of various password pages. |
19.12.3 About Credential Collectors and Password Policy Validation
Regardless of the credential collection method you choose, you can configure one global password policy that applies to all Access Manager-protected resources (using the Password Policy Validation Module in the authentication scheme). Also, the relevant URLs for the credential collector and related forms must be specified as outlined in Table 19-34.
Table 19-34 Specifying Credential Collectors and Related Forms for Authentication
| In the . . . | For the ECC . . . | For the DCC . . . |
|---|---|---|
|
OAM Agent Registration DCC Only |
N/A. |
Check the box beside Allow Management Operations in the OAM Agent registration page. See Also: "Enabling DCC Credential Operations" |
|
login, error, and password pages |
Pages where the user enters credentials arrive out of the box on the OAM Server and require no additional settings or changes.
|
Dynamic pages for general login/logout and password policy with the DCC are excluded automatically through the OHS See Webgate host directories
Perl Scripts for DCC-based Login and Logout The path name of the Perl executable must be updated in Oracle-provided Perl scripts on the Webgate host See Also: Table 19-5, "Comparing the DCC and ECC" |
|
Password Policy, Password Service URL |
The Default/ECC password page is used automatically: Password Service URL for ECC: See Also: "Defining Your Global Password Policy" |
Enter the DCC password page: Password Service URL for DCC: See Also: "Locating and Updating DCC Forms for Password Policy" |
|
User Identity Store |
The user data object definition in the Access Manager schema is extended with attributes that enable password user status and password history maintenance. This definition is provided in an LDIF file, and must be added to each user identity store using the |
Same for both DCC and ECC: See Also: |
|
Password Policy Validation Authentication Module |
Enter the Default Store as the KEY_IDSTORE_REF for each of the three plug-ins / steps (with an Error redirect on Failure): See Also: |
Same for both DCC and ECC: |
|
Authentication Scheme, Challenge Redirect URL |
Enter the Credential Collector host:
|
Enter the Credential Collector host:
|
|
Authentication Scheme, Challenge URL |
Enter the Credential Collector login form relative URI:
|
Enter the Credential Collector login form relative URI:
|
|
Authentication Scheme, Challenge Parameters |
ECC: User-defined Challenge Parameters: OverrideRetryLimit=0 initial_command=NONE See Also: |
DCC: User-defined Challenge Parameters:
See Also: |
|
Server Error Mode |
Same for both DCC and ECC. See: "Setting the Error Message Mode for Password Policy Messages" |
Same for both DCC and ECC. See: "Setting the Error Message Mode for Password Policy Messages" |
|
Authentication Policy |
Credential collectors in authentication policies:
See Also: "Adding Your PasswordPolicyValidationScheme to ECC Authentication Policy" |
Credential collectors in Authentication Policies: DCC Separate from Resource Webgate: ***Protecting (Resource) Webgate Application Domain, (Authentication Policy protecting resources), use the DCC-related Authentication Scheme. ***DCC Webgate Application Domain, Authentication Policy protecting resources, use the DCC-related Authentication Scheme. Consider: --With No Action URL: DCC uses thedefault /oam/server/auth_cred_submit, which is automatically protected with the DCC-related authentication scheme. --With an Action URL: Explicitly protect the specified Action URL with the DCC Scheme. See Also: "Adding PasswordPolicyValidationScheme to Authentication Policy for DCC" |
|
Logout Configuration |
ECC: In the protecting (Resource) Webgate Agent registration, configure the |
DCC:
See "Configuring Logout When Using Detached Credential Collector-Enabled Webgate" |
Caveats for Integrated Deployments
When you are using Oracle Identity Management and Oracle Access Management with Oracle Internet Directory, there are two sets of password policy definitions and enforcement.
-
Password Policy Definition in both Oracle Identity Management and in Oracle Internet Directory
-
Password Policy Enforcement by one of the following:
Oracle Access Management enforces state policies (incorrect password, for example) during Web access; Oracle Internet Directory enforces its own state policies as well as LDAP operations (bind and compare, for example).
Oracle Identity Management enforces value policies (characteristics of the password) during user creation of the password update; Oracle Internet Directory enforces it's own value policies as well for policies for LDAP operations (add, modify for example).
To use just one set of policies you can either:
-
Make the Oracle Internet Directory policies weaker or the same strength as the Oracle Identity Management and Oracle Access Management policies. However, this leads to a double enforcement.
-
Disable native LDAP password policy validation, which unfortunately leaves no enforcement for direct LDAP operations.
19.13 Managing Global Password Policy
Authentication involves determining which credentials a user must supply when requesting access to a resource, gathering credentials, and returning a response that is based on the results of credential validation.
Access Manager authentication processing relies on an authentication module (or plug-in) to define the rules governing requirements and transmission of information to the back-end authentication scheme. By default, Access Manager supports using the OAM Server Embedded Credential Collector (ECC) for authentication processing. However, you can also configure an 11g Webgate to use as an detached credential collector (DCC) instead.
Both the ECC and DCC facilitate multi-step authentication flows where credentials are not provided all at once. This increases the flexibility of interaction with users or programmatic entities for the purpose of collecting authentication-related information. For more information on multi-factor authentication, see the Oracle Fusion Middleware Developer's Guide for Oracle Access Management.
Regardless of the credential collection method you choose (default ECC or optional DCC), you can configure a global password policy as described in this section that applies to all Access Manager-protected resources.
The following overview provides links to topics that describe how to configure and use the password policy. Unless explicitly stated, all tasks apply equally to the ECC and DCC. Skip any tasks that do not apply to your deployment.
Task overview: Password policy management includes
-
Adding an Administrator to Change User Attributes After a Password Change
-
DCC: Configuring 11g WebGates and Authentication Policy for DCC
19.13.1 Defining Your Global Password Policy
Users with Oracle Access Management Administrator credentials can use the following procedure to define a common password policy based on enterprise-defined requirements.
Note:
The only difference between a global password policy for the ECC versus the DCC isPassword Service URL, which is credential collector-specific and defaults to ECC pages as shown in Step 2.The specifications in this example are for illustration only. Your environment will be different.
To configure the password policy in Oracle Access Management
-
From the Oracle Access Management Console, click Password Policy under the Access Manager panel.
-
On the Password Policy page, enter the Password Service URL for the desired credential collector login page (ECC or DCC, Table 19-34).
ECC Password Service URL DCC Password Service URL /pages/login.jsp/oamsso-bin/login.pl -
On the Password Policy page, enter values (Table 19-33) based on requirements for your enterprise. For example:
-
Warn After 3
-
Expire After 20
-
Permanent Lockout (Disable)
-
Lockout duration 1
-
Minimum Special Characters 1
-
-
Click Apply to submit the policy.
-
Proceed as needed for your environment; skip any tasks that have been completed already:
19.13.2 Designating the Default Store for Your Password Policy
The Password Policy operates only with the designated Default Store. Administrator roles and credentials must reside in the System Store.
To designate a Default Store for the global password policy
-
From the Oracle Access Management Console, click User Identity Stores.
-
Set the System Store: Administrator roles and credentials must reside in this store.
-
Open the page of the store to designate as the System Store.
-
Check Set as system store (for domain wide authentication and authorization operations).
-
Click Applyn.
-
Add Administrators: See "Managing the Administrators Role".
-
Authentication Module: Set the LDAP Authentication Module used by the
OAMAdminConsoleScheme(authentication scheme) to use this System Store. -
Configure one or more authentication plug-ins to use this store, as described in "Orchestrating Multi-Step Authentication with Plug-in Based Modules".
-
-
Set Default Store: This store is required for Password Policy, Security Token Service, and migration when patching.
-
Open the page of the store to designate as the Default Store.
-
Check the box beside Set as default store.
-
Authentication Module: Locate
OAMAdminConsoleSchemeand confirm that the LDAP module does not refer to this store. See "Managing Native Authentication Modules". -
Authorization Policy Conditions: Choose the desired user identity store when setting Identity Conditions in Authorization Policies. See "Defining Authorization Policy Conditions".
-
Token Issuance Policy Conditions: Choose the desired user identity store when setting Identity Conditions in Token Issuance Policies. See "Managing Token Issuance Policies, Conditions, and Rules".
-
-
Close the registration page.
19.13.3 Adding Key Password Attributes to the Default Store
The Password Policy operates only with the designated Default Store. This section provides steps for extending the default store schema for Oracle Access Management password policy operations.
19.13.3.1 About Extending the Default Store Schema
The LDIF (Lightweight Directory Interchange Format) files distributed as part of Access Manager are meant to extend the schema with required object classes. Generally, these are applied using the idmConfigTool or Access Manager and Oracle Identity Management wiring has been performed manually.
The user data object definition in the Access Manager schema is extended with attributes that enable password user status and password history maintenance. This definition is provided in an LDIF file, and must be added to each user identity store using the ldapadd tool. Oracle-provided LDIFs are identified in Table 19-35.
Note:
OAM_HOME contains installed files necessary to host Oracle Access Management. OAM_HOME resides within the directory structure of the Middleware home ($MW_HOME).Table 19-35 Location of Oracle-provided LDIFs for LDAP Providers
| LDAP Provider | LDIF Location |
|---|---|
|
OID: Oracle Internet Directory |
$OAM_HOME/ oam/server/pswdservice/ldif/OID_PWDPersonSchema.ldif |
|
OVD: Oracle Virtual Directory |
$OAM_HOME/ oam/server/pswdservice/ldif/OVD_PWDPersonSchema.ldif |
|
AD: Microsoft Active Directory |
$OAM_HOME/ oam/server/pswdservice/ldif/AD_PWDPersonSchema.ldif |
|
SJS: sun Java System Directory |
$OAM_HOME/ oam/server/pswdservice/ldif/IPLANET_PWDPersonSchema.ldif |
|
eDirectory: Novell eDirectory |
$OAM_HOME/ oam/server/pswdservice/ldif/EDIR_PWDPersonSchema.ldif |
|
ODSEE: Oracle Directory Server Enterprise Edition |
$OAM_HOME/ oam/server/pswdservice/ldif/IPLANET_PWDPersonSchema.ldif |
|
OUD: Oracle Unified Directory |
$OAM_HOME/
oam/server/pswdservice/ldif/OUD_PWDPersonSchema.ldif
|
|
SLAPD: OpenLDAP Directory |
$OAM_HOME/ oam/server/pswdservice/ldif/OLDAP_PWDPersonSchema.ldif |
|
IBM: OBM Tivoli Directory |
$OAM_HOME/ oam/server/pswdservice/ldif/TIVOLI_PWDPersonSchema.ldif |
The attributes that enable password user status and password history maintenance are shown in Table 19-36. The user data object of each user identity store must include the attributes shown in Table 19-36. These can be added with the ldapadd tool, LDIF (Lightweight Directory Interchange Format) file.
Table 19-36 Key Password Attributes in a Password Policy
| Attribute | Description | Format and Values |
|---|---|---|
|
obPasswordCreationDate |
The date and time used to calculate (at the time of user login) whether the password has expired and whether a warning needs to be issued. |
YYYY-MM-DDThh:mm:ssZ |
|
obPasswordHistory |
Used to track the number of last passwords used. Access Manager understands 10g oblixPersonPwdPolicy format and changes it to new format. |
New format: Previous format:
|
|
obPasswordChangeFlag |
Used during forced password change for first time user login (or forced password change initiated by the Administrator. |
Boolean string value.
Empty string represents |
|
obuseraccountcontrol |
Used to represent a disabled user. |
Non-encrypted string value.
Empty string represents "activated". |
|
obpasswordexpirydate |
The time after which the user password is considered to be expired. |
YYYY-MM-DDThh:mm:ssZ Empty value represents |
|
obLockoutTime |
The time up to which the user is considered to be locked out due to too many login attempts. |
Epoch value (in seconds) representing time in the future.
|
|
obLoginTrvCount |
The number of consecutive login failures by the user. This counter is reset on the first correct password entry. |
Non-encrypted integer value.
|
|
oblastsuccessfullogin |
The time of the last successful login. |
YYYY-MM-DDThh:mm:ssZ |
|
oblastfailedlogin |
The time of the last failed login. |
YYYY-MM-DDThh:mm:ssZ |
19.13.3.2 Extending the Default Store Schema with Password Policy Attributes
You can skip this task if the environment has been configured using idmConfigTool -prepareIDStore.
If your user identity store has not been extended with the oblix schema, you must update the schema to include the object classes required by the password service.
LDAP tools should be run from the /bin directory beneath $OAM_HOME. The following procedure illustrates extending the Oracle Internet Directory schema. Your environment might be different.
To extend the Default User Identity Store schema
-
Use the following command to update the Oracle Internet Directory object classes of the designated Default Store required by the password service:
ldapadd -D "cn=orcladmin" -w <password> –h <hostname> -p 3060 –x -f $OAM_HOME/ oam/server/pswdservice/ldif/OID_PWDPersonSchema.ldif
-
Proceed to "Adding an Administrator to Change User Attributes After a Password Change".
19.13.4 Adding an Administrator to Change User Attributes After a Password Change
In this procedure, you modify the Default Store (Oracle Internet Directory in this example) to use a different privileged account as the Bind DN. This enables sufficient privileges to change user attributes after a password change.
Register a supported LDAP store and designate it as the Default Store. Ensure that the user you add is defined within the Default Store.
See Also:
"Managing the Administrators Role"Figure 19-30 shows the completed registration page for the designated Default Store. The procedure to add an Administrator follows the figure.
-
Log in to the Oracle Access Management Console, as usual.
https://hostname:port/oamconsole/ -
Open the desired User Identity Store registration page:
System Configuration tab
Common Configuration section
Data Sources node
User Identity Stores
OID -
Add a New Administrator:
-
In the Access System Administrators section of the page, click + above the table.
-
In the dialog box, search All Users, highlight desireduser, then click Add Selected.
-
Click Apply to submit the changes.
-
-
Default Store: Confirm the designated Default Store (or click Default Store) then click Apply.
-
Proceed with "Configuring Password Policy Authentication".
19.14 Configuring Password Policy Authentication
After preparing your password policy, Default Store, and Administrator, you can develop your authentication module and scheme as described in this section.
-
Configuring the Password Policy Validation Authentication Module
-
Adding Your PasswordPolicyValidationScheme to ECC Authentication Policy—If you are using the DCC, skip this topic and go to "Configuring 11g WebGates and Authentication Policy for DCC"
19.14.1 Configuring the Password Policy Validation Authentication Module
You must also configure the Password Policy Validation Authentication Module to use the Default Store.
Note:
There are no credential collector dependencies when defining the Password Policy Validation Module for authentication.A sample module is shown in Figure 19-31. The User Password Status Step is the unique step that relies on the UserPasswordPolicyPlugin.
Each step identifies the action provided by a specific named plug-in.
Figure 19-32 shows the orchestration of steps within the authentication module. For more information on modules and steps, see "About Plug-in Based Modules for Multi-Step Authentication".
Table 19-37 describes the Password Policy Validation module step details that you specify.
Table 19-37 User Password Step Details
| Step Name | Step Details | Description |
|---|---|---|
|
User Identification Step |
KEY_LDAP_FILTER |
Add the LDAP filter to the KEY_LDAP_FILTER attribute. Only standard LDAP attributes can be used when defining an LDAP search filter. For example:
(uid={KEY_USERNAME})
See Also: Table 20-22, "LDAP Search Filter Examples for Access Manager" and your vendor documentation for the exact syntax for your identity store |
|
KEY_IDENTITY_STORE_REF |
The name of the registered Identity Store containing the module users. Default: The registered Default Store. |
|
|
KEY_SEARCH_BASE_URL |
Base URL for user searches. For example: dc=us,dc=example,dc=com |
|
|
User Authentication Step |
KEY_IDENTITY_STORE_REF |
The name of the registered Identity Store containing the module users. Default: The registered Default Store. |
|
KEY_PROP_AUTHN_EXCEPTION |
Enable or disable the propagation of LDAP errors. |
|
|
User Password Status Step |
PLUGIN_EXECUTION_MODE |
The execution mode of plug-in. Depending upon the configuration, this plug-in can operate either alone or with other default plug-ins. Values are one of the following:
Default: PSWDONLY |
|
KEY_IDENTITY_STORE_REF |
The name of the registered Identity Store containing the module users. Default: The registered Default Store. |
|
|
NEW_USERPSWD_BEHAVIOR |
Configures retroactive behavior of the new-user password-policy. Values are either:
Default: FORCEPASSWORDCHANGE |
|
|
POLICY_SCHEMA |
Policy schema for password service. Currently only OAM10G is supported. Default: OAM10G |
|
|
URL_ACTION |
The type of servlet action needed for redirecting the user to the specific password page for expiry and warning pages. Values can be either:
Default: REDIRECT_POST |
|
|
DISABLED_STATUS_SUPPORT |
Specifies whether the disabled status is to be supported and acted upon in this password service. Valid values are either True or False. Default: TRUE |
Defining Your Global Password Policy
Note:
There are no credential collector dependencies when defining the Password Policy Validation Module. Enter the Default Store as the KEY_IDSTORE_REF for each of the three plug-ins (with an Error redirect on Failure).To configure the Password Policy Validation Module
-
From the Oracle Access Management Console, click Authentication Modules, Custom Authentication Modules and then Password Policy Validation Module.
-
Click the Steps tab; for each of the three steps add the Default Store name in the field beside KEY_IDSTORE_REF (Save after each change). For example:
-
User Identification Step
KEY_IDSTORE_REF: OID
Save.
-
User Authentication Step
KEY_IDSTORE_REF: OID
Save.
-
User Password Status Step
KEY_IDSTORE_REF: OID
Save.
-
-
Click Apply.
-
Proceed to "Configuring the PasswordPolicyValidationScheme".
19.14.2 Configuring the PasswordPolicyValidationScheme
You can have multiple authentication schemes for use with the global password policy. Users with Administrator credentials can follow this procedure to configure the PasswordPolicyValidationScheme.
Note:
Differences between values for the ECC versus the DCC include (Table 19-34):-
Challenge Redirect URL: Credential Collector host and port
-
Challenge URL: Credential Collector Pages
-
Challenge Parameters: Table 19-23
The sample scheme in Figure 19-33 is configured for the ECC. The sample scheme in Figure 19-34 is configured for the ECC. Your authentication scheme will be different.
Configuring the Password Policy Validation Authentication Module
See Also:
"Managing Authentication Schemes"To configure the PasswordPolicyValidationScheme
-
From the Oracle Access Management Console, click Authentication Schemes and then PasswordPolicyValidationScheme.
-
Set up the scheme for your environment. For example:
-
Authentication Level 2
-
Default (blank)
-
Challenge Method: Form
-
Challenge Redirect URL:
http://CredCollector_host:port/ -
Authentication Module: Password Policy Validation Module
-
Challenge URL:
/CredCollector_pages/ -
Context Type: External
-
Challenge Parameters:
ECC Challenge Parameters DCC Challenge Parameters
OverrideRetryLimit=0
initial_command=NONE
OverrideRetryLimit=0
creds=userid passwordSee Also: Table 19-23, "User-Defined Challenge Parameters for Authentication Schemes" action
If not specified, the default for both ECC and DCC is /oam/server/auth_cred_submit.DCCCtxCookieMaxLength
(default is 4096)TempStateMode
controls how the DCC stores the OAM Server state: cookie or form (the default) as specified with the parameter's value.MaxPostDataBytes
Restricts the maximum number of bytes of POST data submitted as user credentials.creds
Whatever is passed must be specified in theobMapcredentials parameter of theObUserSessionobject, as described in the Oracle Fusion Middleware Developer's Guide for Oracle Access Management
-
-
Click Apply.
-
Proceed to "Adding Your PasswordPolicyValidationScheme to ECC Authentication Policy".
19.14.3 Adding Your PasswordPolicyValidationScheme to ECC Authentication Policy
A user with Administrative privileges can use the PasswordPolicyValidationScheme configured for the ECC in the application domain of the protecting Webgate (Resource Webgate).
Configuring the PasswordPolicyValidationScheme
To add PasswordPolicyValidationScheme to an ECC authentication policy
-
ECC: In the console, search for and open the appropriate Application Domain. (See "Searching for an Existing Application Domain").
-
ECC: Protect Resources using the PasswordPolicyValidationScheme:
-
Find and open your Protected Resource Policy on the Authentication Policies tab (see "Viewing or Editing an Authentication Policy"):
Authentication Policies
Protected Resource Policy -
Select PasswordPolicyValidationScheme for the Protected Resource Policy (Authentication Scheme) and click Apply.
-
Finish updating your Authentication and Authorization policies, as desired (Chapter 20).
-
-
Proceed as needed for your environment:
19.15 Configuring 11g WebGates and Authentication Policy for DCC
The following task overview documents how to configure an 11g WebGate and Authentication Policy for use with the DCC. The appropriate sub sections are linked within each step.
-
Enabling DCC Credential Operations provides steps for either configuration:
DCC Combined with Resource Webgate: Enable Allow Credential Collector Operations in the DCC's OAM Agent registration page.
Separate DCC and Resource Webgate: Enable Allow Credential Collector Operations in the DCC's OAM Agent registration page and edit the Resource Webgate registration page to set the
Logout Redirect URLto the DCC's logout.pl. -
Adding PasswordPolicyValidationScheme to Authentication Policy for DCC provides steps for either configuration:
DCC Combined with Resource Webgate: In the combined DCC/Resource Webgate Application Domain, update the Protected Resources Authentication Policy to use your DCC Authentication Scheme.
Separate DCC and Resource Webgate: In the separate Resource Webgate Application Domain, update the Protected Resources Authentication Policy to use your DCC Authentication Scheme.
-
Supporting Federation Flows With DCC provides steps to incorporate the DCC into Federation flows.
Note:
If your environment uses the ECC, go to "Completing Password Policy Configuration".19.15.1 Enabling DCC Credential Operations
Whether you are using a separate DCC or combined DCC and Resource WebGate, you must enable Allow Credential Collector Operations in the DCC's OAM Agent registration page.
With a separate DCC and Resource WebGate, you must also edit the Resource WebGate registration page to set the Logout Redirect URL to the DCC's logout.pl, as described in Step 3.
The following procedure presumes your deployment uses Open mode communication. If your deployment uses Simple or Cert mode communication, be sure to copy the appropriate artifacts when you perform Step 4.
-
Configuring and Managing Registered OAM Agents Using the Console
-
Configuring Password Policy Authentication using DCC-specific details
To enable DCC credential operations
-
In the Access Manager section of the Oracle Access Management Console, click SSO Agents to find and open the registration page for the 11.1.2 Webgate that will function as the DCC.
-
DCC Webgate Registration: Check Allow Credential Collector Operations, click Apply, then perform Steps 4 and 5.
Note:
If the DCC is combined with a Resource WebGate, skip Step 3. -
Separate Resource Webgate: Edit the Resource WebGate registration to set the
Logout Redirect URLto the DCC's logout.pl (Table 19-34), click Apply, then perform Steps 4 and 5. -
Copy Agent configuration file (including Simple or Cert mode files) from the AdminServer (Console) host to the Agent host. For example:
Agent & Artifacts Artifacts 11g Webgate/Access Client ObAccessClient.xml and cwallet.sso
From the AdminServer (Console) host: $DOMAIN_HOME/output/$Agent_Name/
To the Agent host: $11gWG_install_dir/webgate/config
Simple or Cert Mode Copy to the Agent host: $11gWG_install_dir/webgate/config -
aaa_key.pem
-
aaa_cert.pem
-
aaa_chain.pem
-
password.xml
See Also: Appendix C, "Securing Communication"
-
-
Restart the OHS Web server.
-
Proceed to "Locating and Updating DCC Forms for Password Policy".
19.15.2 Locating and Updating DCC Forms for Password Policy
Access Manager provides several dynamic pages for user interactions with the DCC.
Enabling DCC Credential Operations
To locate and update the DCC forms
-
Locate the DCC forms in the Webgate host (
Table 19-34):
$WEBGATE_HOME/webgate/ohs/oamsso/*,
$WEBGATE_HOME/webgate/ohs/oamsso-bin/*pl, and
$WEBGATE_HOME/webgate/ohs/oamsso-bin/templates/* -
Customize their location, depending on the desired topology of the authentication scheme being developed.
-
Update Perl Location: Update the Perl location to be consistent with the actual location, in the first line of the login, logout, and securid scripts on Webgate host in
$WEBGATE_HOME/webgate/ohs/oamsso-bin/*pl("Perl Scripts for DCC-based Login and Logout" in Table 19-34). -
Customize the default pages for your enterprise, or replace them entirely with custom pages. For example, you can design, implement, and deploy a custom page that displays a different version of the login form for a mobile browser than is used for a desktop browser.
-
Proceed to "Adding PasswordPolicyValidationScheme to Authentication Policy for DCC".
19.15.3 Adding PasswordPolicyValidationScheme to Authentication Policy for DCC
The following procedure provides steps that you must perform to use your DCC Authentication Scheme in a Protected Resources Authentication Policy. The steps you perform depend on the type of deployment you have:
-
Combined DCC/Resource Webgate: Perform Step 1 to add your DCC Authentication Scheme to the Protected Resources Authentication Policy of the combined DCC/Resource Webgate Application Domain.
-
Separate Resource Webgate: Perform Step 3 to add your DCC Authentication Scheme to the Protected Resources Authentication Policy of the separate Resource Webgate Application Domain.
Perform Step 2 regardless of your DCC deployment type. By default, login and logout forms are excluded through OHS /httpd.conf/webgate.conf so that you do not need to exclude them through policies. However, with the Chrome browser, you must explicitly exclude the async favicon.ico request (which overrides the DCCCtxCookie).
Note:
This example refers to the PasswordPolicyValidationScheme set for the DCC in Section 19.14, "Configuring Password Policy Authentication."Locating and Updating DCC Forms for Password Policy
To use the DCC Authentication Scheme in an Authentication Policy
-
Combined DCC/Resource Webgate: Open the DCC application domain:
Policy Configuration
Application Domains
DCCDomain
-
Locate and open the Authentication Policy, Protected Resource Policy (see "Searching for an Authentication Policy").
-
Add your DCC Authentication Scheme to this policy (see "Defining Authentication Policies for Specific Resources").
PasswordPolicyValidationScheme (DCC Authentication Scheme) -
Perform Step 2 if you have the Chrome Browser. Otherwise, go to Step 4.
-
-
Chrome Browser: Add and exclude resource
/favicon.icoin the DCCDomain, as follows.-
From DCCDomain, click the Resources tab.
-
Find and open the HTTP resource
/favicon.ico(or click the New Resource button and then add this resource). -
Confirm or edit the Resource URL to:
/favicon.ico
-
In the Protection section, Protection Level list, select Excluded, then click Apply.
-
Proceed to Step 4.
-
-
Separate Resource Webgate: Open the Resource Webgate application domain.
Policy Configuration
Application Domains
ResourceWGDomain
-
Locate and open the Authentication Policy, Protected Resource Policy (see "Searching for an Authentication Policy").
-
Add your DCC Authentication Scheme and an optional Failure URL (when not specified, Failure URL displays the default error page) to this policy (see "Defining Authentication Policies for Specific Resources"):
DCC Authentication Scheme
Failure URL (optional) -
Perform Step 2 if you have the Chrome Browser. Otherwise, go to Step 4.
-
-
Restart your Web server and proceed to "Completing Password Policy Configuration".
19.15.4 Supporting Federation Flows With DCC
The DCC is enhanced to work as a public end-point to the Access Manager server. HTTP requests to the DCC are tunneled via NAP to the proxy module of the Access Manager server. The JSP pages and servlets are executed in the Access Manager server and the response is tunneled back to the DCC. The end user effectively communicates only to the DCC.
Note:
If a WebGate is configured as a DCC and federated flows are in use, the DCC WebGate cannot be used to protect the resource. A separate WebGate must be configured and used to protect the resource.To use DCC for converged Federation flows, perform the following manual steps.
-
Configure the following internal resources as Public instead of Excluded.
/oamfed/…/* /oam/…/* /…/*
-
In the DCC WebGate, set the logout value to a valid DCC WebGate logout URL; for example,
/oamsso-bin/logout.pl -
Update the DCC Agent entry by adding the following entry to the User Defined Parameters list using the Access Manager Administration Console.
TunneledUrls=/oam,/oamfed
19.16 Completing Password Policy Configuration
These tasks are the same regardless of the credential collector you have configured. Perform the following tasks to complete your password policy configuration:
19.16.1 Setting the Error Message Mode for Password Policy Messages
Users with administrative privileges can use this procedure to set the Server Error Mode for password policy messages, as shown in Figure 19-35.
-
From the Oracle Access Management Console, click Access Manager settings.
-
In the Load Balancing section, set the Server Error Mode to Internal.
-
Click Apply.
-
Proceed with "Overriding Native LDAP Password Policy Validation".
19.16.2 Overriding Native LDAP Password Policy Validation
As described earlier, you need to disable native LDAP password policy validation before the non-native password policy can be used.
For example, with Oracle Internet Directory registered for Oracle Access Management, native password policy is generally located as follows:
dn: cn=default,cn=pwdPolicies,cn=Common,cn=Products,cn=OracleContext,<DOMAIN_CONTAINER>
Caution:
Disabling the native LDAP password policy validation leaves no enforcement for direct LDAP operations. There are various password policies in Oracle Internet Directory, including one in the following:dn: cn=default,cn=pwdPolicies,cn=Common,cn=Products,cn=OracleContext
However, this might not apply to your domain.
You can disable the Oracle Internet Directory password policy by setting the orclpwdpolicyenable parameter to zero (0).
See Also:
The various attributes described in Oracle Fusion Middleware Administrator's Guide for Oracle Internet DirectoryThe following procedure is only an example. Your environment will be different.
Setting the Error Message Mode for Password Policy Messages
To override native LDAP policy with Oracle Access Management password policy
-
Refer to the manual from your LDAP directory vendor.
-
Oracle Internet Directory: Disable native policy by setting
orclpwdpolicyenableto zero (0).-
Confirm the location of the password policy for your domain.
-
When you are sure you have the proper native LDAP policy, disable the policy. For example:
orclpwdpolicyenable = 0
-
-
Proceed as follows, depending on your deployment:
19.16.3 Disabling ECC Operation and Using DCC Exclusively
You can skip this task to allow the DCC and ECC to co-exist, and maintain authentication schemes and policies for both credential collectors.
To disable ECC, you must edit the oam-config.xml file as described here. Generally, Oracle recommends not editing oam-config.xml. Changes to this file could result in lost data or overwriting of the file during data sync operations. However, there is no other way to disable the ECC completely in favor of the DCC.
Note:
After disabling the ECC, access to resources protected by schemes and policies that rely on the ECC will be prohibited, including access to the Oracle Access Management Console.Configuring 11g WebGates and Authentication Policy for DCC
To disable ECC operation and use DCC exclusively
-
Make your changes on the node running the AdminServer to minimize possible conflicts that another AdminConsole user might make.
-
Back up oam-config.xml in $DOMAIN_HOME/config/fmwconfig/ and store the copy in a different location for use later if needed.
-
Locate the
ECCEnabledparameter in theOAMServicesDescriptorsection and make the changes shown here in bold:<Setting Name="OAMServicesDescriptor" Type="htf:map"> ... ... <Setting Name="ECCEnabled" Type="htf:map"> <Setting Name="ServiceStatus" Type="xsd:boolean">false</Setting> </Setting> -
Increment by 1, the configuration version number at the top of the file to associate your change and enable automatic propagation and dynamic activation across all running OAM Servers (see the next to last line of this example):
<Setting Name="Version" Type="xsd:integer"> <Setting xmlns="http://www.w3.org/2001/XMLSchema" Name="NGAMConfiguration" Type="htf:map:> <Setting Name="ProductRelease" Type="xsd:string">11.1.1.3</Setting> <Setting Name="Version" Type="xsd:integer">2</Setting> </Setting> -
Proceed to "Testing Your Multi-Step Authentication".
19.16.4 Testing Your Multi-Step Authentication
This section provides a number of evaluations you can perform to confirm that your deployment is working properly.
To confirm your multi-step authentication
-
Confirm access after login:
-
Open a new browser and request a resource.
-
Log in with your user credentials.
-
Confirm that you have access to the resource.
-
-
Confirm no access on incorrect login:
-
Open a new browser and request a resource.
-
Log in with incorrect user credentials.
-
Confirm that you must re-authenticate.
-
-
Confirm lockout after exceeding maximum incorrect login attempts:
-
Open a new browser and request a resource.
-
Log in with incorrect user credentials repeatedly.
-
Confirm that the user account is locked.
-
-
Modify and evaluate your password expiry policy:
-
Log in to the Oracle Access Management Console.
-
In your password policy, reset the expiry and lockout periods (Table 19-33) so that you will see warnings on your next login.
-
Save the policy updates.
-
Open a new browser and request a resource.
-
Verify the warning page appears advising that the password will expire.
-
Click the link to continue without password change.
-
-
Change your password:
-
Open a new browser and request a resource.
-
On the password expiry warning page, click the link to change your password.
-
On the password change page, enter your correct old password.
-
In the new password field, enter a different new password that does not follow the password policy and confirm the password validation error.
-
Enter a new password that meets requirements and confirm success and access to the resource.
-
19.17 Configuring Authentication POST Data Handling
Post data preservation and restoration functions apply to both credential collectors (ECC or DCC). This section provides the following topics:
19.17.1 About Authentication Post Data Preservation and Restoration
POST data preservation and restoration functions come into play when an application has a form wherein the user has entered a credential (or other data) but the session has expired, an idle session timeout has occurred, or the token validity period has ended by the time the user submits the form. If this scenario occurs, the user is presented with a fresh login form (depending on the authentication scheme) unless POST data is preserved and restored.
Administrators can configure the Resource Webgate to perform POST data preservation when the expired user and newly authenticated user are the same. Table 19-38 describes Resource Webgate support and behavior for post data.
Note:
Authentication POST data preservation and restoration is not supported when Access Manager performs authentication through custom agents.Table 19-38 Resource Webgate Support of POST Data Preservation and Restoration
| Resource Webgate | Description |
|---|---|
|
Supports Authentication Schemes |
LDAP, Basic, Sessionless Basic, X509, WNA |
|
Supports form encoding |
with text/html, text/plain, multipart/form-data, and application/x-www-form-urlencoded type data posted by the application form. |
|
Preserves |
The encoding type of the data posted by the original application form, except the input field of file type. |
|
Ensures |
The downstream application sees the same post data that was posted by the original application form. |
|
Constrains |
The overall size of the inbound request data or the inbound front channel message. There shall be a configuration parameter to override the code default value. This shall be per application. |
|
Maintains application data confidentiality and integrity |
Neither the Resource Webgate nor credential collector will interpret, nor log, application post data. If, after expiration and during re-authentication, the user authenticates with different credentials, then the post data of the previous user is cleared by the Resource Webgate and not restored. However, Webgate will post to the downstream application URL that was posted by the original application form. |
|
Ignores Preservation if ... Logs a Message when ... Performs Standard Authentication if ... Shows an Error when ... |
Post data is larger than the configured or hard-coded limit, preservation is ignored. Post data is skipped because it is bigger than the allowed limit, a message is logged. Post data size is larger than the hard-coded limit (or the configured value), the standard authentication flow is used. Together, if both front channel message data and application post data are large an error occurs. |
Table 19-39 describes credential collector feature support for POST data handling.
Table 19-39 Credential Collector Support for POST Data Handling
| Credential Collector Support |
|---|
|
ECC and DCC |
|
Compatible with earlier 11g Webgates |
|
Supports post data preservation for Form based authentication scheme with the default login form provided out of the box. |
|
Preserves application post data during authentication processing by:
Does not interpret application post data. |
|
Constrains the overall size of inbound front-channel messages using a configuration parameter to override the default value, per application. |
|
Logs a warning when post data is skipped because it is larger than the allowed limit. |
|
Does not preserve application post data when:
|
|
ECC Only
|
|
DCC Only
|
19.17.2 About Configuring Authentication POST Data Handling
Table 19-40 summarizes the authentication schemes that support authentication POST data handling.
Table 19-40 Authentication Schemes Supporting POST Data Handling
| Authentication Schemes |
|---|
|
Table 19-41 summarizes complete configuration requirements for authentication POST data handling. All requirements described in Table 19-41 are supported end to end with the authentication schemes in Table 19-40.
Table 19-41 Parameters Required for Authentication POST Data Handling
| Parameter | Description |
|---|---|
|
MaxPostDataBytes |
Configure this Authentication Scheme challenge parameter for POST-data preservation used by the DCC only to limit the maximum size of the POST data that can be posted as on the login form. DCC compares the value of the content-length header with the limit set. Default: unlimited This Authentication Scheme challenge parameter requires a positive integer value that restricts the maximum number of bytes of POST data that is submitted as user credentials and sent to the OAM Server. |
|
MaxPreservedPostDataBytes |
Configure this Authentication Scheme challenge parameter (or user-defined Webgate parameter) for authentication POST-data preservation. Default: 8192 bytes Note: Preference is given first to the Authentication Scheme containing this parameter; second to the Webgate providing this user-defined parameter. Otherwise, default behavior is 8192 bytes. This parameter defines the maximum length of POST data that Webgate can preserve. If the size of inbound raw user POST data (or encrypted post data after processing), crosses this limit, POST data is dropped and the existing authentication flow continues. The event is logged as usual. |
|
TempStateMode=form DCC Only |
With the DCC, a Form-based Authentication Scheme requires the challenge parameter TempStateMode=form for POST data restoration For Form authentication scheme, if this parameter is not defined, the value will be "form". |
|
ChallengeRedirectMaxMessageBytes |
Configure this user-defined Webgate parameter to limit the size of the message data received as obrareq.cgi and obrar.cgi. Message data is comprised of query string length (if present) or POST data length (if POST data is present). If message size exceeds this limit, the message is not processed and the existing message is shown in the browser. The event is logged as usual. Default: 8192 bytes Notes: obrareq.cgi is the authentication request in the form of a query string redirected from Webgate to the credential collector (OAM Server or DCC). obrar.cgi is the authentication response string redirected from the credential collector (OAM Server or DCC) to Webgate. |
|
PostDataRestoration |
Configure this user-defined Webgate parameter to initiate authentication POST-data preservation for the resource Webgate. This parameter requires a value of Default: When set to |
|
serverRequestCacheType ECC Only |
Configure this OAM parameter to define the mechanism used to remember the request context by the embedded credential collector (ECC). This OAM Server parameter in $DOMAIN_HOME Default: COOKIE FORM is the required value for POST data preservation, Long URL handling and Form-based authentication schemes. See Also: |
19.17.3 About Post Data Size Limits
Assuming the usual form data entered by users is about several kilobytes, putting a limit on data comsumption from the incoming request is a general requirement. The data transferred in the front channel protocol (either request or response) must also go through the size check. Considering these situations:
-
Limit the size of data passed to the OAM Server on the back channel using the maxpostdatabytes authentication challenge parameter
In cases where the DCC is used, the maxpostdatabytes authentication challenge parameter performs this check on the overall POST data.
-
Limit the size of the POST data from the end user application using MaxPreservedPostDataBytes authentication scheme challenge parameter.
The MaxPreservedPostDataBytes authentication scheme challenge parameter handles this. Additionally, this can be set as a user-defined Webgate parameter.
-
Limit size of the front channel payload on obrar.cgi or obrareq.cgi with a Webgate user-defined parameter ChallengeRedirectMaxMessageBytes.
19.17.4 Configuring Authentication POST Data Handling
Be sure to read all POST data topics in this section before attempting this procedure. There is no need to make any explicit change in your authentication scheme.
To configure authentication POST data handling
-
Configure the Authentication Scheme:
-
From the Oracle Access Management Console, create or find the desired scheme (Table 19-40).
-
On the Authentication Scheme page, modify values for POST data handling.
This example uses the embedded credential collector (Table 19-20) and values for POST data handling (Table 19-23):
Name: DesiredScheme
Authentication Level 2
Challenge Method: Form
Challenge Redirect URL: /oam/server/
Authentication Module: LDAP
Challenge URL: /pages/login.jsp
Context Type: External
Challenge ParametersAuthentication Scheme Challenge Parameters for Post Data with ECC Authentication Scheme Challenge Parameters for Post Data with DCC
MaxPreservedPostDataBytes=9000
MaxPreservedPostDataBytes=9000
TempStateMode=form -
Click Apply to submit the changes.
-
-
ECC: Configure serverRequestCacheType, the OAM parameter in oam-config.xml, if using ECC.
-
Stop the managed server.
-
Stop the administration server.
-
Open oam-config.xml and modify the value of serverRequestCacheType.
-
Save the file.
-
Restart the administration server.
-
Restart the managed server.
-
-
Configure Webgate Parameters for POST data handling:
-
From the System Configuration tab, Access Manager section, create or find the desired OAM Agent registration.
-
On the agent registration page, submit values for POST data handling (Table 19-23):
Name: DesiredAgent
User-Defined ParametersUser-Defined Webgate Post Data Parameters with ECC User-Defined Webgate Post Data Parameters with DCC
PostDataRestoration=true
PostDataRestoration=true -
Click Apply to submit the changes.
-
19.17.5 Testing POST Data Handling Configuration
The following actions can be performed in sequence to test your POST data handling configuration.
-
Complete all configurations as documented.
-
Develop a simple script to print the POST data and the URL protected by Webgate.
-
Use a browser to access the protected resource.
-
Provide credentials and establish SSO. Wait for the idle session timeout period.
-
With the same browser, use the form to post data to the same Webgate using the URL which can print the POST data. You will be redirected to credential collector.
-
Enter the same credentials previously used.
From the HTTP headers you can see, after getting obrar.cgi from the credential collector, the protected resource Webgate will give a 200 response (previously it was 302) and the POST data can be printed by your script.
19.18 Long URL Handling During Authentication
Long URL handling applies to both credential collectors (ECC or DCC) and is a default operation.
19.18.1 About Long URLs and Authentication Handling
Authentication involves redirecting the user's request to a centralized component that performs authentication, known as a Credential Collector. The mechanism used to redirect user from the policy enforcement point (OAM Agent) to the Credential Collector, is a proprietary front channel protocol over HTTP. This protocol currently provides the context of the request and the authentication response on the query string. In situations where the URL of the requested page is larger, the overall context becomes larger and can go beyond the browser's permissible size. This is referred to as Long URL Handling.
By default, the Resource Webgate checks the payload size of the front channel protocol message to determine if it is larger than the coded limit. When long URL handling is explicitly enabled, the limit is ignored and has no impact.
The credential collector determines if the front channel response payload is to be sent as HTTP Post data when:
-
The incoming request indicates that the agent is capable of handling HTTP POST or REDIRECT type of response
-
The credential collector is configured to always send the payload as HTTP post data
-
The credential collector is configured to always send the payload as a query string
If no explicit configuration is present, then if the payload size is greater than predefined limit, then it shall send payload as the HTTP post data. But if the payload size is lower than the predefined limit, then it shall send it on the query string.
Note:
If application post data is also preserved there is no impact.Table 19-42 identifies Long URL handling functionality with both the ECC and DCC.
Table 19-42 ECC and DCC: Long URL Handling
| ECC Long URL Handling | DCC Long URL Handling |
|---|---|
|
ECC is compatible with all 11g Webgates. |
Same as ECC. |
|
N/A |
Long URL handling is limited to the maximum allowed size of the DCCContextCookie. The DCC does not perform explicit long URL handling. There is no support to preserve the front channel payload on the form. |
19.18.2 About Configuring Long URL Handling
Table 19-43 summarizes the authentication schemes that support authentication Long URL handling.
Table 19-43 Authentication Schemes Supporting Long URL Handling
| Authentication Schemes |
|---|
|
Table 19-44 summarizes the parameters and complete configuration requirements for authentication Long URL handling. All requirements described in Table 19-44 are supported end to end with the authentication schemes in Table 19-43.
Table 19-44 Parameters Required for Long URL Handling
| Parameter | Description |
|---|---|
|
ChallengeRedirectMethod |
Configure this as either as an Authentication Scheme challenge parameter (or as a user-defined Webgate parameter) for POST-data preservation for both the embedded credential collector (ECC) and the detached credential collector (DCC). Note: Preference is given first to the Authentication Scheme containing this parameter; second to the Webgate providing this user-defined parameter. Otherwise, default behavior is Dynamic. Value: GET|POST|DYNAMIC Behavior when value is:
|
|
ChallengeRedirectMaxMessageBytes |
Configure this user-defined Webgate parameter to limit the size of the message data received as obrareq.cgi and obrar.cgi. Message data is comprised of query string length (if present) or POST data length (if POST data is present). If message size exceeds this limit, the message is not processed and the existing message is shown in the browser. The event is logged as usual. Default: 8192 bytes Notes: obrareq.cgi is the authentication request in the form of a query string redirected from Webgate to the credential collector (OAM server or DCC). obrar.cgi is the authentication response string redirected from the credential collector (OAM server or DCC) to Webgate. |
|
serverRequestCacheType ECC Only |
Configure this OAM parameter to define the mechanism used to remember the request context by the embedded credential collector (ECC). This OAM Server parameter in $DOMAIN_HOME Default: COOKIE FORM is the required value for POST data preservation, Long URL handling and Form-based authentication schemes. See Also: |
Long URL handling is enabled by default. The Webgate/credential collector sends data either as a query string or a POST. The length of the querystring parameter sent with obrareq.cgi and obrar.cgi is 2000 characters maximum.
19.19 Using Application Initiated Authentication
Access Manager exposes a Reauthentication URL that applications may choose to invoke if the user is accessing a sensitive URL or operation. This re-authentication will be triggered irrespective of whether or not the user already has a valid session. An application can trigger re-authentication by invoking the /oamreauthenticate URL at:
http://<ohs_host>:<ohs_port>/oamreauthenticate
Access Manager will expect the /oamreauthenticate to be registered and associated with an authentication policy. Re-authentication will be performed using the scheme associated with this policy. The re-authentication URL takes the redirection URL as a query parameter. After re-authentication is complete, Access Manager redirects the user to this URL. A request to re-authenticate the user might look like the following:
http://<host>:<port>/oamreauthenticate? redirect_url=http://<host>:<port>/<redirection_resource_url>
If the redirection URL is not specified, a 404 error code is returned. If the incorrect credentials are specified during re-authentication, the user will remain on the login page and, after the maximum retry limit, the user will be redirected to an appropriate error page. The following process is how to configure for application initiated authentication.
-
Create an
http://<ohs_host>:<ohs_port>/oamreauthenticateresource and assign the desired authentication scheme to it. -
In the redirect URL, set the appropriate responses to verify that re-authentication has been successful and to communicate back to the application about the re-authentication responses.
Access Manager sets the last re-authentication time as a "OAM_LAST_REAUTHENTICATION_TIME" header and this value is updated every time the user is re-authenticated.
19.20 Using the Adaptive Authentication Service
Oftentimes, passwords alone are not enough to protect resources from hackers and cyber-criminals. The Adaptive Authentication Service is a One Time Password Authenticator that provides multifactor authentication in addition to the standard user name and password type authentication. Multifactor authentication is a two-step process in which users are required to provide a user name, password and a second generated password before access to a requested service is allowed. The second password, referred to as a One Time Password (OTP), is generated using an app on a mobile device. The supported apps are Oracle Mobile Authenticator and Google Authenticator. (For this release, only iOS and Android devices are supported.)
Note:
Time-based One Time Password (TOTP) is a two-factor authentication scheme specified by the Internet Engineering Task Force (IETF) under RFC 6238 and used by the Adaptive Authentication Service. TOTP is an extension of the HMAC-based One Time Password algorithm and supports a time-based moving factor (a value that must be changed each time a new password is generated).To use the Adaptive Authentication Service, a user downloads one of the authenticator apps to a mobile device (for example, Oracle Mobile Authenticator to an Apple iPhone) and configures it by clicking a link provided by the Access Manager administrator. Then, to obtain a secret key, the user launches the app, clicks Online Configuration, and enters his/her credentials. Following a successful authentication, the app displays a OTP with validity. The following sections have more details.
Note:
The Adaptive Authentication Service requires either an Oracle Adaptive Access Manager license or an Application Management Services license.19.20.1 Understanding the Adaptive Authentication Service
The following sections contain specific details on the Adaptive Authentication Service.
19.20.1.1 Understanding the One Time Password Flow
When using an Authenticator mobile app to generate a One Time Password (OTP), the Authenticator app is first configured with the Access Manager server details in order to obtain the secret key to generate a OTP. Following this, the user authenticates with Access Manager using the proper credentials and Access Manager returns the user's secret key. This secret key is unique to each user and known only to Access Manager and the Authenticator app. (See Generating a Secret Key for details.)
When the user accesses a protected resource, a page is displayed that requests a user name and password. If these initial credentials are authenticated successfully, a OTP page is displayed. The user enters the OTP displayed by the mobile Authenticator app in the OTP page. Once the OTP is validated by Access Manager, access is allowed.
Note:
The Authenticator app refreshes the OTP every 30 seconds so the OTP entered by a user is valid only for that period of time. Access Manager also generates a OTP for the user with the same secret key and refresh period. Thus if the OTP generated by Access Manager matches the OTP entered by the user, access to the protected resource is allowed. If the OTP entries do not match, access is not allowed.19.20.1.2 Generating a Secret Key
Businesses can generate secret keys in different ways. The means in which the secret key is generated makes no difference to Access Manager although the specific information required by Access Manager must be integrated within it. The secret key needs to be shared with Access Manager and the Authenticator app. The following list of parameters and their values must be passed to the business before they generate a shared secret key.
-
Client Id - identifier for the Mobile and Social client configured in Configuring OAuth for the Google Authenticator. For example, 54321id
-
Client Pass - is the Mobile and Social client password configured in Configuring OAuth for the Google Authenticator.
-
OAMMS Endpoint URL - is the URL where the Mobile and Social REST services are deployed. For example, http://host.example.com:14100/ms_oauth
-
Secret Key Attribute Name - is the LDAP attribute in which the shared secret key will be stored.
19.20.1.3 Understanding Adaptive Authentication Configurations
To use the Adaptive Authentication Service, you must configure Access Manager and the mobile authenticator app. For information on configuring Access Manager to use the Adaptive Authentication Service, see:
For information on configuring your mobile authenticator app for use with the Adaptive Authentication Service, see the applicable section:
19.20.2 Configuring Access Manager for Two-Factor Authentication
The following sections contain details on two-factor authentication configurations using the Administration Console. They assume that Access Manager 11gR2PS2, a WebGate and the Oracle HTTP Server (OHS) are installed and configured.
19.20.2.1 Configuring OAuth for the Oracle Mobile Authenticator
Using the Administration Console, follow this procedure to enable the Mobile and Social Service and update the User Profile Service to protect the REST Secret Key Service using the Basic Authentication Scheme. This configuration is for use with the Oracle Mobile Authenticator.
-
From the Launch Pad, navigate to the Configuration panel and click Available Services.
-
Click Enable to enable Mobile and Social.
-
From the Launch Pad, click OAuth Service under the Mobile and Social panel.
-
Click DefaultDomain under OAuth Identity Domains.
-
From the Resource Servers tab, click UserProfile under User Profile Services.
-
Expand the Resource URIs.
-
From the
/secretkeytab, update the value ofbasicauth.allowedto true. -
Click Apply.
19.20.2.2 Configuring OAuth for the Google Authenticator
Using the Administration Console, follow this procedure to create an OAuth web client. This configuration is for use with the Google Authenticator.
-
From the Launch Pad, navigate to the Configuration panel and click Available Services.
-
Click Enable to enable Mobile and Social.
-
From the Launch Pad, click OAuth Service under the Mobile and Social panel.
-
From the OAuth Identity Domain tab, open the DefaultDomain identity domain.
-
From the DefaultDomain tab, click the OAuth Clients tab.
-
From the Oauth Clients tab, click Create to create a Web Client.
This opens a new configuration tab.
-
Enter the following details.
-
Name - a mandatory name for the Mobile and Social client.
-
Description - an optional description of the Mobile and Social client.
-
Client Id - a mandatory identifier for the Mobile and Social client. For example, 54321id
-
Client Secret - is the mandatory Mobile and Social client password.
See Generating a Secret Key for details.
-
-
Open the Privileges section and tick the "Allow access to all scopes" check box.
Scopes are configured per use case.
-
Tick the All check box under Grant Types.
Grants are configured per use case.
-
Click Create.
19.20.2.3 Configuring Access Manager
The following configurations are for Access Manager.
19.20.2.3.1 Creating an Instance of TOTPModule
Access Manager provides an authentication module called TOTPModule that can be used out-of-the-box for TOTP authentication. Follow this procedure to create an instance of this module.
-
From the Launch Pad, click Authentication Modules in the Access Manager panel.
-
From the Authentication Modules tab, click Search.
The search results are displayed.
-
Click TOTPModule to open its tab.
-
Under the TOTPModule tab, click the Steps tab.
-
Click the plus sign (+) to create a new step.
A step instance is created by default. You can use it to configure or delete it, create a new one and configure.
-
Enter a step name (for example, OTPInstance) and select TOTP Plugin from the Plugin drop down.
-
Configure the KEY_OTP_SECRETKEY_ATTRIBUTE and KEY_IDENTITY_STORE_REF properties.
These parameters take as values the name of the user attribute in which the secret key will be stored. Leave the other properties as default.
Note:
The value of KEY_OTP_TIME_WINDOW is the number of OTP codes generated by the mobile device that Access Manager will accept for validation. Since the mobile device generates a new OTP every 30 seconds, if the property's value is 3, Access Manager will accept the current and last three OTPs generated by the mobile device. -
Save the changes and click Apply.
19.20.2.3.2 Configuring the TOTP Plug-in Parameters
Follow this procedure to configure the parameters for the TOTP plug-in.
-
Click "Plug-ins" under the Access Manager panel on the Launch Pad.
-
Click "TOTPPlugin".
A configuration details page is displayed.
-
Configure the plugin properties KEY_OTP_SECRETKEY_ATTRIBUTE and KEY_IDENTITY_STORE_REF.
Leave default values in the other properties.
Note:
The value of KEY_OTP_TIME_WINDOW is the number of OTP codes generated by the mobile device that Access Manager will accept for validation. Since the mobile device generates a new OTP every 30 seconds, if the property's value is 3, Access Manager will accept the current and last three OTPs generated by the mobile device. -
Click Save.
19.20.2.3.3 Creating an OTP Authentication Scheme
Follow this procedure to create an OTP Authentication Scheme to use with the module instance previously created.
-
From the Launch Pad, click Authentication Schemes under the Access Manager panel.
-
Under Authentication Schemes, click LDAPScheme.
The LDAPScheme tab is displayed.
-
Under the LDAP Scheme tab, click Duplicate to create a copy.
-
Under the the new copy's tab, change the values of the name (currently, TOTPScheme) and the Challenge URL (currently, /pages/getOTP.jsp).
The scheme name may be any valid name.
-
Click Apply.
19.20.2.3.4 Configuring Specific Use Case Values
Configure details for a specific use case. This procedure is an example. Your procedure might differ.
-
From the Launch Pad, click Application Domains under the Access Manager panel.
-
Search for the Application Domain in which the protected resource is configured.
Search results are displayed.
-
Click the name of the applicable Application Domain in the search results to display its configuration.
-
Navigate through Authentication Policies to the Protected Resource Policy that is protecting the resource.
-
Under the Protected Resource Policy, click the Advanced Rules tab and then Post Authentication Rules.
-
Create a new Rule.
-
Click on the + icon to create a new Rule.
-
Enter values for the Rule Name and Description.
-
Enter a value for the condition.
Condition is a Jython script. An example value might be location.clientIP.startwith("127.1"). See Using Pre-Authentication Advanced Rules for details.
-
Specify what to do when the condition evaluates to true.
Two options are Deny Access and Change the Authentication Scheme. In the current example, change the authentication scheme to "TOTPScheme".
-
Click Add to add the Rule.
-
Click Apply to save the changes made to the policy.
-
-
Click Apply.
19.20.3 Configuring the Oracle Mobile Authenticator App
The following sections contain configuration details when using the Oracle Mobile Authenticator (OMA) app on an iOS or Android mobile device.
19.20.3.1 Understanding Oracle Mobile Authenticator Configuration
The Oracle Mobile Authenticator (OMA) app can retrieve the secret key required to generate a OTP. This can be done online or offline.
-
Online Configuration enables the REST web services using the Mobile and Social OAuth functionality described in Configuring OAuth for the Oracle Mobile Authenticator. Once enabled, the Oracle Mobile Authenticator app can invoke this service to get a secret key from Access Manager.
To invoke REST, the Oracle Mobile Authenticator needs to know its location URL so the administrator creates a web page with a link to configure it. When the user clicks this link (provided via e-mail), it launches the Oracle Mobile Authenticator, passes the URL to it and the REST location is configured. The format of the URL follows.
oraclemobileauthenticator://settings?LoginURL::=http://host:port/secretKeyURL
The value specified for the LoginURL query parameter is based on the OAuth settings for Oracle Mobile Authenticator. See Configuring OAuth for the Oracle Mobile Authenticator for details. Online configuration details are documented in Configuring OMA on iOS Using the Online Option and Configuring OMA on Android Using the Online Option.
-
Offline Configuration supports use cases in which the mobile device does not have access to a network or could not connect to the REST end point. The Access Manager administrator sets up a web application which allows the user to generate or recreate a secret key. The user logs into this web application and, after authentication, the user is allowed to view the secret key and enter it in the Authenticator app manually (after clicking the Offline Configuration button). This web application is protected using OAuth as described in Configuring OAuth for the Google Authenticator. Offline configuration details are documented in Configuring OMA on Android Using the Online Option and Configuring OMA on Android Using the Offline Option.
19.20.3.2 Configuring the Oracle Mobile Authenticator App on iOS
The following sections contain configuration details when using OMA on an iOS mobile device.
19.20.3.2.1 Configuring OMA on iOS Using the Online Option
This procedure will configure the OMA on iOS using the administrator URL and create an account. Details about the URL are in Understanding Oracle Mobile Authenticator Configuration.
-
Use the browser on your mobile device to navigate to the URL provided by the Access Manager administrator.
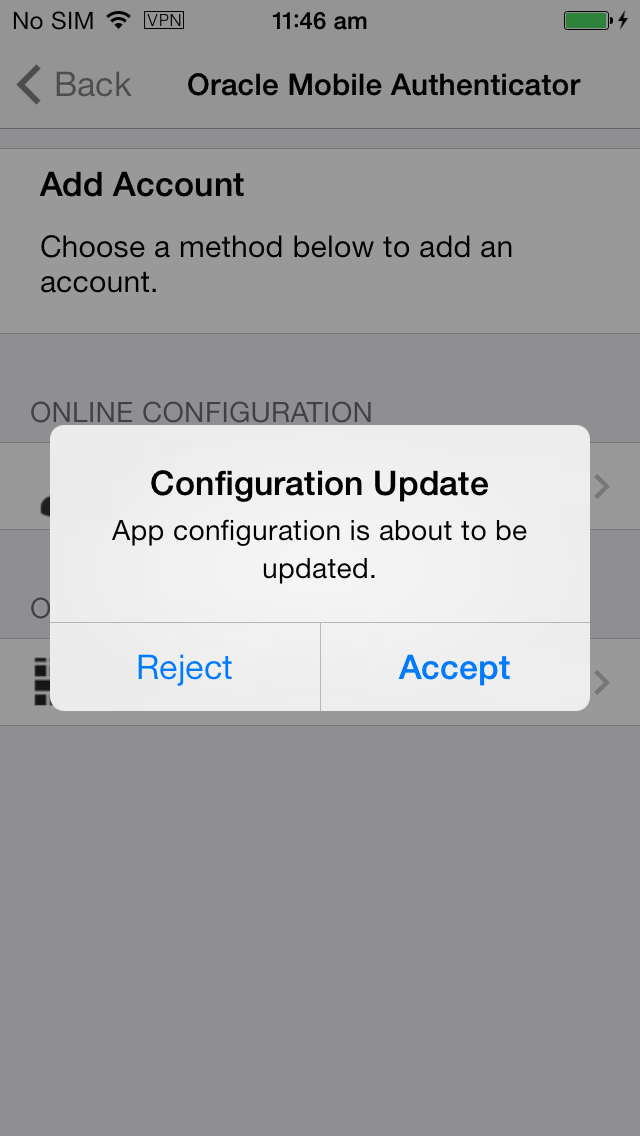
-
Click the link provided on that page to configure Oracle Mobile Authenticator.
The OAM app will open and the user is prompted to accept the update
-
Tap Accept to update.
When the update is complete, a notification is displayed.
-
Tap OK on the notification screen.
-
Tap Sign in.
This will take you to a new screen.
-
Enter your user name, password and tap Submit.
If the user name and password is correct, the OTP screen with details of the new account is displayed. If authentication with the server is successful but an account with the same user name already exists, you will be asked to enter a new user name. Once the user name is unique, you will be taken to the OTP screen with details of the new account.
19.20.3.2.2 Configuring OMA on iOS Using the Offline Option
You can also create an account and retrieve the OTP by manually entering the secret key.
-
Tap on Enter Provided Key.
This will take you to a new screen.
-
Enter a user name and secret key and tap Add Account.
If the user name and key are valid, you will be taken to the OTP screen with details of the new account. If user name is not unique or the key is not valid, you will be prompted to enter the information again.
19.20.3.2.3 Copying a One-Time Password from the Oracle Mobile Authenticator
-
Tap on the account from which you want to copy the OTP.
Three icons are displayed.
-
Tap on the left icon to copy the account.
The OTP will be copied to the clipboard and you can paste it in any text input area.
19.20.3.2.4 Editing an Account on the Oracle Mobile Authenticator
-
Tap on the account you want to edit.
Three icons are displayed.
-
Tap the middle icon to edit an account.
A new screen in which you can edit the user name and secret key is displayed. You can update both user name and password
-
Tap Update Account to complete the modifications.
19.20.3.2.5 Deleting an Account on the Oracle Mobile Authenticator
-
Tap on the account you want to delete.
Three icons are displayed.
-
Tap the right icon to delete an account.
You will be prompted to confirm your decision.
-
Tap Delete Account to confirm and delete.
19.20.3.3 Configuring the Oracle Mobile Authenticator App on Android
The following sections contain configuration details when using OMA on an Android mobile device.
19.20.3.3.1 Configuring OMA on Android Using the Online Option
This procedure will configure the OMA on Android using the administrator URL and create an account. Details about the URL are in Understanding Oracle Mobile Authenticator Configuration.
-
Use the browser on your mobile device to navigate to the URL provided by the Access Manager administrator.
The OMA app will open and the user is prompted to accept the update.
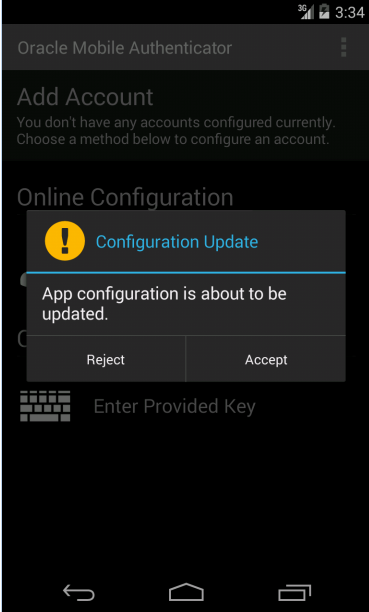
-
Tap Accept to update.
When the update is complete, a notification is displayed.
-
Tap OK on the notification screen.
After configuring the account, get the secret key and generate a OTP.
-
Open the OMA app.
-
Tap Sign in.
This will take you to a new screen.
-
Enter your user name, password and tap Submit.
If the user name and password is correct, the Authentication Code screen with details of the new account is displayed. If authentication with the server is successful but an account with the same user name already exists, you will be asked to enter a new one. If authentication with the server is successful but the account is already configured on a different device, you cannot configure that account as an account can be configured from the server only on a single device. It will show an error as below.
19.20.3.3.2 Configuring OMA on Android Using the Offline Option
You can also create an account and retrieve the OTP by manually entering the secret key.
-
Open the OMA app.
-
Tap on Enter Provided Key.
This will take you to a new screen.
-
Enter a name and key and tap Add Account.
If the user name and key are valid, you will be taken to the OTP screen with details of the new account. If the user name is not unique or the key is not valid, you will be prompted to enter the information again.
-
Tap Sign in.
This will take you to a new screen.
-
Enter your user name, password and tap Submit.
If the user name and password is correct, the Authentication Code screen with details of the new account is displayed. If authentication with the server is successful but an account with the same user name already exists, you will be asked to enter a new one. If authentication with the server is successful but the account is already configured on a different device, you cannot configure that account as an account can be configured from the server only on a single device. It will show an error as below.
19.20.3.3.3 Copying a One-Time Password from the Oracle Mobile Authenticator
-
Long click on the account from which you want to copy the OTP.
A menu bar opens and three icons are displayed.
-
Tap on the left icon to copy the account.
The OTP will be copied to clipboard. You can then paste it in any text input area.
19.20.3.3.4 Editing an Account on the Oracle Mobile Authenticator
-
Long click on the account you want to edit.
A menu bar opens and three icons are displayed.
-
Tap the middle icon to edit an account.
A pop-up is displayed in which you can edit user name and key.
-
Enter the new name and/or key value.
-
Tap Save to update the account.
19.20.3.3.5 Deleting an Account on the Oracle Mobile Authenticator
-
Long click on the account you want to delete.
A menu bar opens and three icons are displayed.
-
Tap the right icon to delete an account.
You will be prompted to confirm your decision.
-
Tap Delete Account to confirm and delete.
19.20.4 Configuring the Google Authenticator App
After receipt of the secret key, it is entered manually into the TOTP client mobile app by the user. For example, to initiate configuration in the supported Google Authenticator, the user creates an account for two-factor authentication using the app. After account creation, the user manually enters the shared secret key received from the resource owner. Additionally, ensure that Time Based OTP is enabled at the bottom of the Google Authenticator screen. The Google Authenticator app generates the OTP code in an offline, disconnected mode; it does not interact with Access Manager.